The document outlines a general product direction from Oracle that is intended for informational purposes only and should not be relied upon for purchasing decisions. Any features or functionality described are subject to change at Oracle's sole discretion. Statements in the presentation relating to Oracle's future plans are forward-looking statements subject to risks and uncertainties detailed in Oracle's SEC filings. All information is current as of September 2019 and Oracle undertakes no duty to update any statements. The document is protected by copyright law.
![CSI (Crash Scene Investigation) HotSpot:
Common JVM Crash Causes and Solutions
[DEV4421]
Principal Member of Technical Staff
Java Platform Group
September 17, 2019
David Buck
Copyright © 2019 Oracle and/or its affiliates.](https://image.slidesharecdn.com/oco19crash-191015115653/75/CSI-Crash-Scene-Investigation-HotSpot-Common-JVM-Crash-Causes-and-Solutions-Code-One-2019-2-2048.jpg)
![Insurance Institute
for Highway Safety
[CC BY-SA 3.0
(https://creativecom
mons.org/licenses/by
-sa/3.0)]](https://image.slidesharecdn.com/oco19crash-191015115653/75/CSI-Crash-Scene-Investigation-HotSpot-Common-JVM-Crash-Causes-and-Solutions-Code-One-2019-4-2048.jpg)







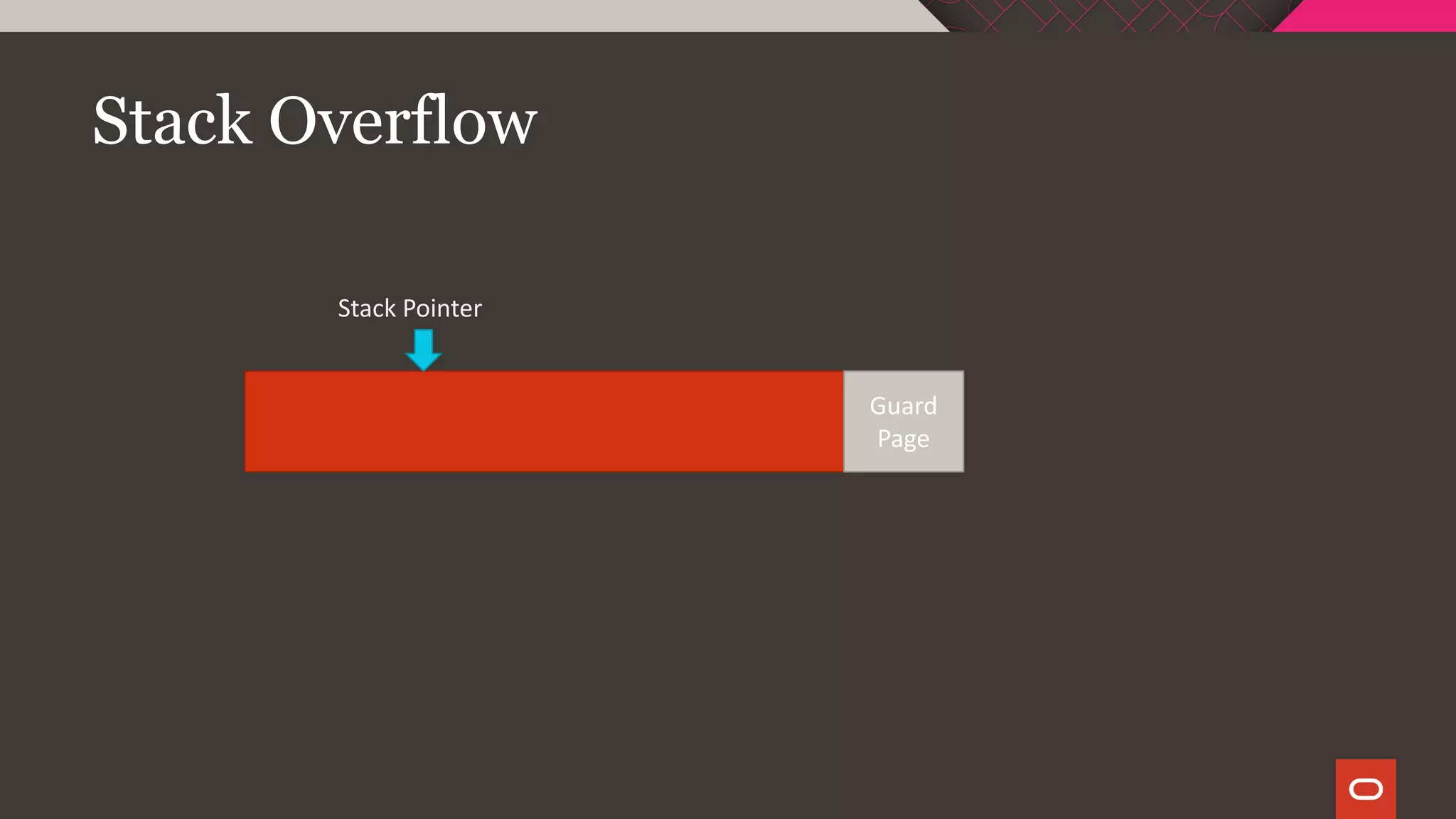
![Stack Overflow
Red
Pages
Stack Pointer
Yellow
Pages
[guard page]
○ Read
○ Write
× Execute
× Read
× Write
× Execute
× Read
× Write
× Execute](https://image.slidesharecdn.com/oco19crash-191015115653/75/CSI-Crash-Scene-Investigation-HotSpot-Common-JVM-Crash-Causes-and-Solutions-Code-One-2019-32-2048.jpg)
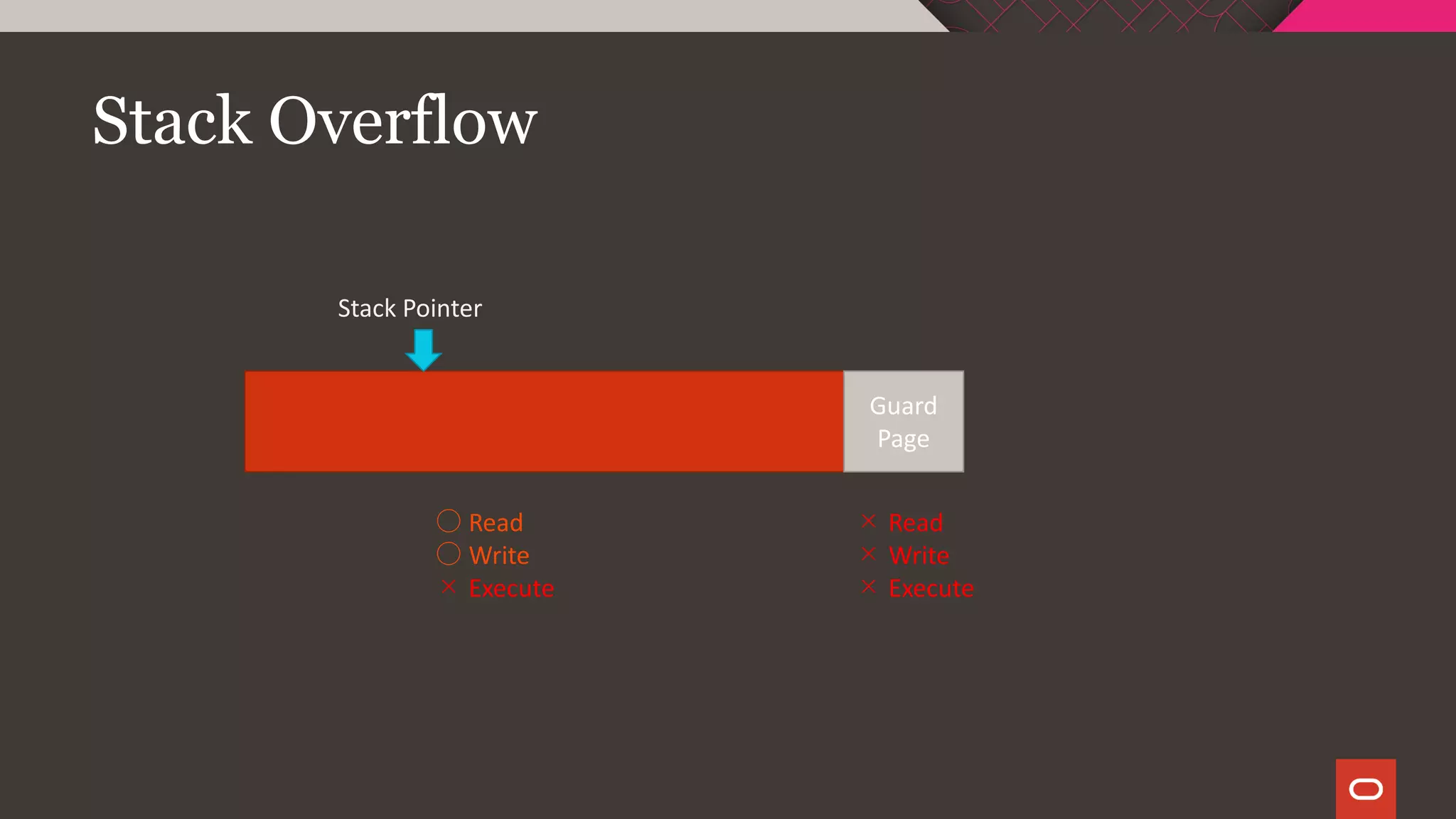
![Stack Overflow
Red
Pages
Stack Pointer
Yellow
Pages
[guard page]
○ Read
○ Write
× Execute
× Read
× Write
× Execute
× Read
× Write
