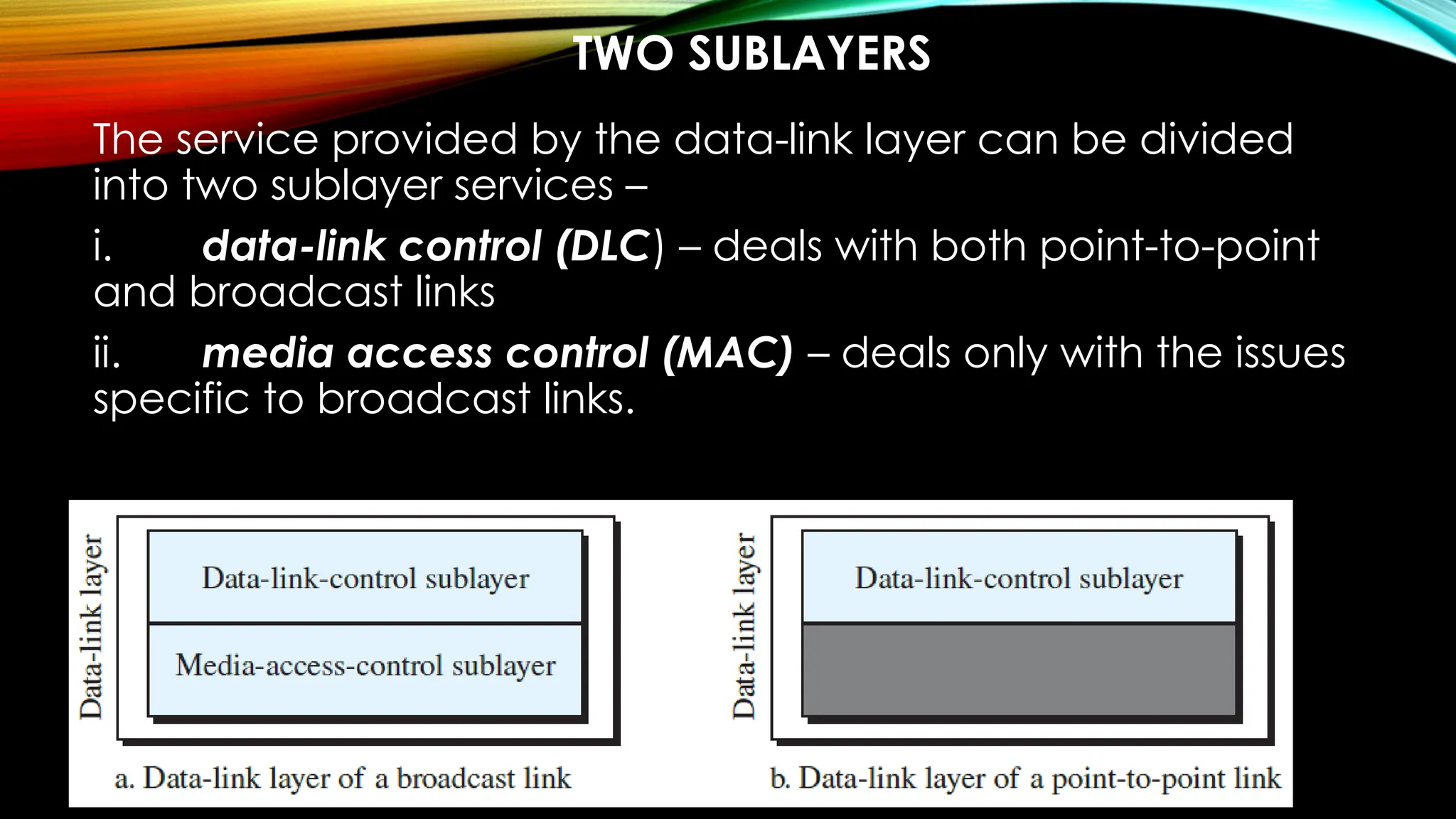
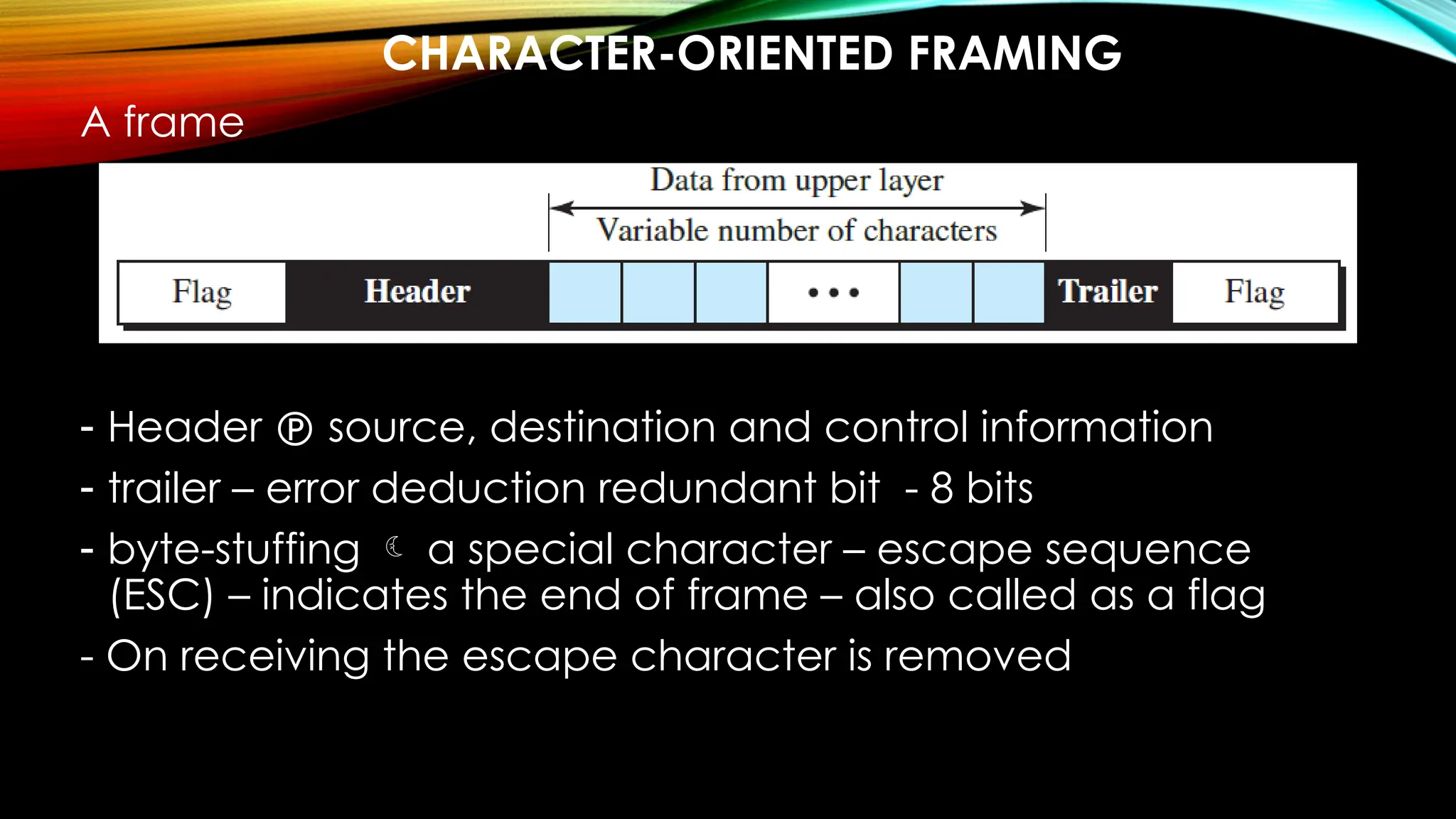
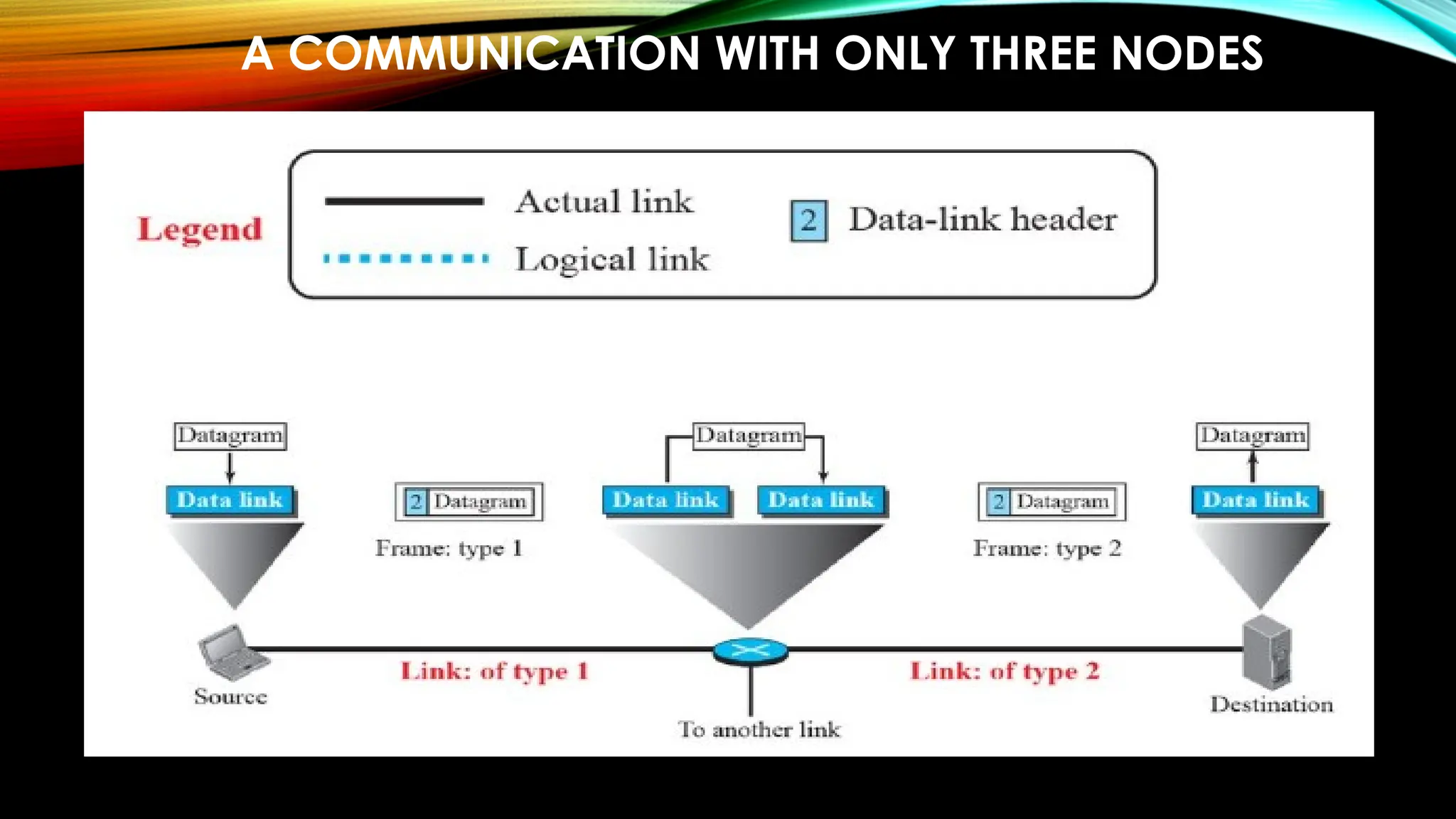
