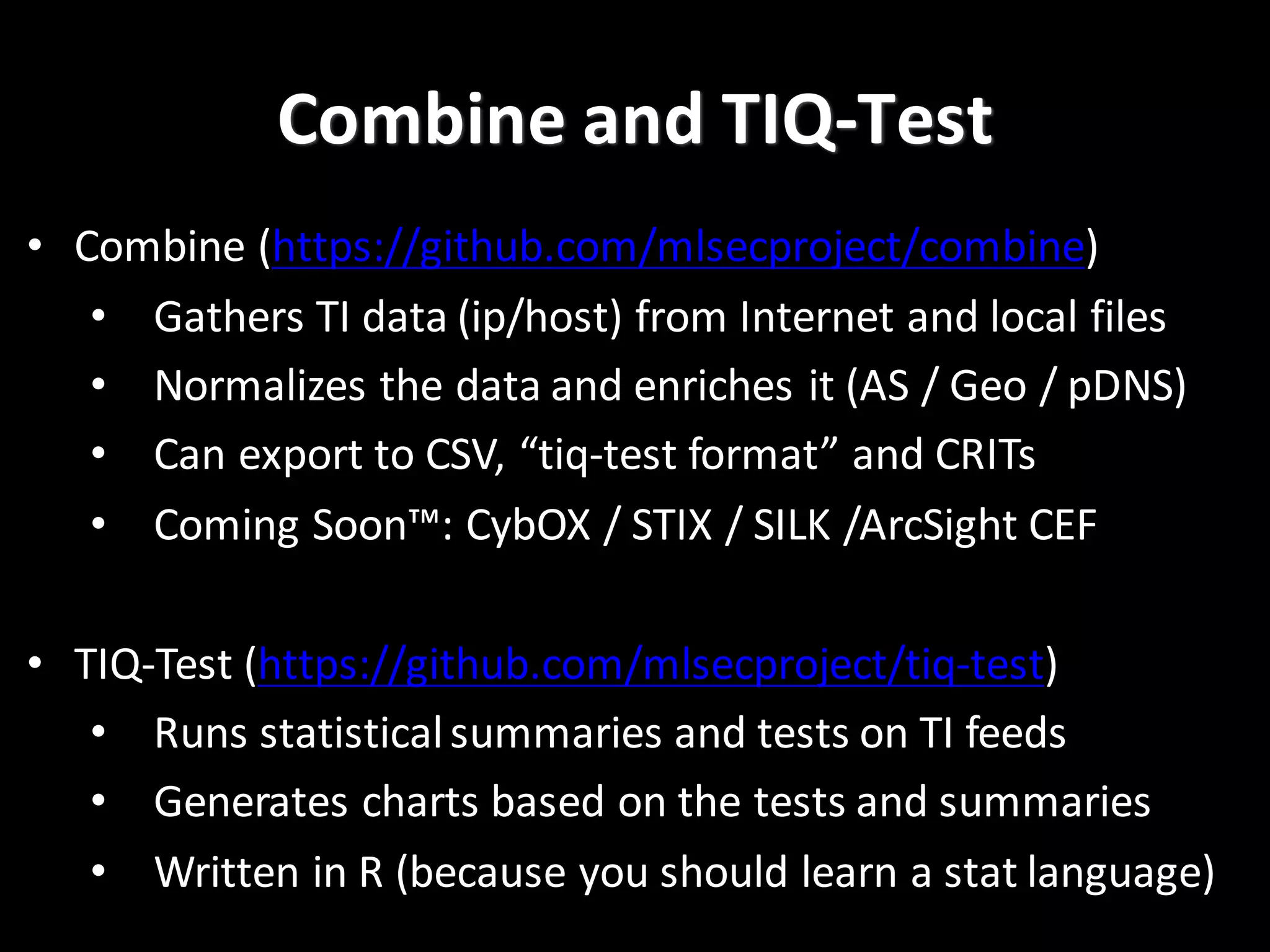
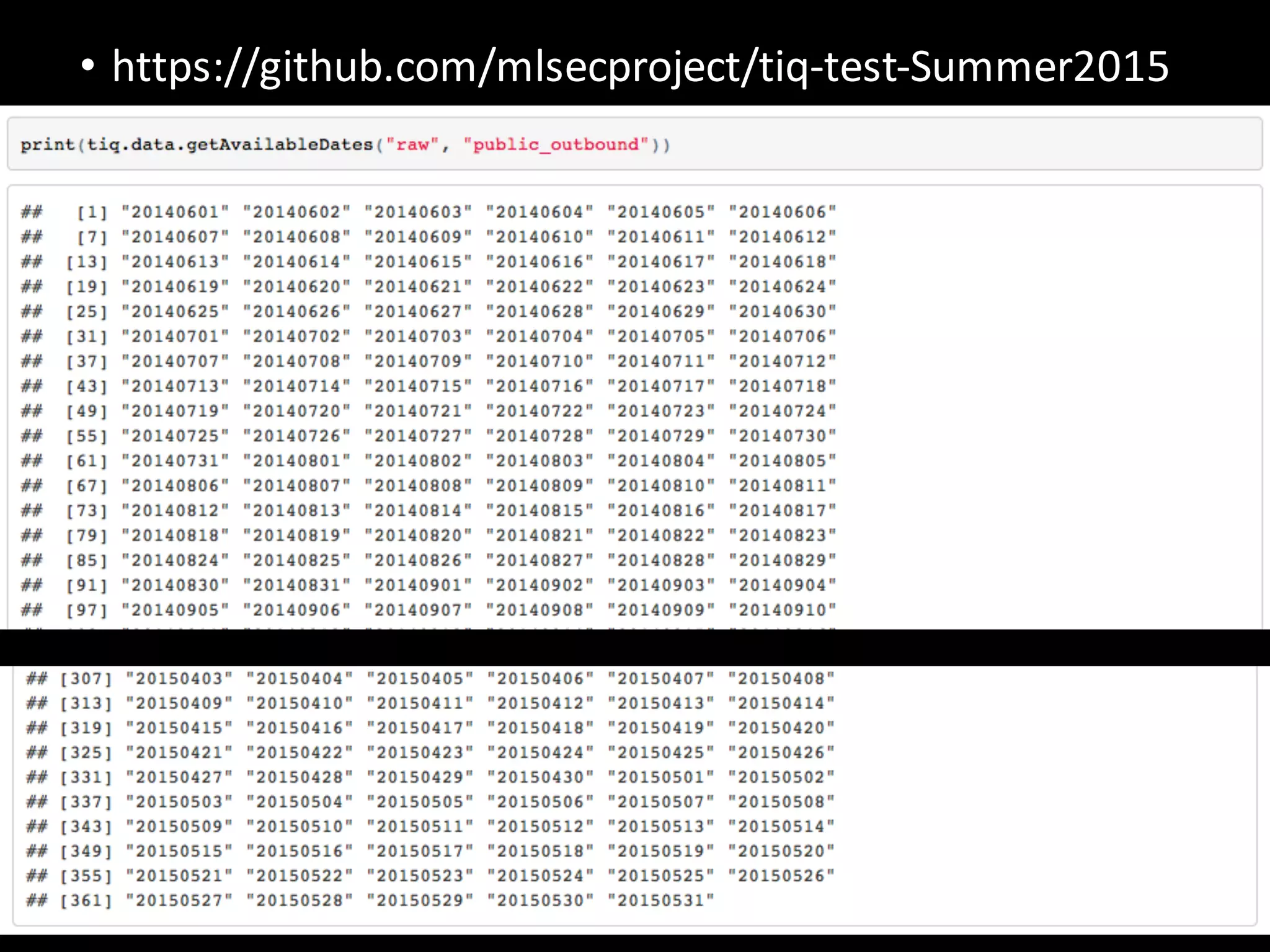
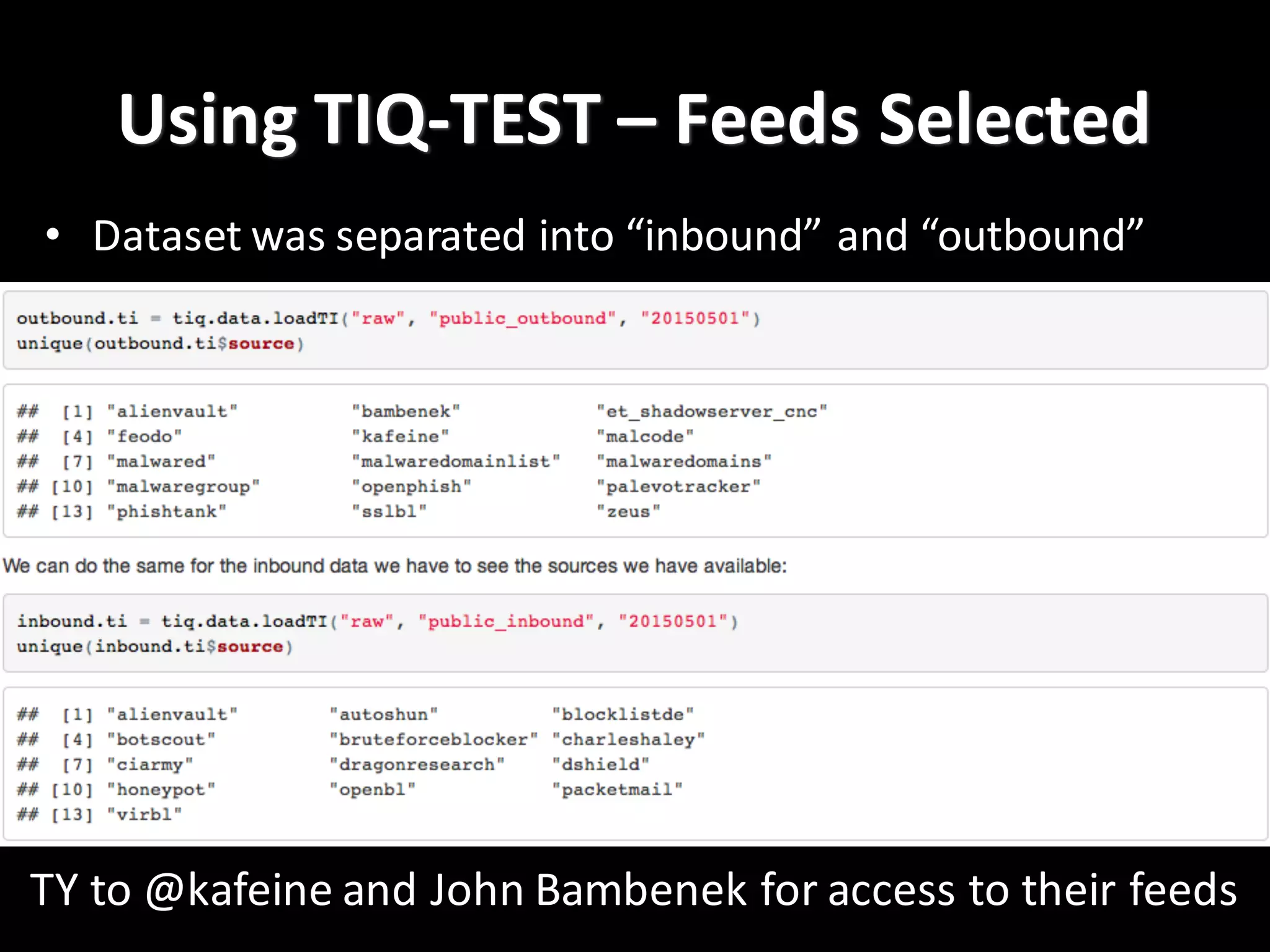
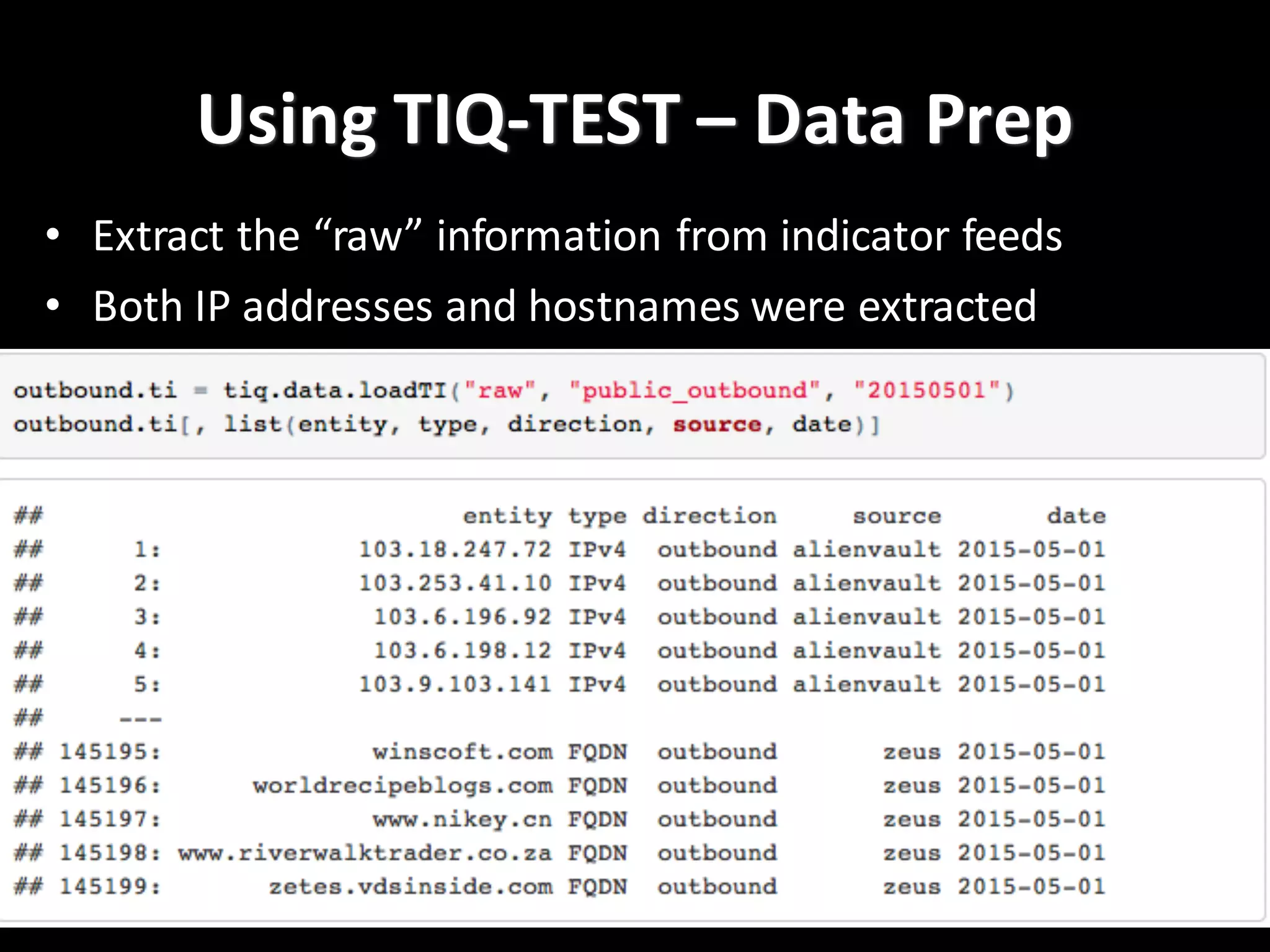