× Execute](https://image.slidesharecdn.com/oco19crash-191015115653/75/CSI-Crash-Scene-Investigation-HotSpot-Common-JVM-Crash-Causes-and-Solutions-Code-One-2019-33-2048.jpg)
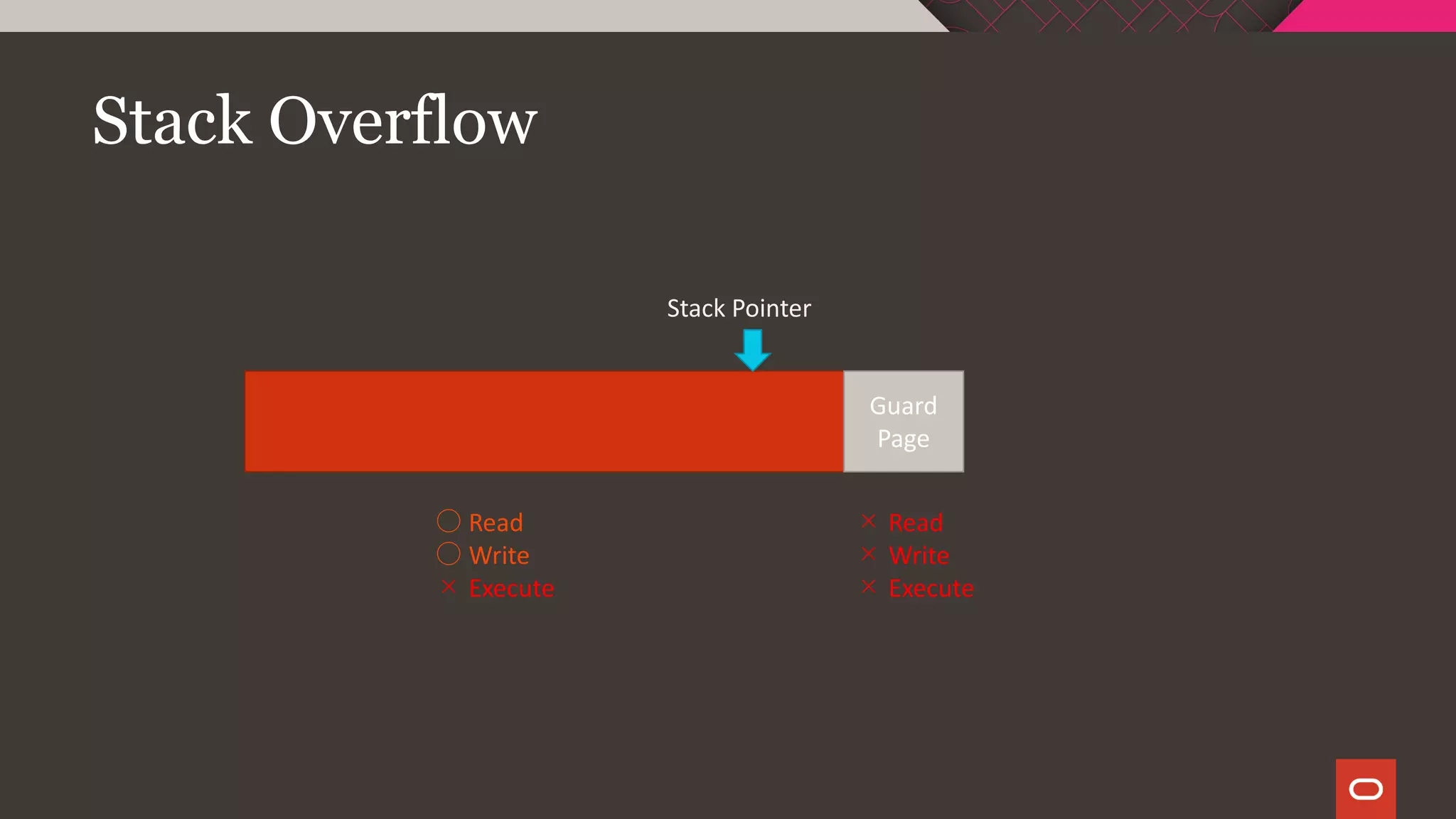
![Stack Overflow
Red
Pages
Stack Pointer
Yellow
Pages
[guard page]
○ Read
○ Write
× Execute
× Read
× Write
× Execute
× Read
× Write
× Execute
SIGSEGV](https://image.slidesharecdn.com/oco19crash-191015115653/75/CSI-Crash-Scene-Investigation-HotSpot-Common-JVM-Crash-Causes-and-Solutions-Code-One-2019-34-2048.jpg)
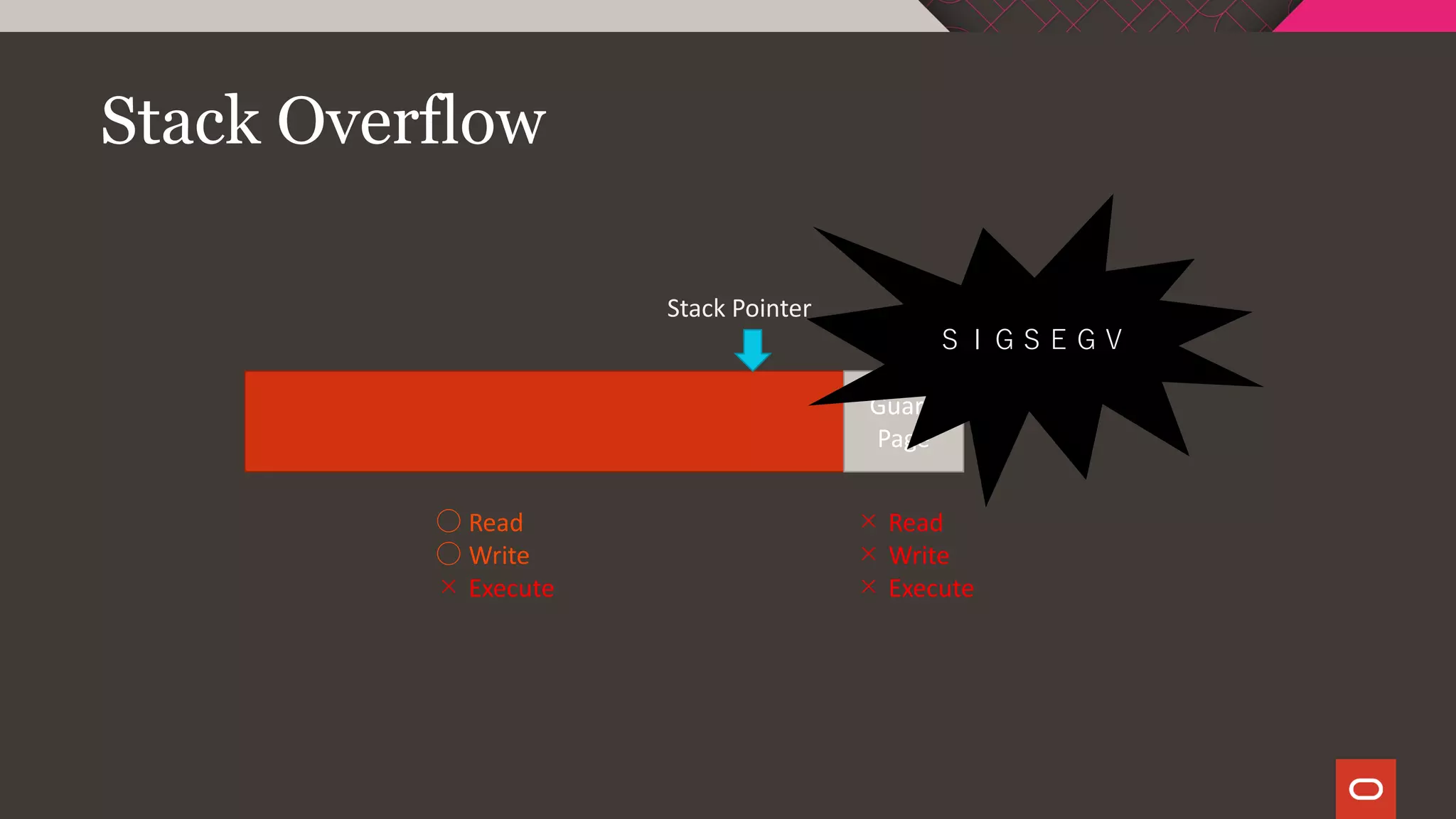
![Stack Overflow
Red
Pages
Stack Pointer
Yellow
Pages
[guard page]
○ Read
○ Write
× Execute
○ Read
○ Write
× Execute
× Read
× Write
× Execute
StackOverFlowError](https://image.slidesharecdn.com/oco19crash-191015115653/75/CSI-Crash-Scene-Investigation-HotSpot-Common-JVM-Crash-Causes-and-Solutions-Code-One-2019-35-2048.jpg)
![Stack Overflow
Red
Pages
Stack Pointer
Yellow
Pages
[guard page]
○ Read
○ Write
× Execute
× Read
× Write
× Execute
× Read
× Write
× Execute](https://image.slidesharecdn.com/oco19crash-191015115653/75/CSI-Crash-Scene-Investigation-HotSpot-Common-JVM-Crash-Causes-and-Solutions-Code-One-2019-36-2048.jpg)
![Stack Banging
Red
Pages
Stack Pointer
Yellow
Pages
[guard page]
○ Read
○ Write
× Execute
× Read
× Write
× Execute
× Read
× Write
× Execute](https://image.slidesharecdn.com/oco19crash-191015115653/75/CSI-Crash-Scene-Investigation-HotSpot-Common-JVM-Crash-Causes-and-Solutions-Code-One-2019-39-2048.jpg)
![Stack Banging
Red
Pages
Stack Pointer
Yellow
Pages
[guard page]
○ Read
○ Write
× Execute
× Read
× Write
× Execute
× Read
× Write
× Execute](https://image.slidesharecdn.com/oco19crash-191015115653/75/CSI-Crash-Scene-Investigation-HotSpot-Common-JVM-Crash-Causes-and-Solutions-Code-One-2019-40-2048.jpg)
