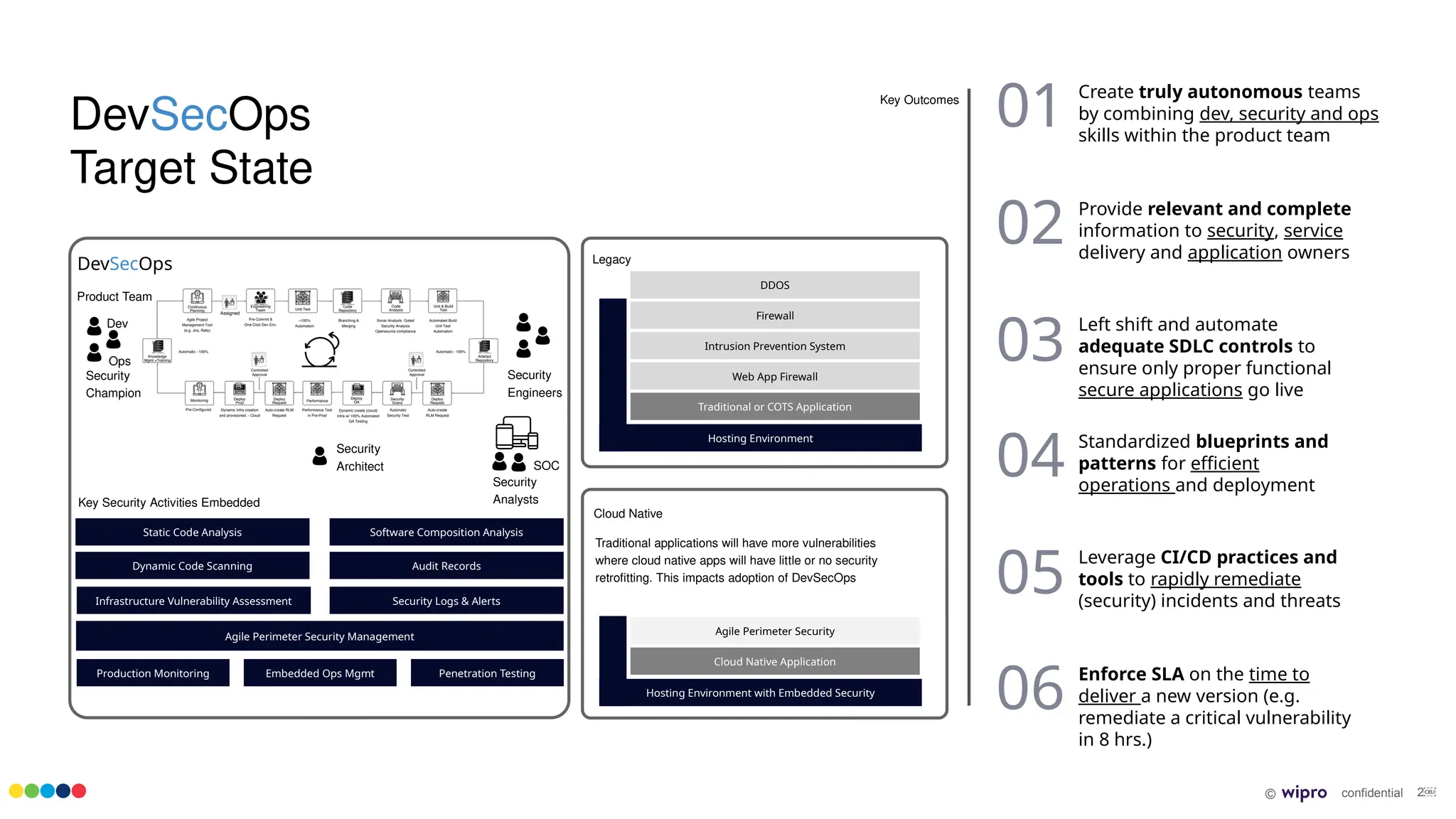
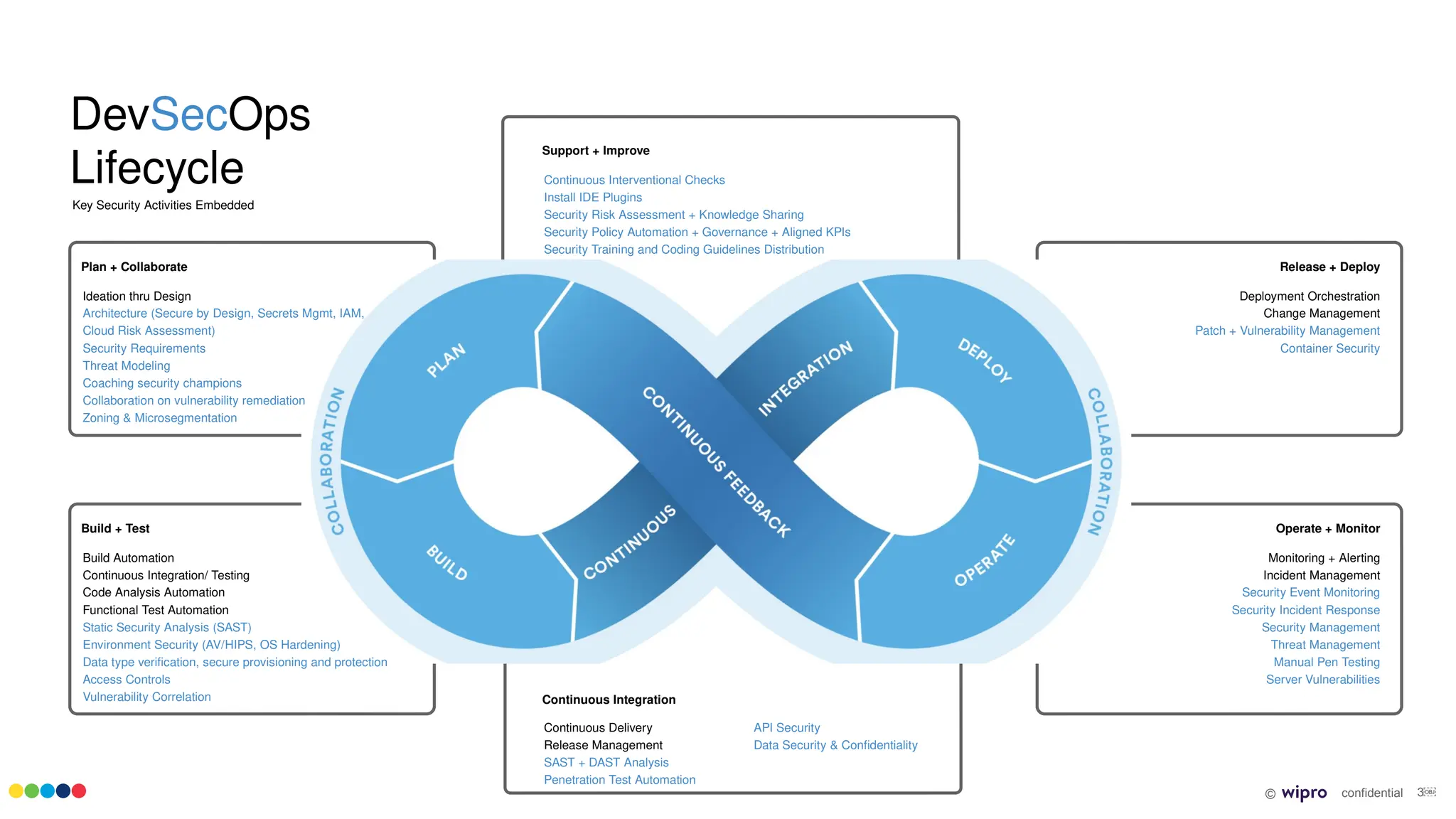
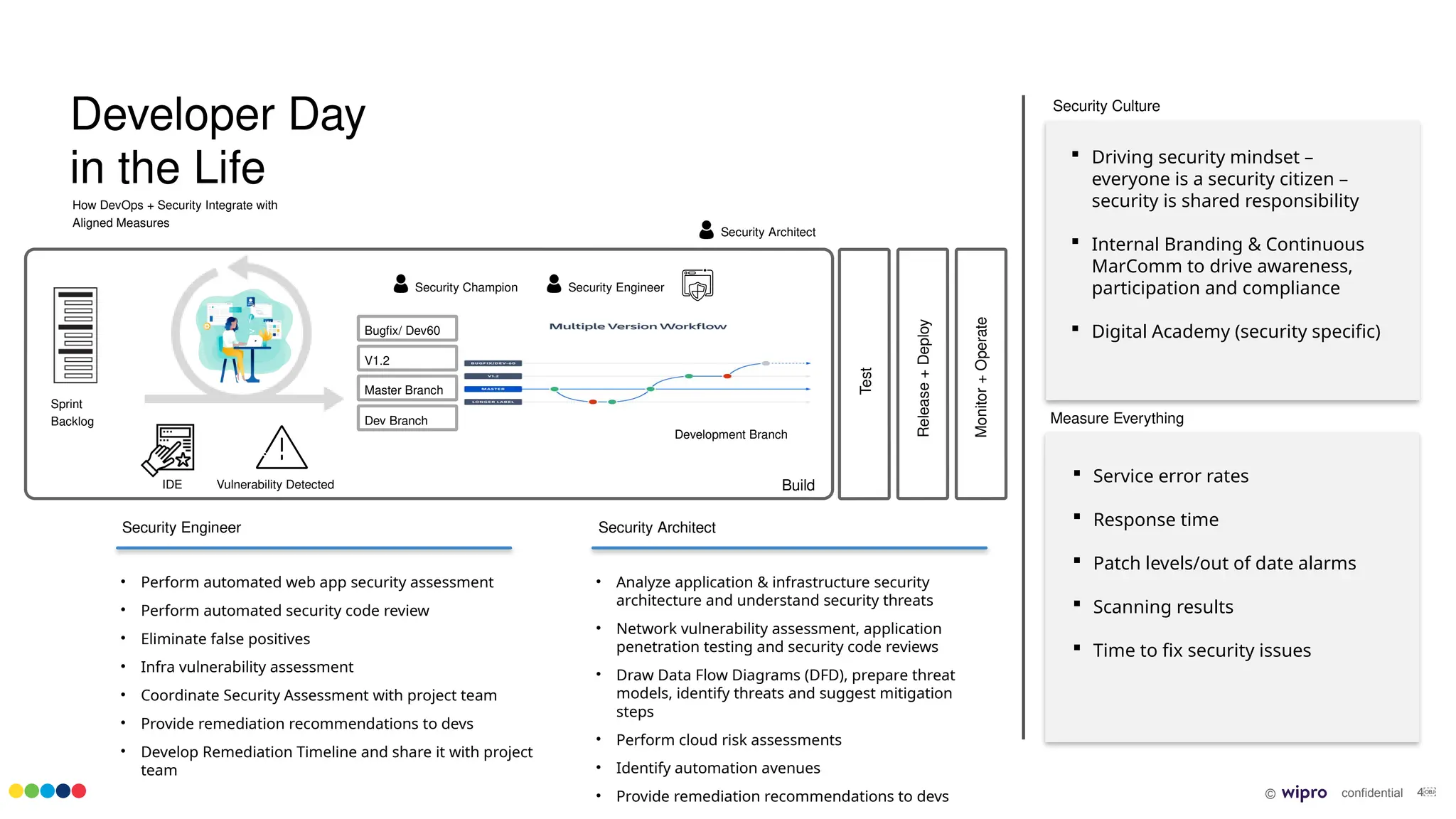
