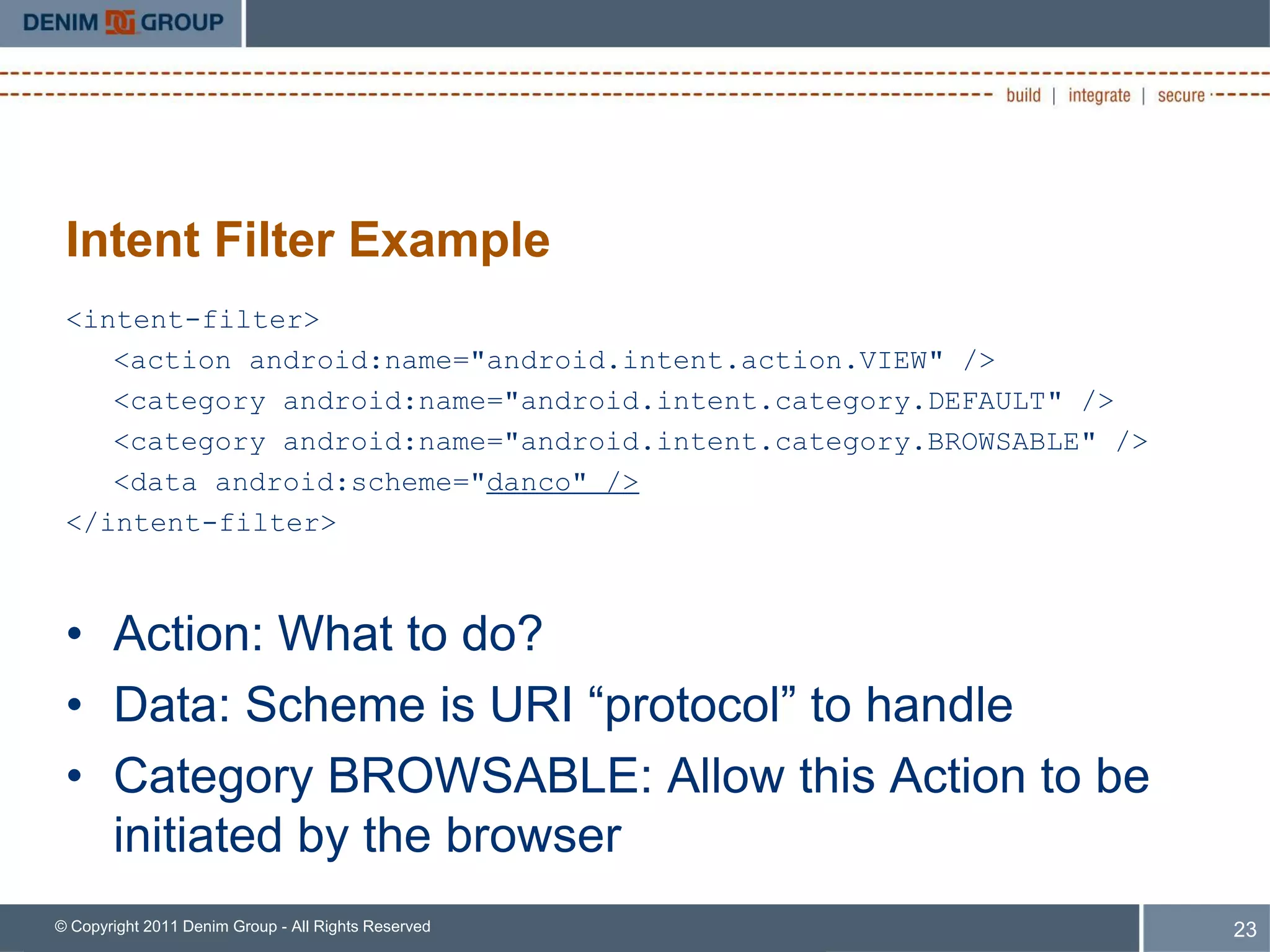
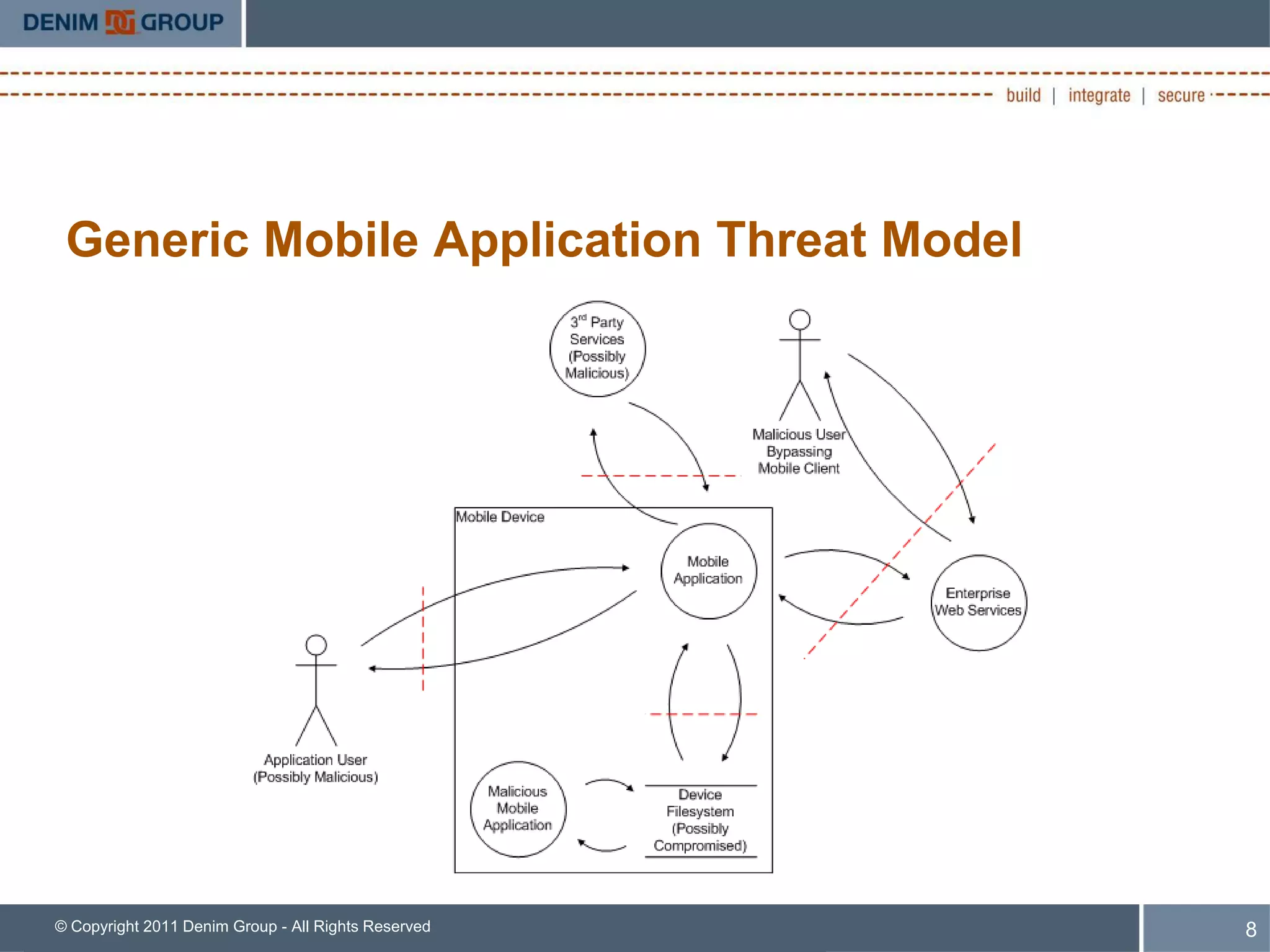
Dan Cornell presented on designing secure mobile apps. He discussed generic mobile app threats and design concerns like bypassing platform restrictions, permissions, storage, encryption, and native code. He provided an in-depth look at mobile browser content handling via URL schemes and intents. He emphasized that developers should treat data from these sources as untrusted and validate inputs. Security teams should assess apps' data storage, services used, and new services deployed to support apps. The full slides and videos are available online.