![Stack Banging
Red
Pages
Stack Pointer
Yellow
Pages
[guard page]
○ Read
○ Write
× Execute
× Read
× Write
× Execute
× Read
× Write
× Execute
StackOverFlowError](https://image.slidesharecdn.com/oco19crash-191015115653/75/CSI-Crash-Scene-Investigation-HotSpot-Common-JVM-Crash-Causes-and-Solutions-Code-One-2019-41-2048.jpg)
![Stack Overflow
Red
Pages
Stack Pointer
Yellow
Pages
[guard page]
○ Read
○ Write
× Execute
× Read
× Write
× Execute
× Read
× Write
× Execute](https://image.slidesharecdn.com/oco19crash-191015115653/75/CSI-Crash-Scene-Investigation-HotSpot-Common-JVM-Crash-Causes-and-Solutions-Code-One-2019-43-2048.jpg)
![Stack Overflow
Red
Pages
Stack Pointer
Yellow
Pages
[guard page]
○ Read
○ Write
× Execute
× Read
× Write
× Execute
× Read
× Write
× Execute](https://image.slidesharecdn.com/oco19crash-191015115653/75/CSI-Crash-Scene-Investigation-HotSpot-Common-JVM-Crash-Causes-and-Solutions-Code-One-2019-44-2048.jpg)
![Stack Overflow
Red
Pages
Stack Pointer
Yellow
Pages
[guard page]
○ Read
○ Write
× Execute
× Read
× Write
× Execute
× Read
× Write
× Execute](https://image.slidesharecdn.com/oco19crash-191015115653/75/CSI-Crash-Scene-Investigation-HotSpot-Common-JVM-Crash-Causes-and-Solutions-Code-One-2019-45-2048.jpg)
![Stack Overflow
Red
Pages
Stack Pointer
Yellow
Pages
[guard page]
○ Read
○ Write
× Execute
× Read
× Write
× Execute
× Read
× Write
× Execute
??????????????](https://image.slidesharecdn.com/oco19crash-191015115653/75/CSI-Crash-Scene-Investigation-HotSpot-Common-JVM-Crash-Causes-and-Solutions-Code-One-2019-46-2048.jpg)
![Stack Overflow
Red
Pages
Stack Pointer
Yellow
Pages
[guard page]
○ Read
○ Write
× Execute
× Read
× Write
× Execute
× Read
× Write
× Execute