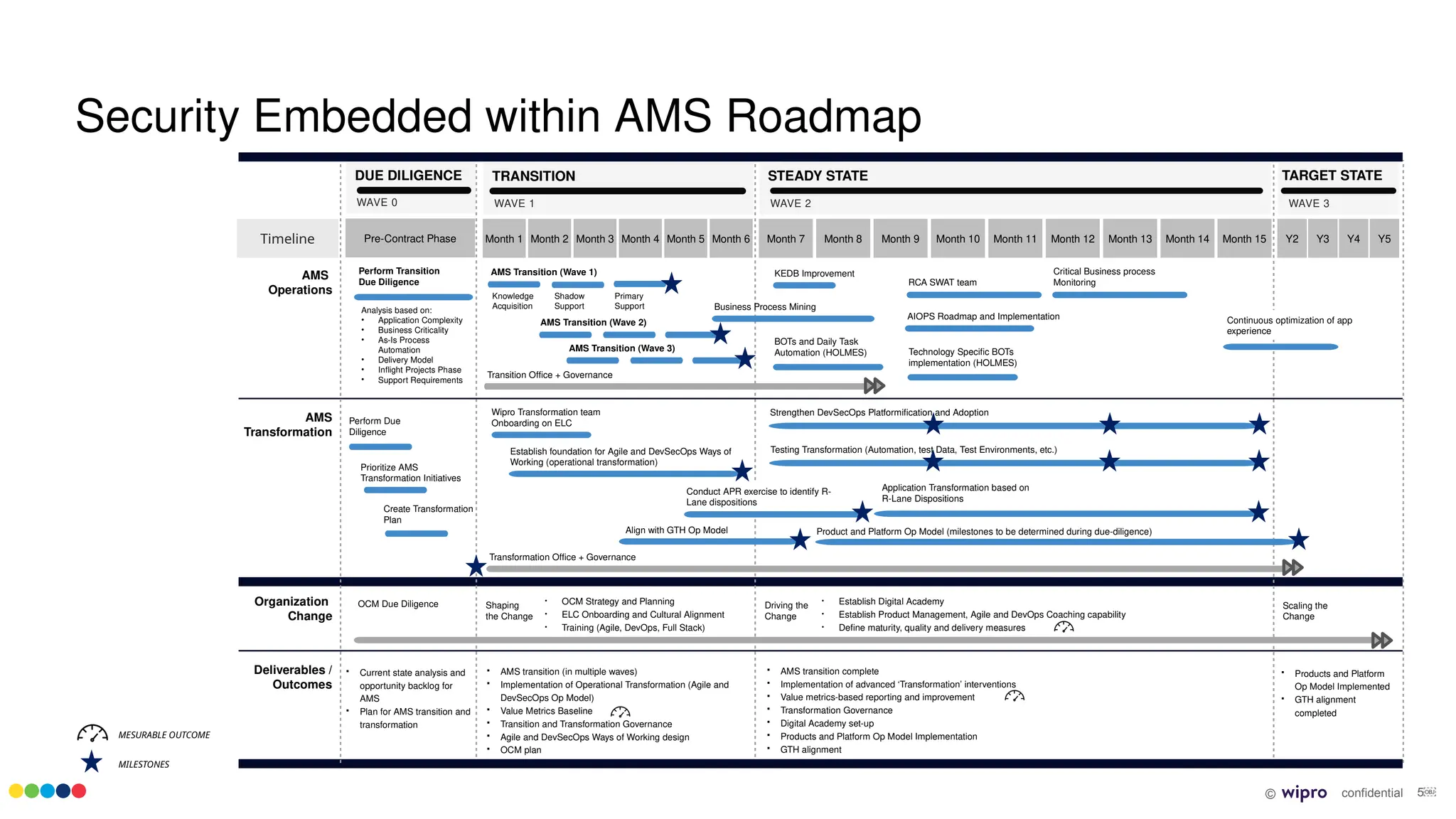
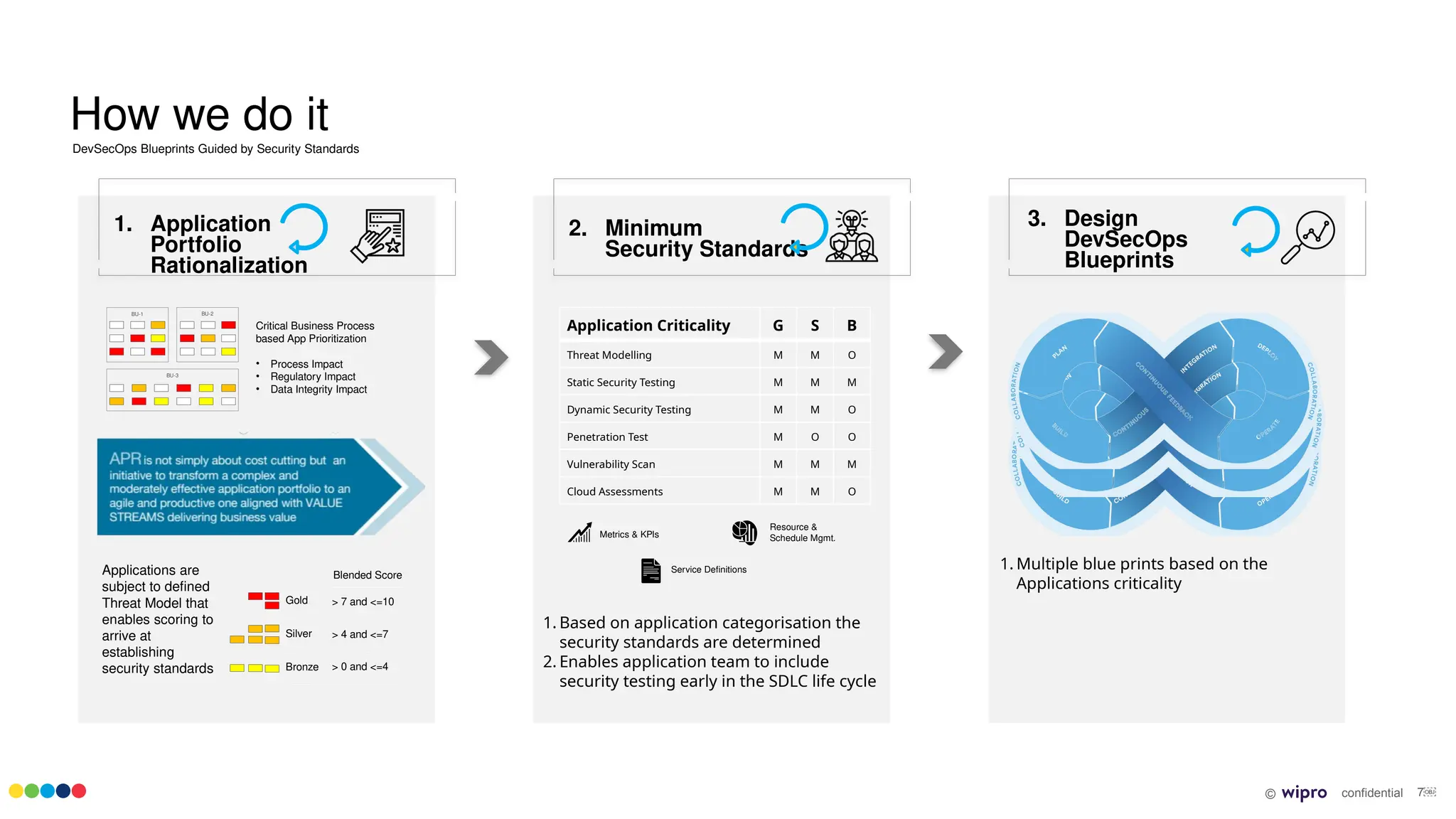
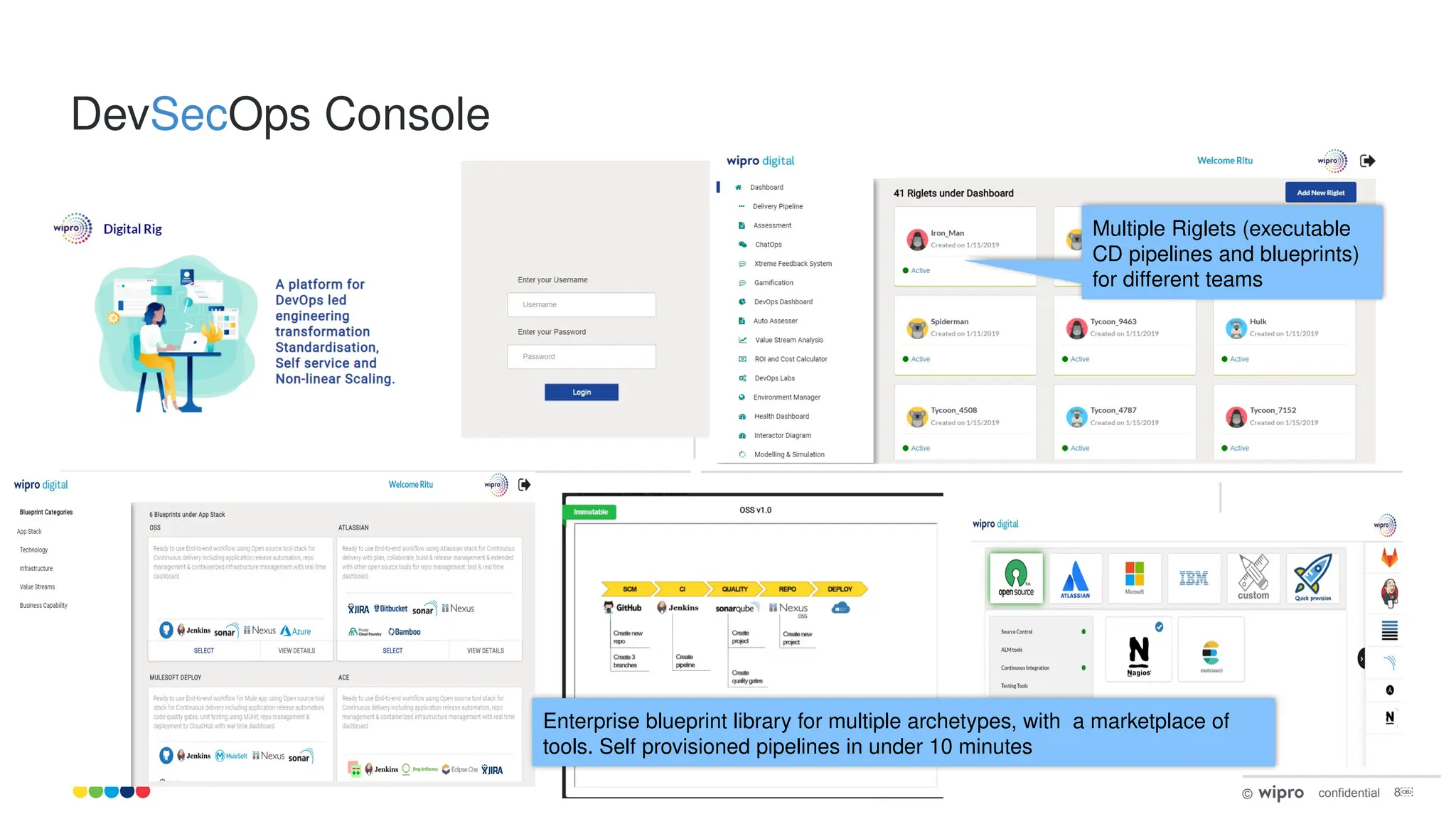