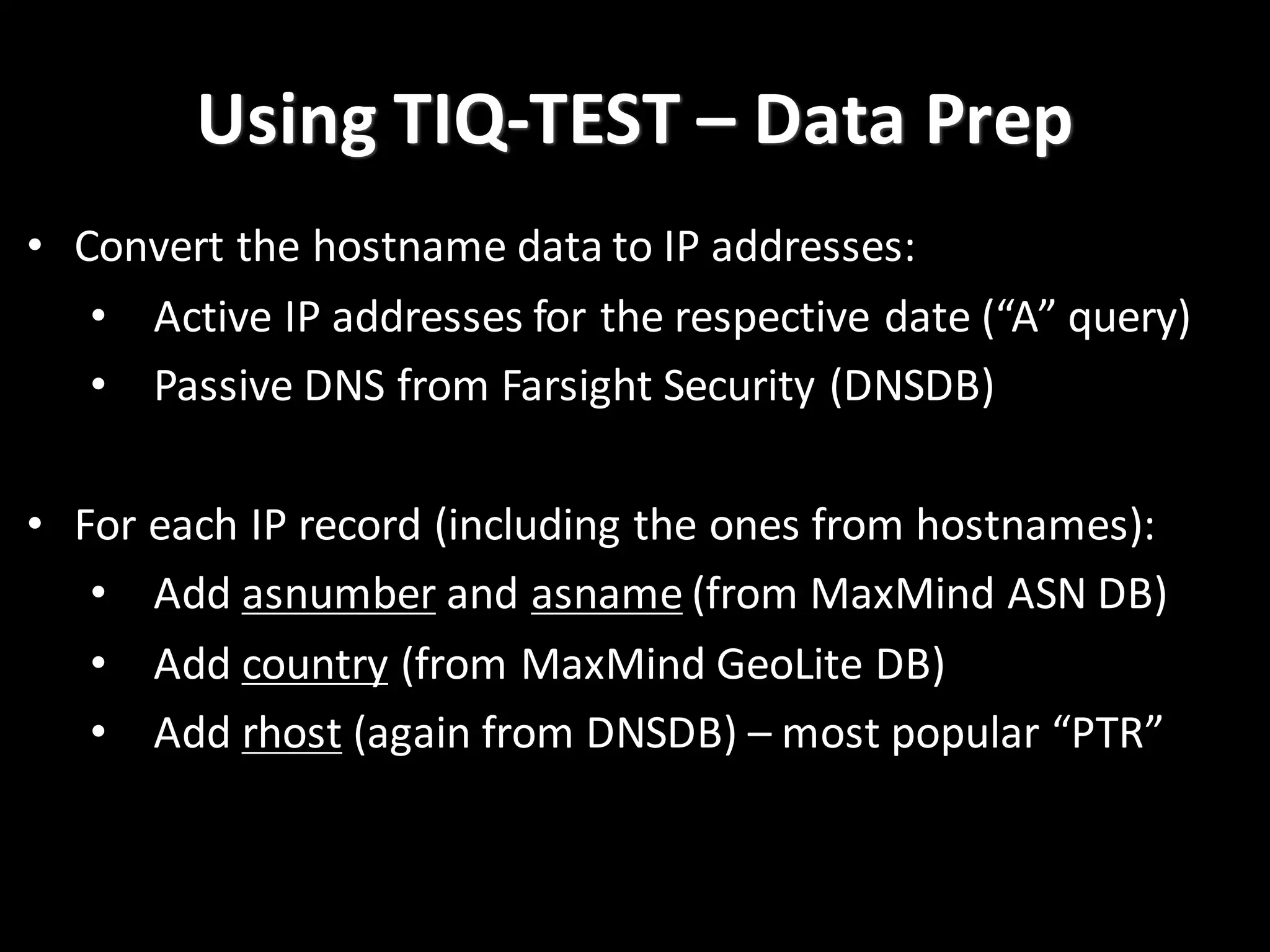
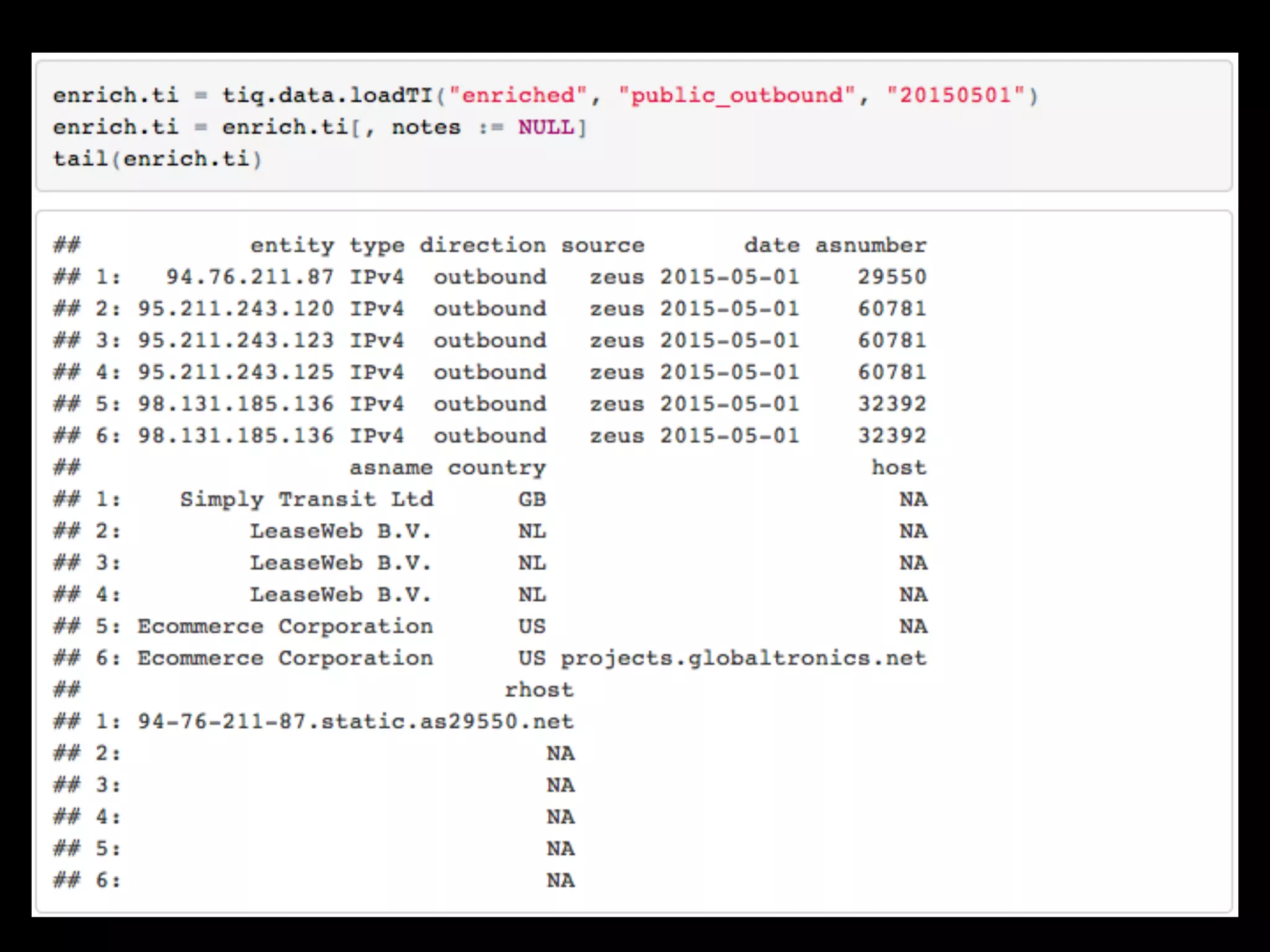
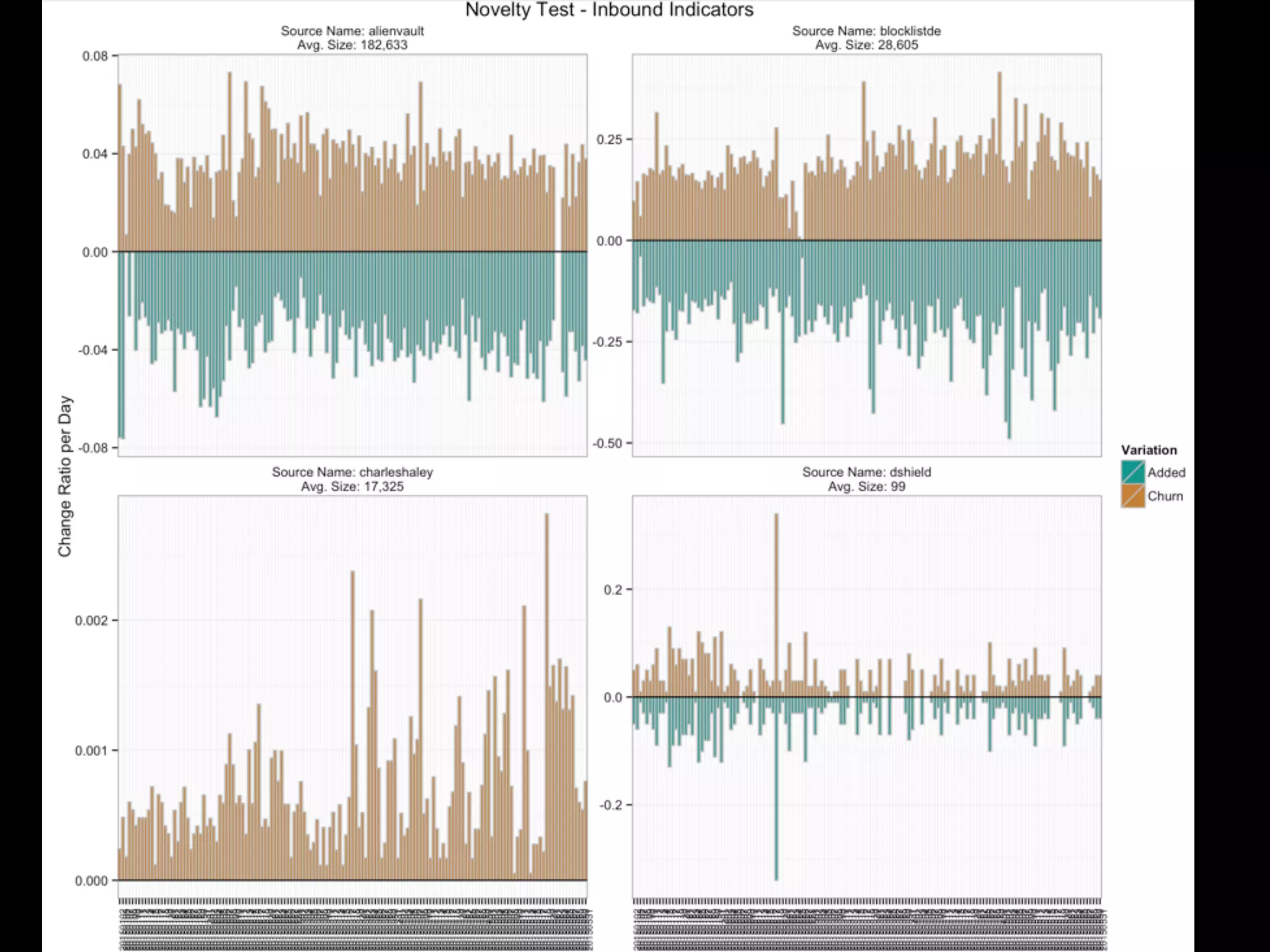
