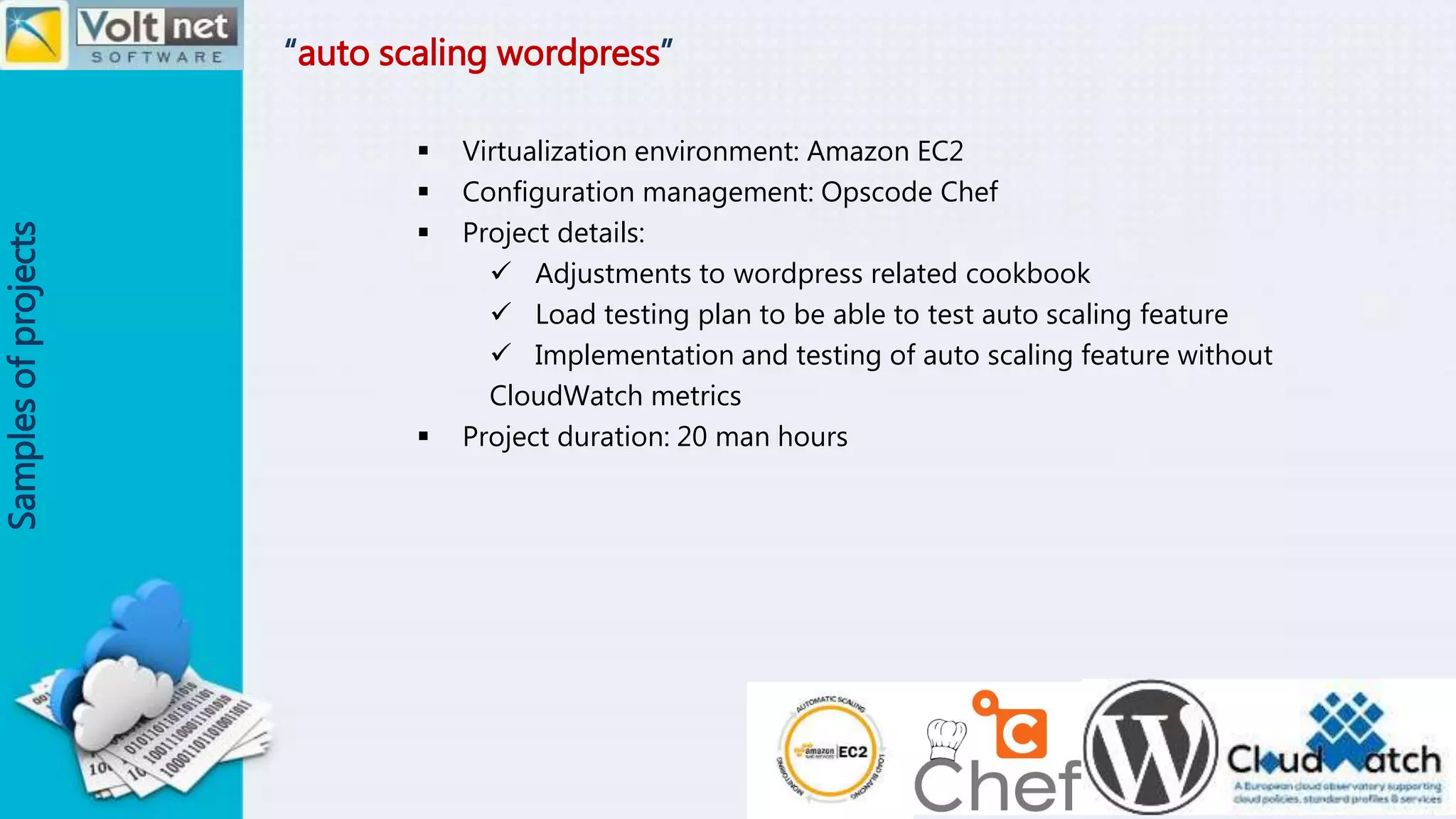
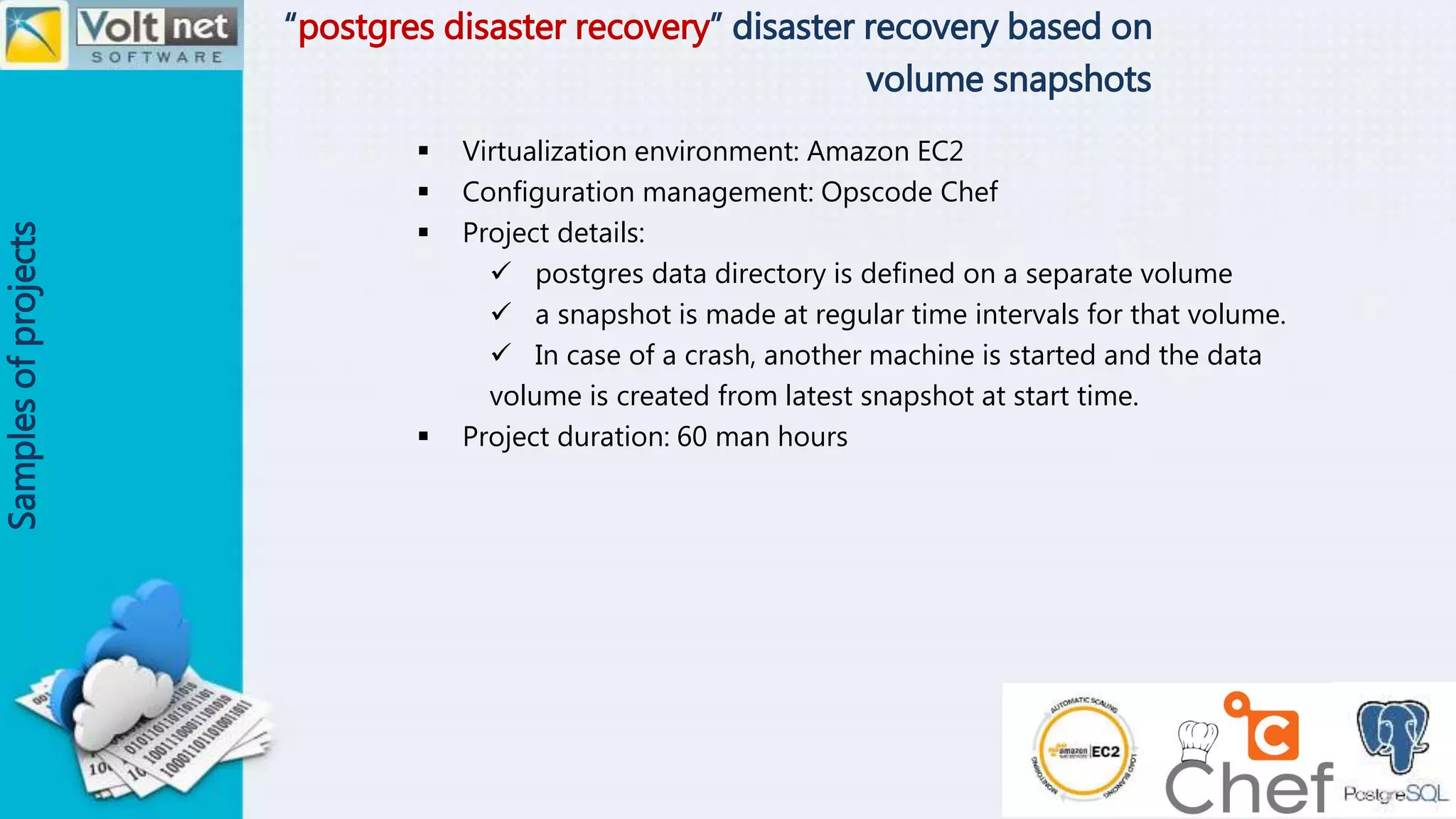
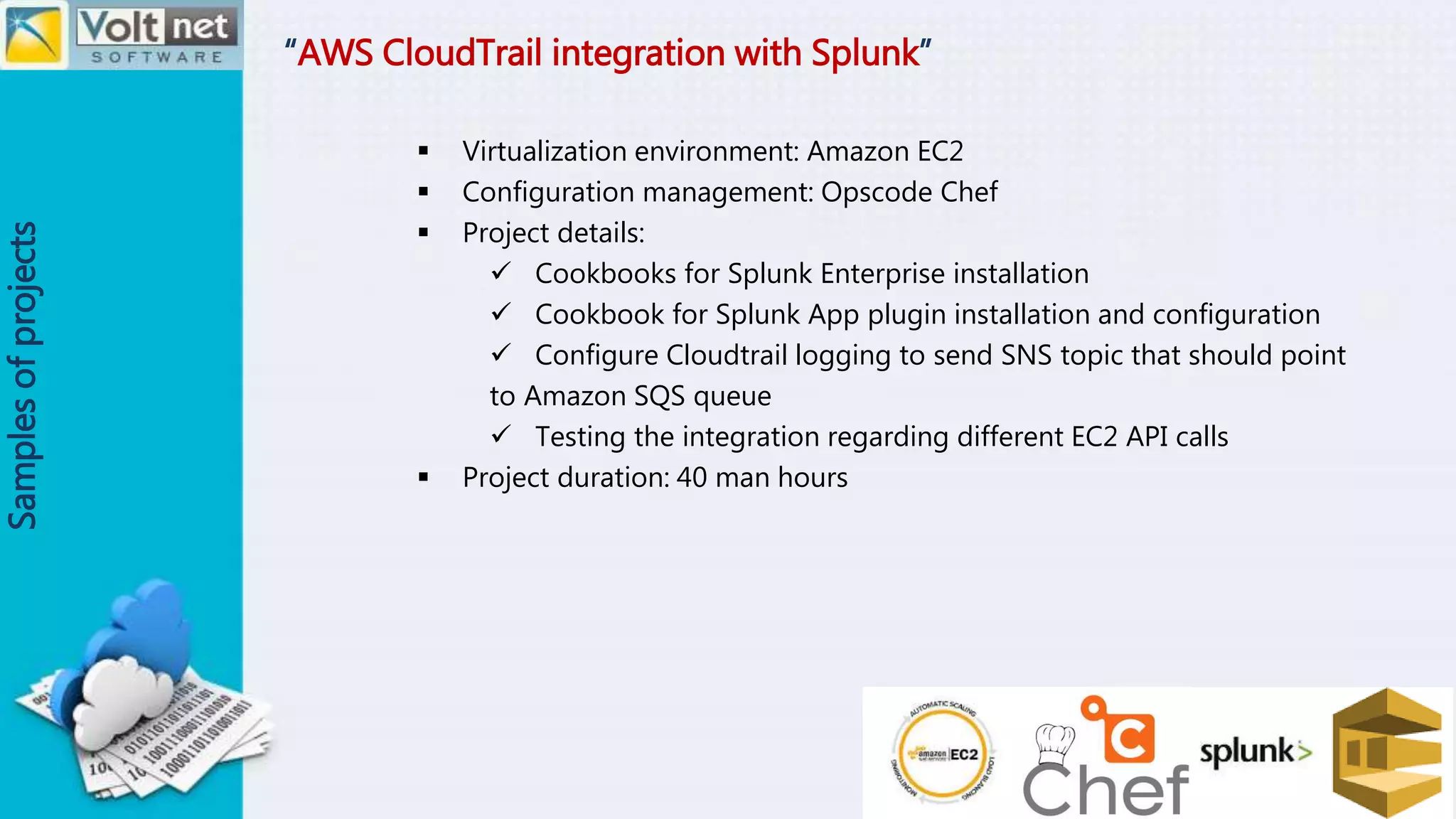