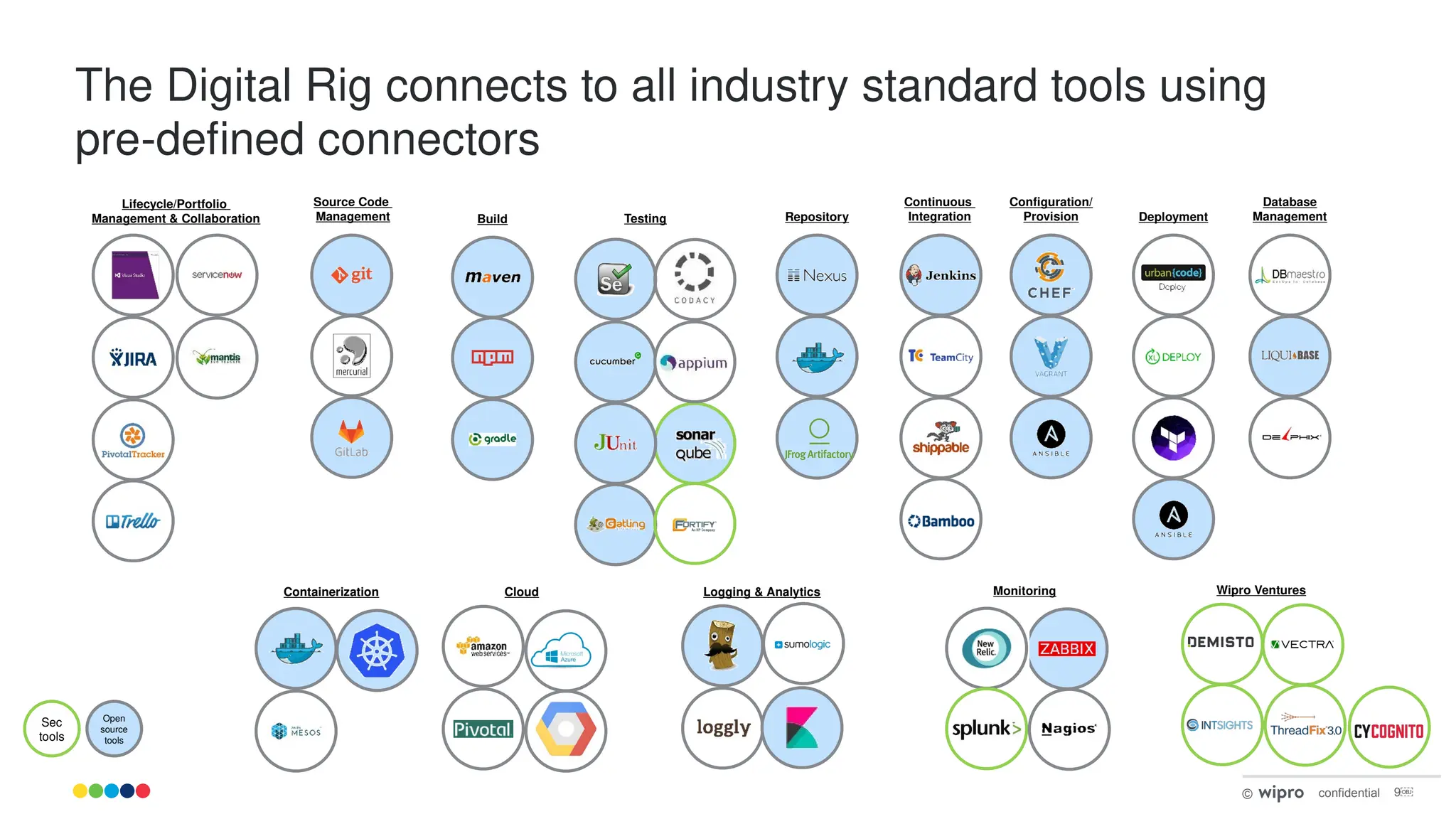
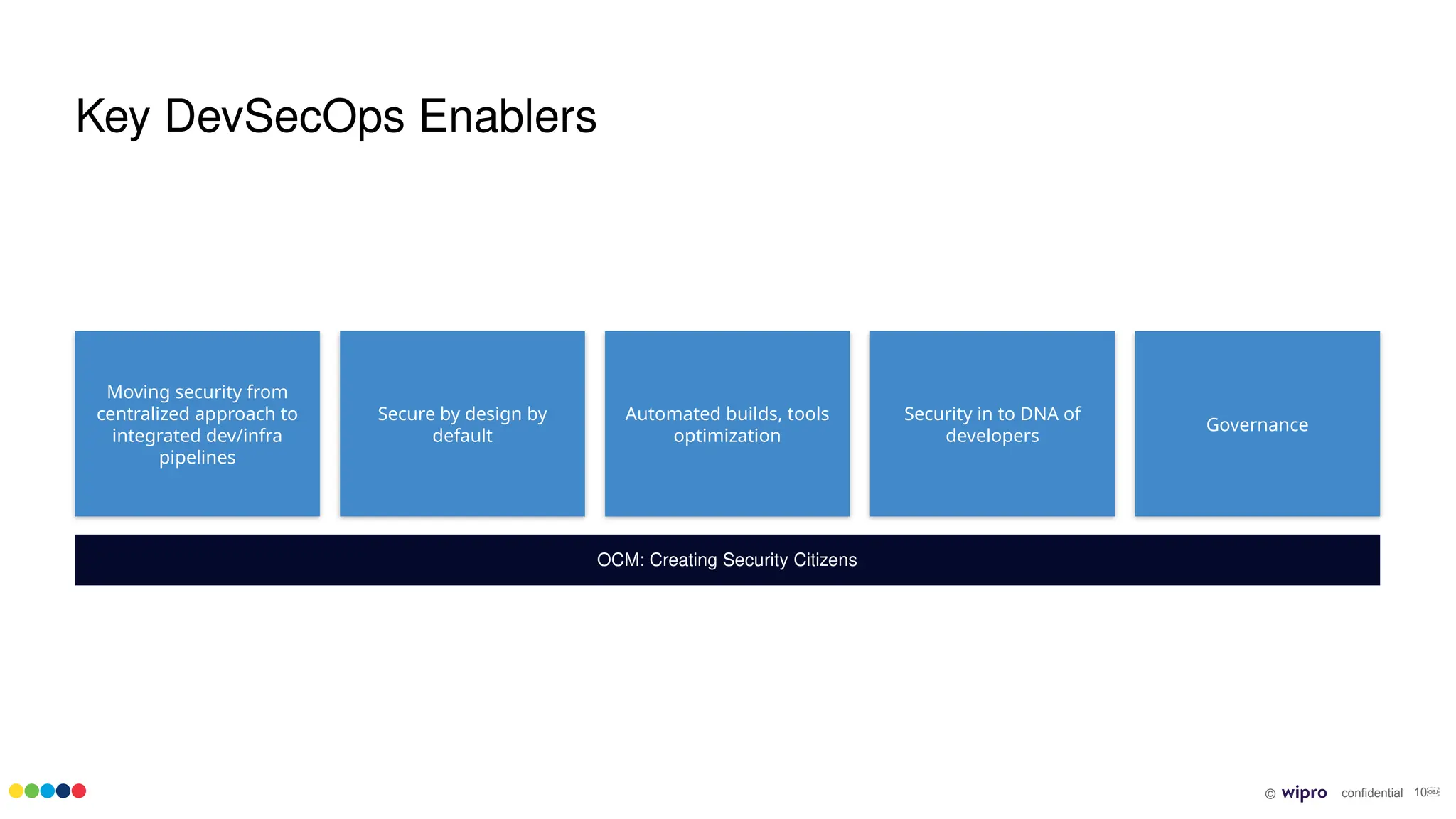
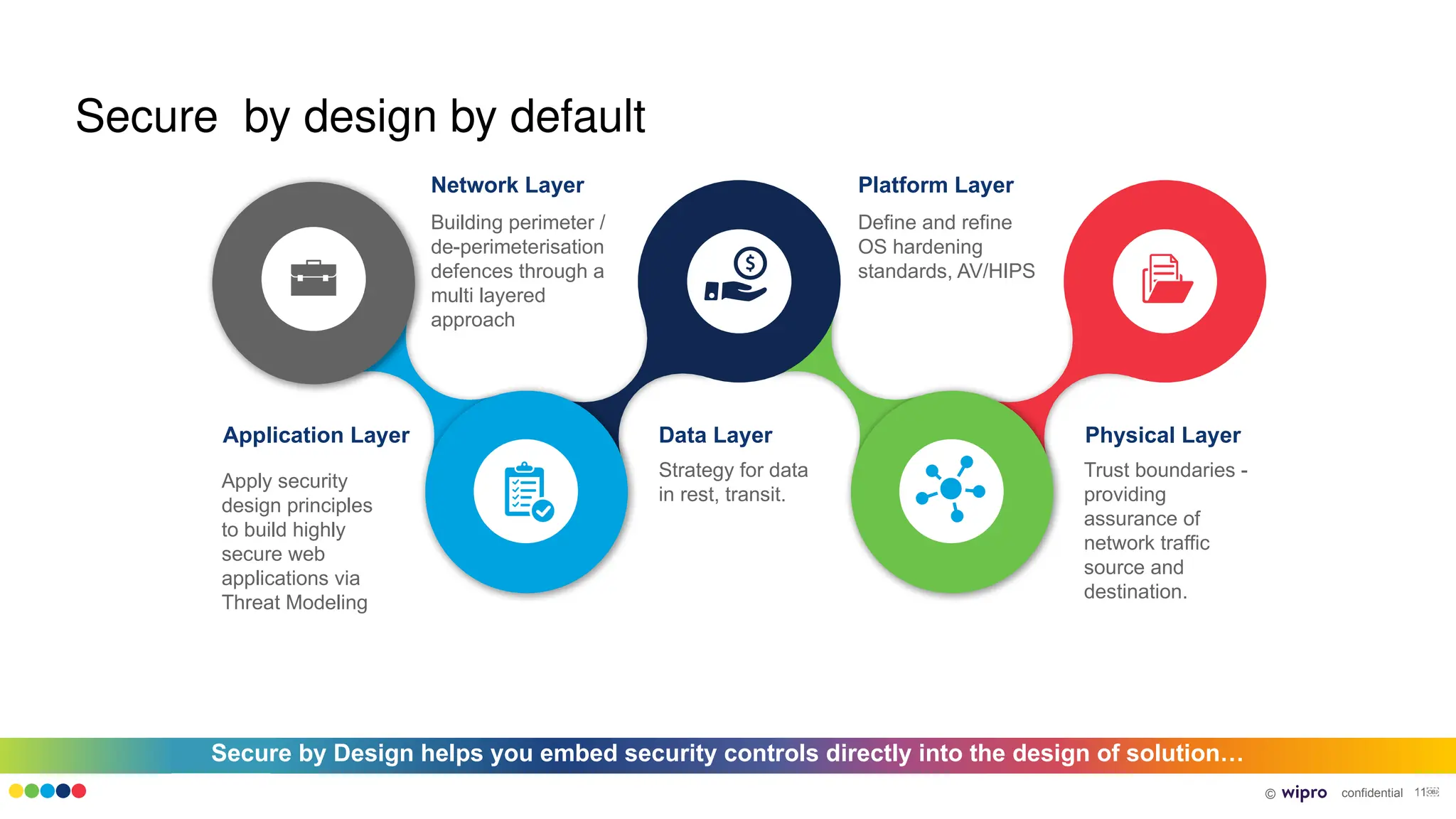
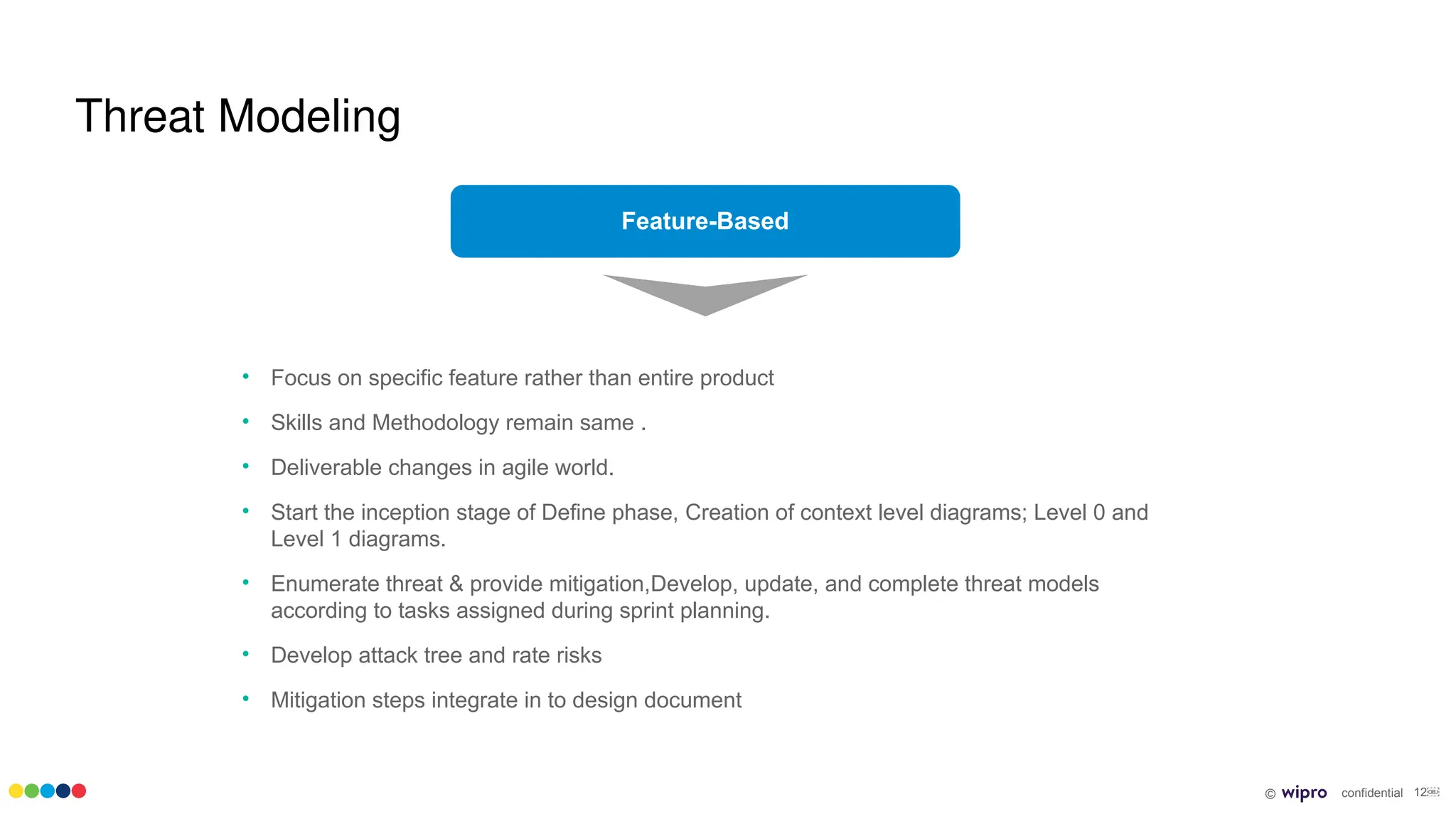
