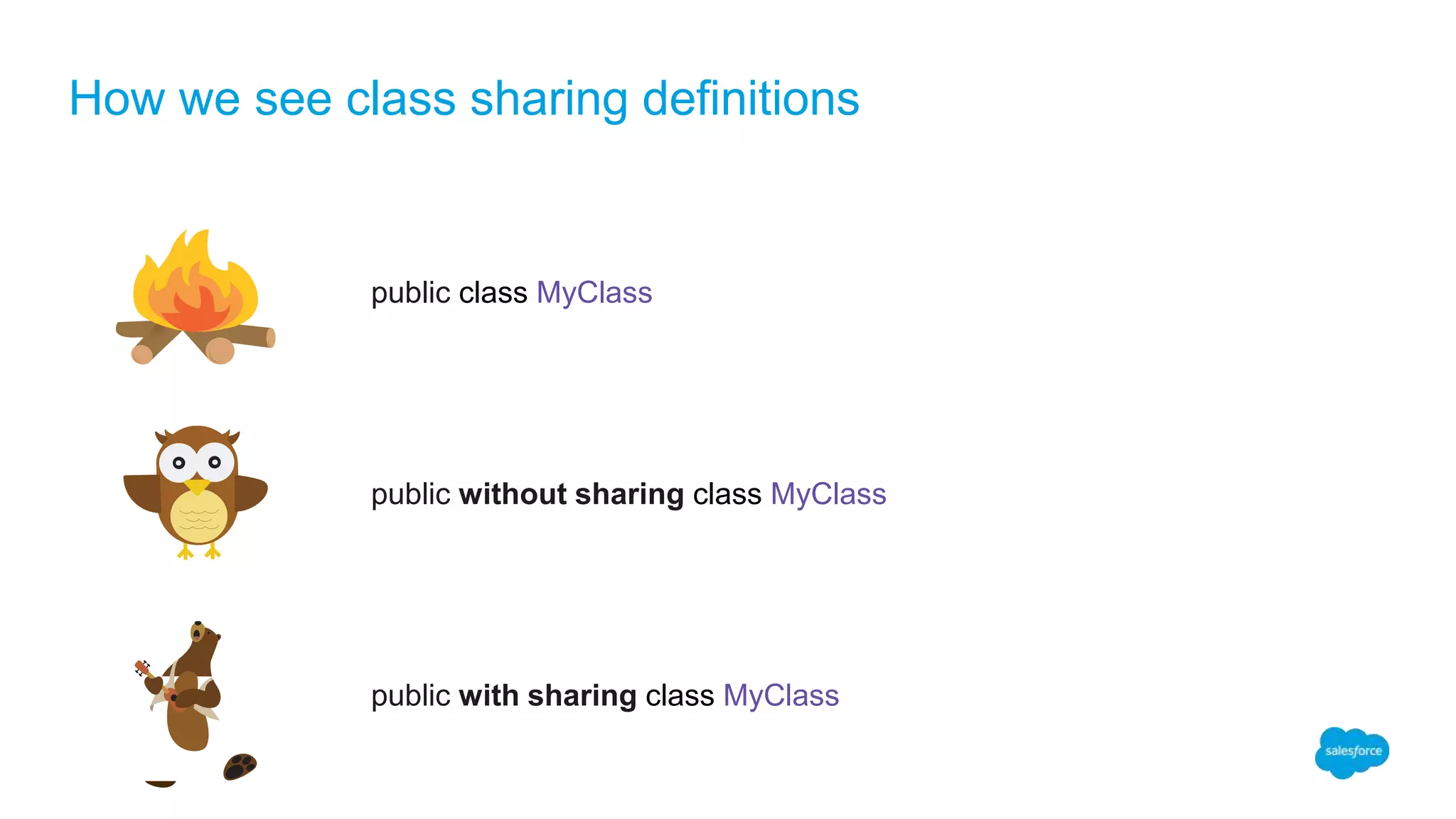
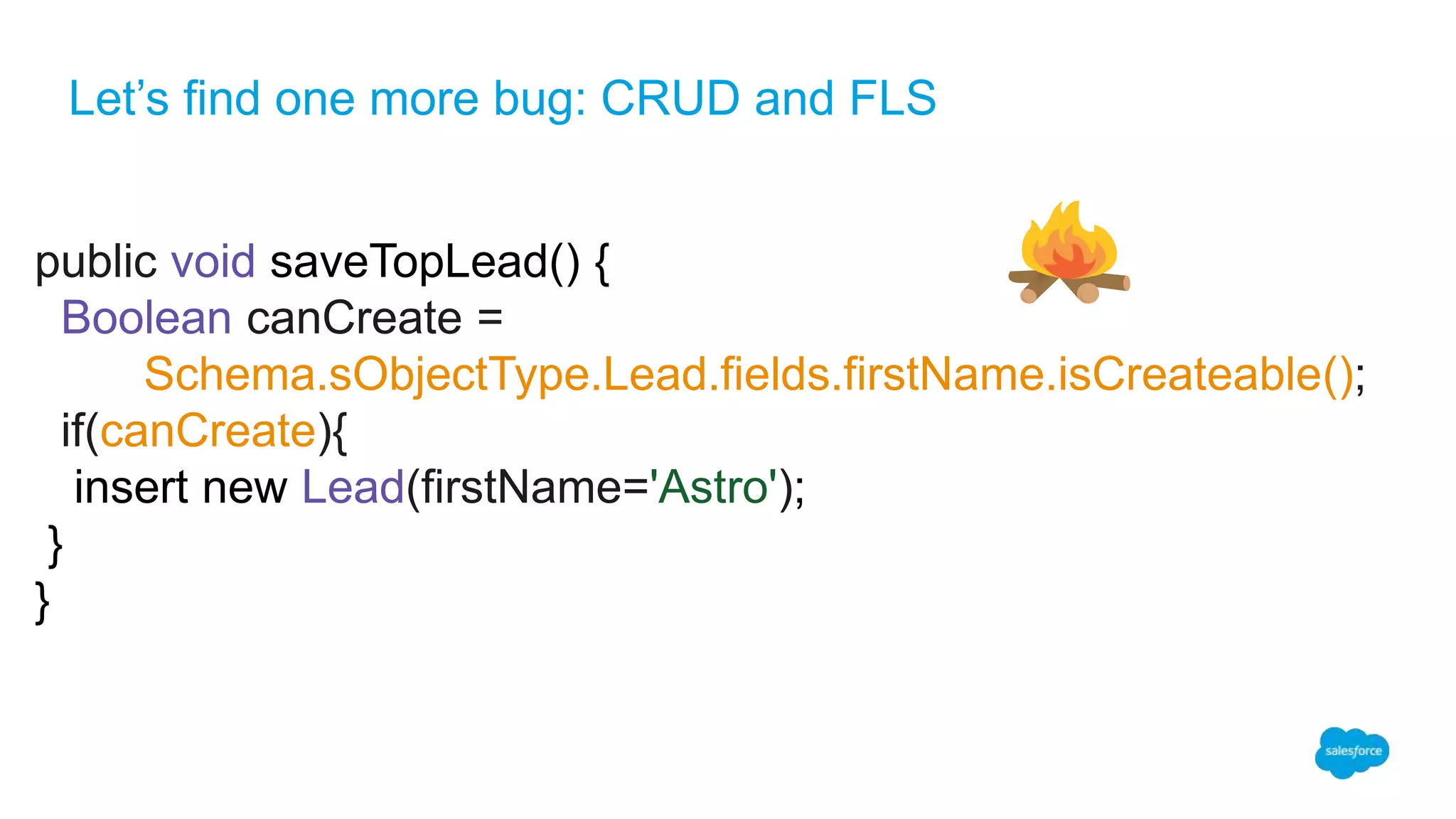
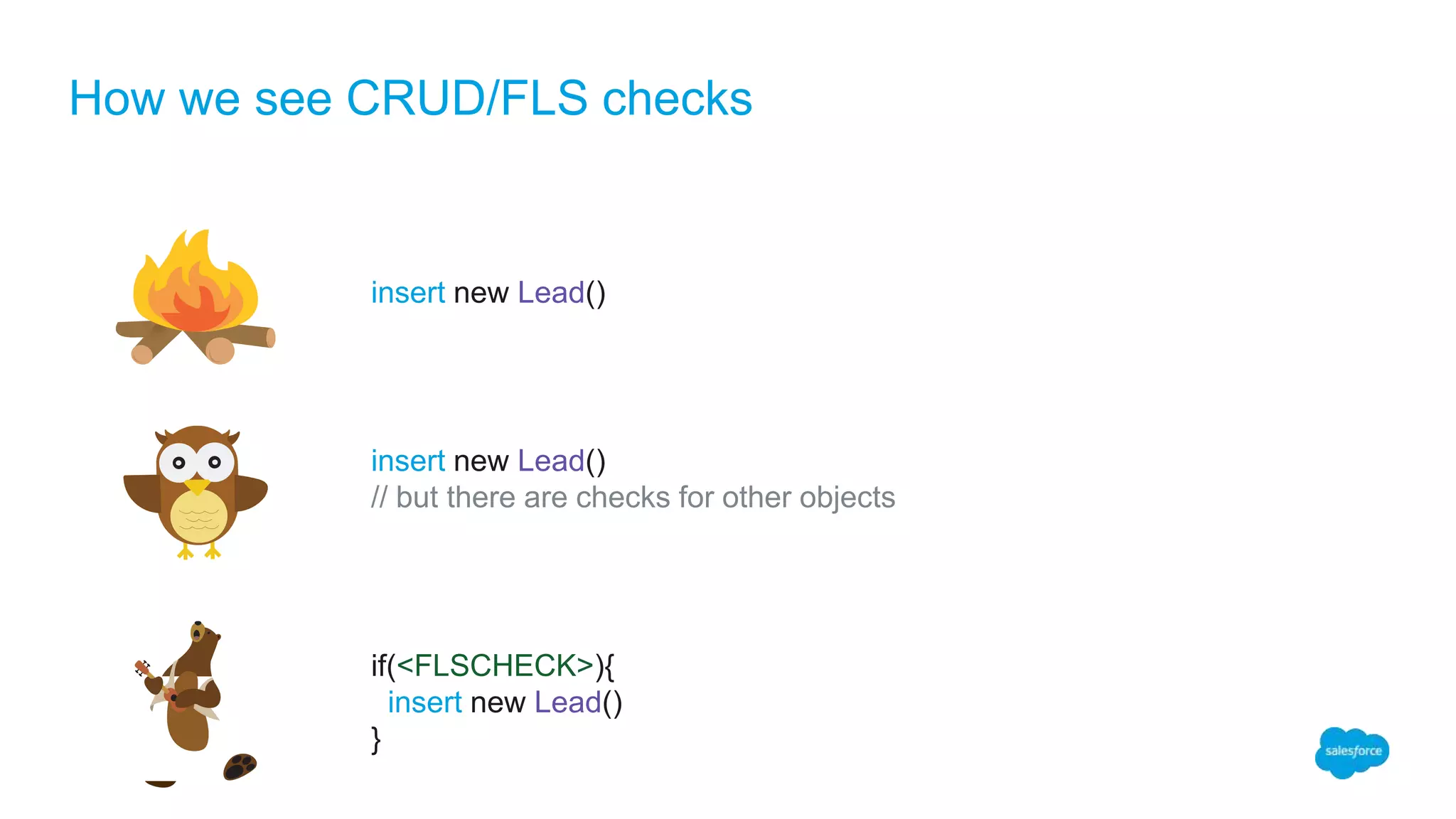
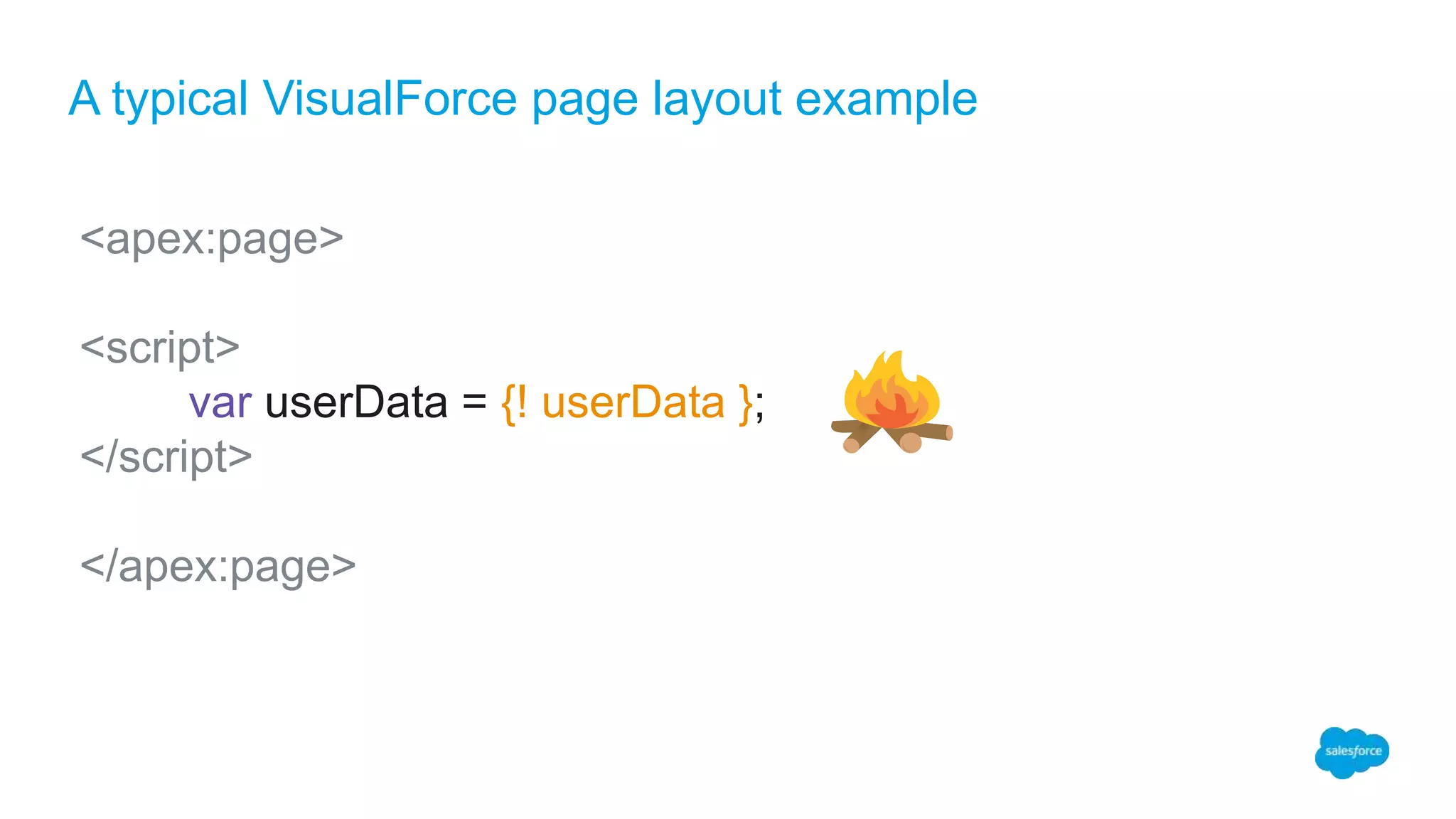
