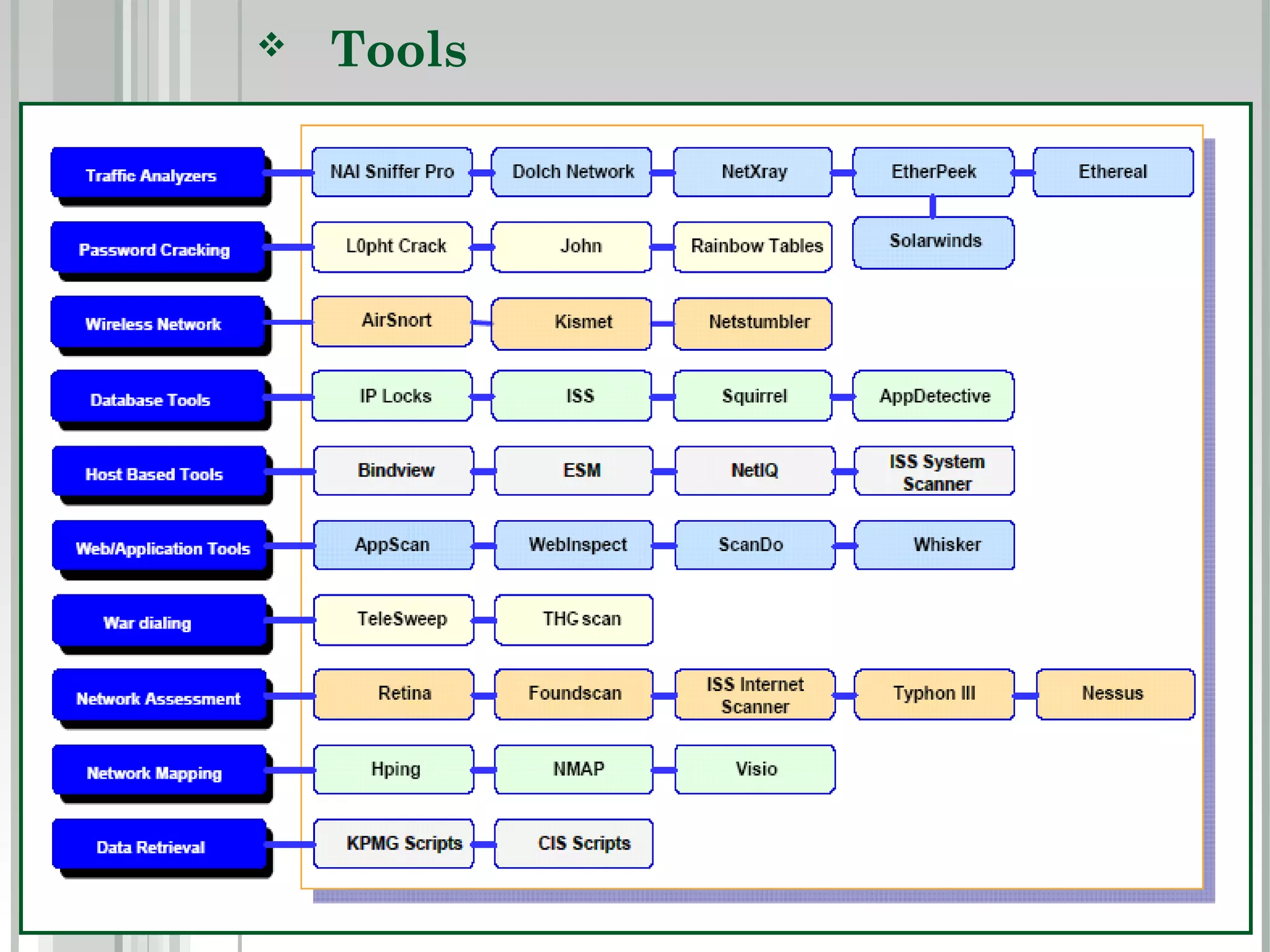
The document outlines the basics of hacking, including types of hackers such as white hat, black hat, and gray hat. It details the process of ethical hacking, which includes steps like signing a contract, footprinting, enumeration, identifying vulnerabilities, and exploiting them. It also lists tools and techniques used in each step of the ethical hacking process.