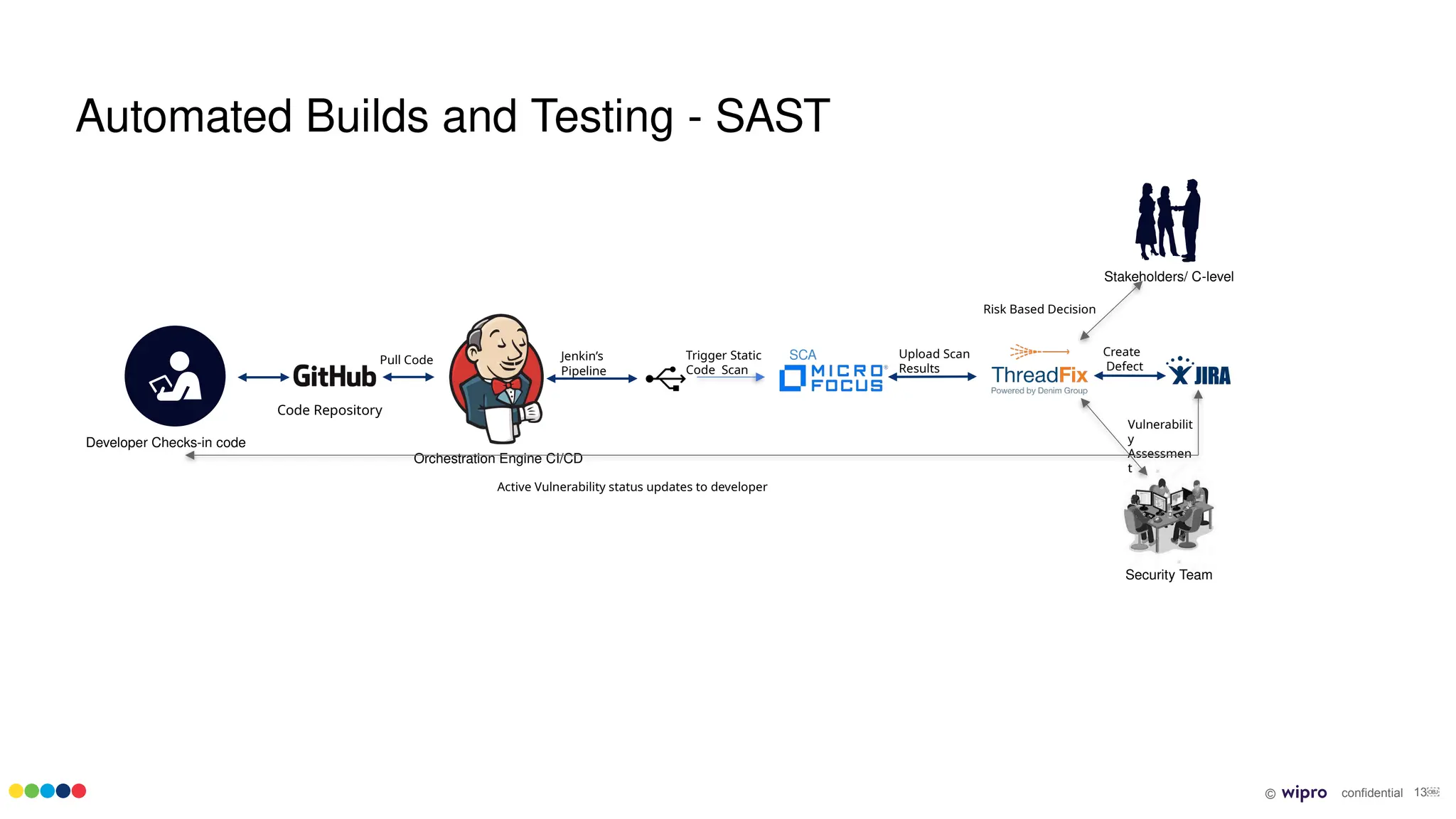
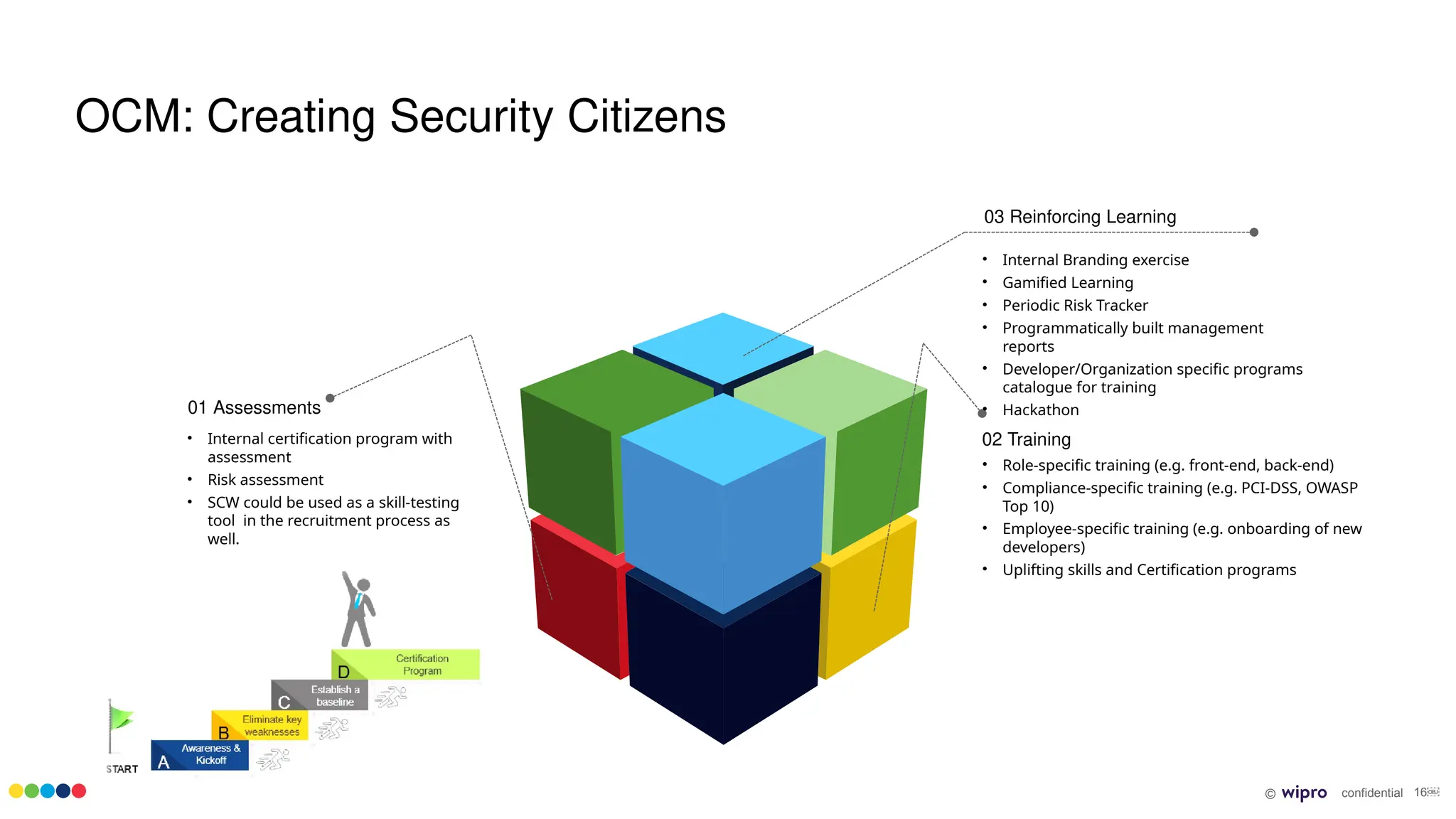
The document outlines a comprehensive DevSecOps strategy aimed at creating autonomous teams that integrate development, security, and operations efficiently. Key initiatives include automating security controls in the software development lifecycle (SDLC), implementing standardized practices for incident remediation, and fostering a culture of security awareness among all team members. The transition to an optimized DevSecOps environment is organized in waves with specific milestones and deliverables focused on embedding security throughout the application lifecycle.