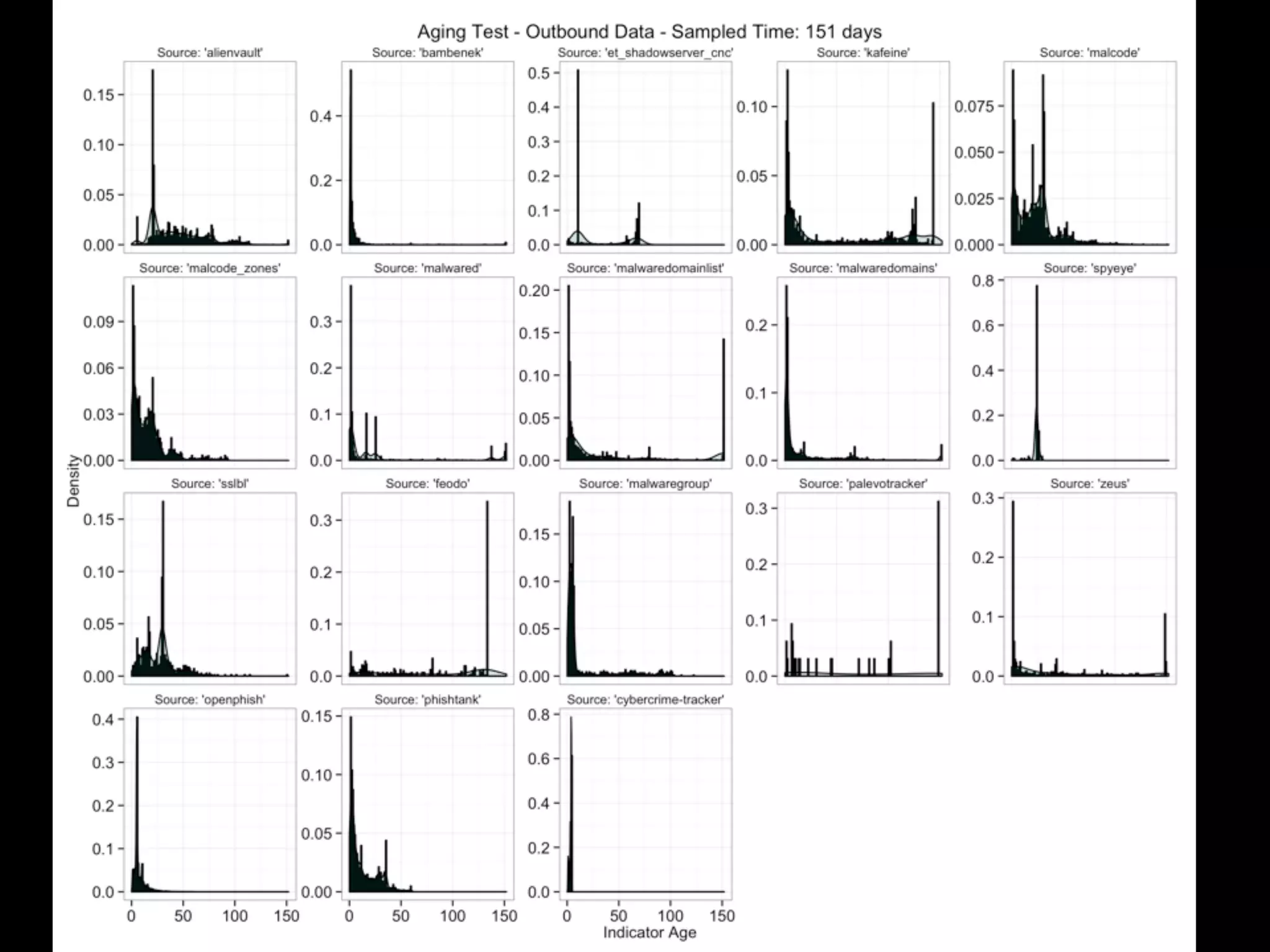
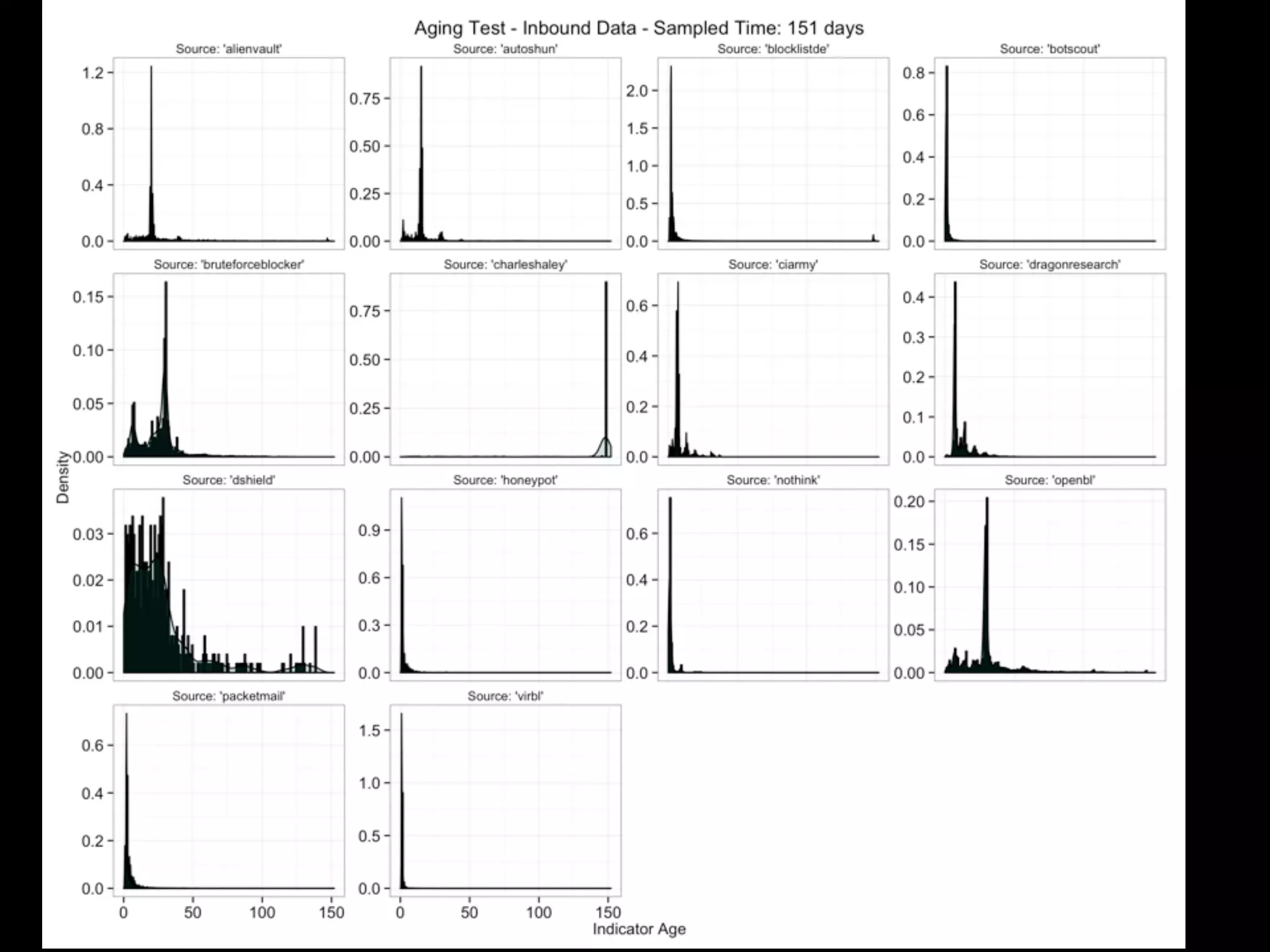
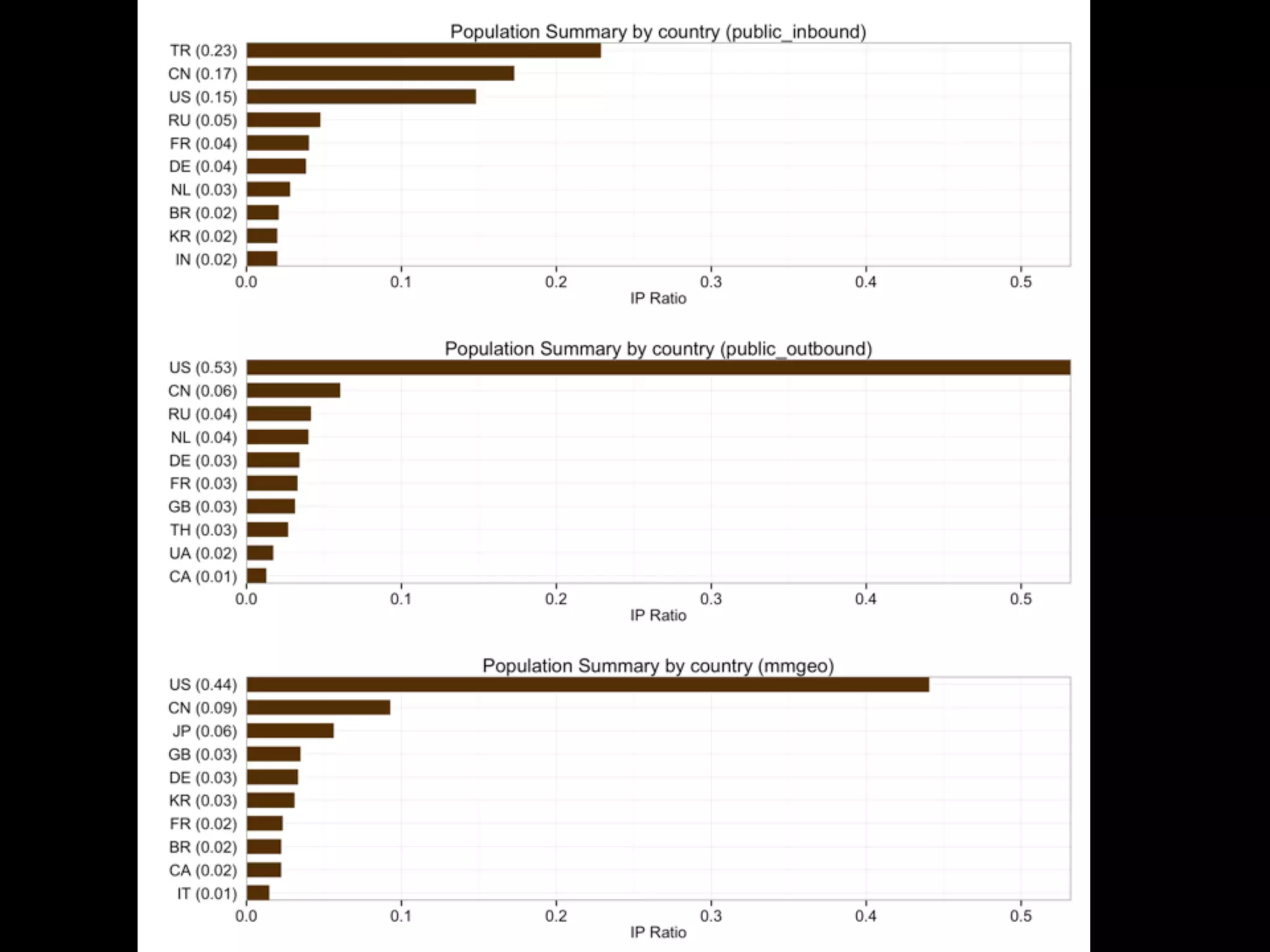
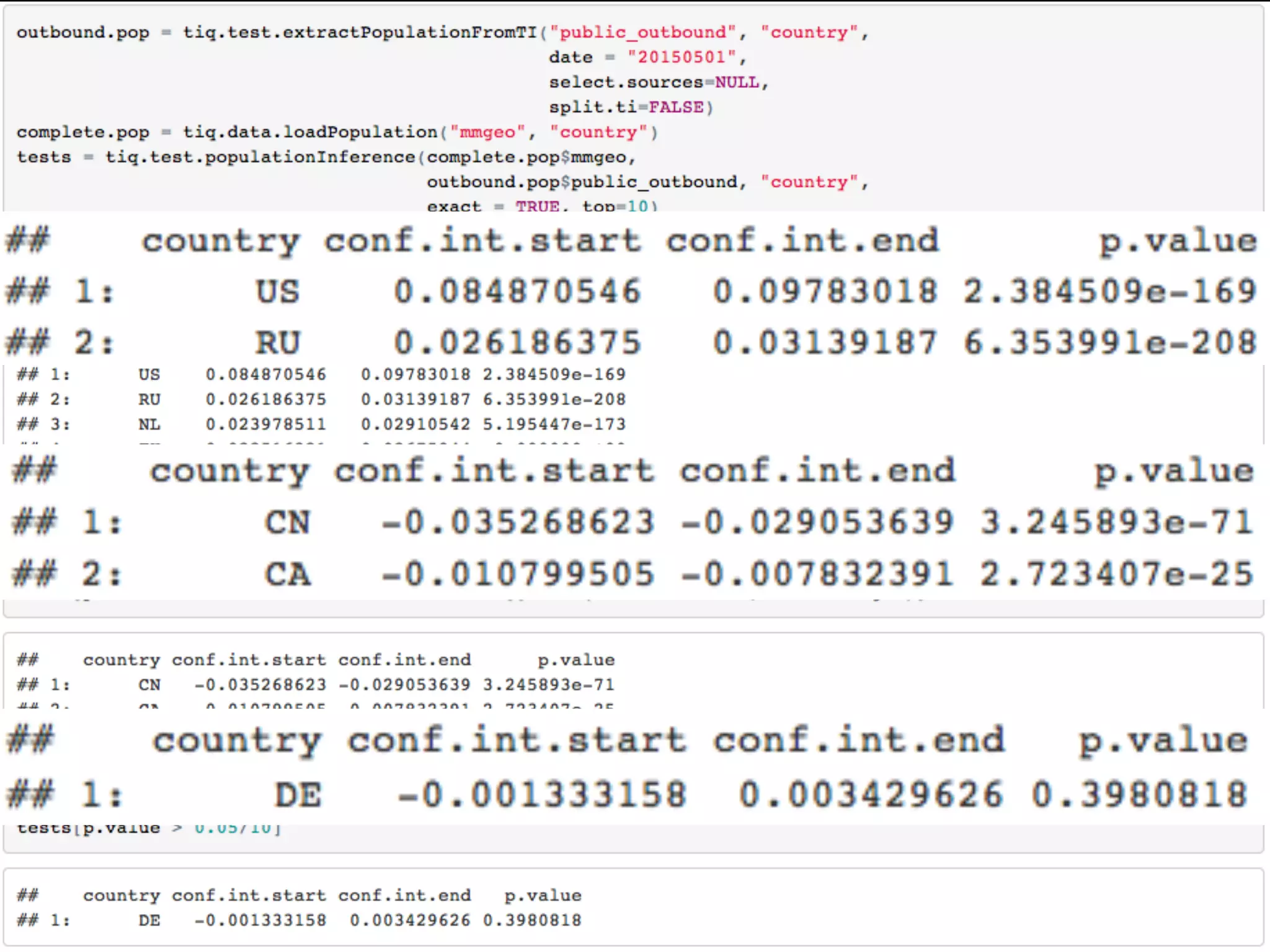