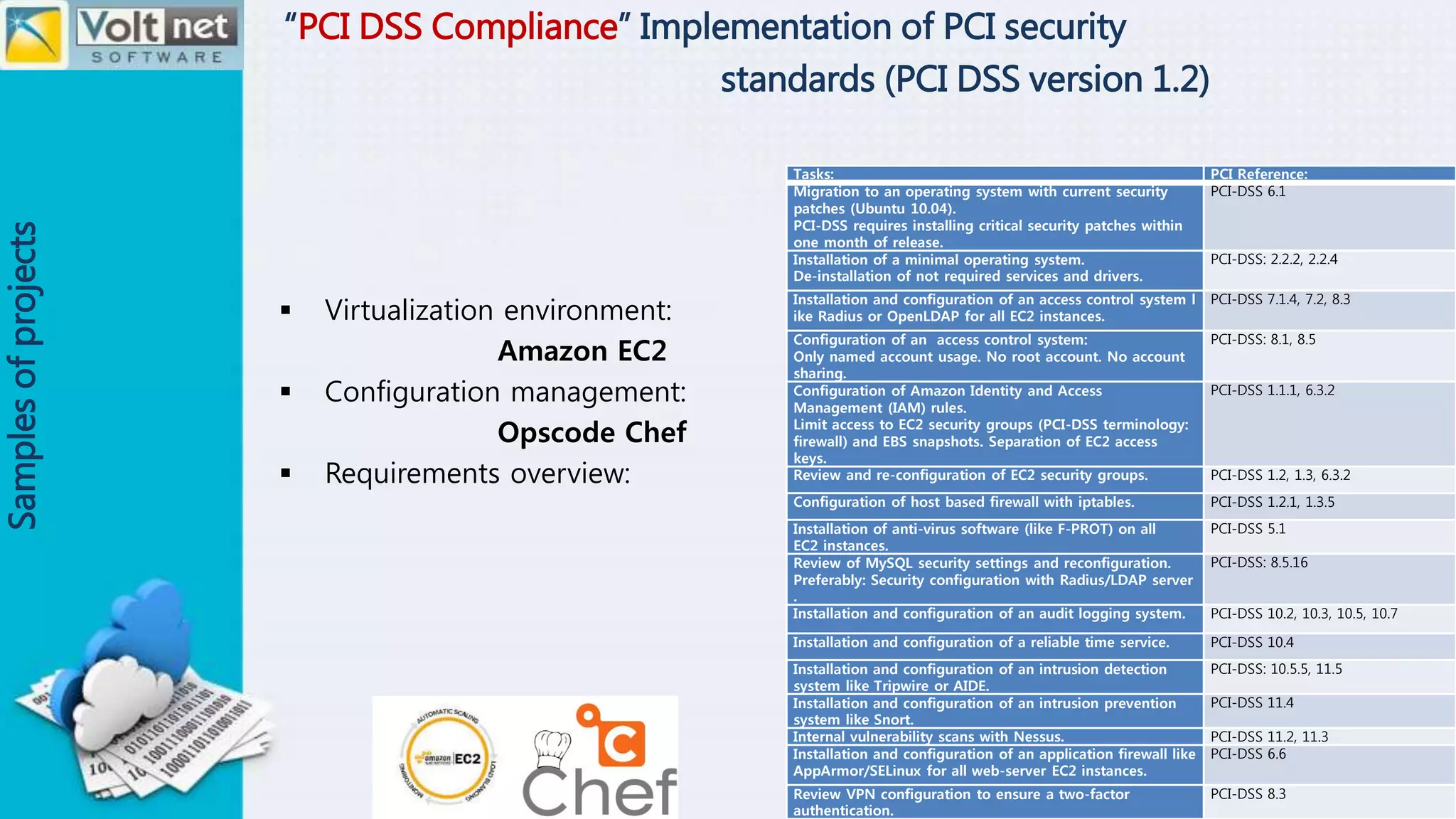
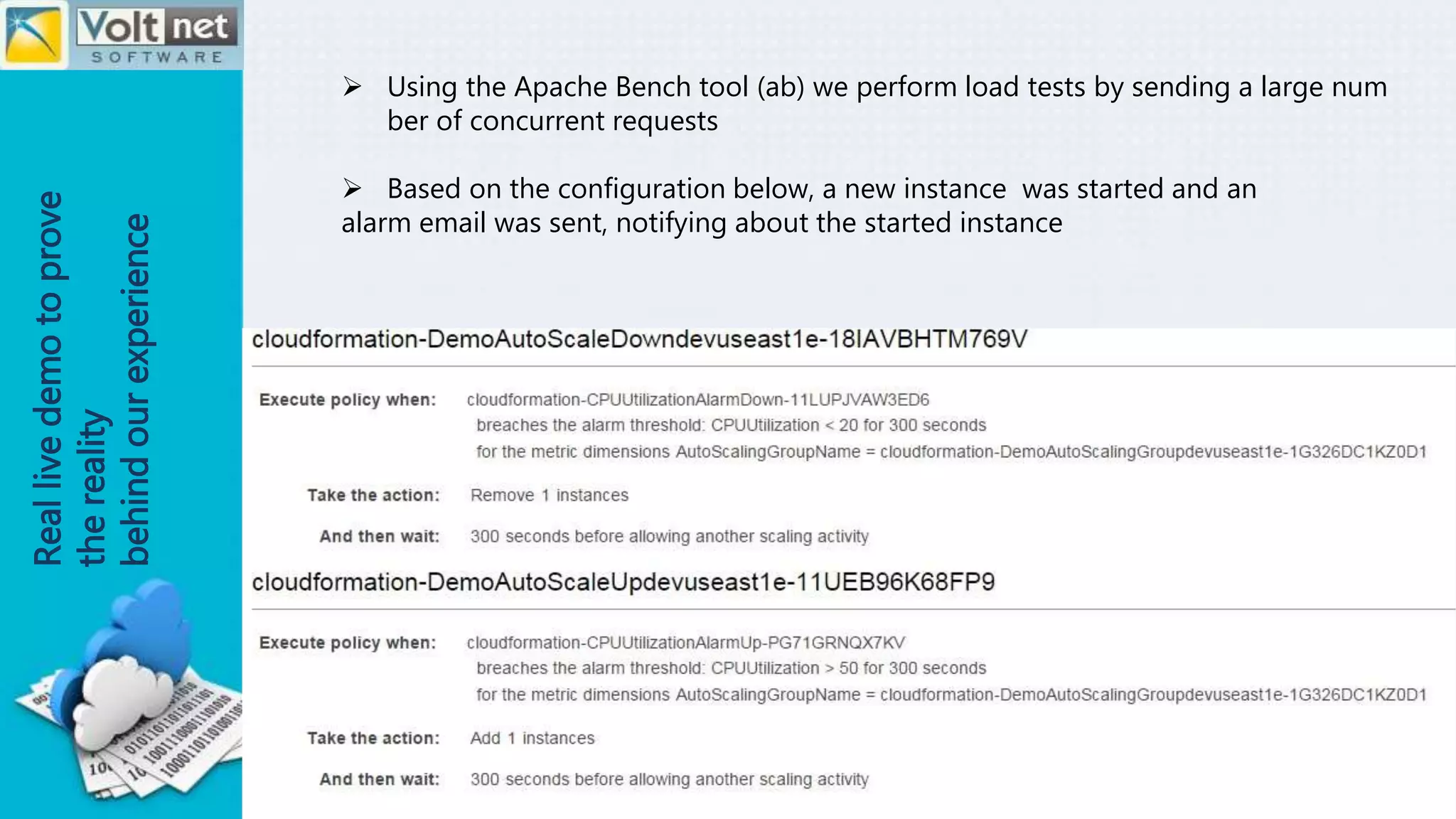
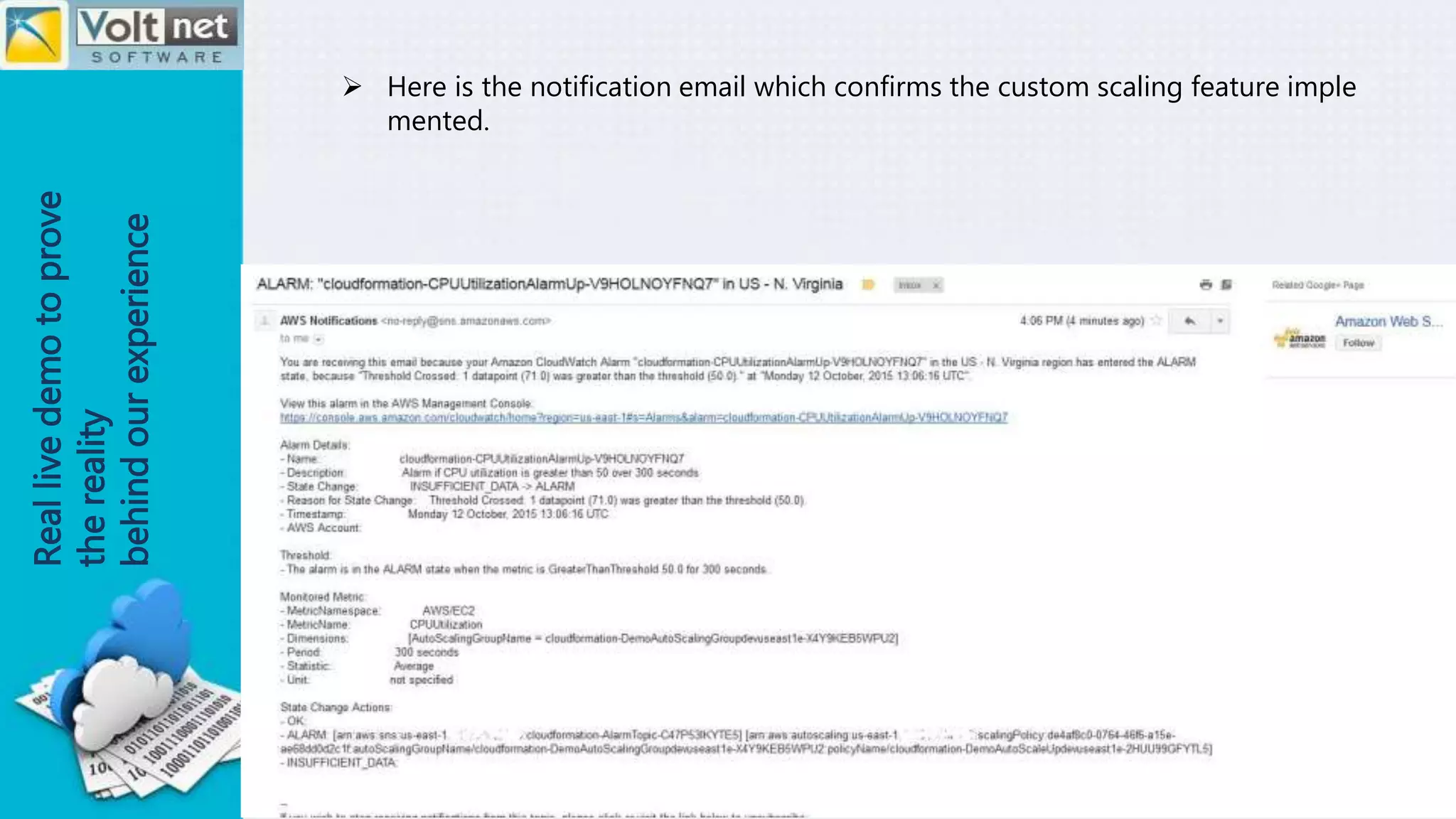
This document outlines the author's expertise in various technologies including DevOps tools like Git, Jenkins, and Chef. It also covers programming languages and frameworks like Java, Spring, databases like PostgreSQL, monitoring tools, AWS services, and experience with PCI compliance and other security standards. The author has hands-on experience across the full stack from version control to deployment and automation and can implement solutions for tasks like scaling, security, and disaster recovery. Sample project descriptions are provided relating to auto-scaling, security, monitoring, and compliance.