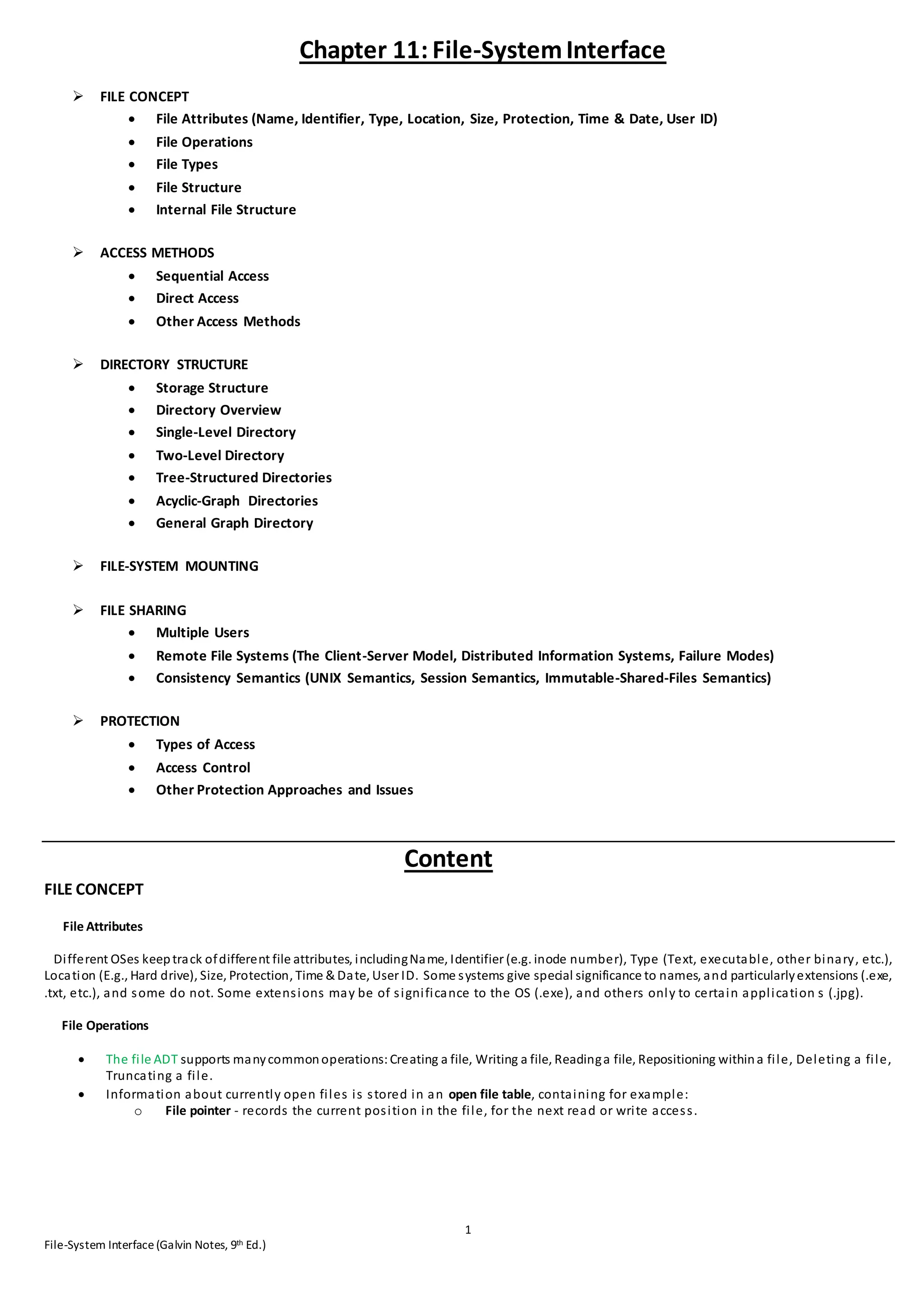
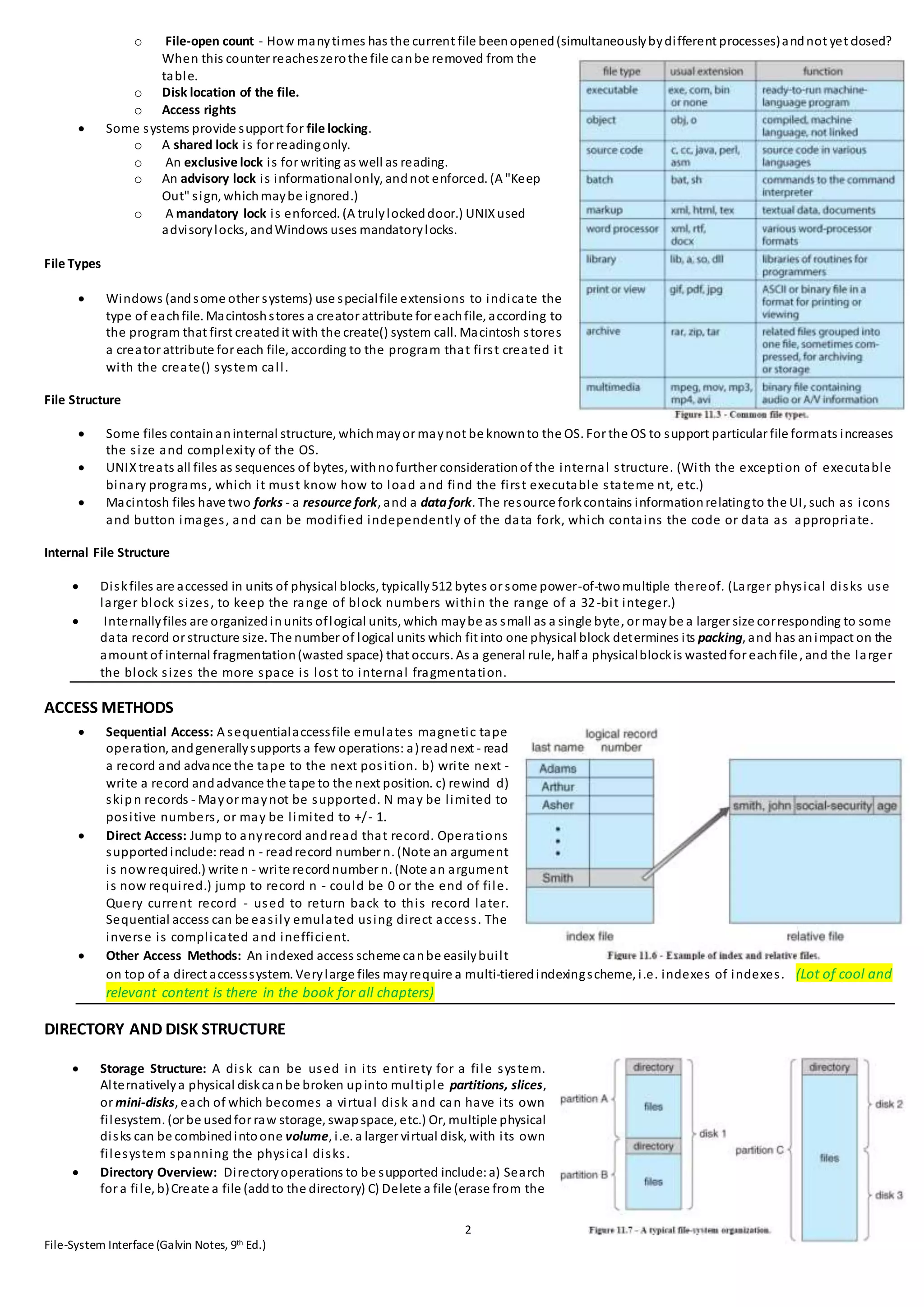
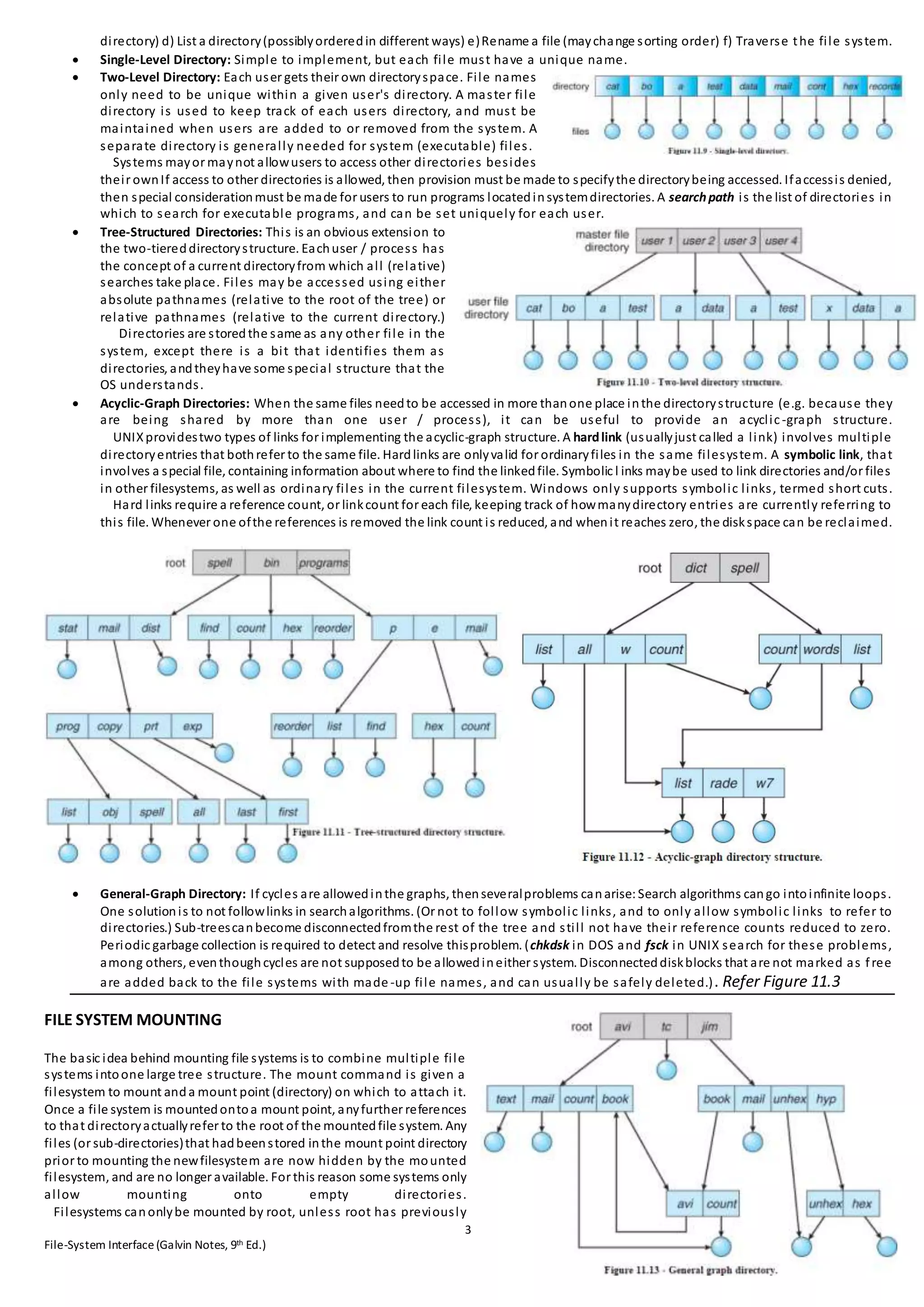