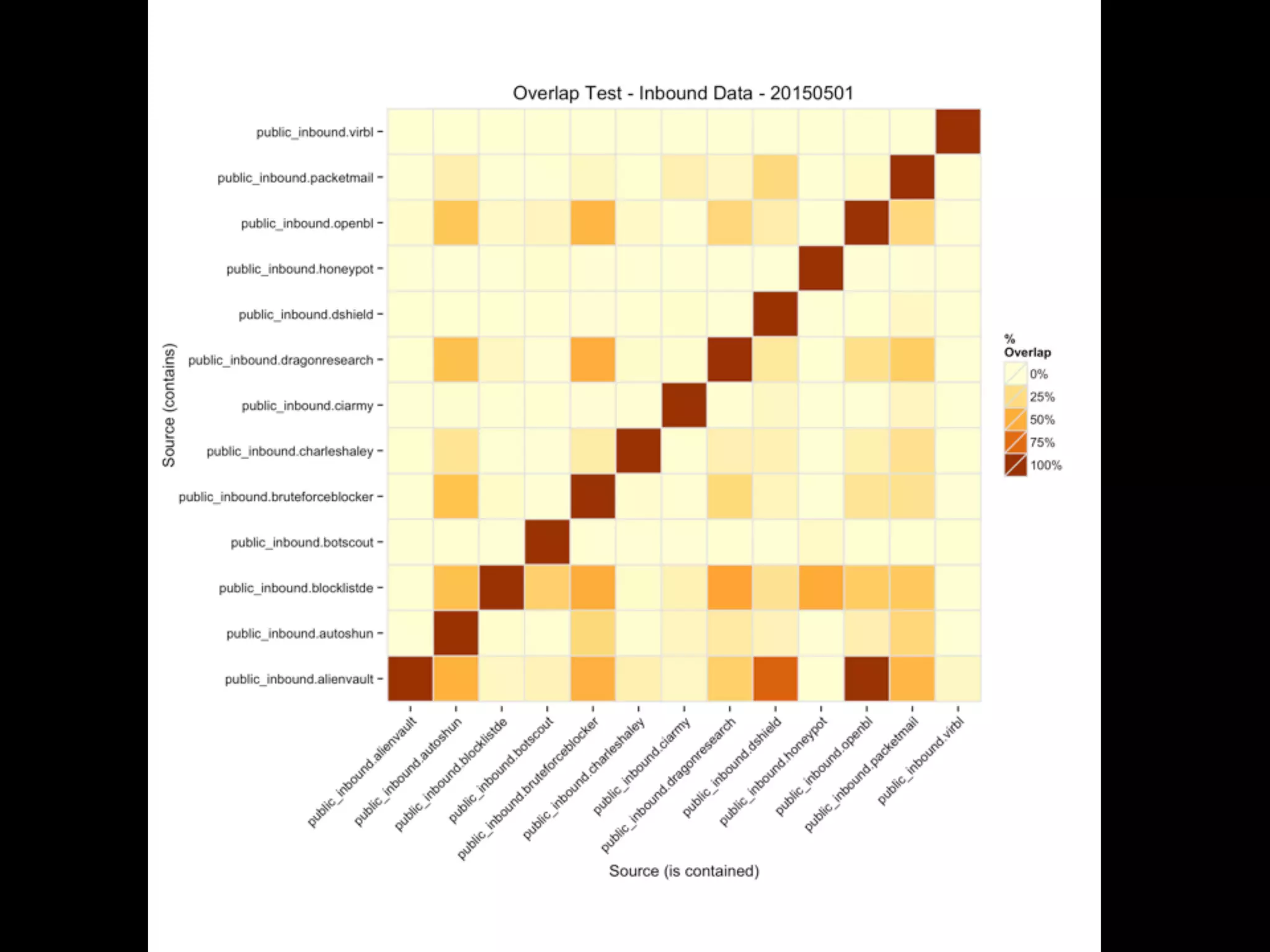
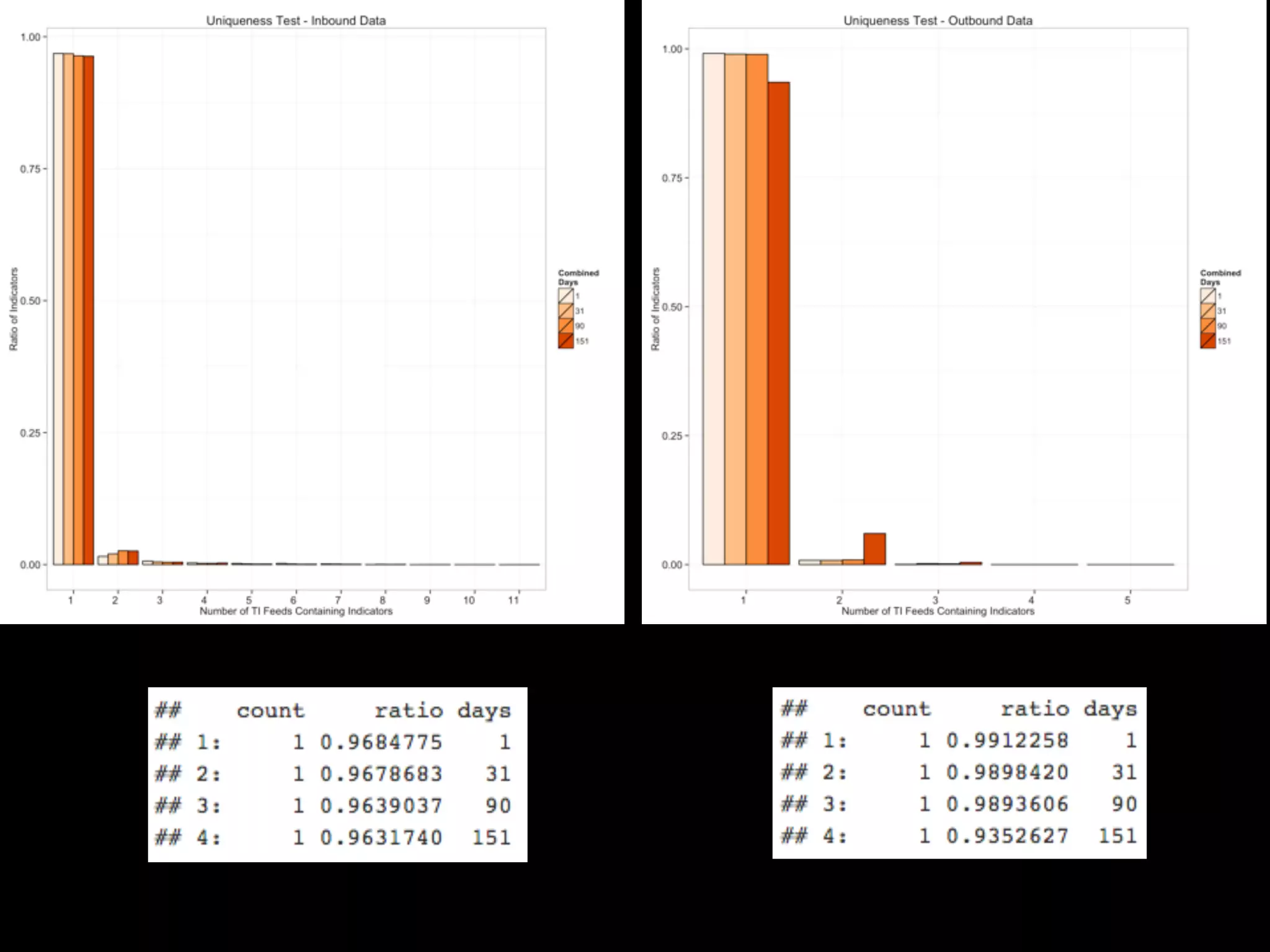
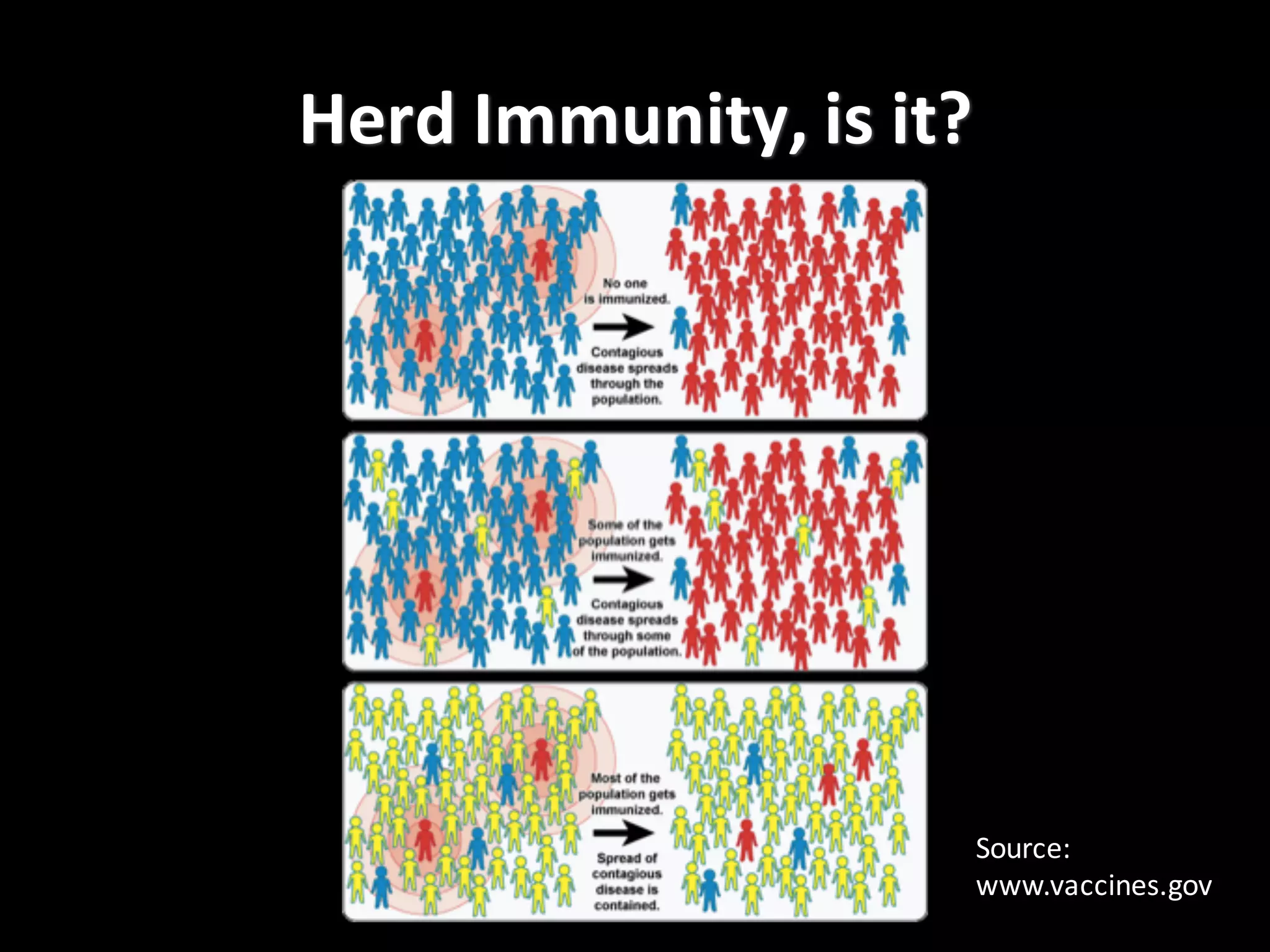
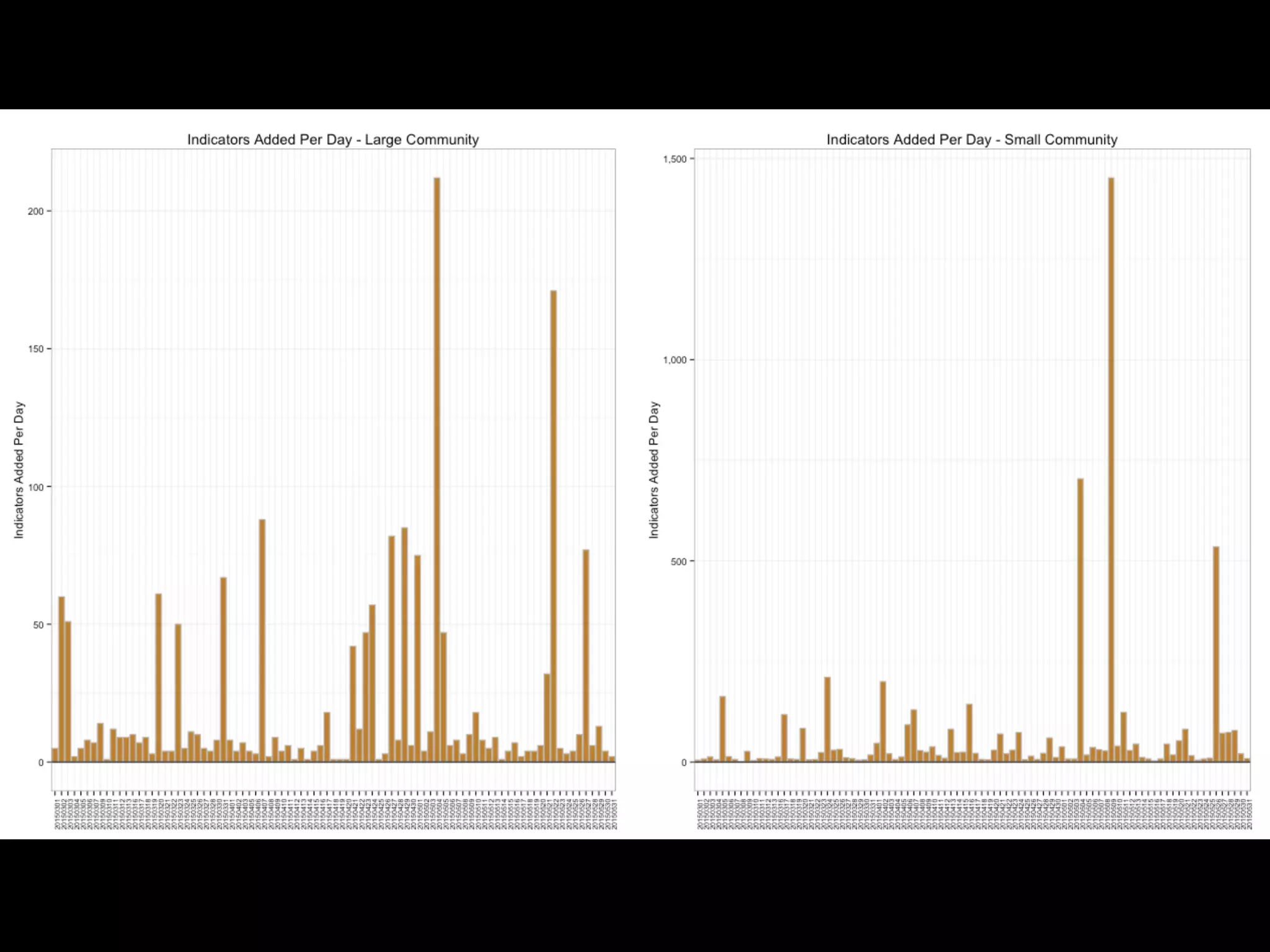