??????????????](https://image.slidesharecdn.com/oco19crash-191015115653/75/CSI-Crash-Scene-Investigation-HotSpot-Common-JVM-Crash-Causes-and-Solutions-Code-One-2019-47-2048.jpg)
![Stack Overflow
Red
Pages
Stack Pointer
Yellow
Pages
[guard page]
○ Read
○ Write
× Execute
× Read
× Write
× Execute
× Read
× Write
× Execute
??????????????](https://image.slidesharecdn.com/oco19crash-191015115653/75/CSI-Crash-Scene-Investigation-HotSpot-Common-JVM-Crash-Causes-and-Solutions-Code-One-2019-48-2048.jpg)


![Native Code – Signal Handling
Native code may install its own signal handlers
HotSpot makes heavy use of signals internally
Error log will list any handlers installed for signals we care about:
Signal Handlers:
…
SIGILL: [libjvm.so+0x8c1cb0],
sa_mask[0]=11111111011111111101111111111110,
sa_flags=SA_RESTART|SA_SIGINFO
SIGUSR1: SIG_DFL,
sa_mask[0]=00000000000000000000000000000000,
sa_flags=none
…](https://image.slidesharecdn.com/oco19crash-191015115653/75/CSI-Crash-Scene-Investigation-HotSpot-Common-JVM-Crash-Causes-and-Solutions-Code-One-2019-74-2048.jpg)
![Native Code – Signal Handling
Native code may install its own signal handlers
HotSpot makes heavy use of signals internally
Error log will list any handlers installed for signals we care about:
Signal Handlers:
…
SIGILL: [libjvm.so+0x8c1cb0],
sa_mask[0]=11111111011111111101111111111110,
sa_flags=SA_RESTART|SA_SIGINFO
SIGUSR1: SIG_DFL,
sa_mask[0]=00000000000000000000000000000000,
sa_flags=none
…](https://image.slidesharecdn.com/oco19crash-191015115653/75/CSI-Crash-Scene-Investigation-HotSpot-Common-JVM-Crash-Causes-and-Solutions-Code-One-2019-75-2048.jpg)
![Native Code – Signal Handling
Native code may install its own signal handlers
HotSpot makes heavy use of signals internally
