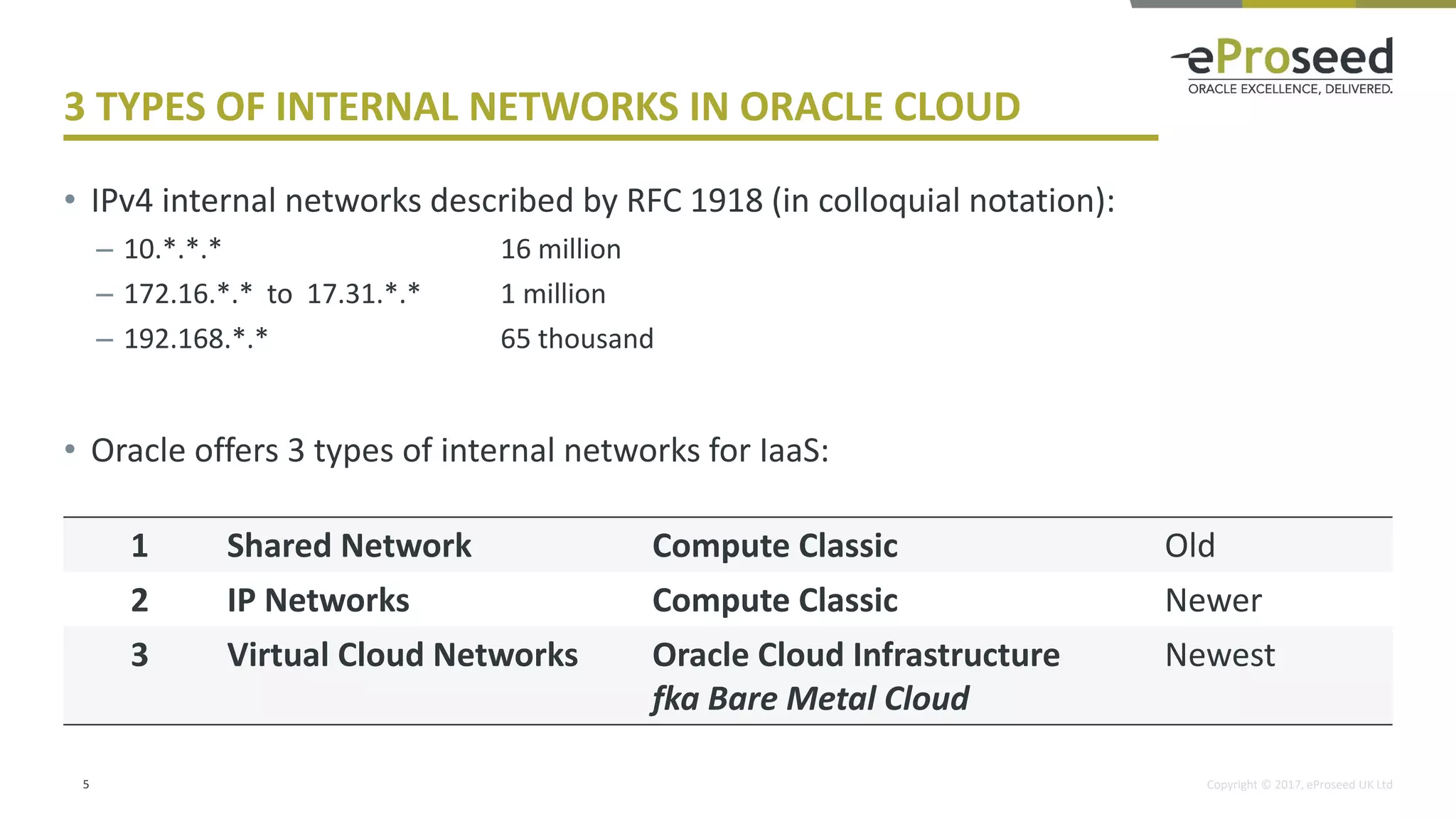