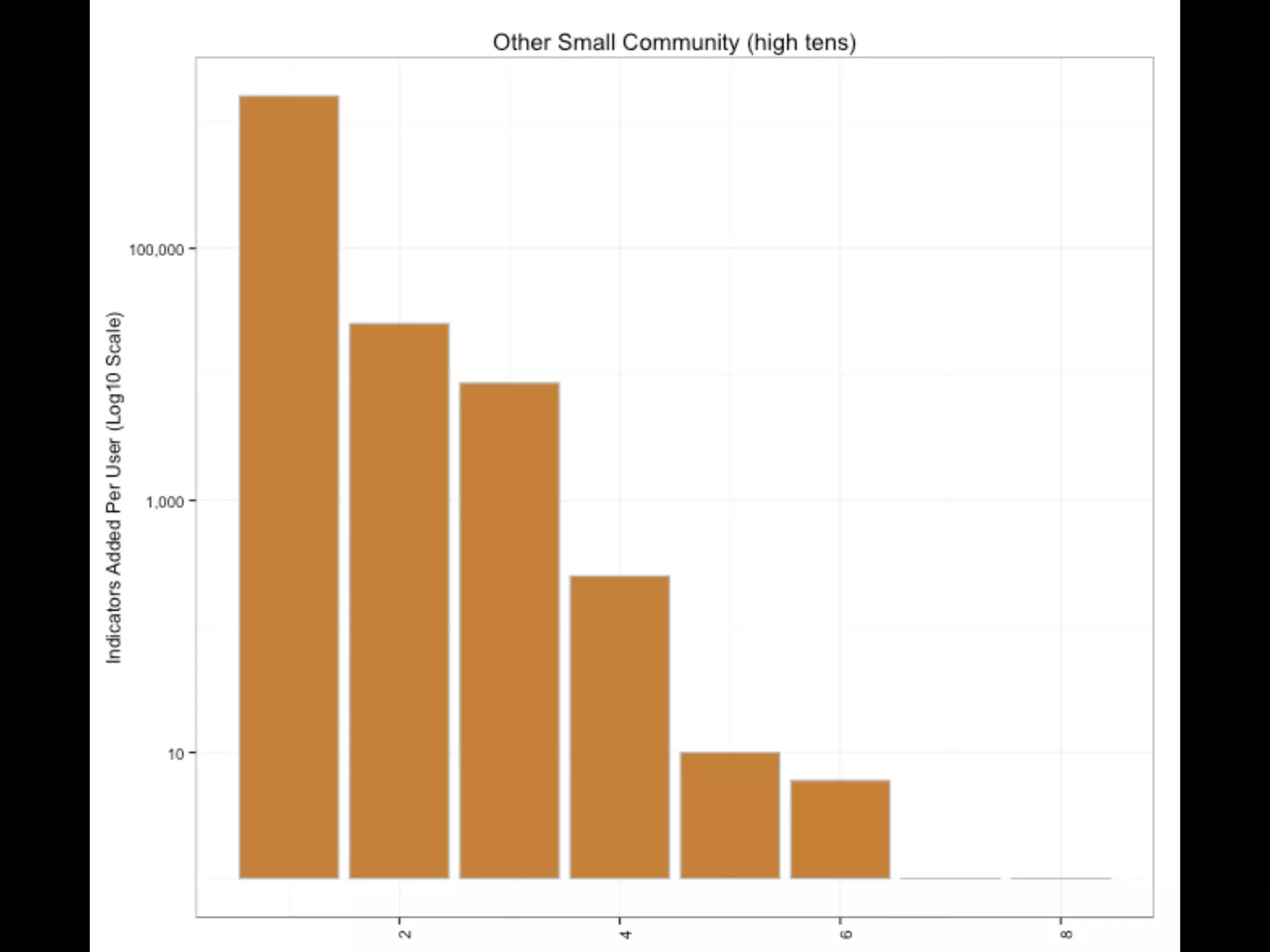
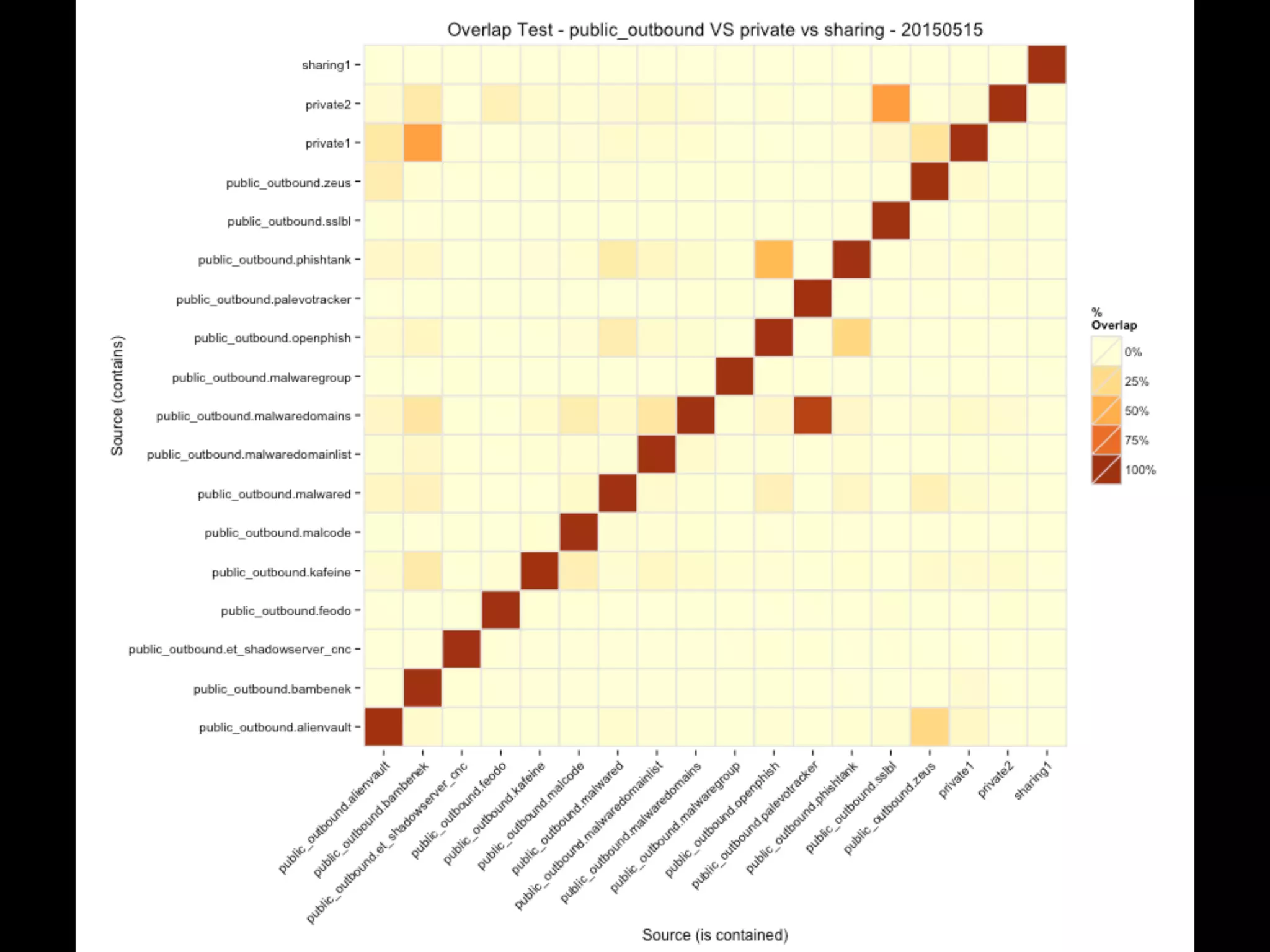
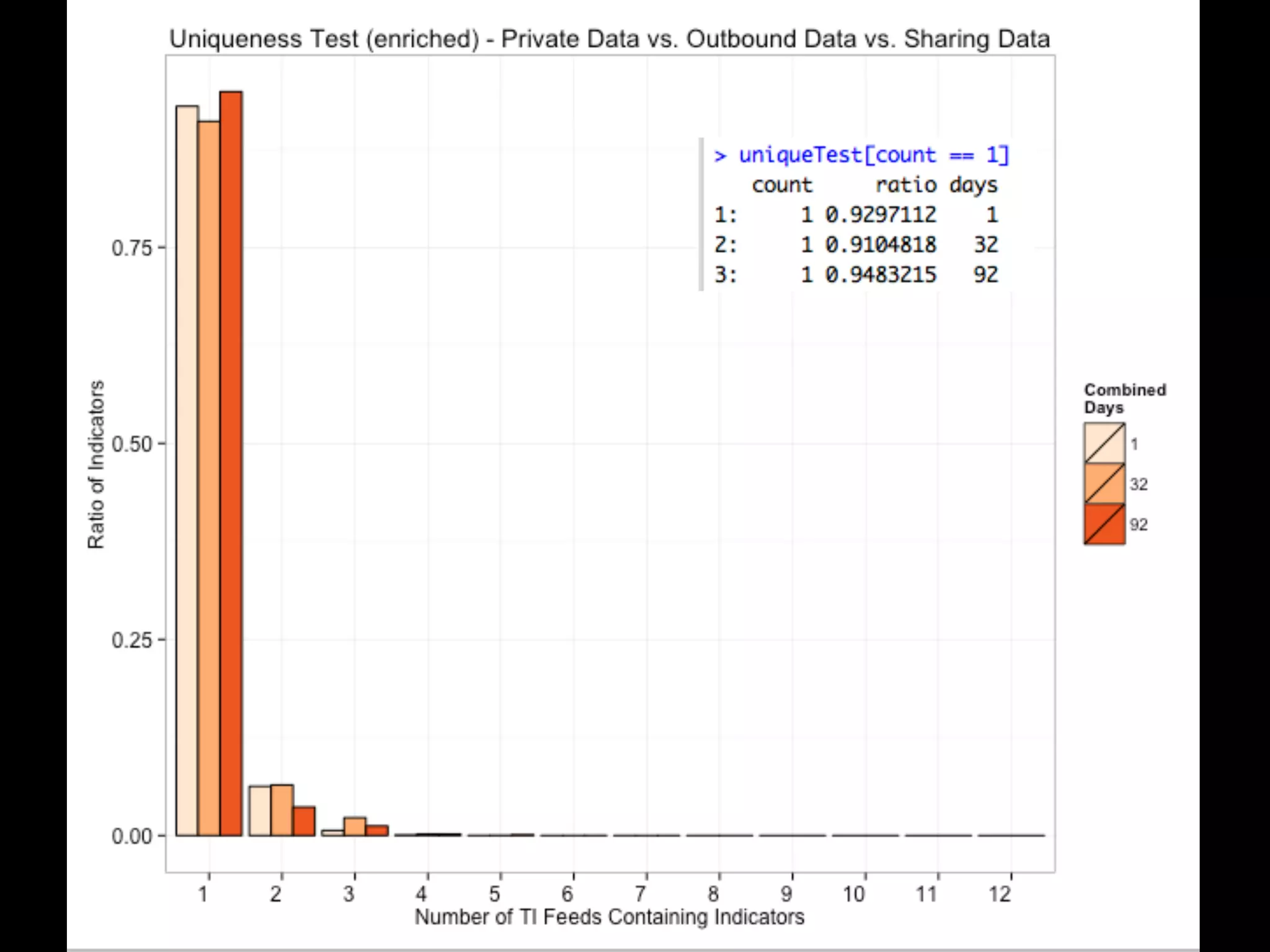
This document discusses metrics for measuring threat intelligence indicator dissemination and sharing. It presents analysis using the Combine and TIQ-Test tools to evaluate novelty, aging, population overlap and uniqueness of indicators in inbound and outbound intelligence feeds. Key findings include that more data does not necessarily mean better, telemetry about attacks is more useful than raw indicators, and maturity in sharing communities impacts their effectiveness.