Error log will list any handlers installed for signals we care about:
Signal Handlers:
…
SIGILL: [libyourmom.so+0x8c1cb0],
sa_mask[0]=11111111011111111101111111111110,
sa_flags=SA_RESTART|SA_SIGINFO
SIGUSR1: SIG_DFL,
sa_mask[0]=00000000000000000000000000000000,
sa_flags=none
…](https://image.slidesharecdn.com/oco19crash-191015115653/75/CSI-Crash-Scene-Investigation-HotSpot-Common-JVM-Crash-Causes-and-Solutions-Code-One-2019-76-2048.jpg)

![Memory Exhaustion
Get Rid of OutOfMemoryError Messages [DEV3420]
Poonam Parhar
Thursday, September 19, 12:15 PM - 01:00 PM | Moscone South - Room
304
Troubleshooting Native Memory Leaks in Java Applications
CodeOne 2018
Slides available on-line
Poonam’s blog has great related content](https://image.slidesharecdn.com/oco19crash-191015115653/75/CSI-Crash-Scene-Investigation-HotSpot-Common-JVM-Crash-Causes-and-Solutions-Code-One-2019-82-2048.jpg)


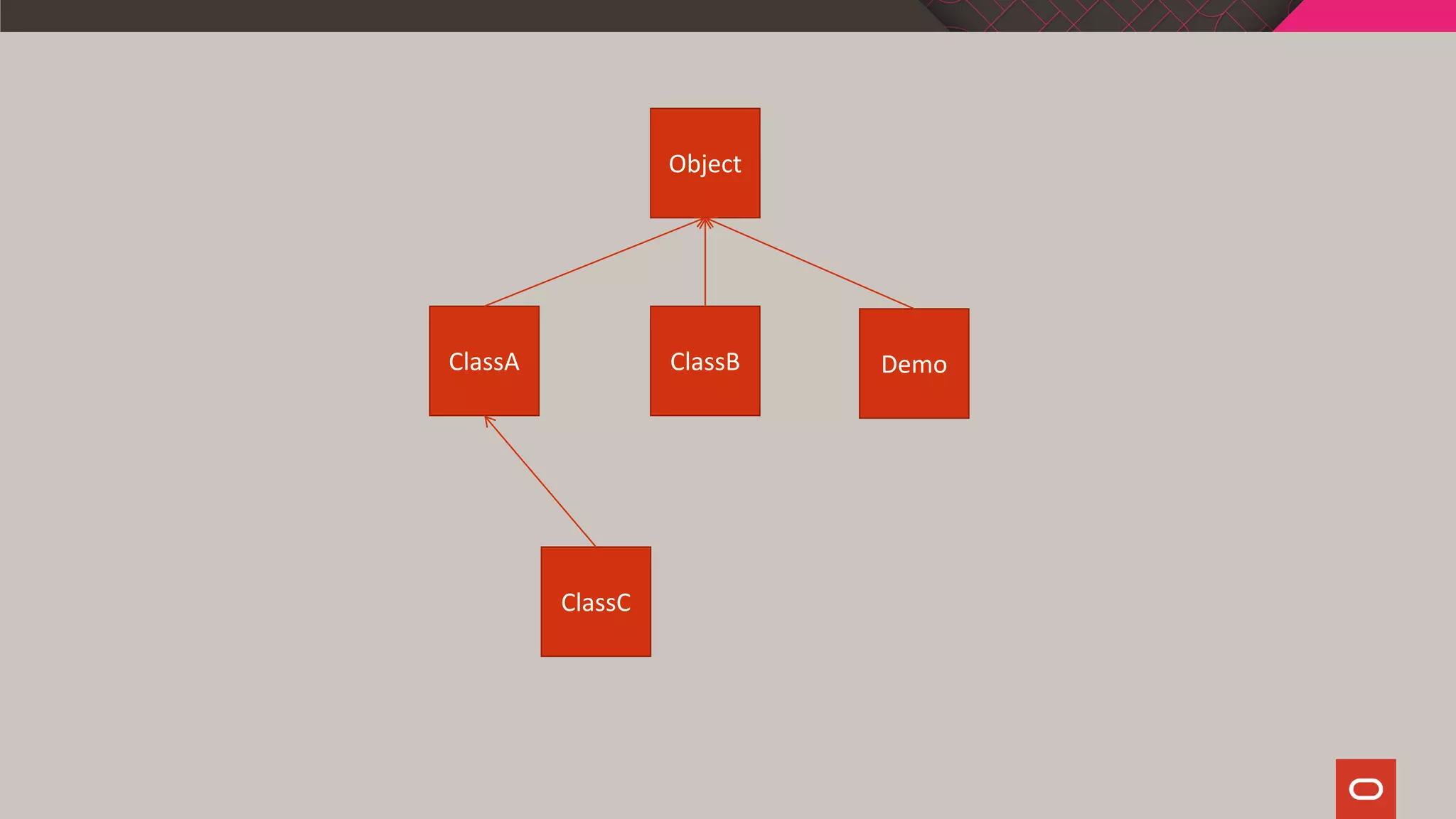
![Demo
public class Demo {
public static void main(String[] args) {
ClassA obj = new ClassC();
System.out.println(obj.doSomething(1,2,3));
}
}](https://image.slidesharecdn.com/oco19crash-191015115653/75/CSI-Crash-Scene-Investigation-HotSpot-Common-JVM-Crash-Causes-and-Solutions-Code-One-2019-88-2048.jpg)
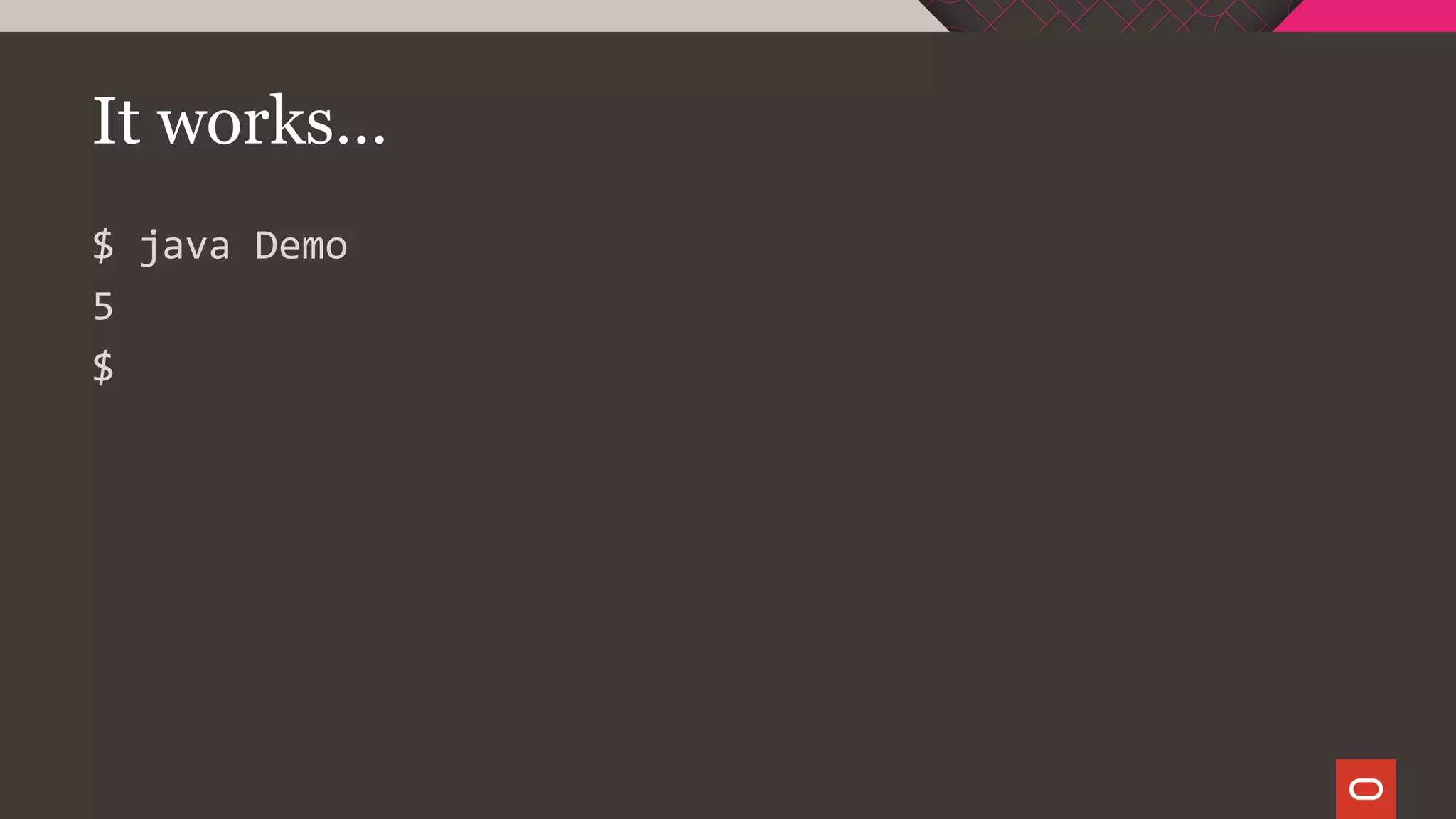
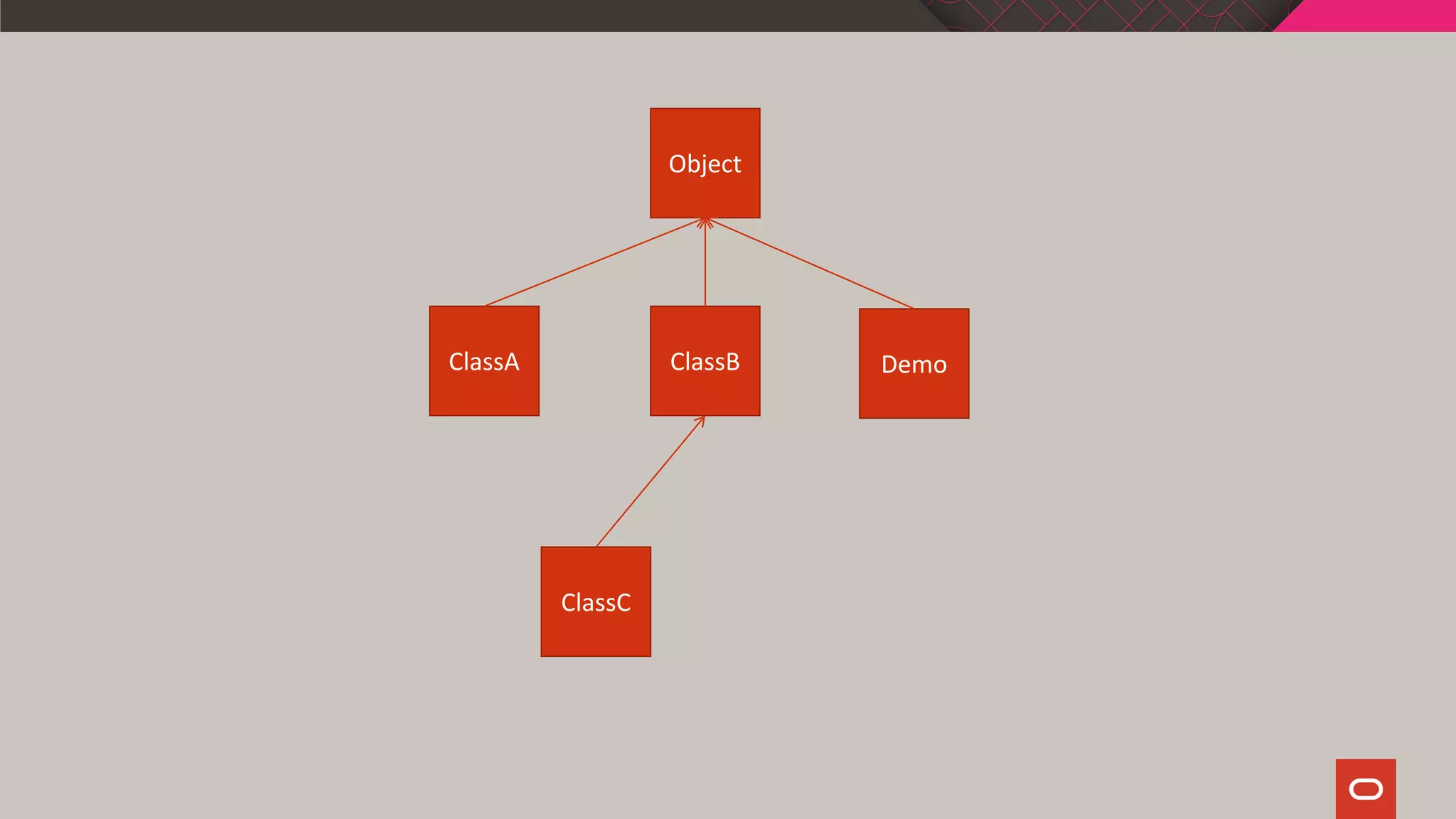
![Demo
public class Demo {
public static void main(String[] args) {
ClassA obj = new ClassC();
System.out.println(obj.doSomething(1,2,3));
}
}](https://image.slidesharecdn.com/oco19crash-191015115653/75/CSI-Crash-Scene-Investigation-HotSpot-Common-JVM-Crash-Causes-and-Solutions-Code-One-2019-95-2048.jpg)
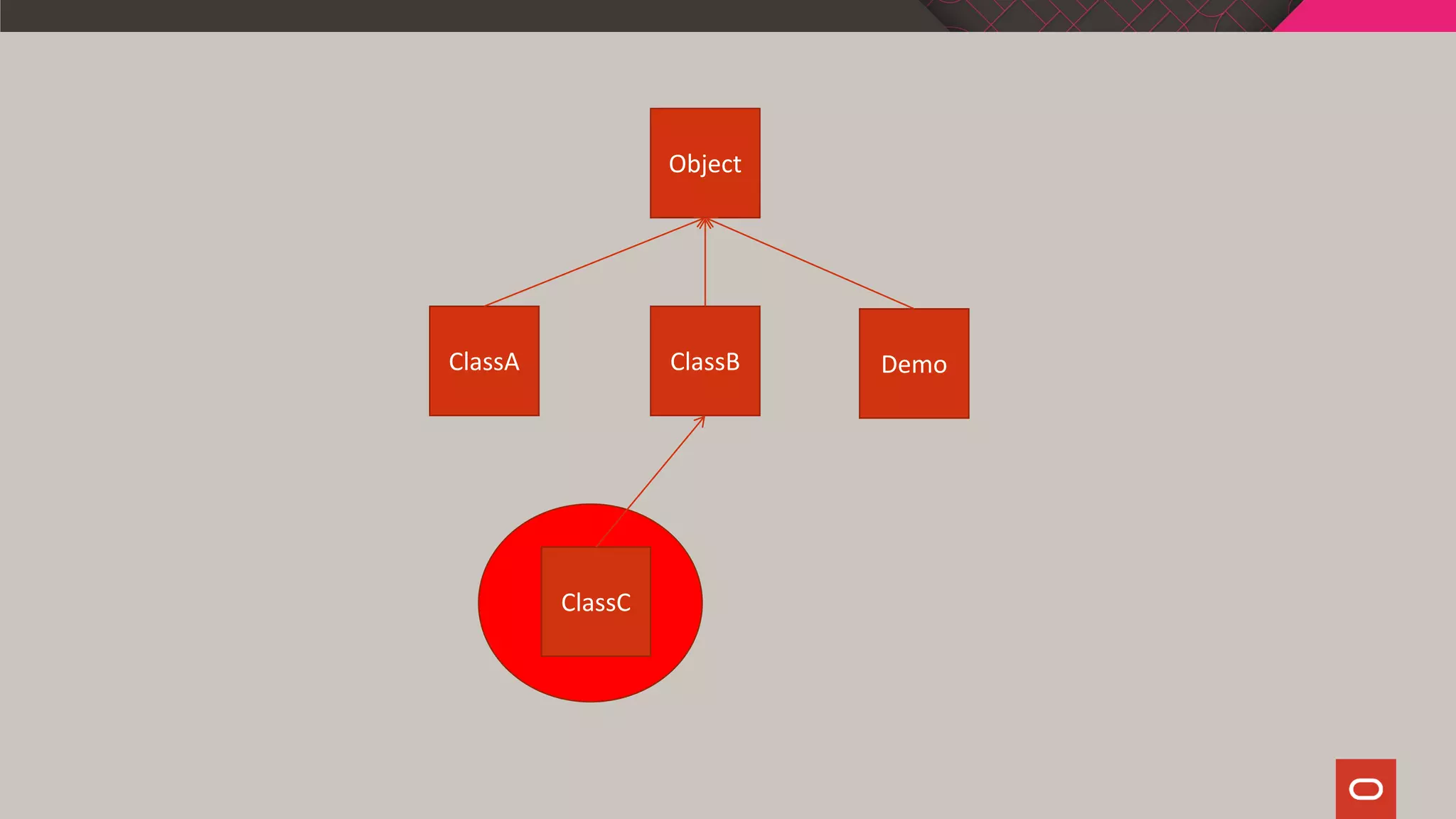
![$ java Demo
Error: A JNI error has occurred, please check your installation and try again
