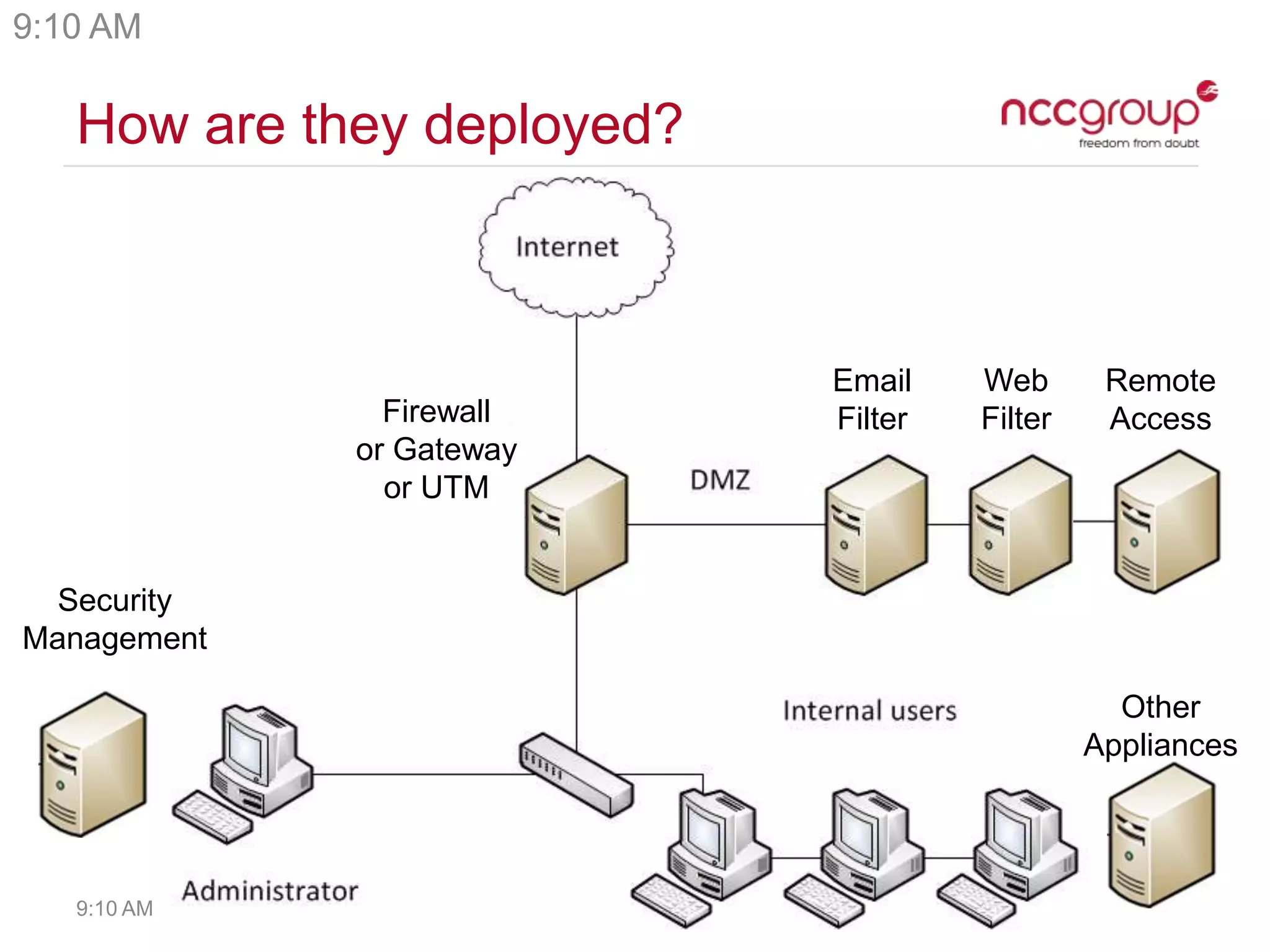
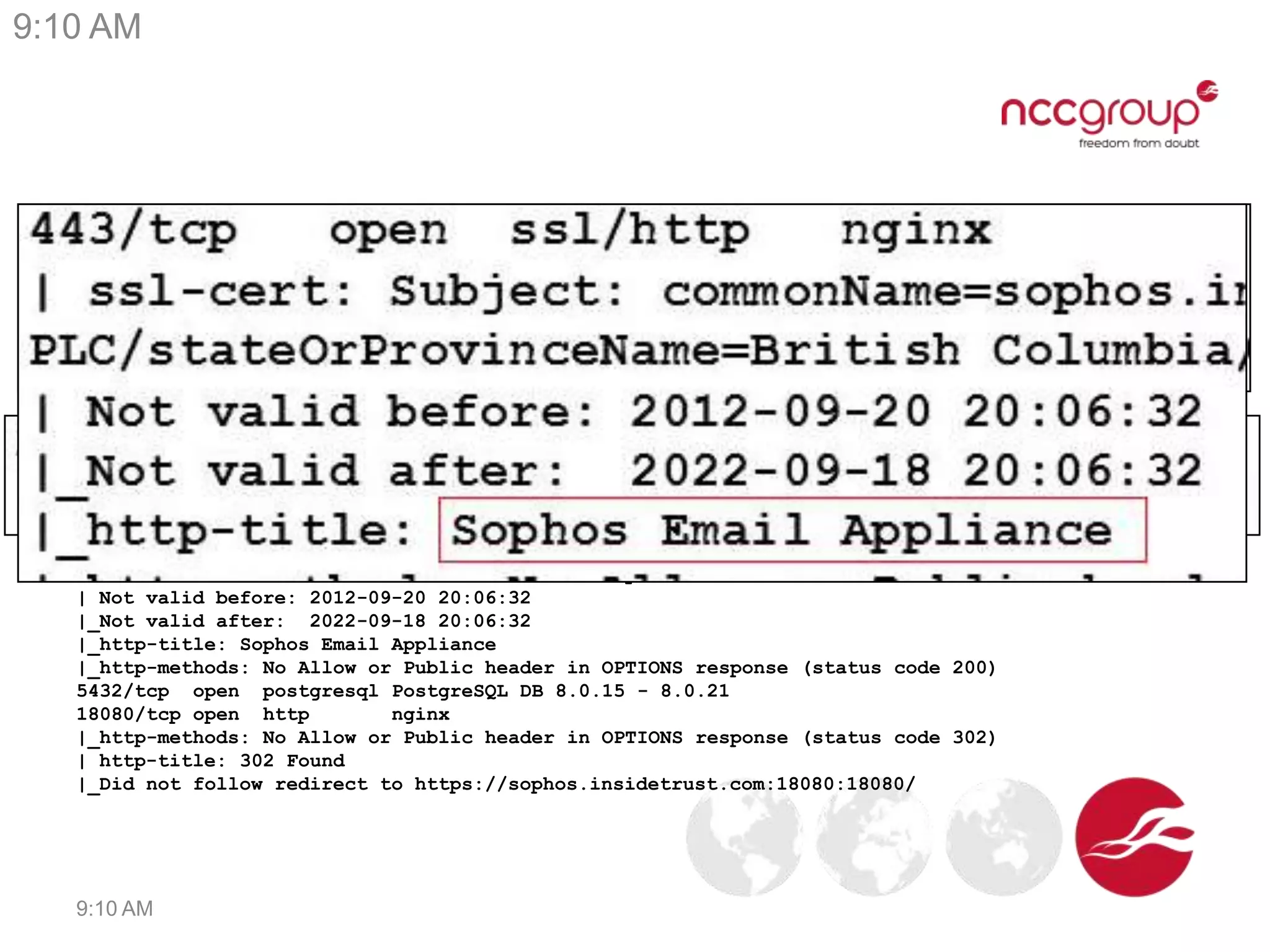
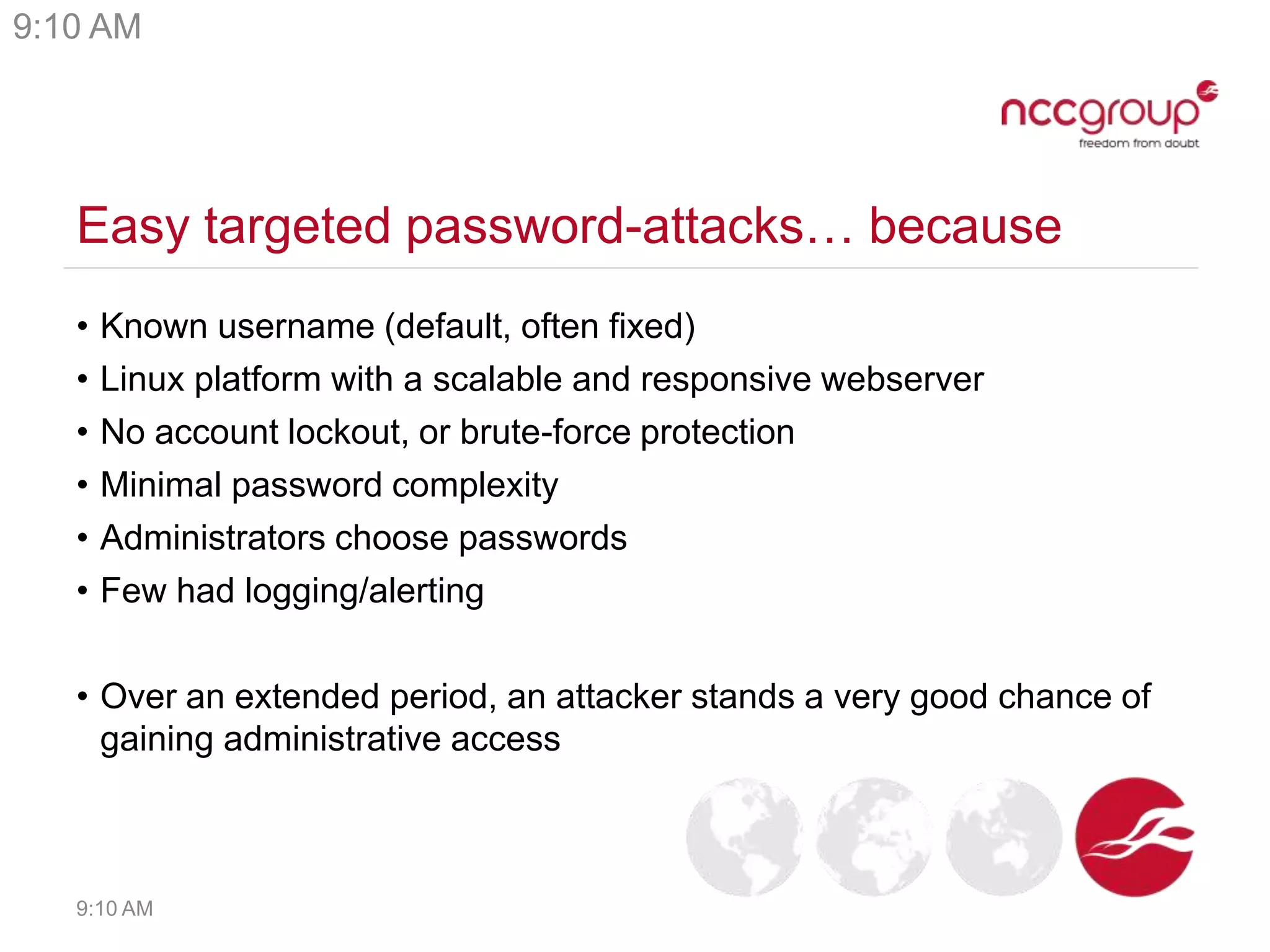
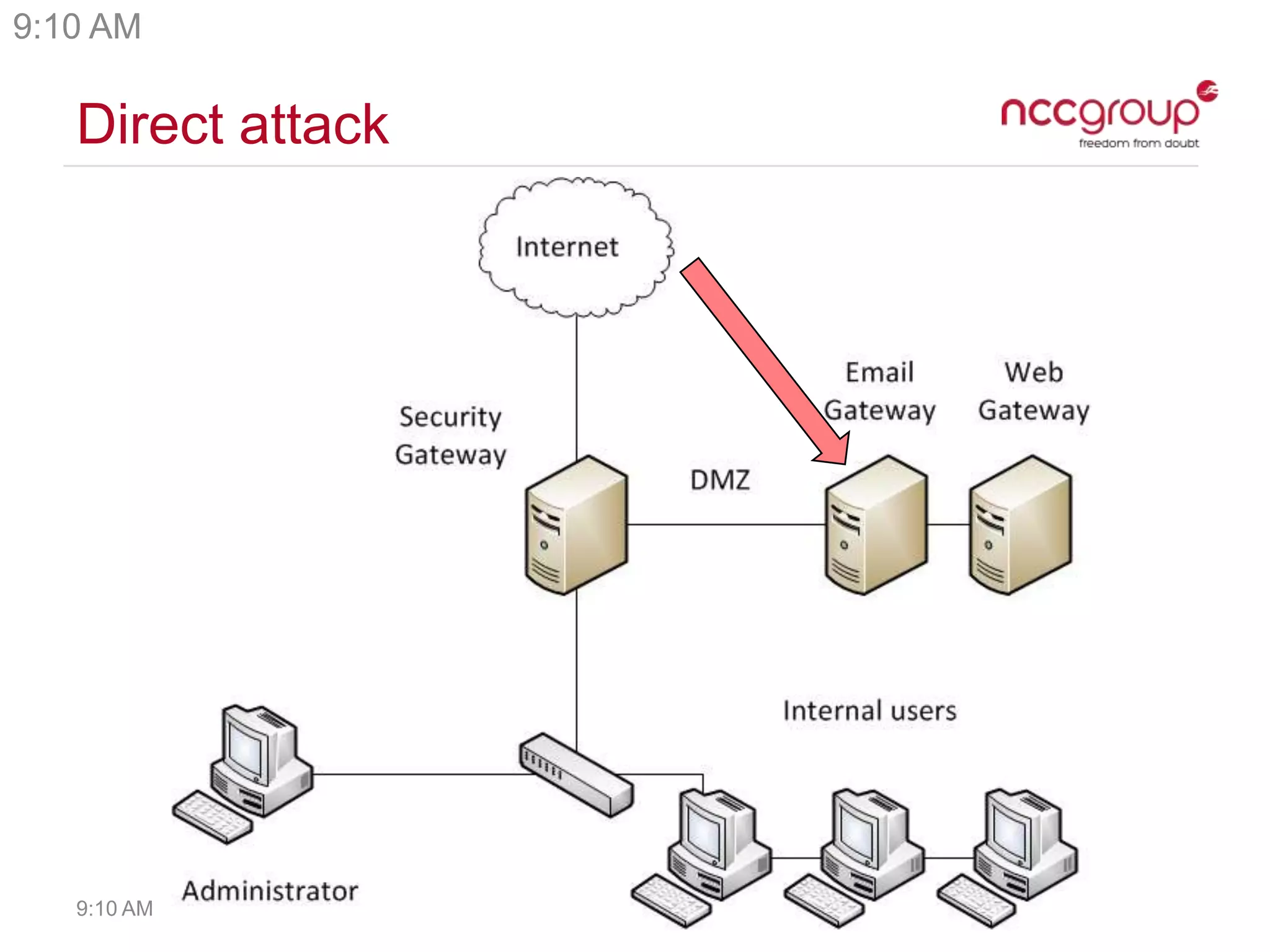
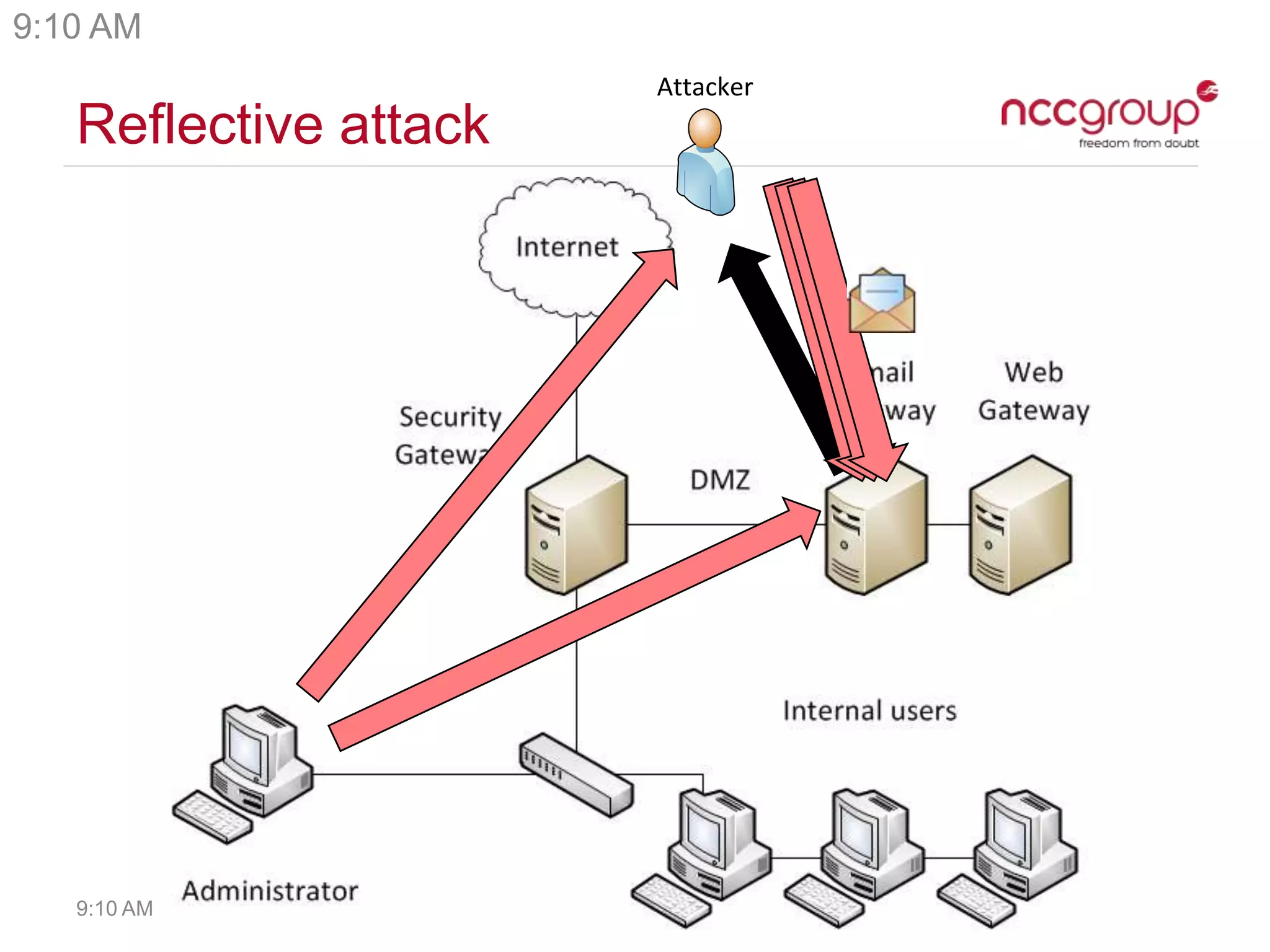