![iOS URL Handlers
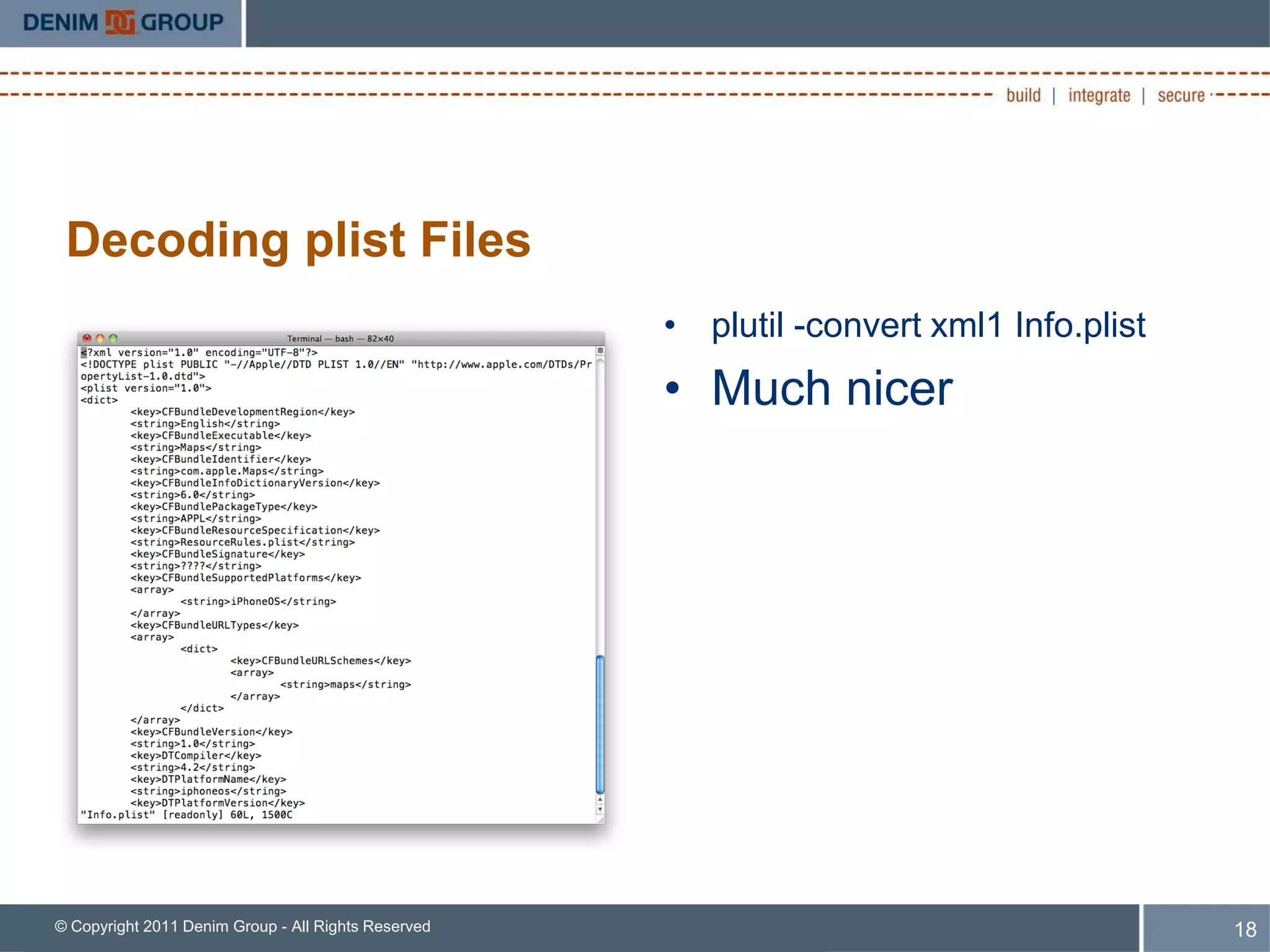
• XPath: Look for:
/plist/dict/array/dict[key='CFBundleURLSchemes']/array/string
• Now you know the URL Schemes the app handles
• SANS blog post on this issue in iOS:
– http://software-security.sans.org/blog/2010/11/08/insecure-handling-url-schemes-
apples-
ios/?utm_source%253Drss%2526utm_medium%253Drss%2526utm_campaign%2
53Dinsecure-handling-url-schemes-apples-ios
– Too long to type? http://bit.ly/ezqdK9
© Copyright 2011 Denim Group - All Rights Reserved 19](https://image.slidesharecdn.com/designingsecuremobileappsbsidesaustin20110312-110316081700-phpapp01/75/Designing-Secure-Mobile-Apps-20-2048.jpg)