Exception in thread "main" java.lang.VerifyError: Bad type on operand stack
Exception Details:
Location:
Demo.main([Ljava/lang/String;)V @15: invokevirtual
Reason:
Type 'ClassC' (current frame, stack[1]) is not assignable to 'ClassA'
Current Frame:
bci: @15
flags: { }
locals: { '[Ljava/lang/String;', 'ClassC' }
stack: { 'java/io/PrintStream', 'ClassC', integer, integer, integer }
Bytecode:
0x0000000: bb00 0259 b700 034c b200 042b 0405 06b6
0x0000010: 0005 b600 06b1
at java.lang.Class.getDeclaredMethods0(Native Method)
at java.lang.Class.privateGetDeclaredMethods(Class.java:2701)
at java.lang.Class.privateGetMethodRecursive(Class.java:3048)
at java.lang.Class.getMethod0(Class.java:3018)
at java.lang.Class.getMethod(Class.java:1784)](https://image.slidesharecdn.com/oco19crash-191015115653/75/CSI-Crash-Scene-Investigation-HotSpot-Common-JVM-Crash-Causes-and-Solutions-Code-One-2019-96-2048.jpg)
![We reap what we sow
[dbuck@dbuck02 demo1]$ java -Xverify:none Demo
#
# A fatal error has been detected by the Java Runtime Environment:
#
# SIGSEGV (0xb) at pc=0x00007fa93be7991c, pid=22925, tid=140364857087744
#
# JRE version: OpenJDK Runtime Environment (8.0_91-b14) (build 1.8.0_91-b14)
# Java VM: OpenJDK 64-Bit Server VM (25.91-b14 mixed mode linux-amd64 compressed oops)
# Problematic frame:
# V [libjvm.so+0x46391c]
#
# Core dump written. Default location: /home/dbuck/BCV_TOI/demo/demo1/core or core.22925
#
# An error report file with more information is saved as:
# /home/dbuck/BCV_TOI/demo/demo1/hs_err_pid22925.log
#
# If you would like to submit a bug report, please visit:
# http://bugreport.java.com/bugreport/crash.jsp
#
Aborted (core dumped)](https://image.slidesharecdn.com/oco19crash-191015115653/75/CSI-Crash-Scene-Investigation-HotSpot-Common-JVM-Crash-Causes-and-Solutions-Code-One-2019-99-2048.jpg)