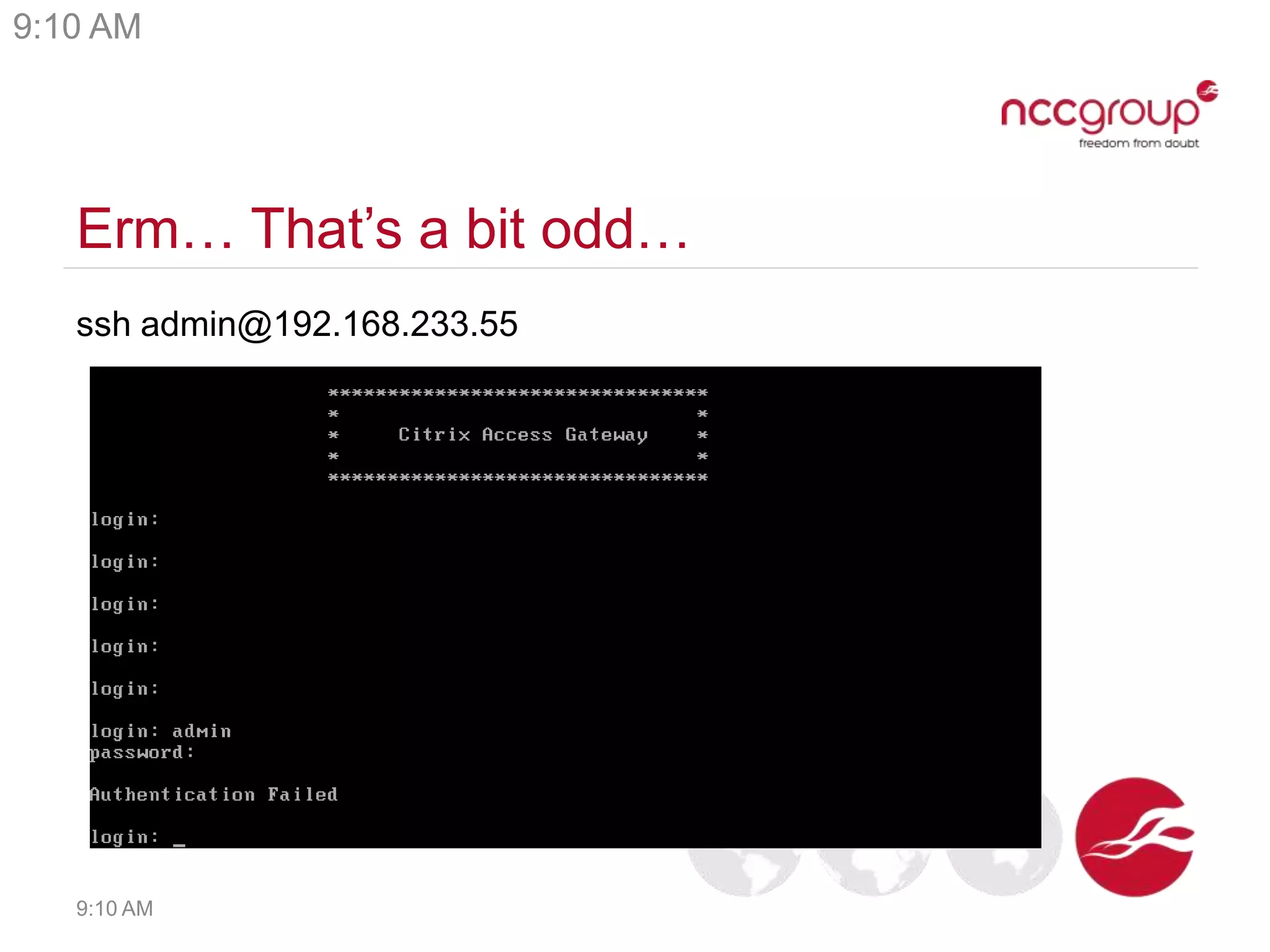
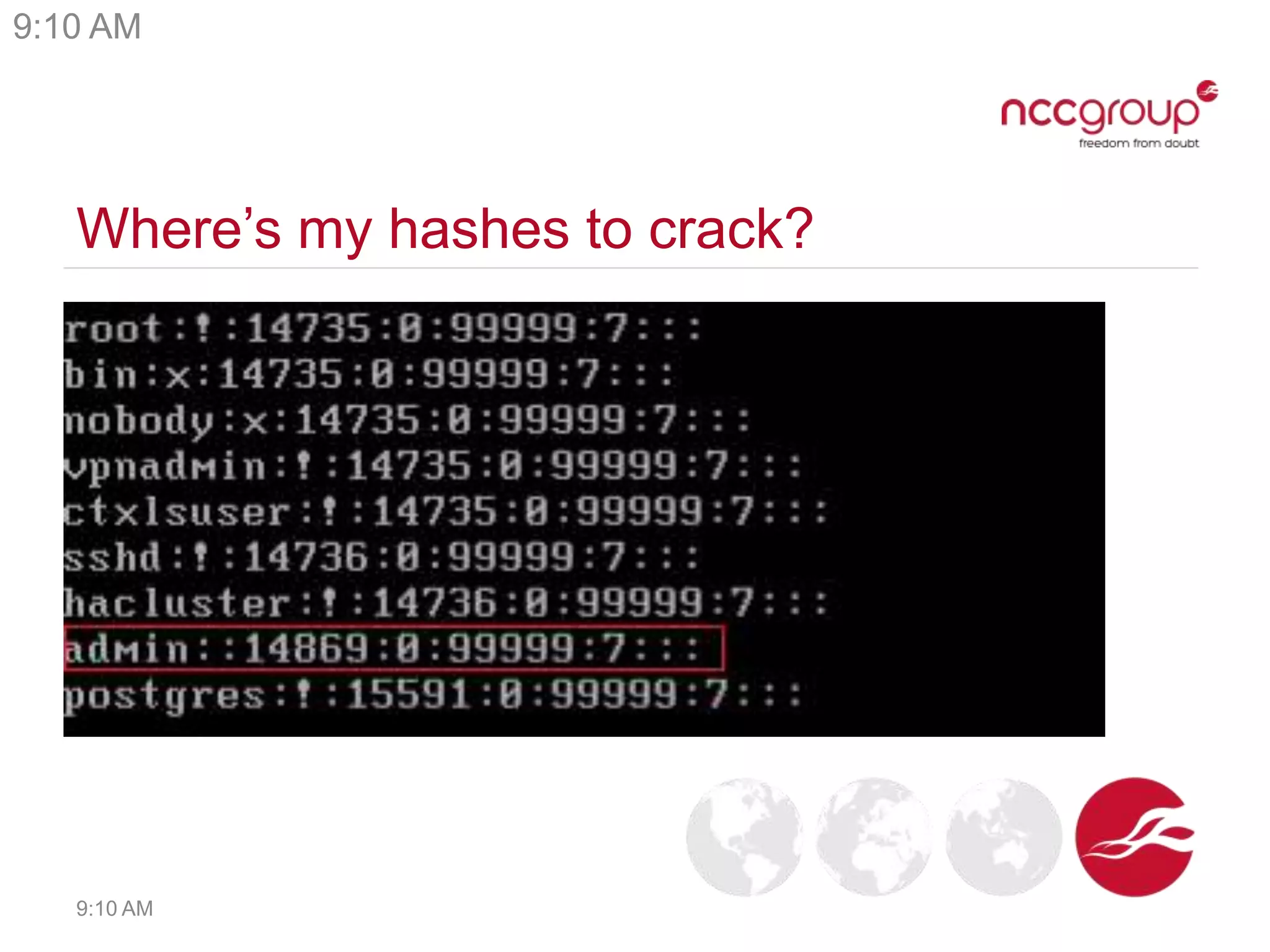
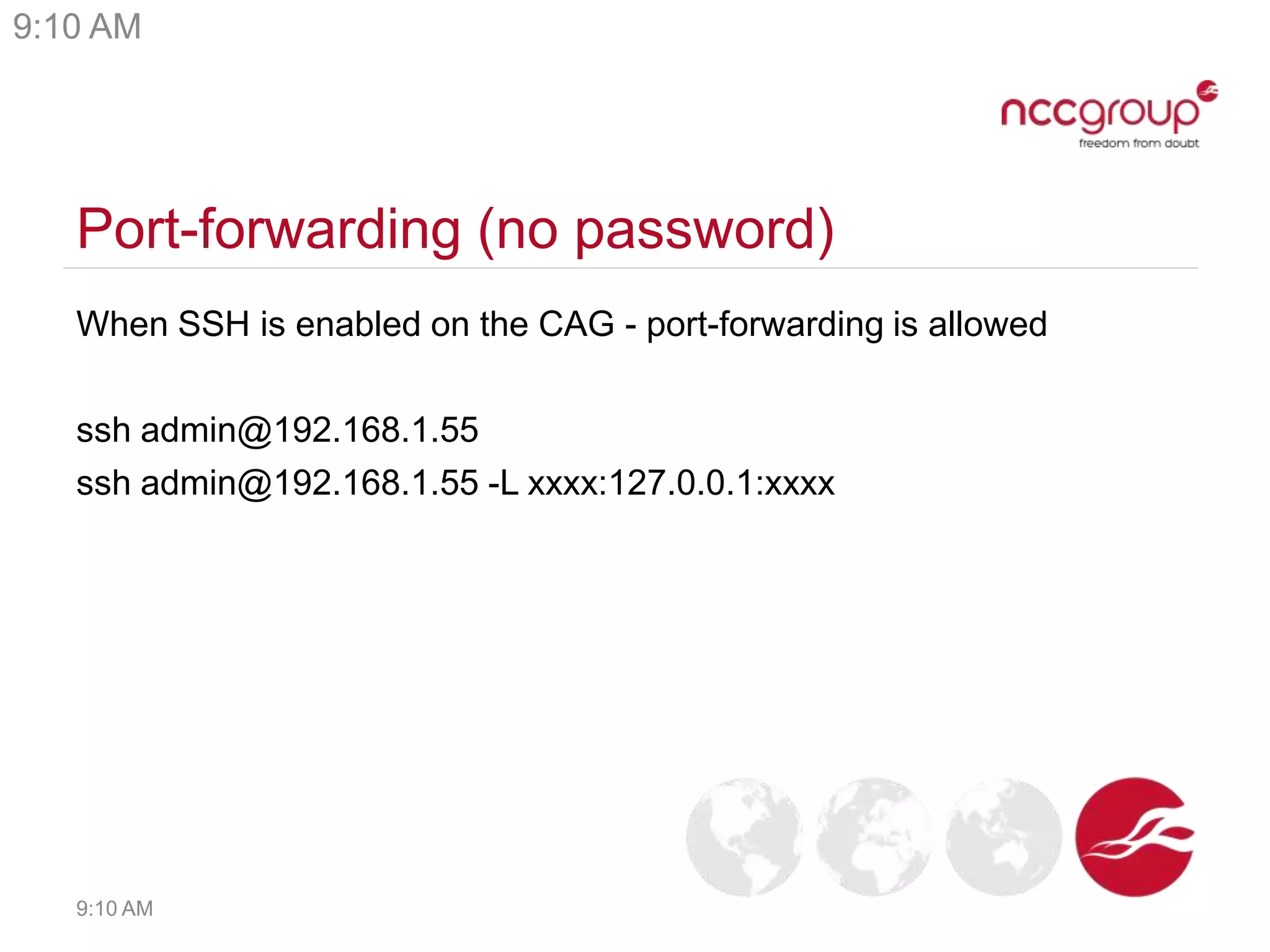
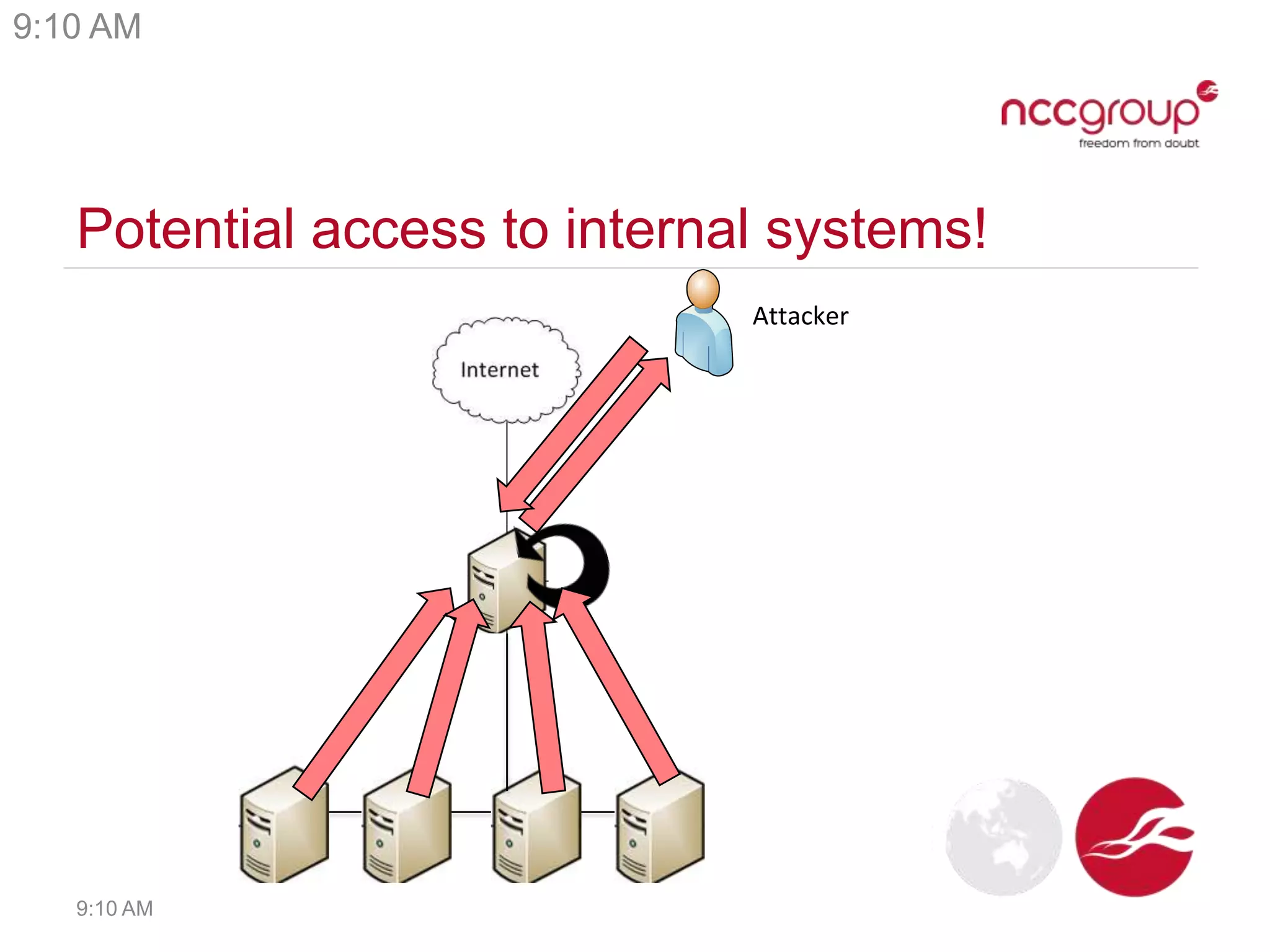
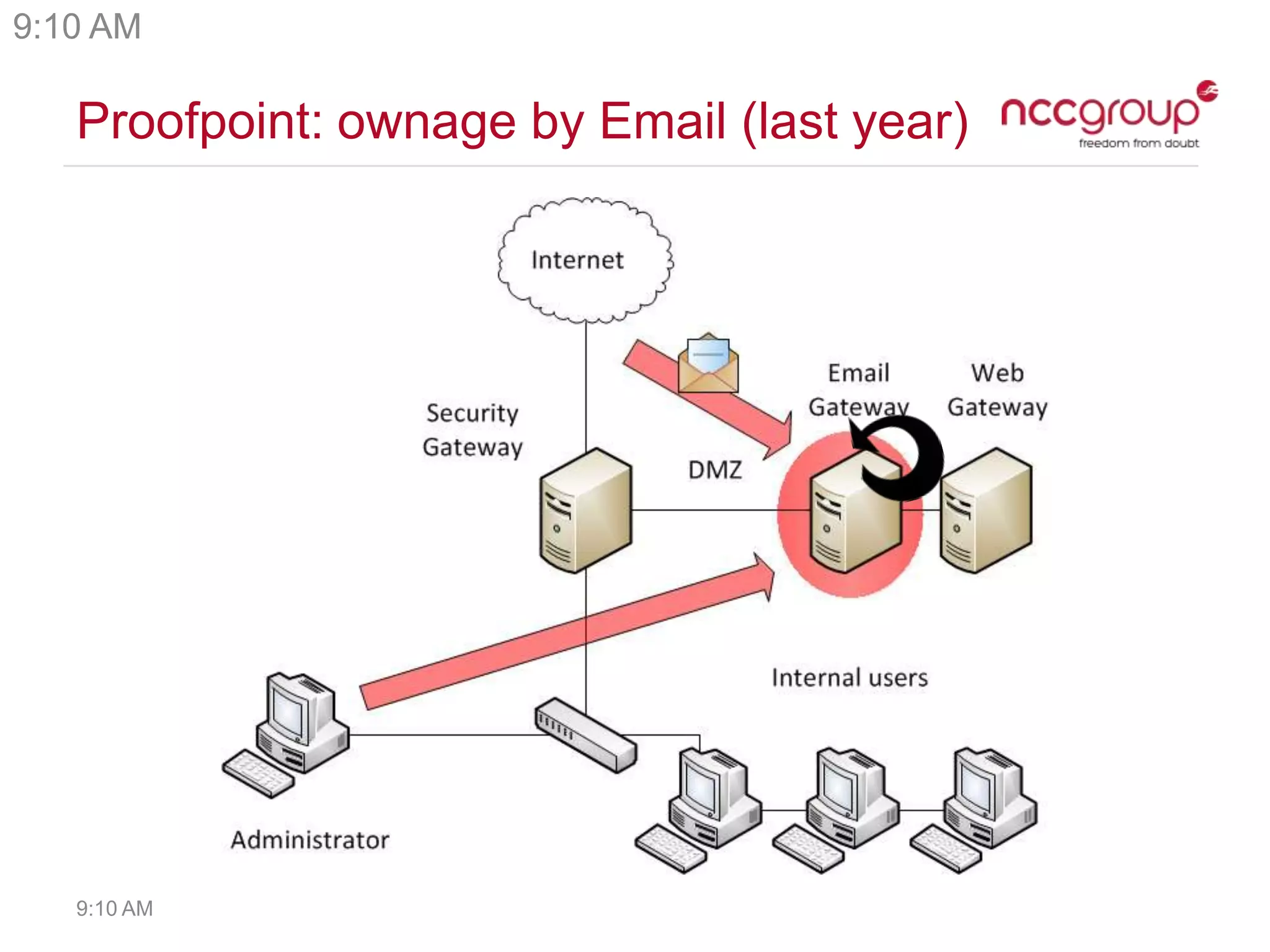