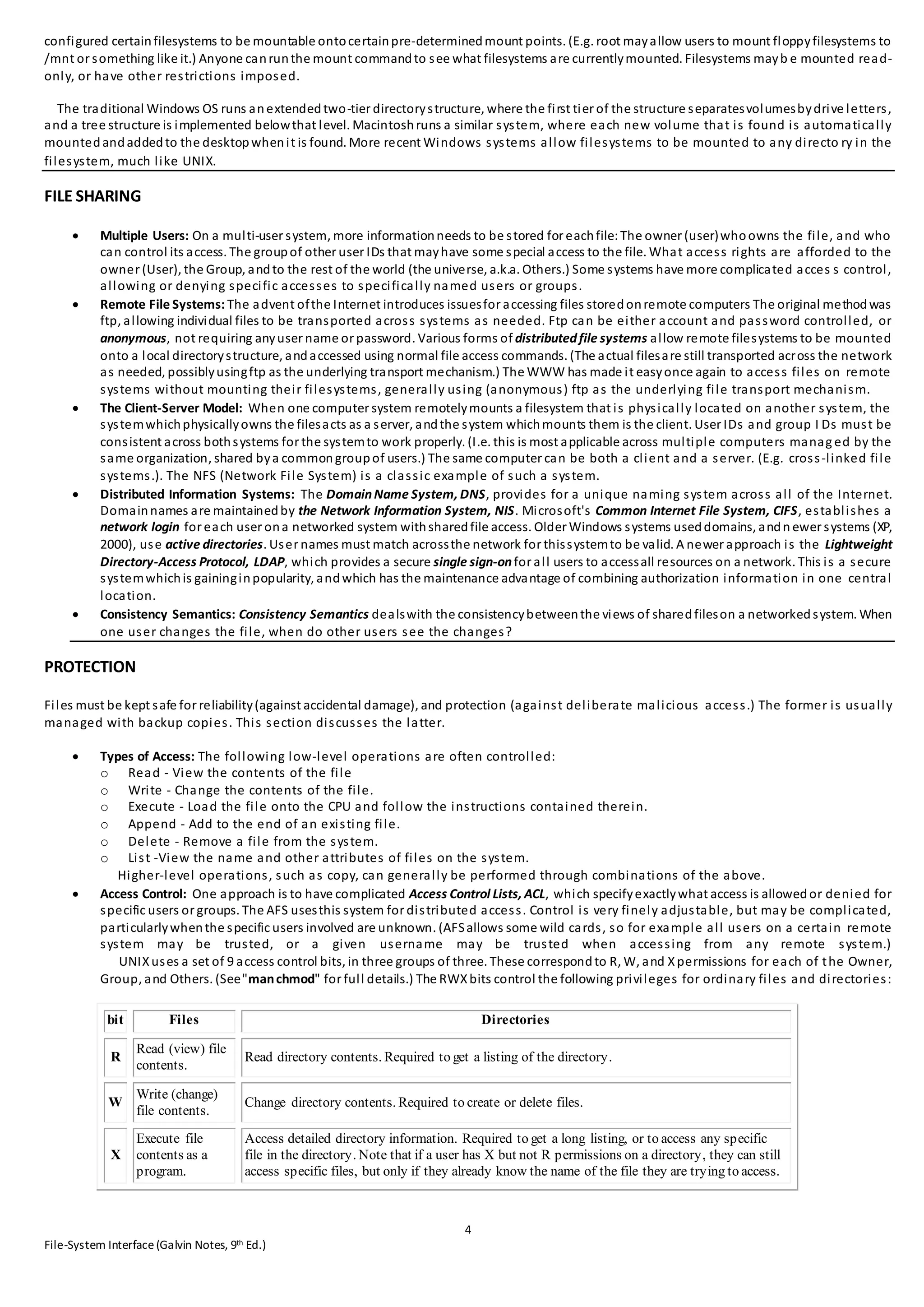
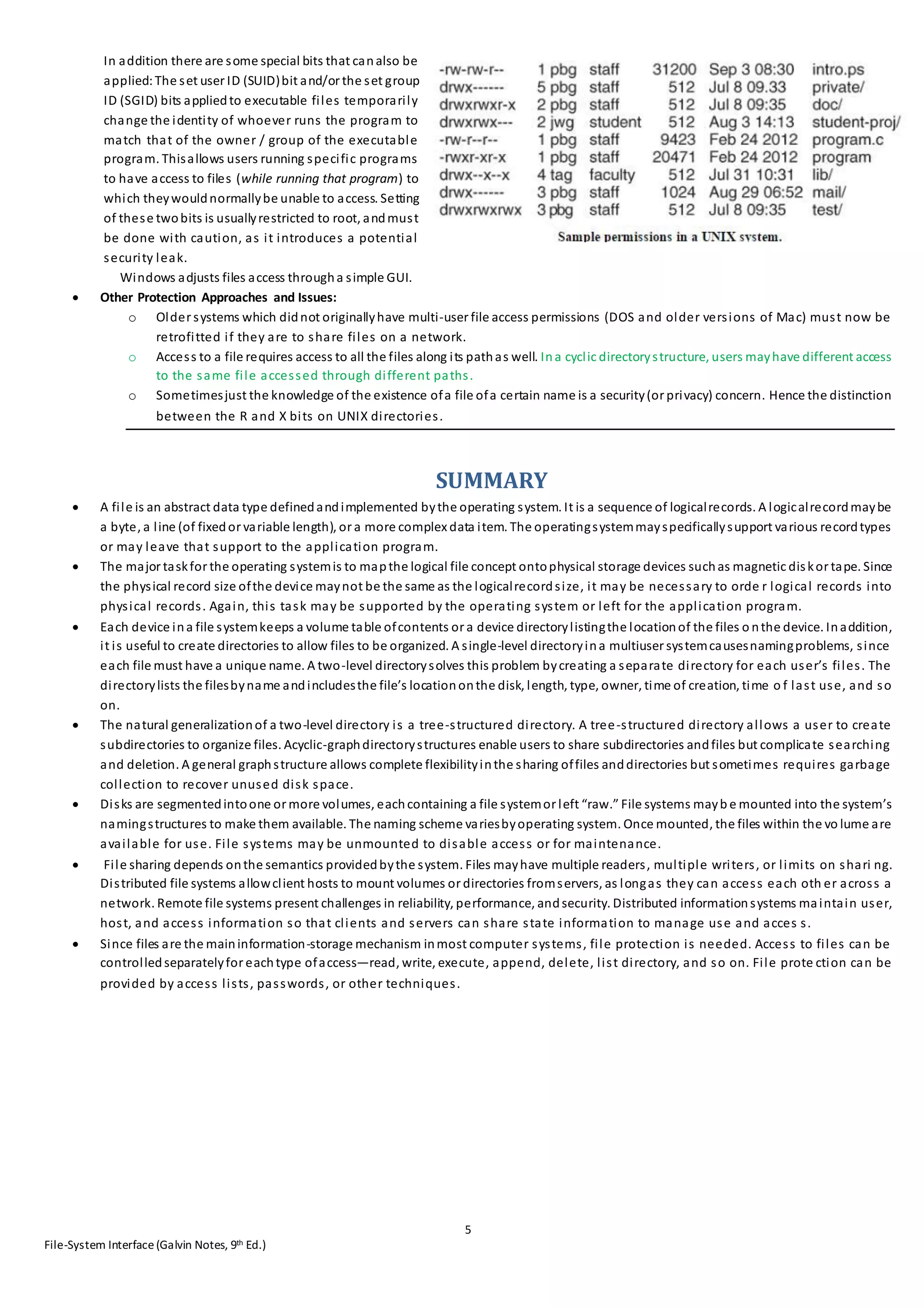
The document discusses key aspects of file systems and file interfaces. It covers file concepts like attributes, operations, and types. It also covers access methods like sequential, direct, and indexed access. It discusses directory structures from single-level to tree-structured directories. Other topics covered include file system mounting, file sharing through multiple users and remote file systems, and protection through access controls and permissions.