![JIT Crash During Compilation
--------------- T H R E A D ---------------
Current thread (0x000000000061e800): JavaThread "C2
CompilerThread1" daemon [_thread_in_vm, id=12,
stack(0xfffffd7ef87fe000,0xfffffd7ef88fe000)]
Current CompileTask:
C2: 15252 9024 b 4
com.sun.crypto.provider.CipherCore::update (609
bytes)](https://image.slidesharecdn.com/oco19crash-191015115653/75/CSI-Crash-Scene-Investigation-HotSpot-Common-JVM-Crash-Causes-and-Solutions-Code-One-2019-109-2048.jpg)
![JIT Crash During Execution
Java Execution Thread (Not JIT compilation thread)
Stack: [0xfffffffcc8a00000,0xfffffffcc8b00000], sp=0xfffffffcc8afb780, free space=1005k
Native frames: (J=compiled Java code, j=interpreted, Vv=VM code, C=native code)
J oracle.j2ee.ws.wsdl.extensions.AbstractSerializer.startMarshall(Ljavax/wsdl/De
finition;Loracle/j2ee/ws/wsdl/util/XMLWriter;Ljavax/wsdl/extensions/Extensibil
ityElement;)V
j oracle.j2ee.ws.wsdl.extensions.addressing.EndpointReferenceSerializer.marshall
(Ljava/lang/Class;Ljavax/xml/namespace/QName;Ljavax/wsdl/extensions/Extensibil
ityElement;Ljava/io/PrintWriter;Ljavax/wsdl/Definition;Ljavax/wsdl/extensions/
ExtensionRegistry;)V+41](https://image.slidesharecdn.com/oco19crash-191015115653/75/CSI-Crash-Scene-Investigation-HotSpot-Common-JVM-Crash-Causes-and-Solutions-Code-One-2019-110-2048.jpg)
![JIT Crash During Execution
Java Execution Thread (Not JIT compilation thread)
Stack: [0xfffffffcc8a00000,0xfffffffcc8b00000], sp=0xfffffffcc8afb780, free space=1005k
Native frames: (J=compiled Java code, j=interpreted, Vv=VM code, C=native code)
J oracle.j2ee.ws.wsdl.extensions.AbstractSerializer.startMarshall(Ljavax/wsdl/De
finition;Loracle/j2ee/ws/wsdl/util/XMLWriter;Ljavax/wsdl/extensions/Extensibil