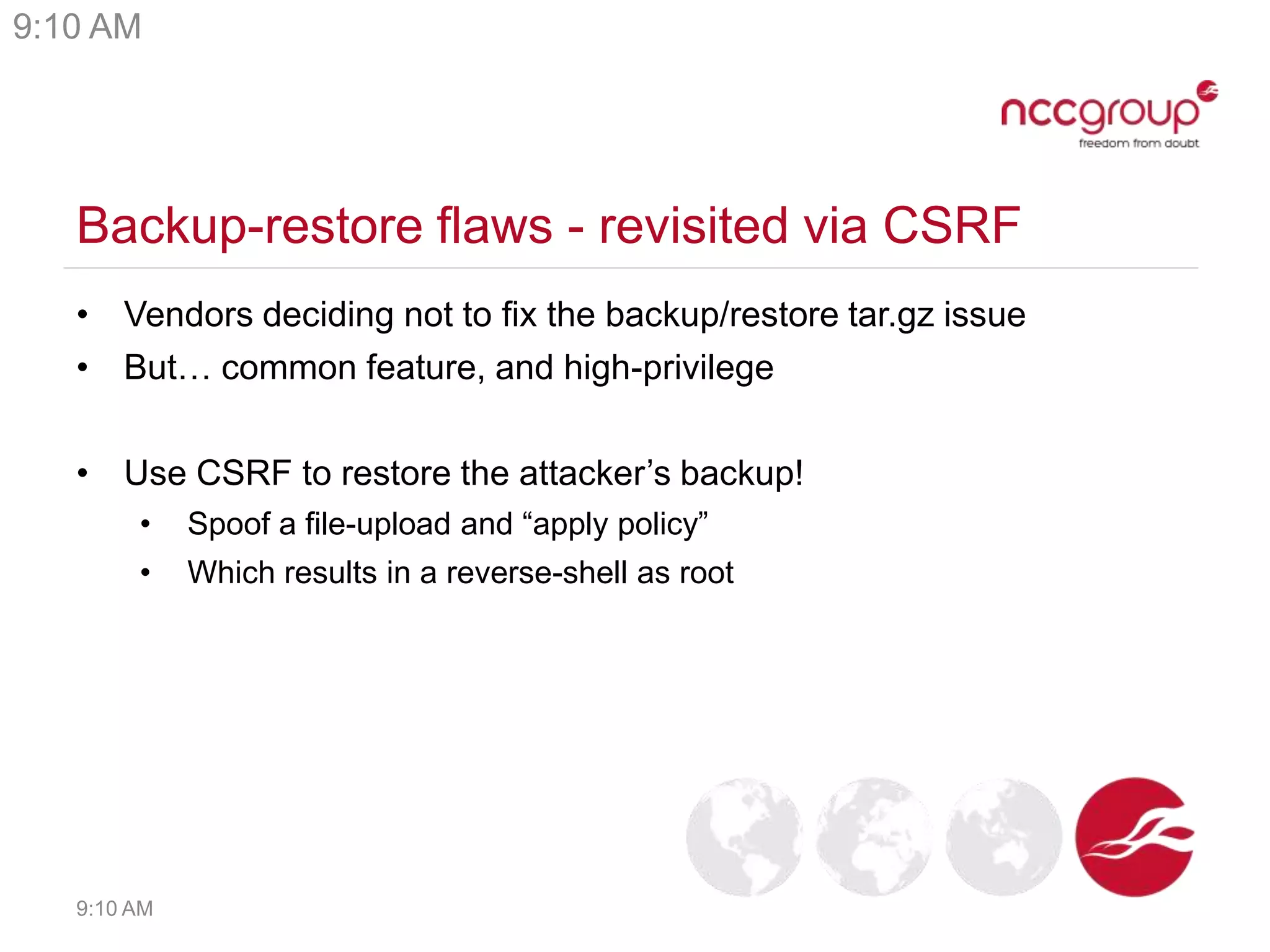
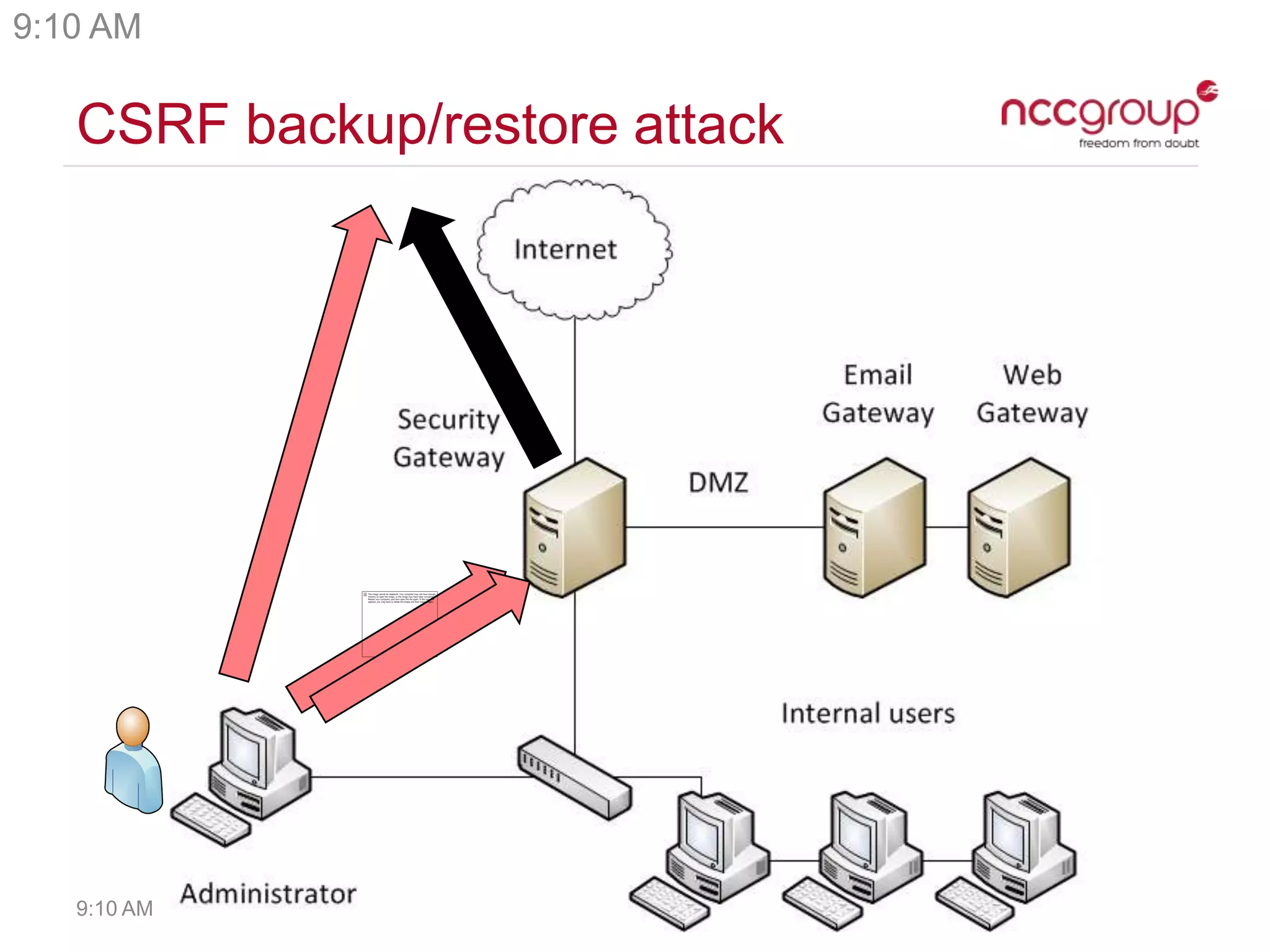
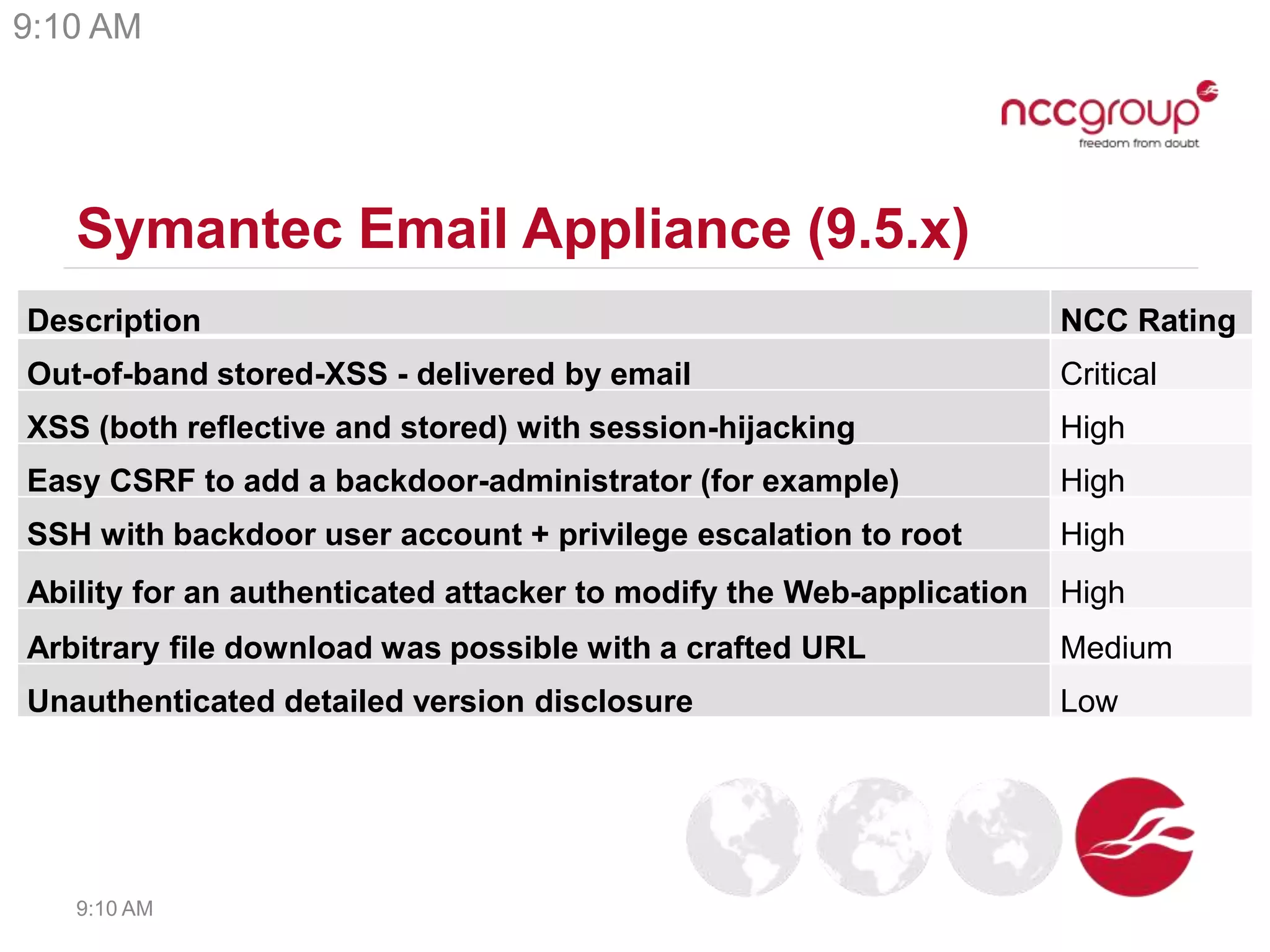
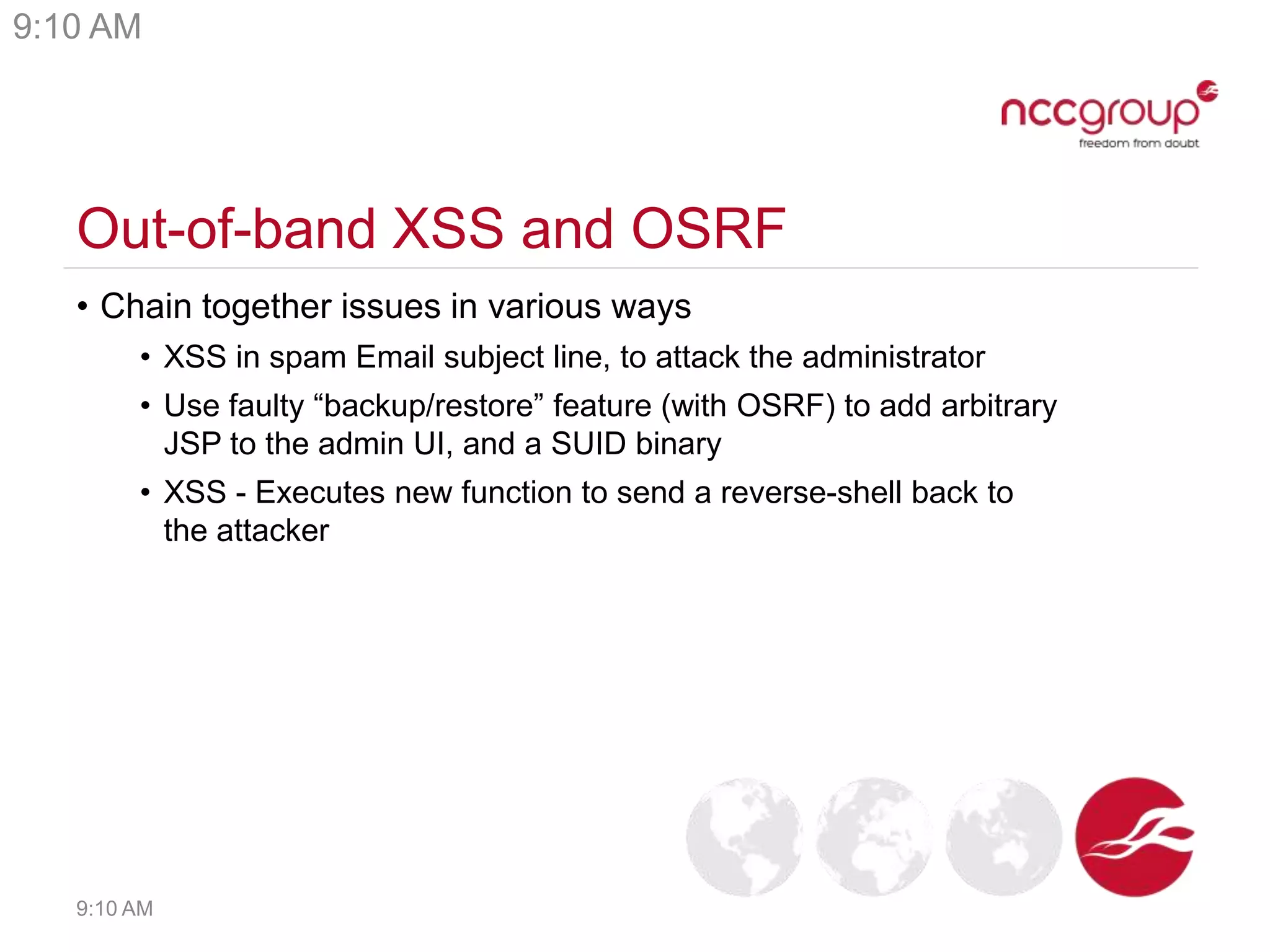
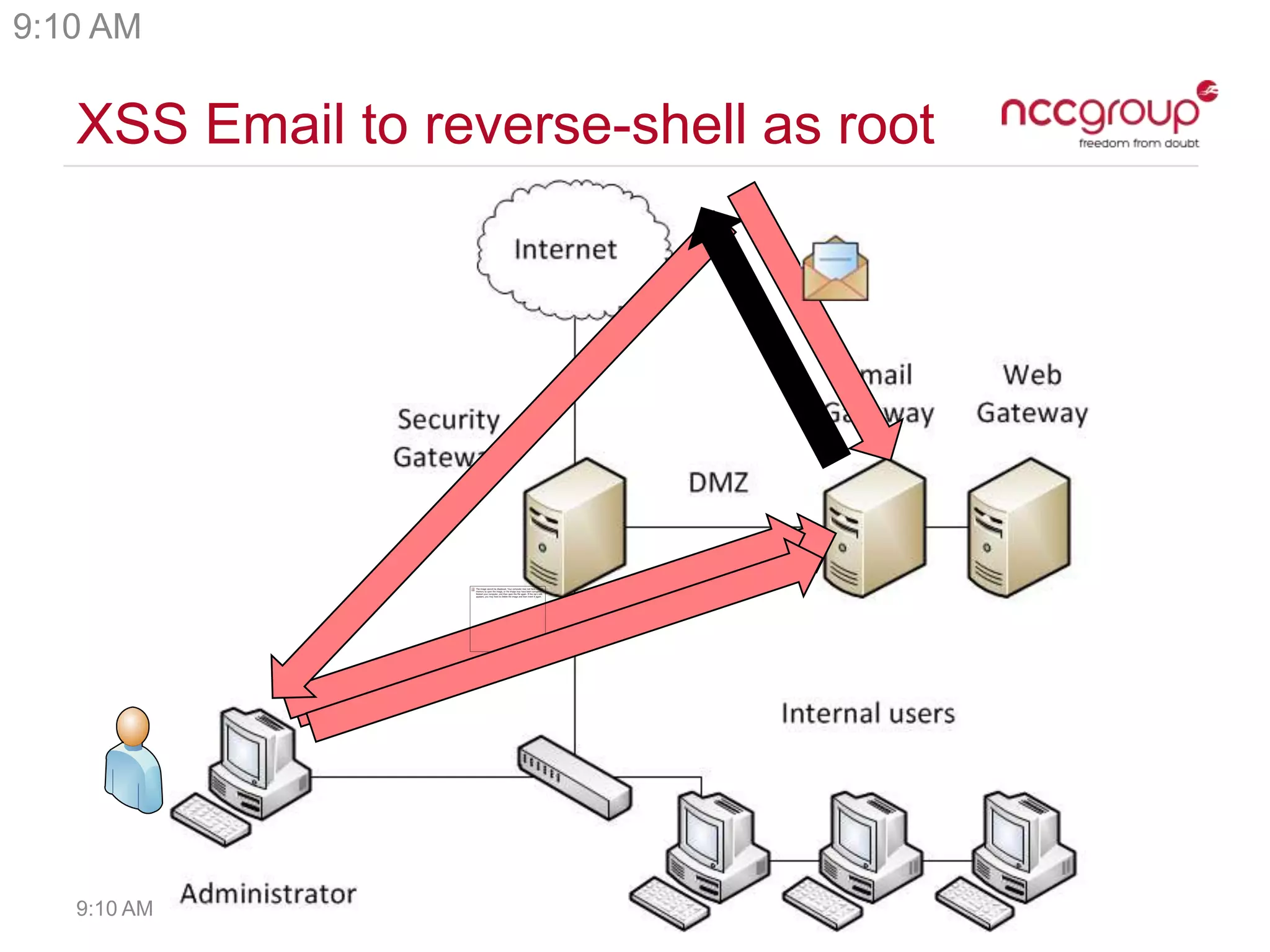