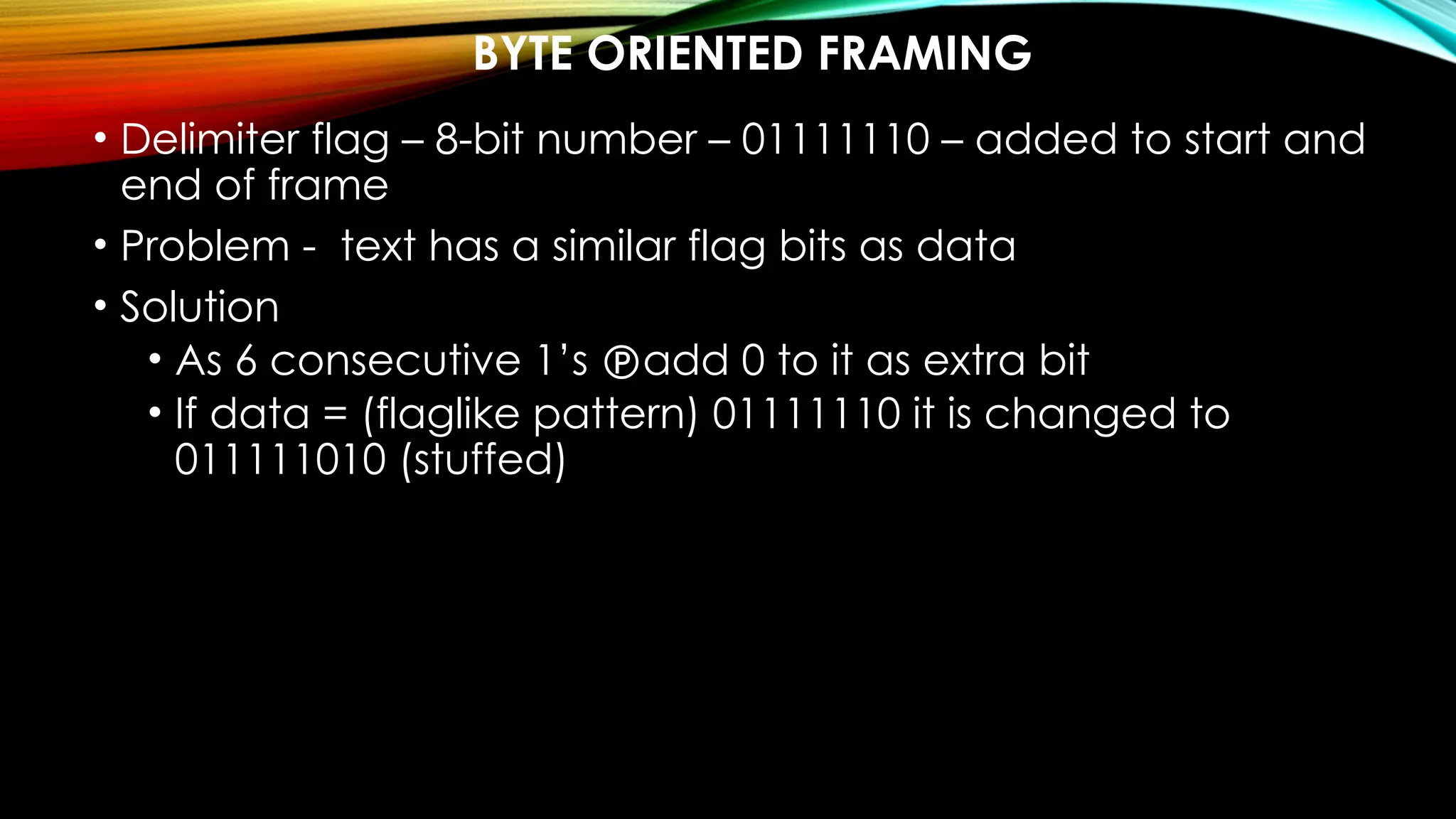
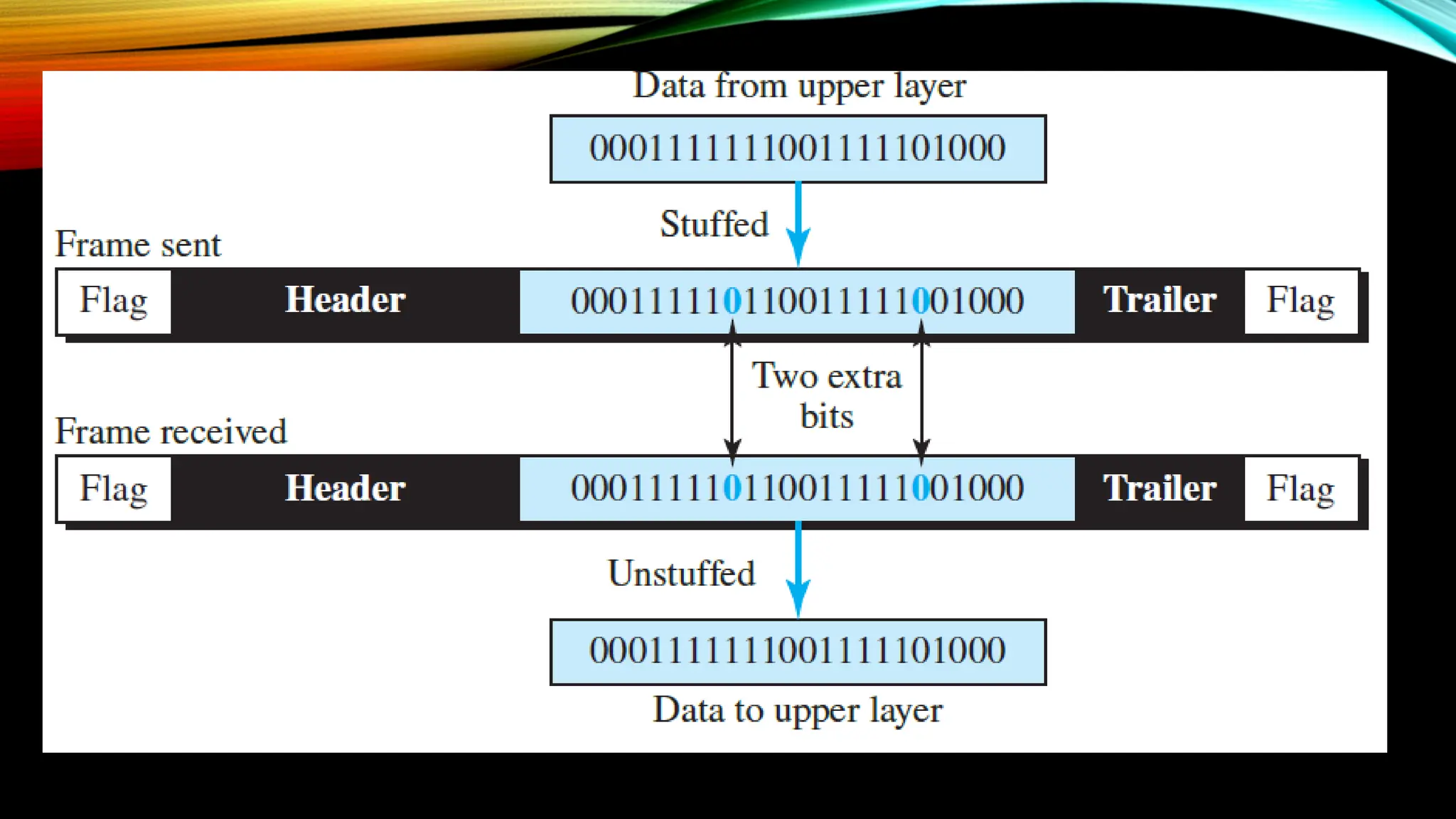
