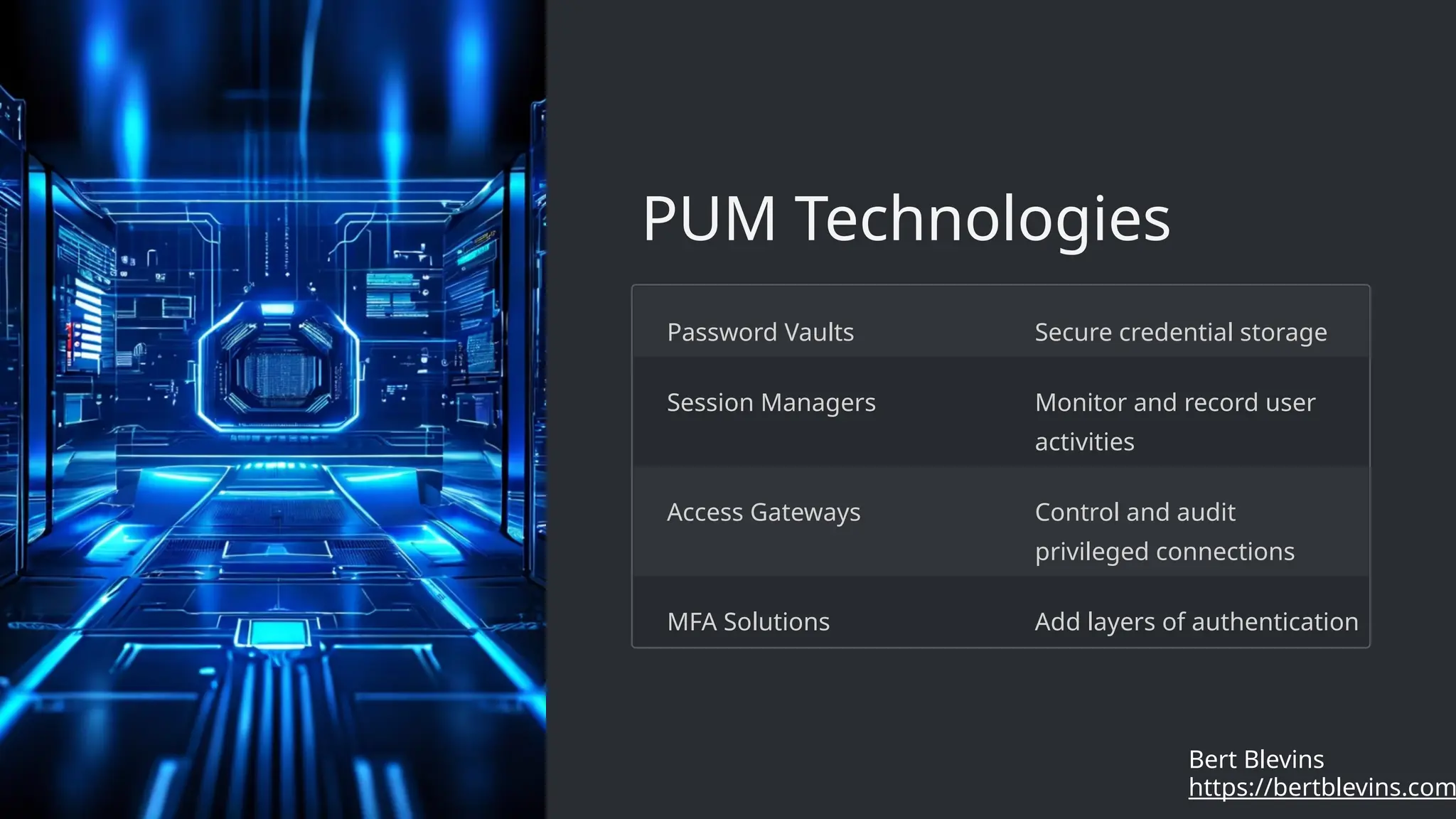
The document outlines the principles and practices of privileged user management (PUM), emphasizing least privilege access, role-based access control, and secure password management. It discusses the benefits of PUM, including enhanced security and compliance, while addressing challenges such as user resistance and evolving cybersecurity threats. Future trends include AI-driven analytics and blockchain integration to strengthen privileged access management.