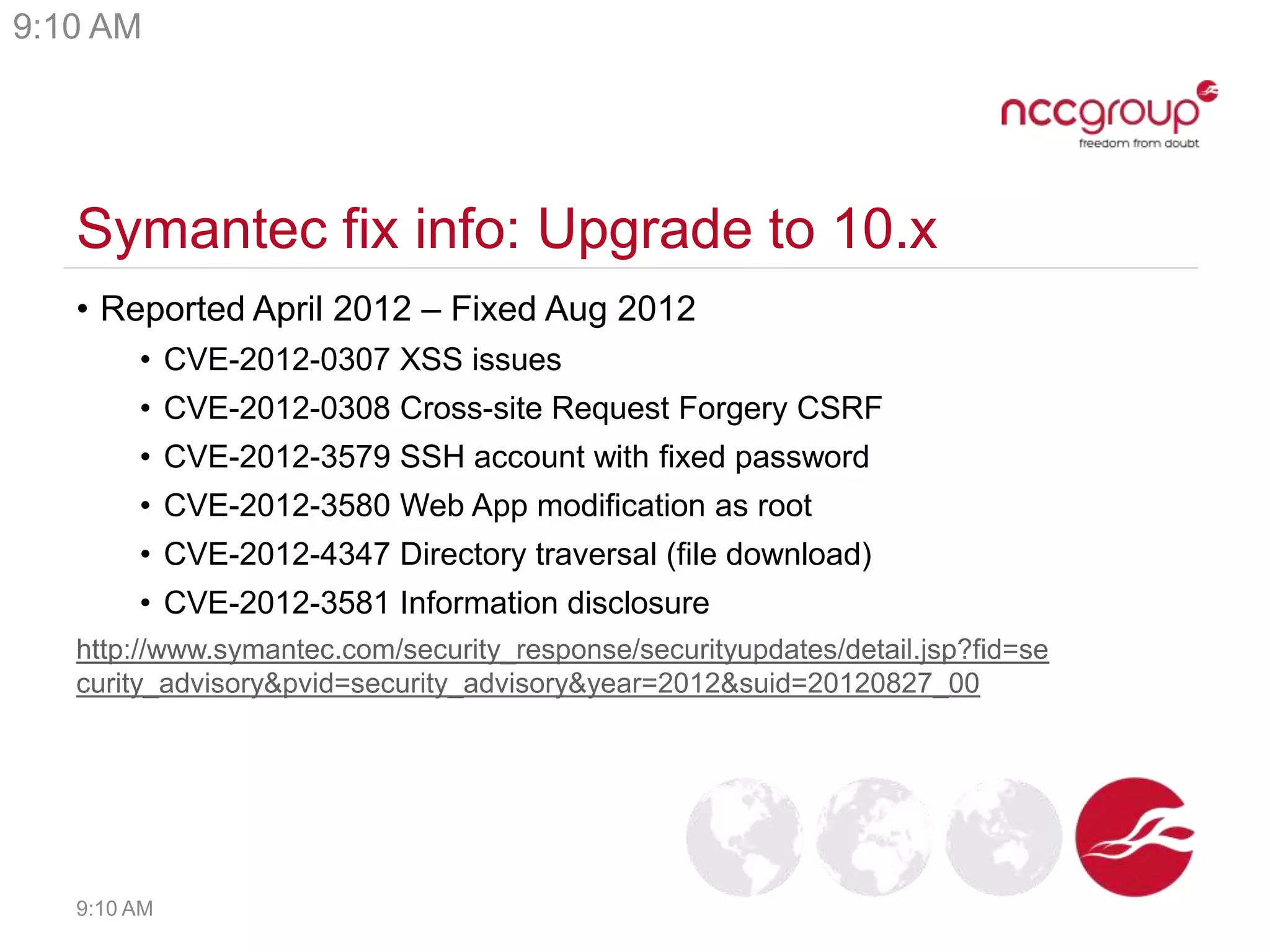
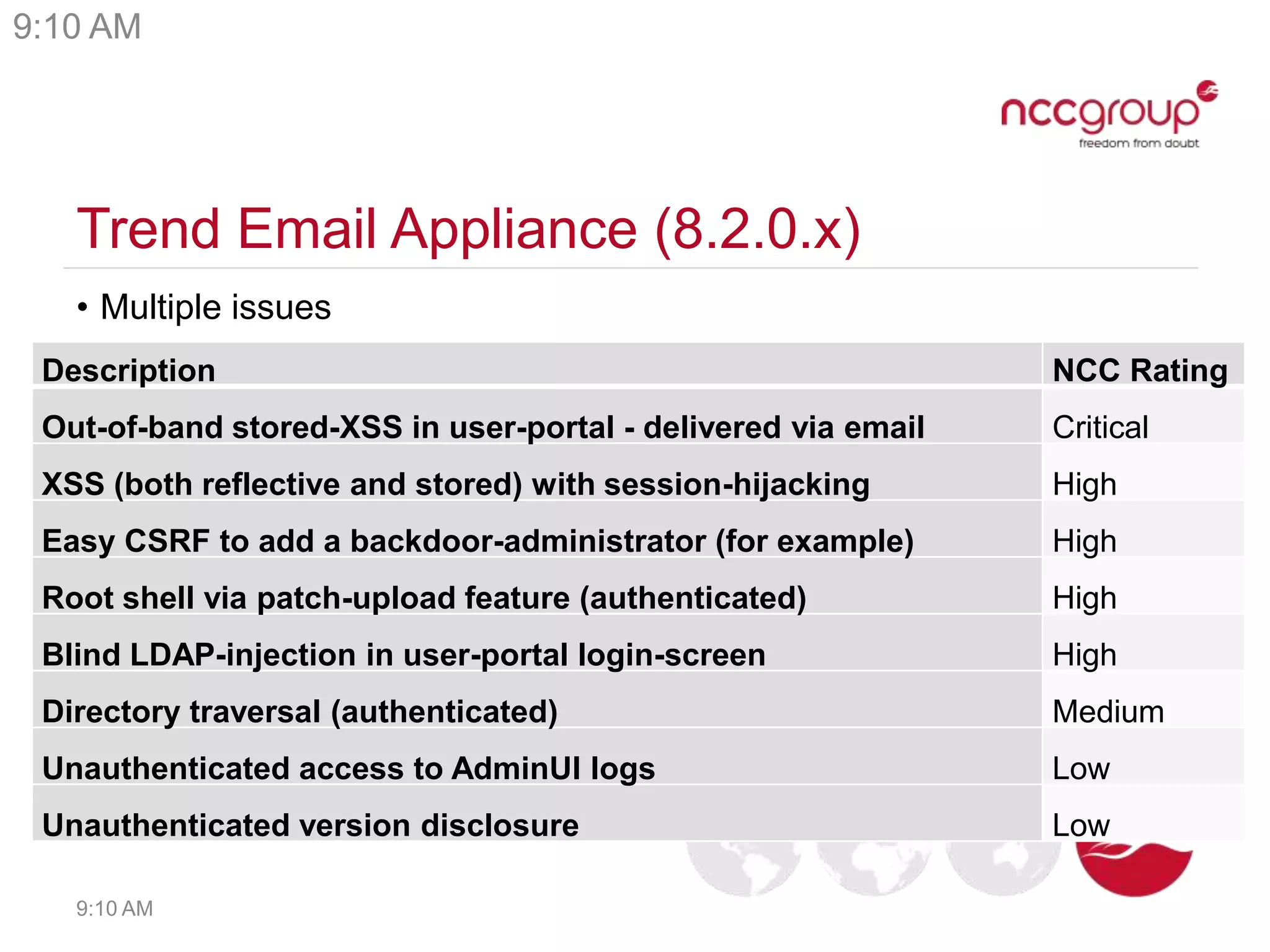
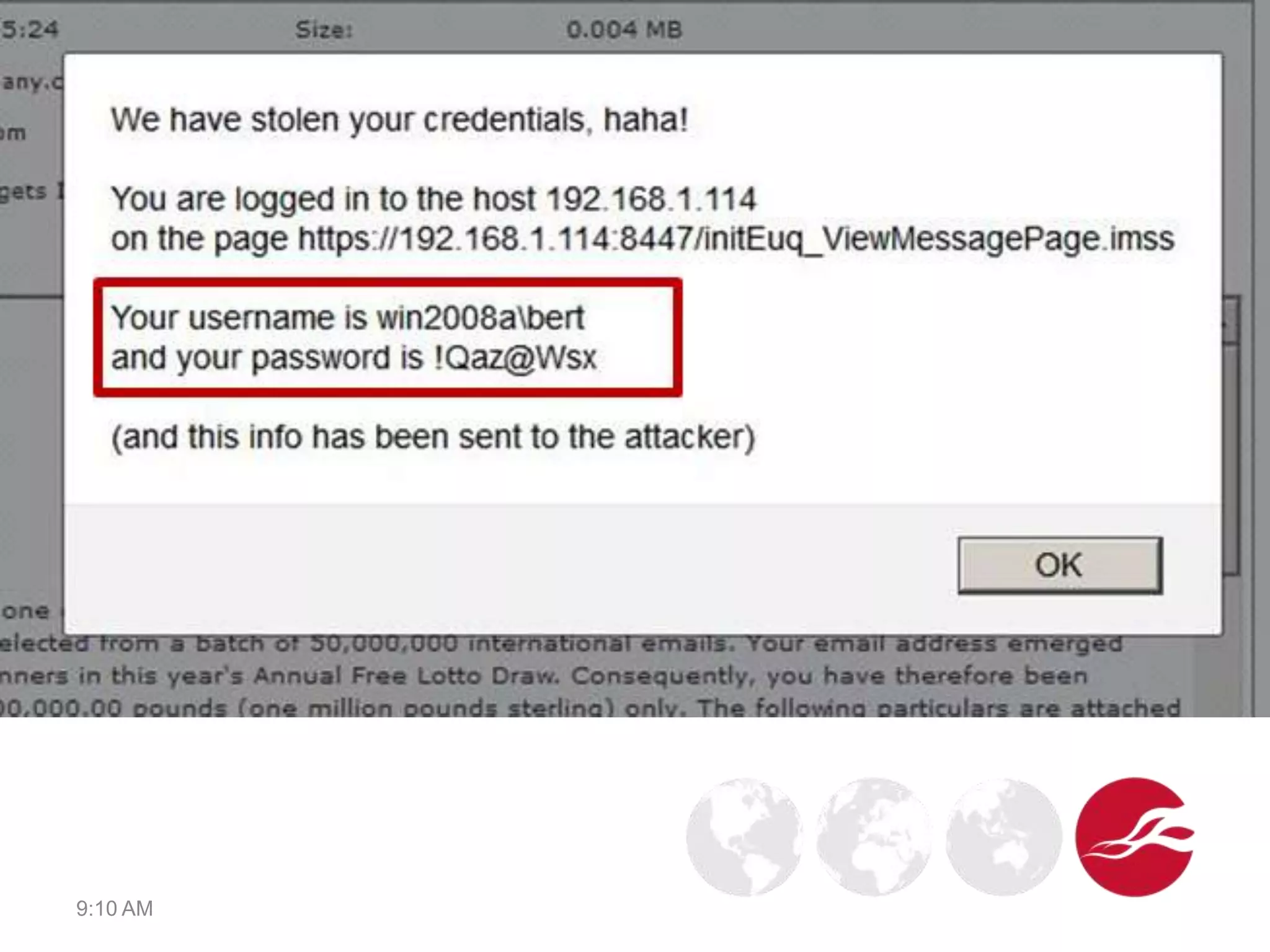
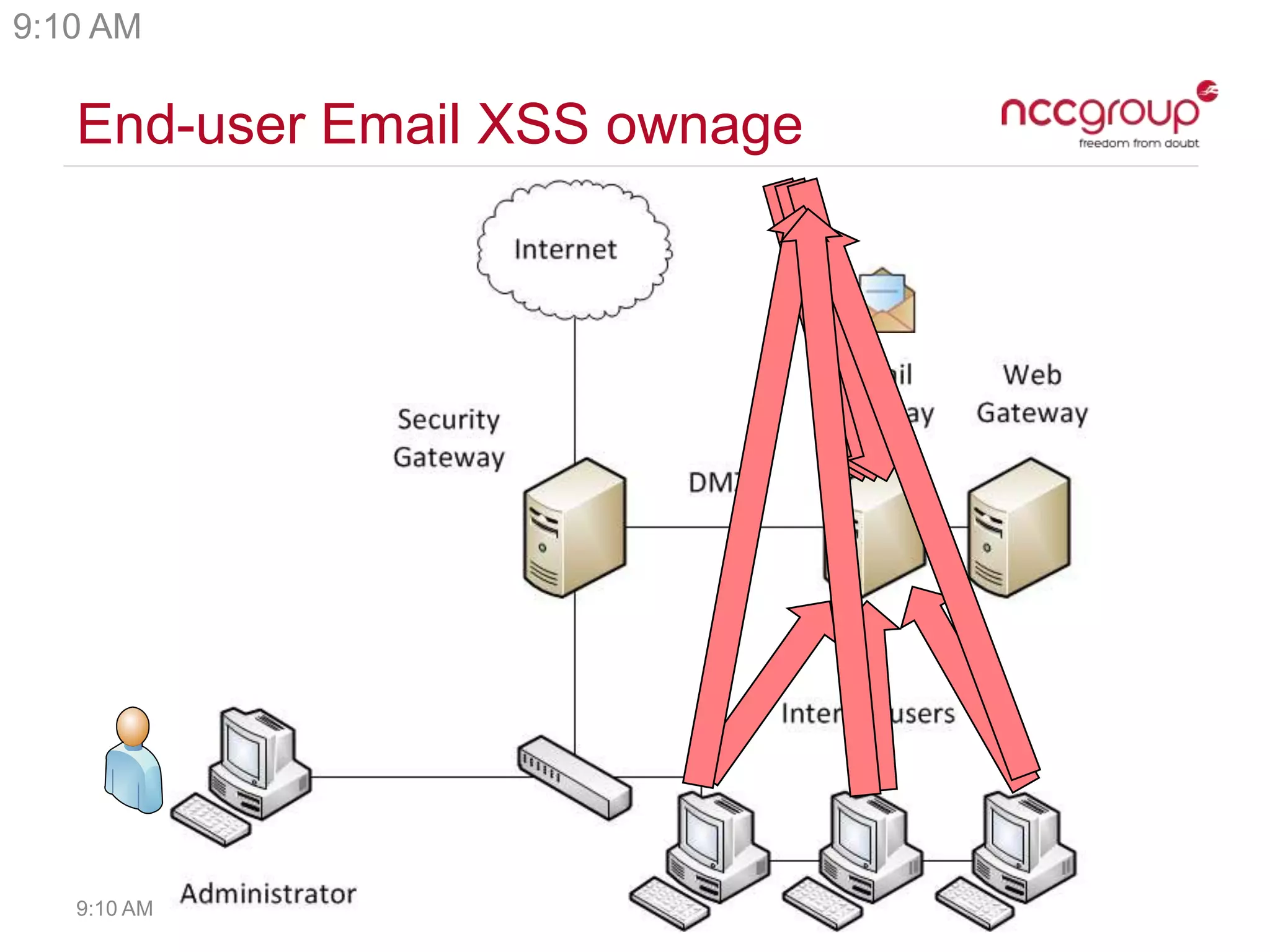
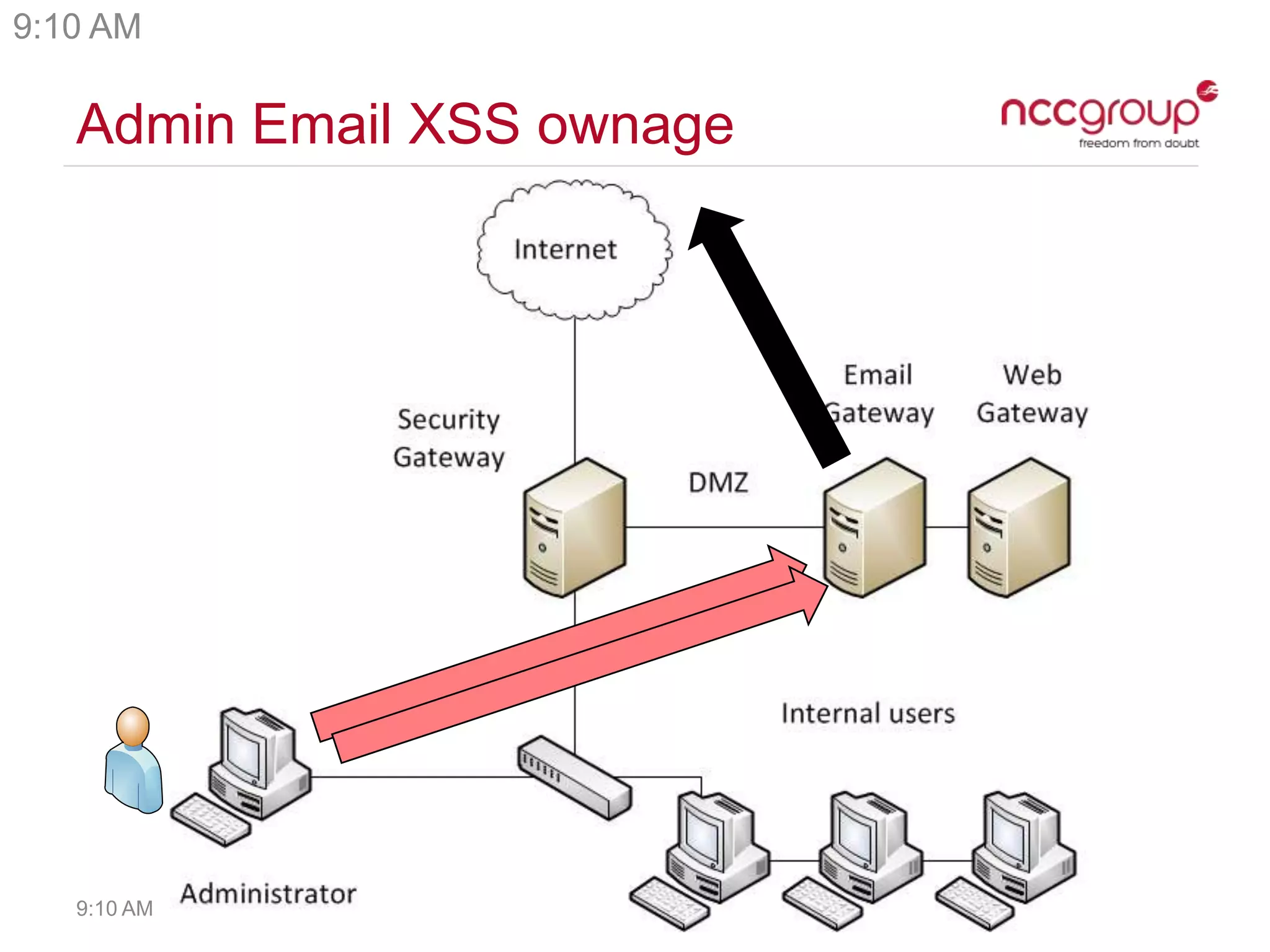