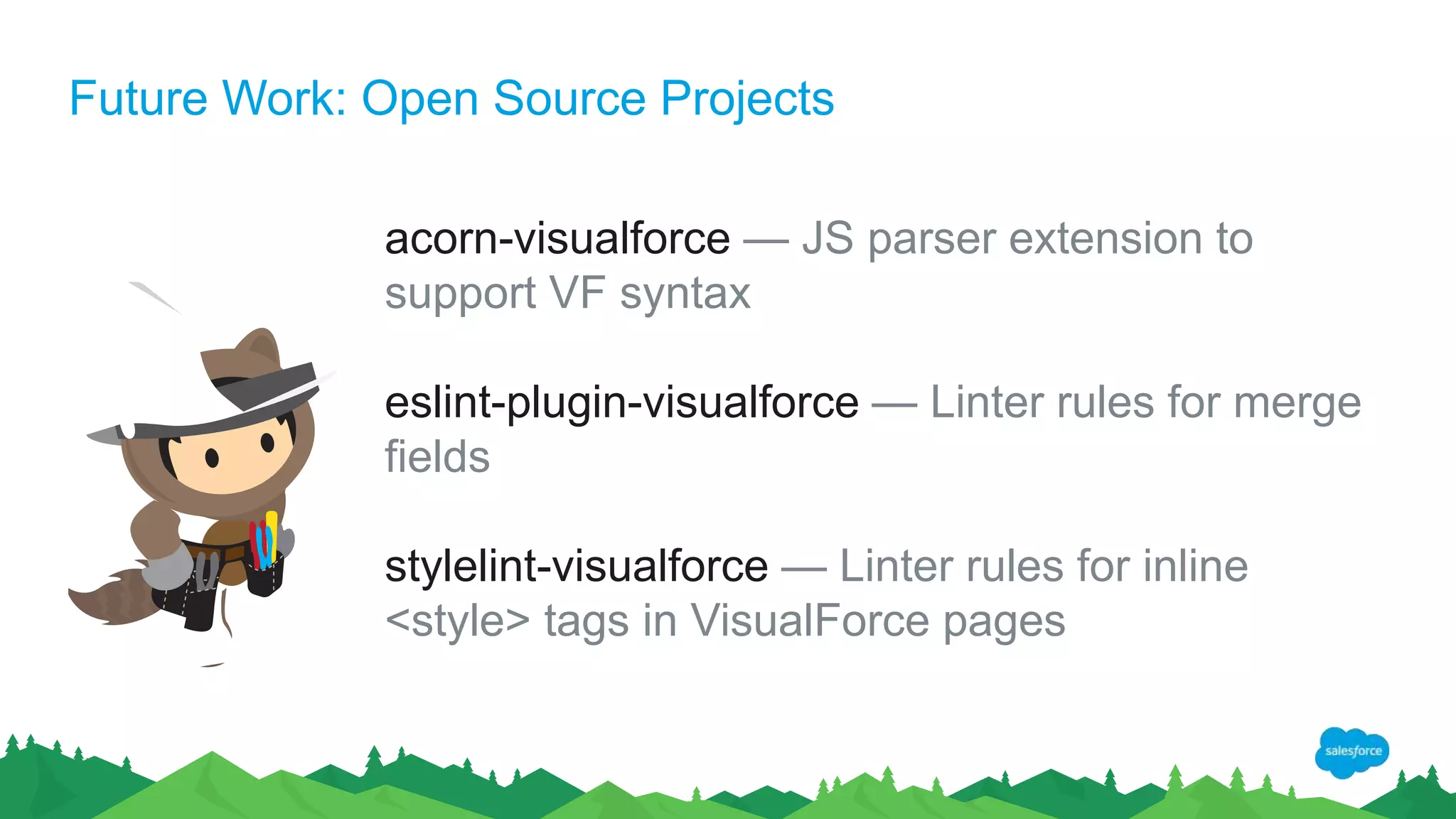
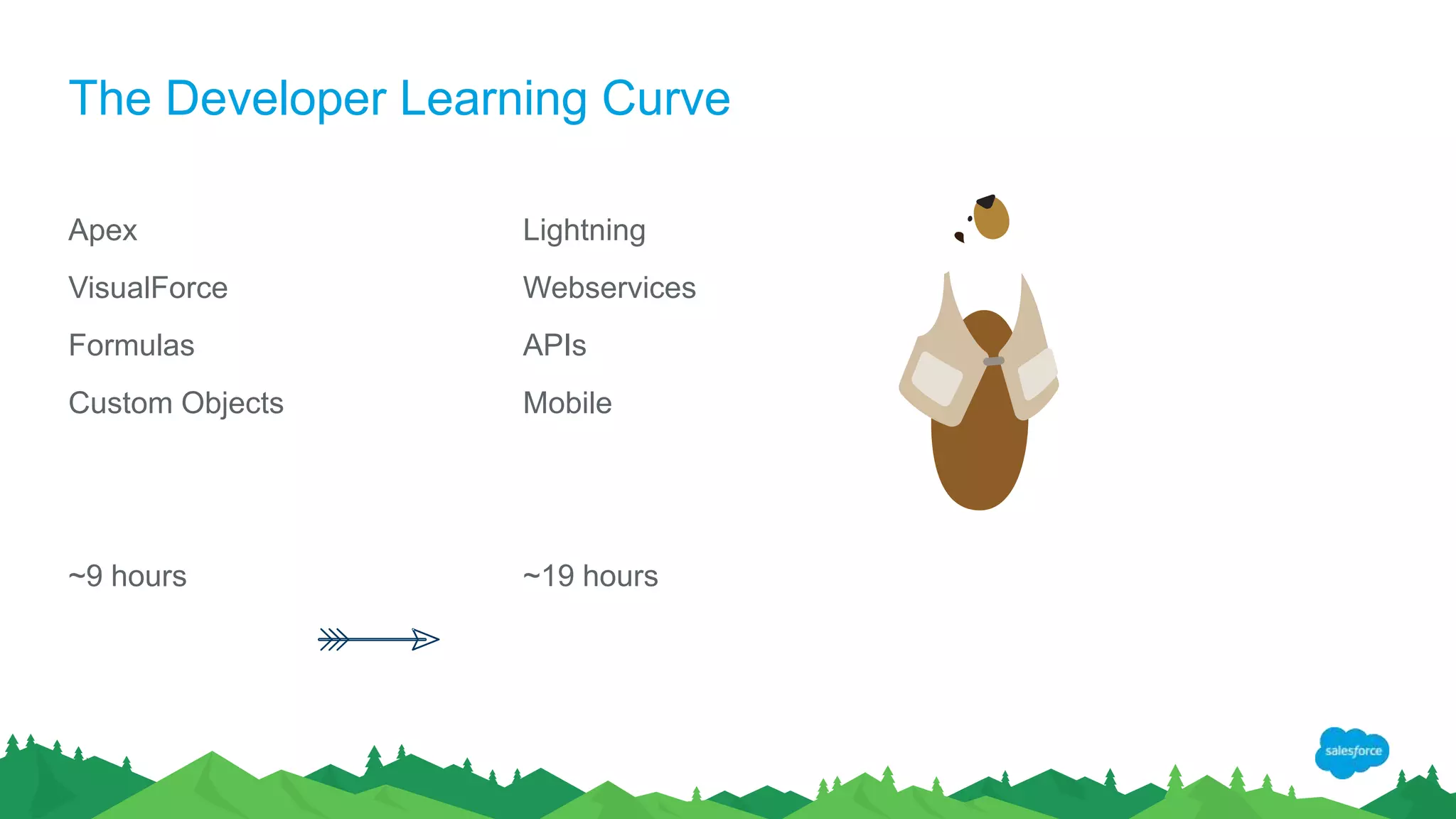
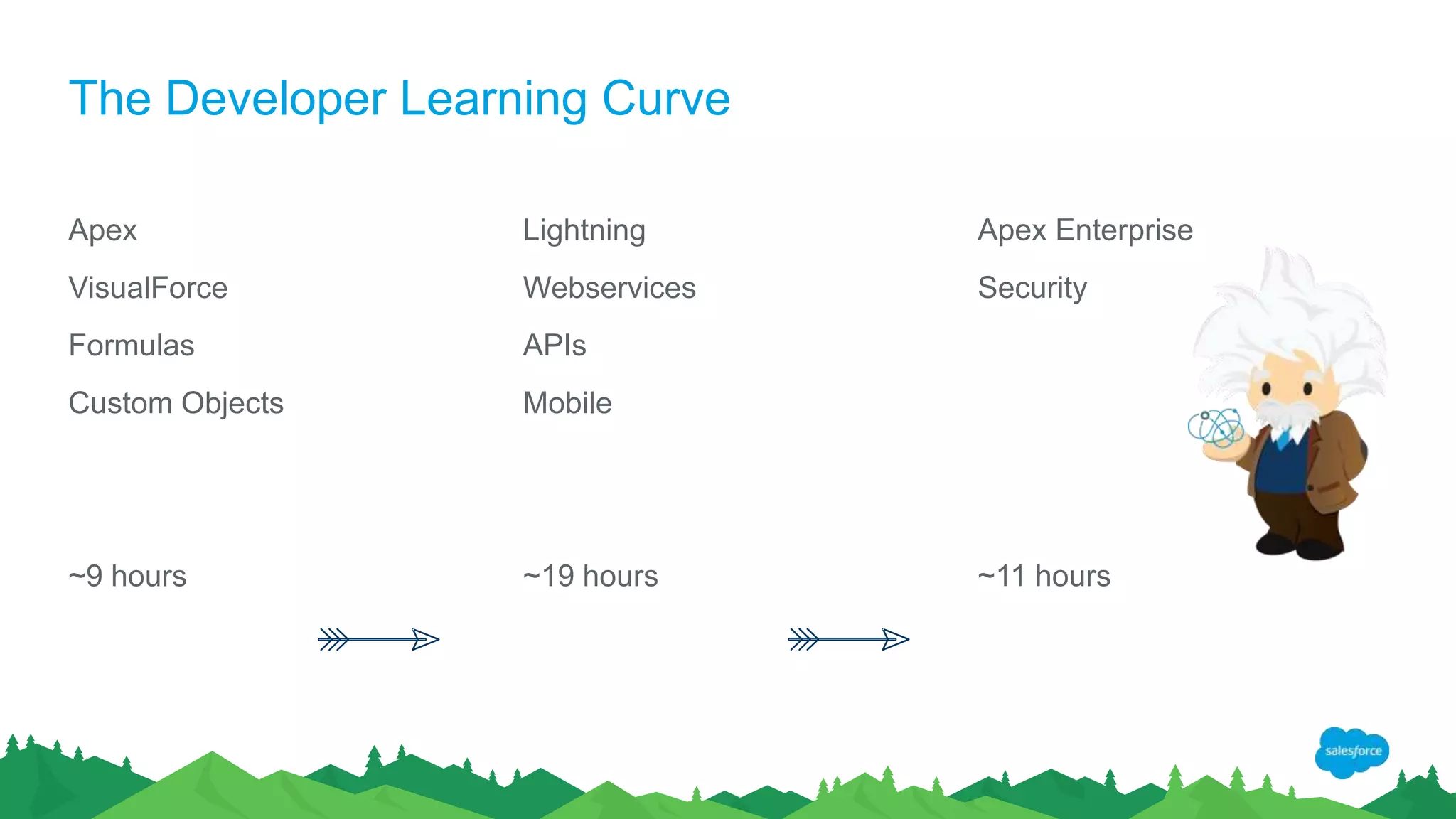
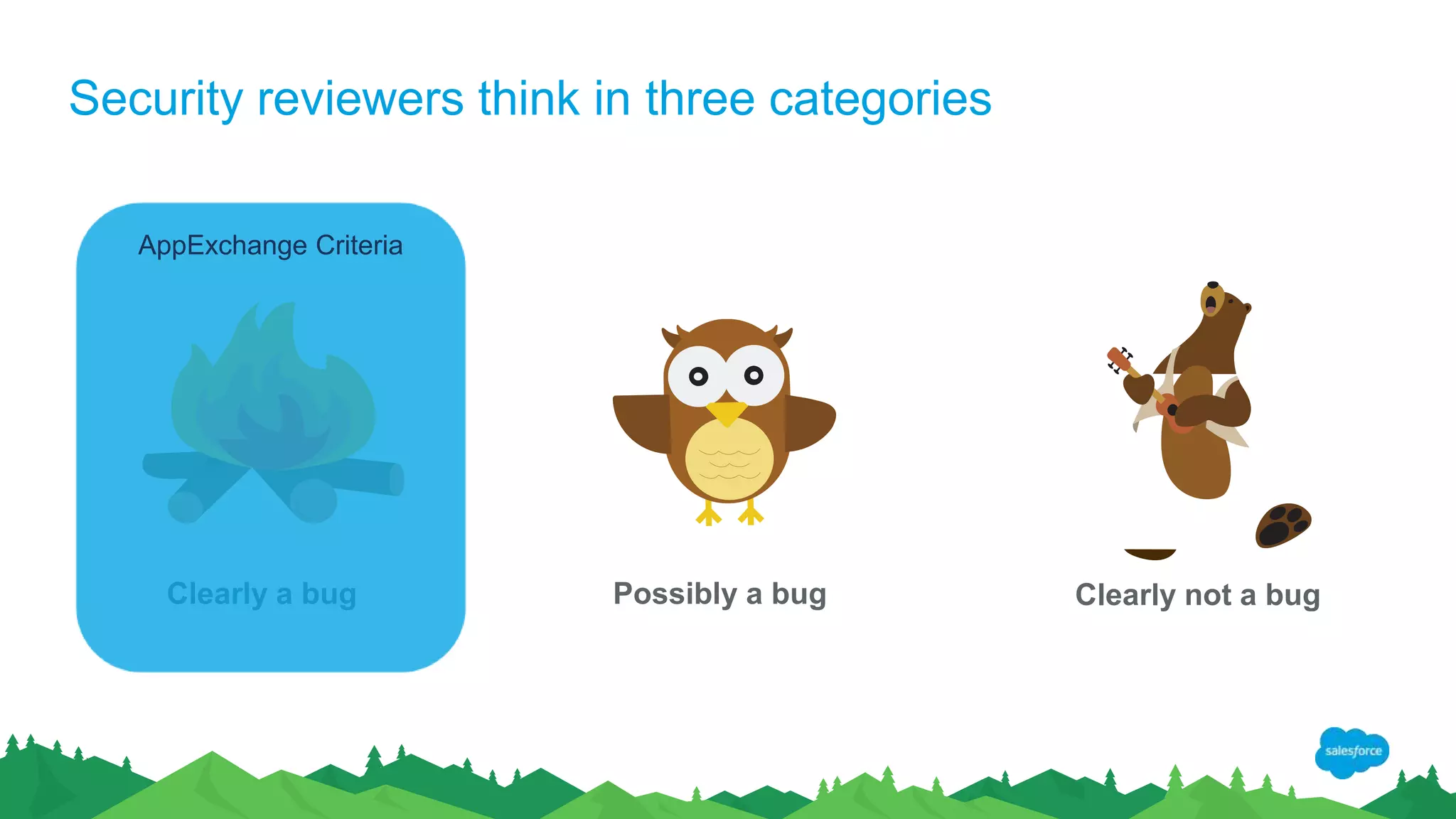