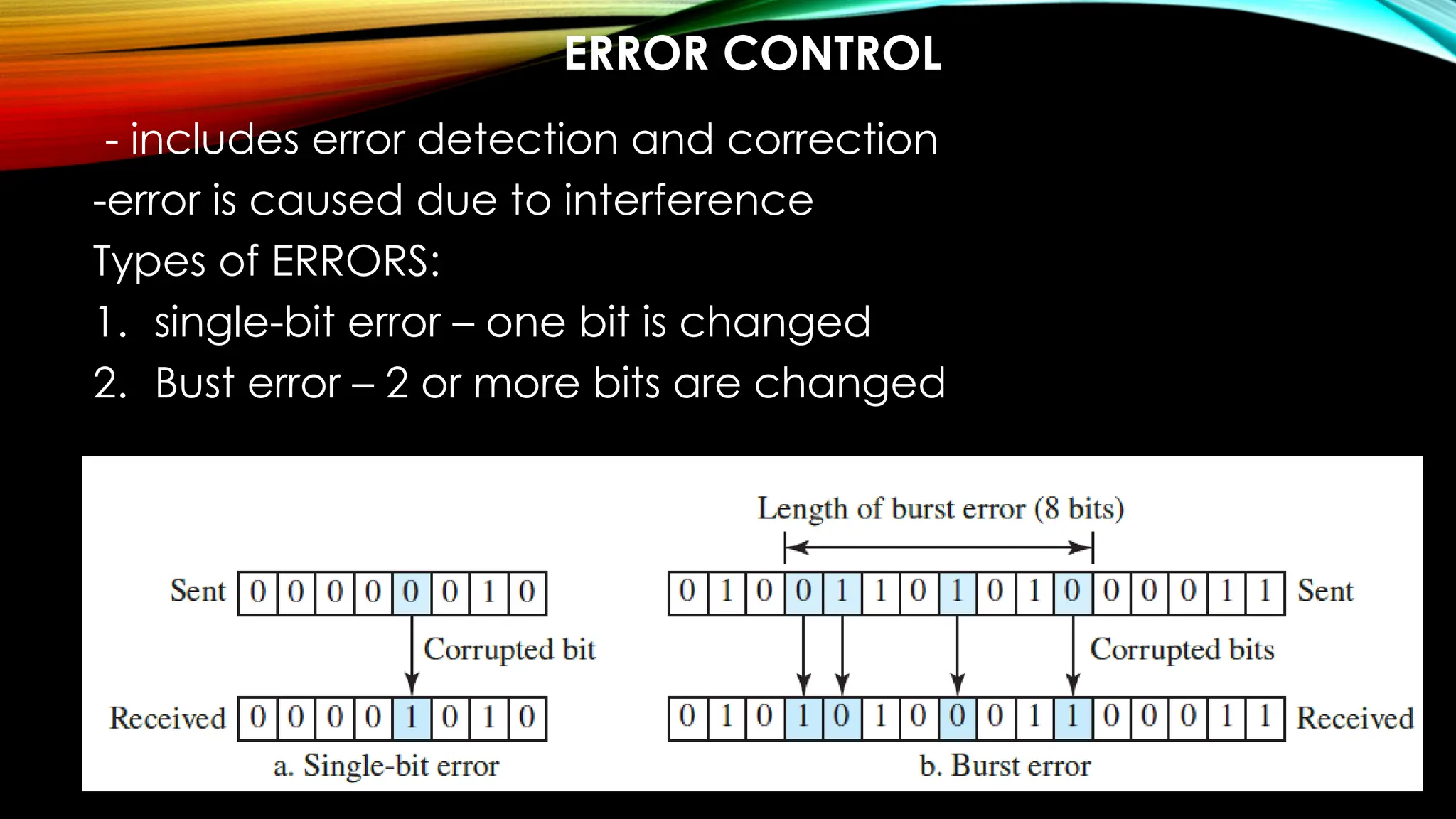
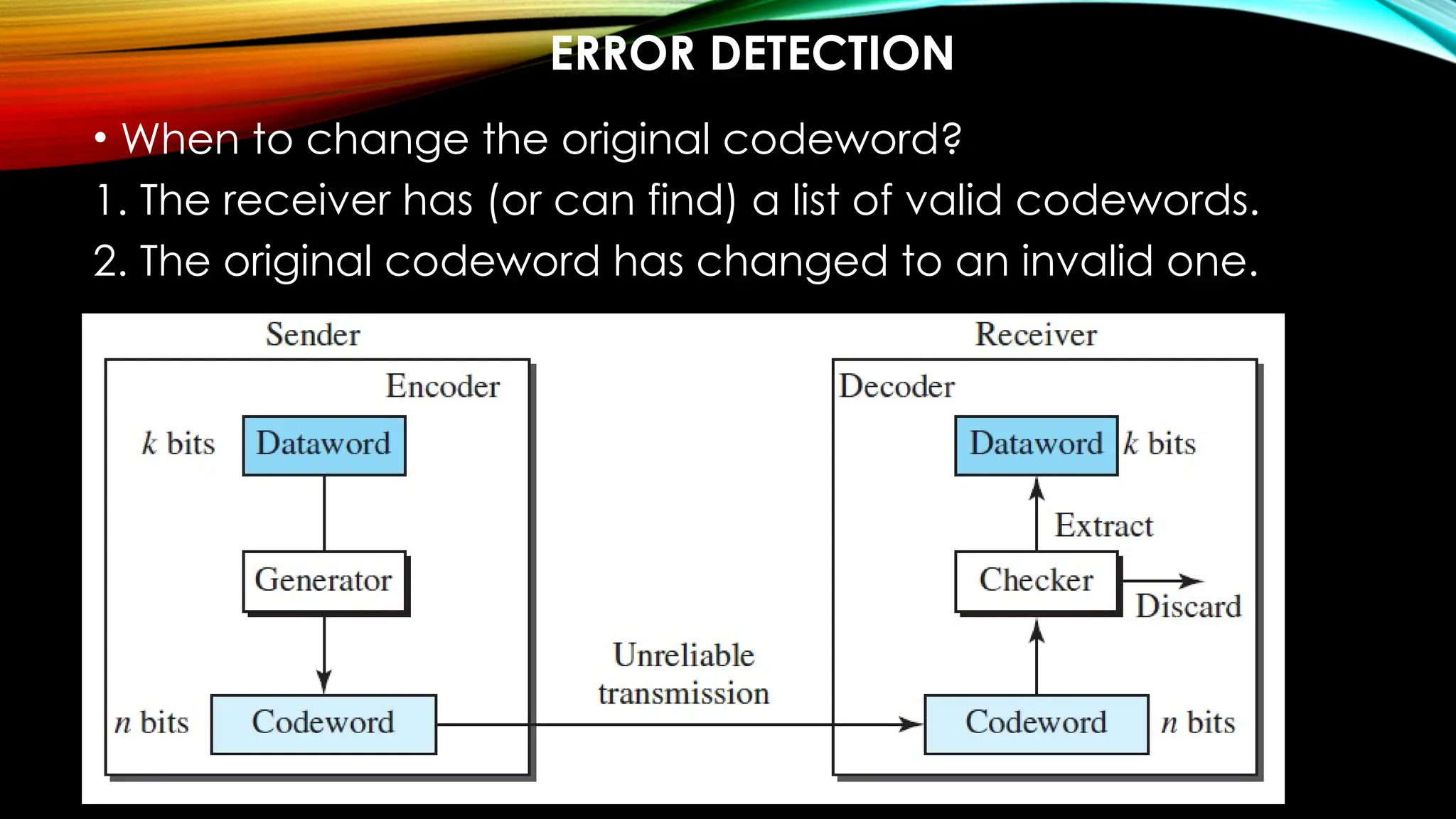
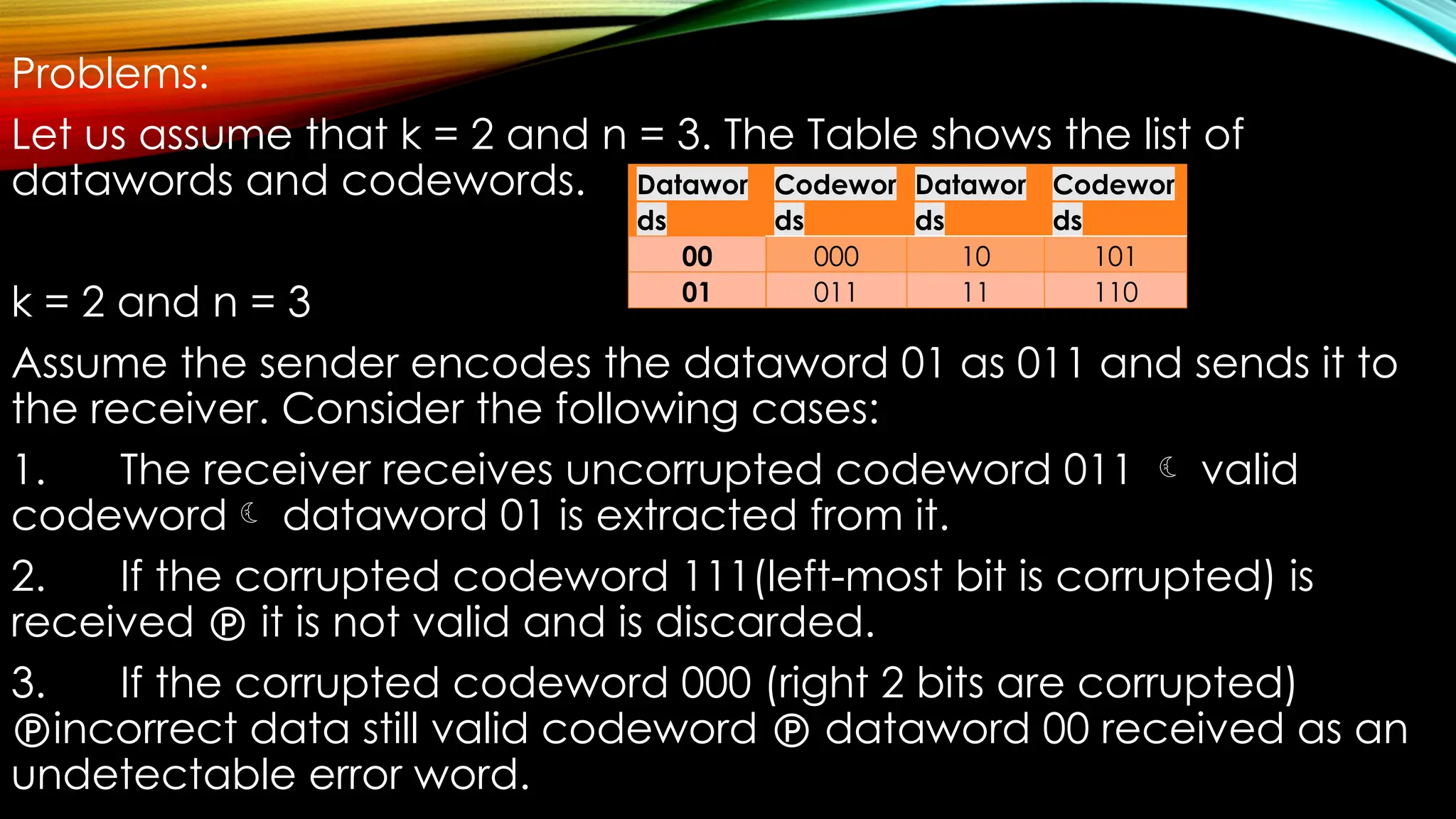
The document covers the data link layer of networking, explaining the structure and transmission of data units such as packets and frames, as well as concepts like fragmentation, flow control, and error control. It details the roles of data link control (DLC) and media access control (MAC) in managing node-to-node communication and addressing. The document also discusses error detection and correction techniques, including block coding and Hamming distance, highlighting how redundancy is used to ensure data integrity during transmission.