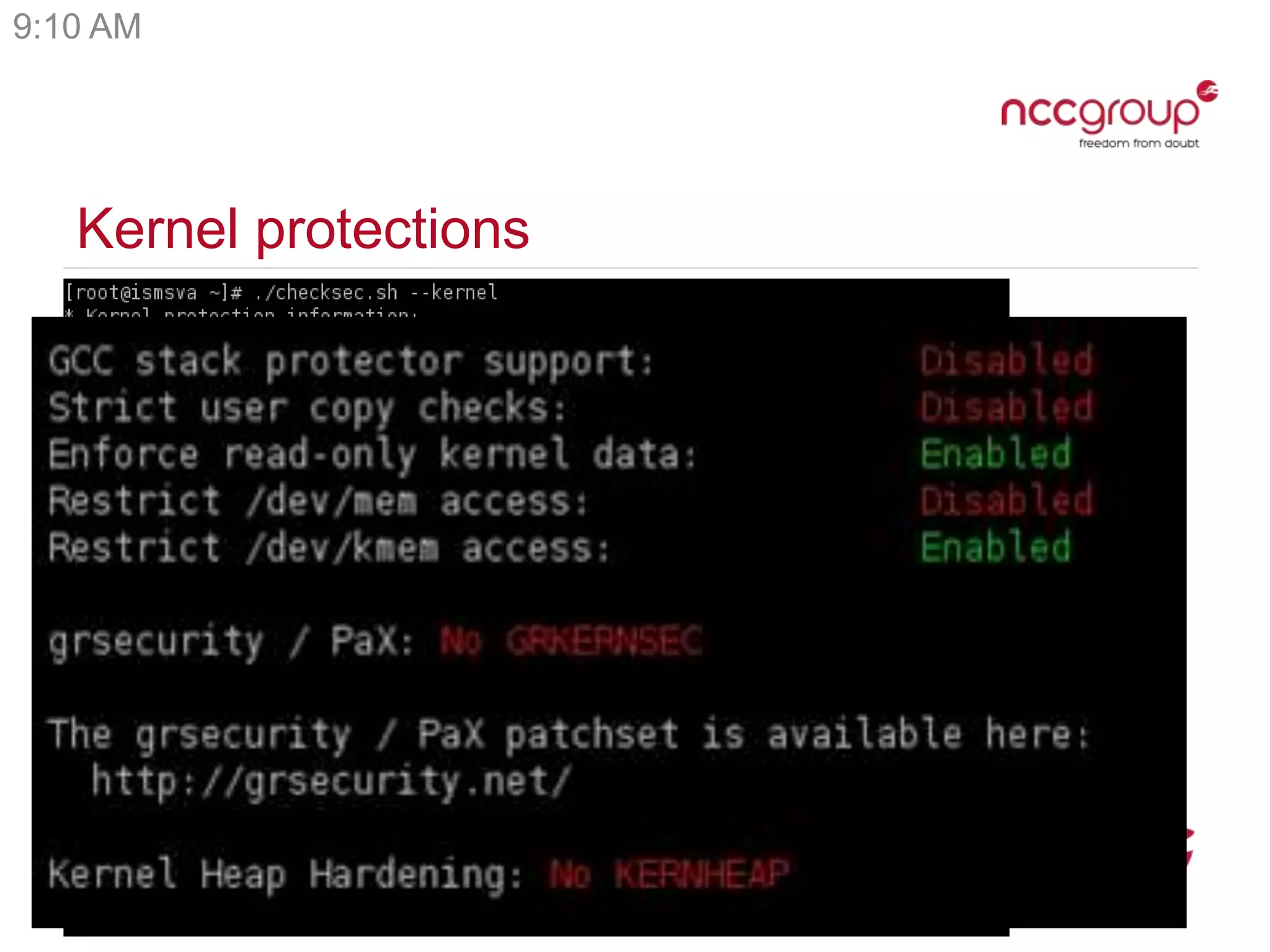
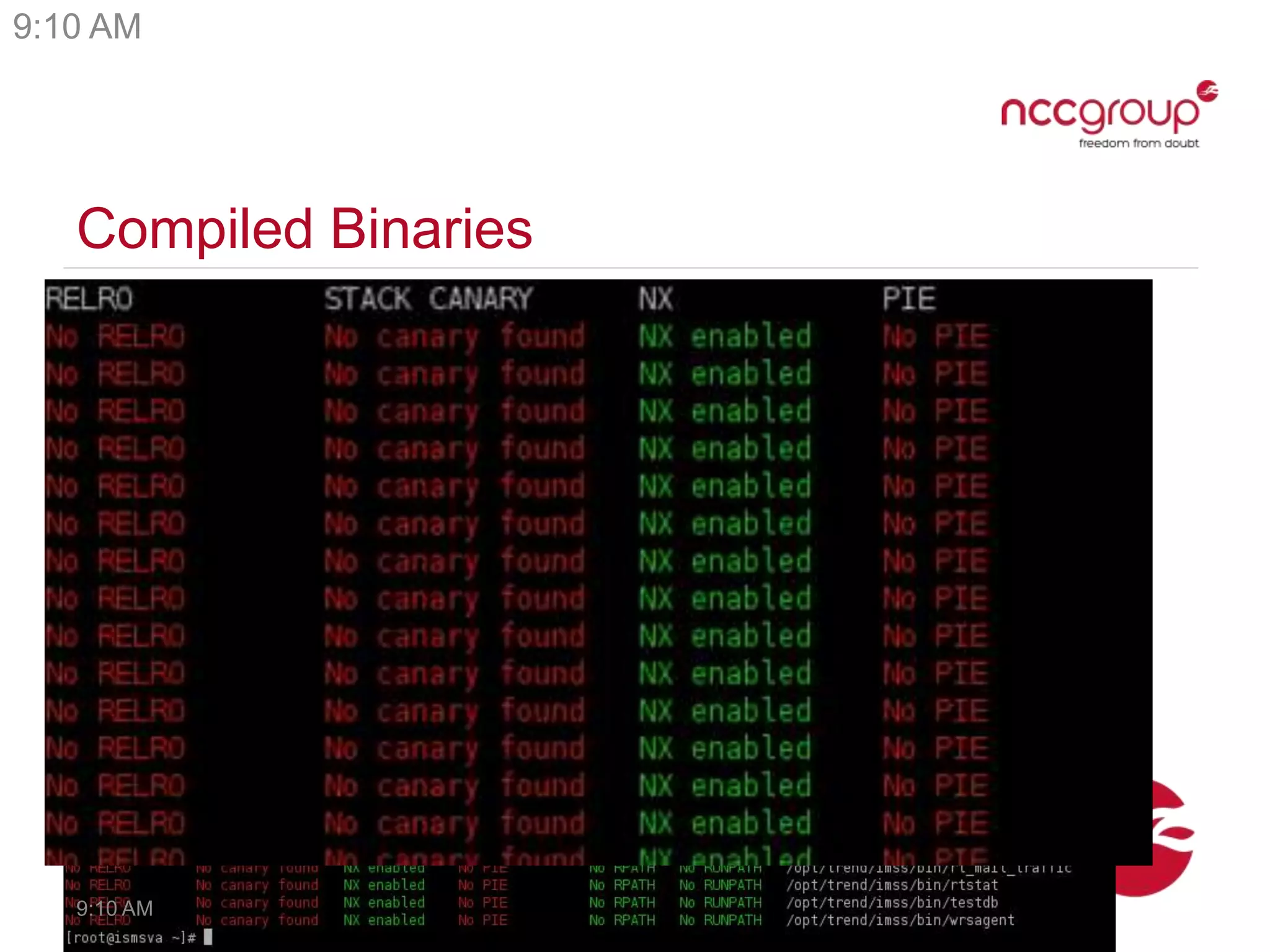
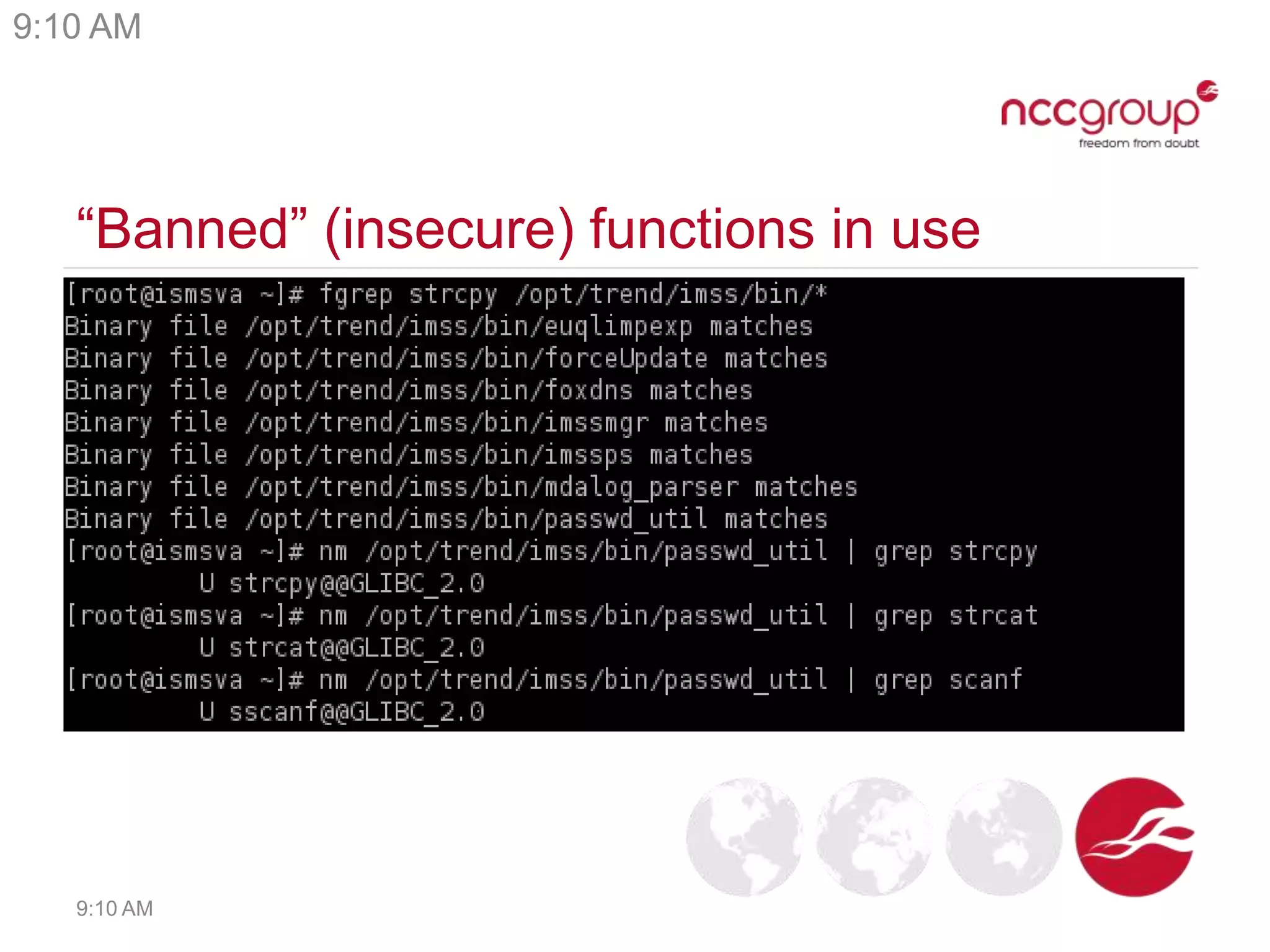
Security appliances like email filters, firewalls, and remote access gateways are often Linux systems with insecure web applications and configurations. The document analyzes vulnerabilities found in many popular security appliances, including easy password attacks, cross-site scripting, command injection, and privilege escalation issues. It describes how these vulnerabilities allow attackers to gain full access to systems and internal networks. Vendors' responses to reported issues varied, with some fixing problems quickly while others provided no fixes. The conclusions encourage vendors to improve software maintenance and security testing of appliances.