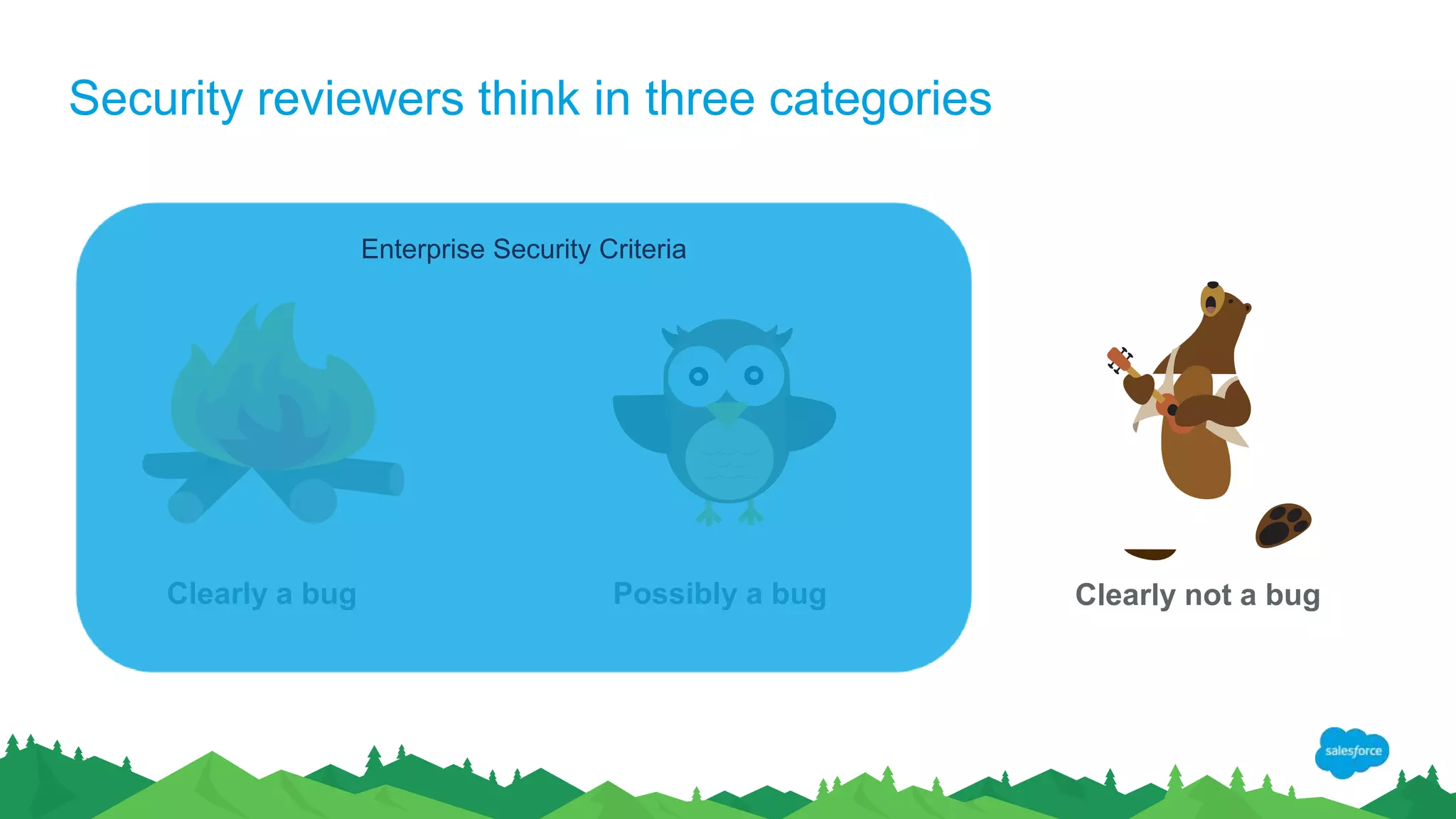
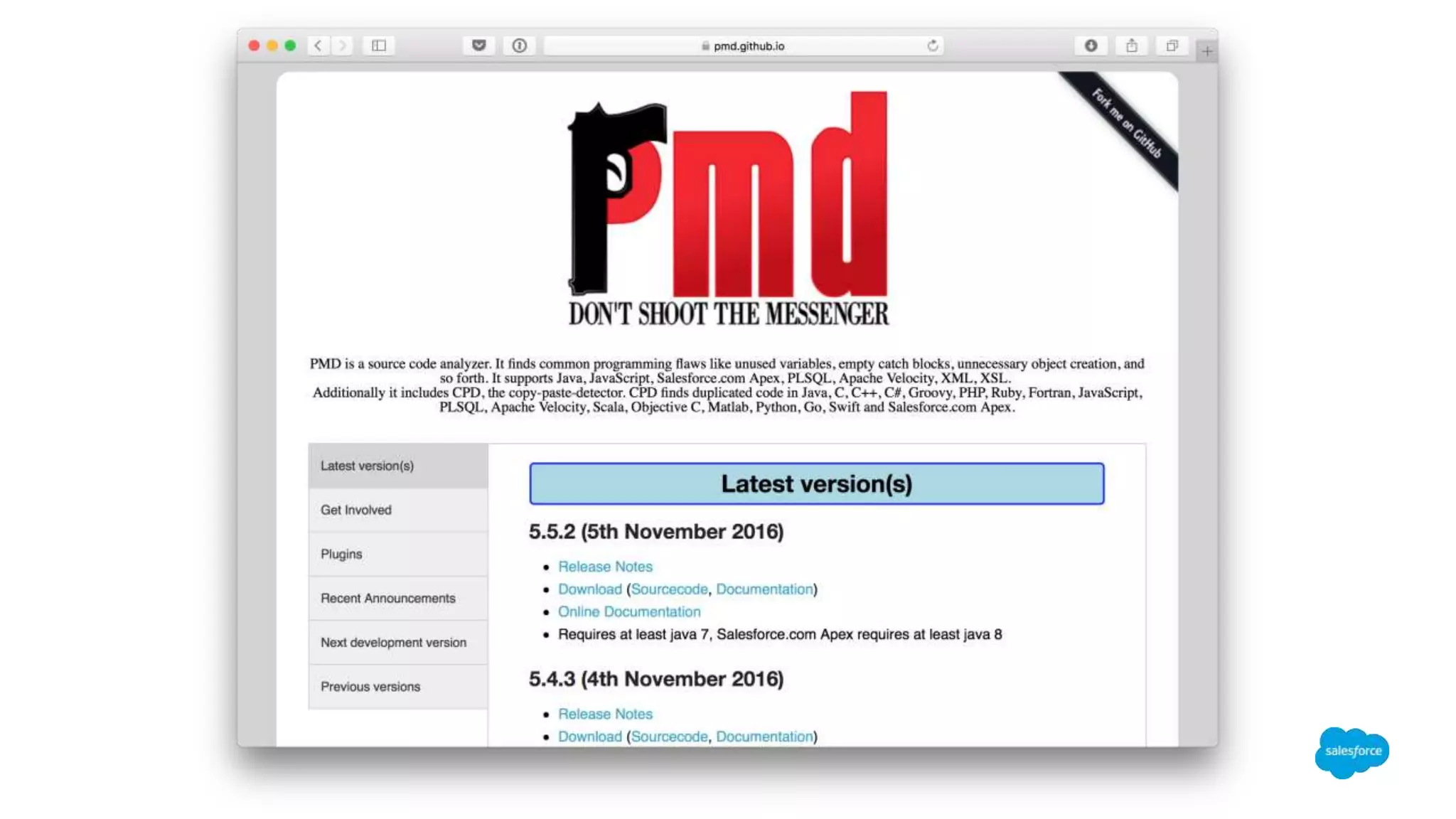
The document discusses salesforce.com's approach to security, highlighting their forward-looking statements and associated risks related to new functionalities, products, and business models. It emphasizes the importance of secure code practices and tools that help developers identify and fix security issues. Additionally, it outlines future work in code quality improvement, including the release of security rules and open-source projects for better coding standards.








![Let’s find a bug with PMD help!
public class HotLeads {
public Lead getTopLead() {
return [SELECT … ] ;
}
}](https://image.slidesharecdn.com/forcedotcommeetup-170130223218/75/Finding-Security-Issues-Fast-16-2048.jpg)
![Let’s find a bug: Sharing violation
public with sharing class HotLeads {
public Lead getTopLead() {
return [SELECT … ] ;
}
}](https://image.slidesharecdn.com/forcedotcommeetup-170130223218/75/Finding-Security-Issues-Fast-17-2048.jpg)