ityElement;)V
j oracle.j2ee.ws.wsdl.extensions.addressing.EndpointReferenceSerializer.marshall
(Ljava/lang/Class;Ljavax/xml/namespace/QName;Ljavax/wsdl/extensions/Extensibil
ityElement;Ljava/io/PrintWriter;Ljavax/wsdl/Definition;Ljavax/wsdl/extensions/
ExtensionRegistry;)V+41](https://image.slidesharecdn.com/oco19crash-191015115653/75/CSI-Crash-Scene-Investigation-HotSpot-Common-JVM-Crash-Causes-and-Solutions-Code-One-2019-111-2048.jpg)
![Other JIT Crashes
Compilation events (10 events):
Event: 15.131 Thread 0x000000000061e800 nmethod 9019 0xfffffd7fee3ecdd0 code [0xfffffd7fee3ed020,
0xfffffd7fee3eddd0]
Event: 15.131 Thread 0x000000000061c000 9020 b 4 javax.crypto.Cipher$Transform::matches (48 bytes)
Event: 15.143 Thread 0x000000000061c000 nmethod 9020 0xfffffd7fee3f3210 code [0xfffffd7fee3f3420,
0xfffffd7fee3f4030]
Event: 15.143 Thread 0x000000000061e800 9021 b 4 javax.crypto.Cipher::checkOpmode (21 bytes)
Event: 15.143 Thread 0x000000000061e800 nmethod 9021 0xfffffd7fee3f2990 code [0xfffffd7fee3f2ae0,
0xfffffd7fee3f2b38]
Event: 15.144 Thread 0x000000000061c000 9022 b 4 com.sun.crypto.provider.CipherCore::init (552 bytes)
Event: 15.150 Thread 0x000000000061c000 nmethod 9022 0xfffffd7fee3ebc90 code [0xfffffd7fee3ebe80,
0xfffffd7fee3ec5e0]
Event: 15.151 Thread 0x0000000000621000 9023 b 2 com.sun.crypto.provider.CipherCore::init (552 bytes)
Event: 15.153 Thread 0x0000000000621000 nmethod 9023 0xfffffd7feea17010 code [0xfffffd7feea17460,
0xfffffd7feea18d48]
Event: 15.182 Thread 0x000000000061e800 9024 b 4 com.sun.crypto.provider.CipherCore::update (609 bytes)](https://image.slidesharecdn.com/oco19crash-191015115653/75/CSI-Crash-Scene-Investigation-HotSpot-Common-JVM-Crash-Causes-and-Solutions-Code-One-2019-112-2048.jpg)