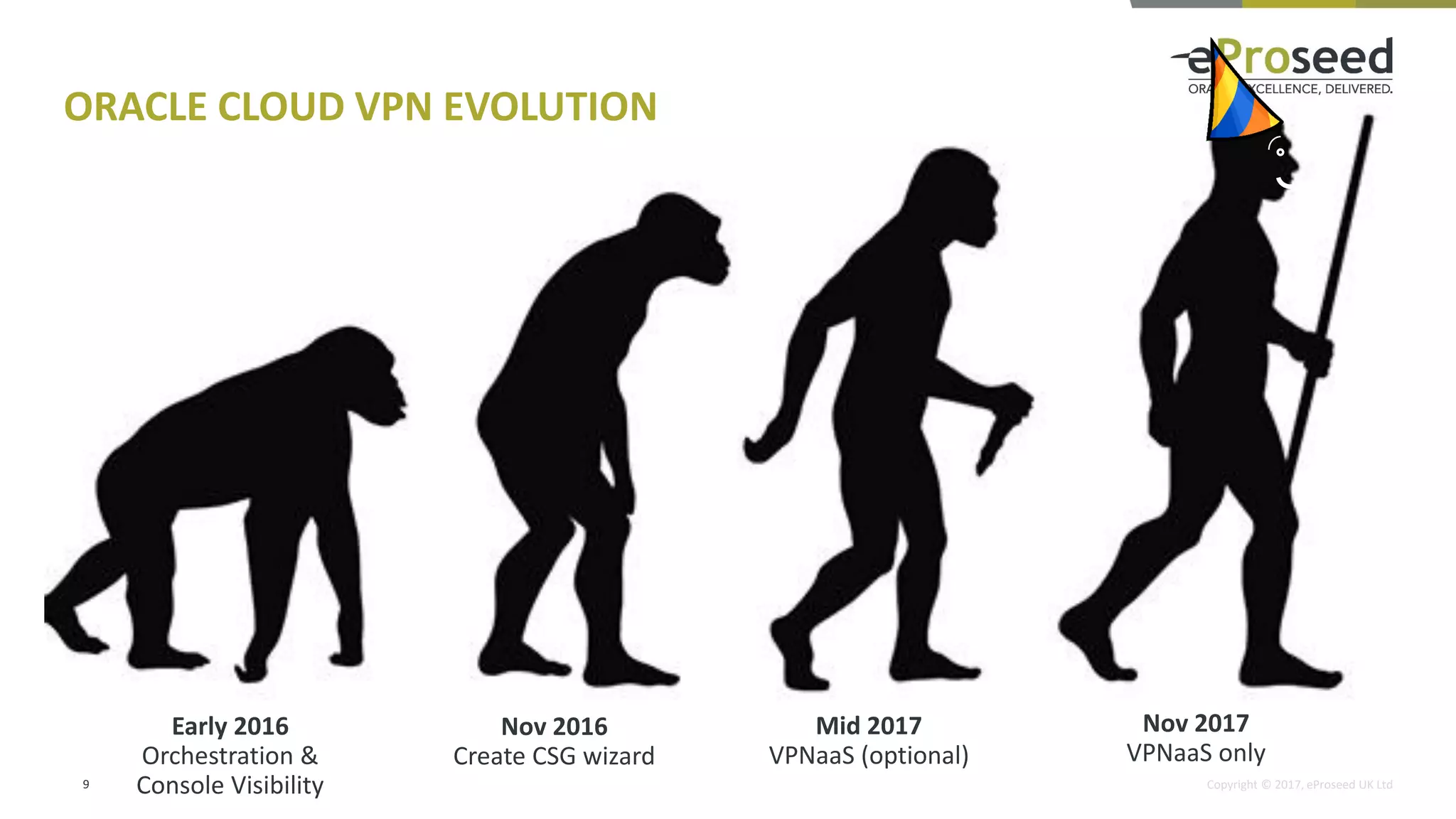
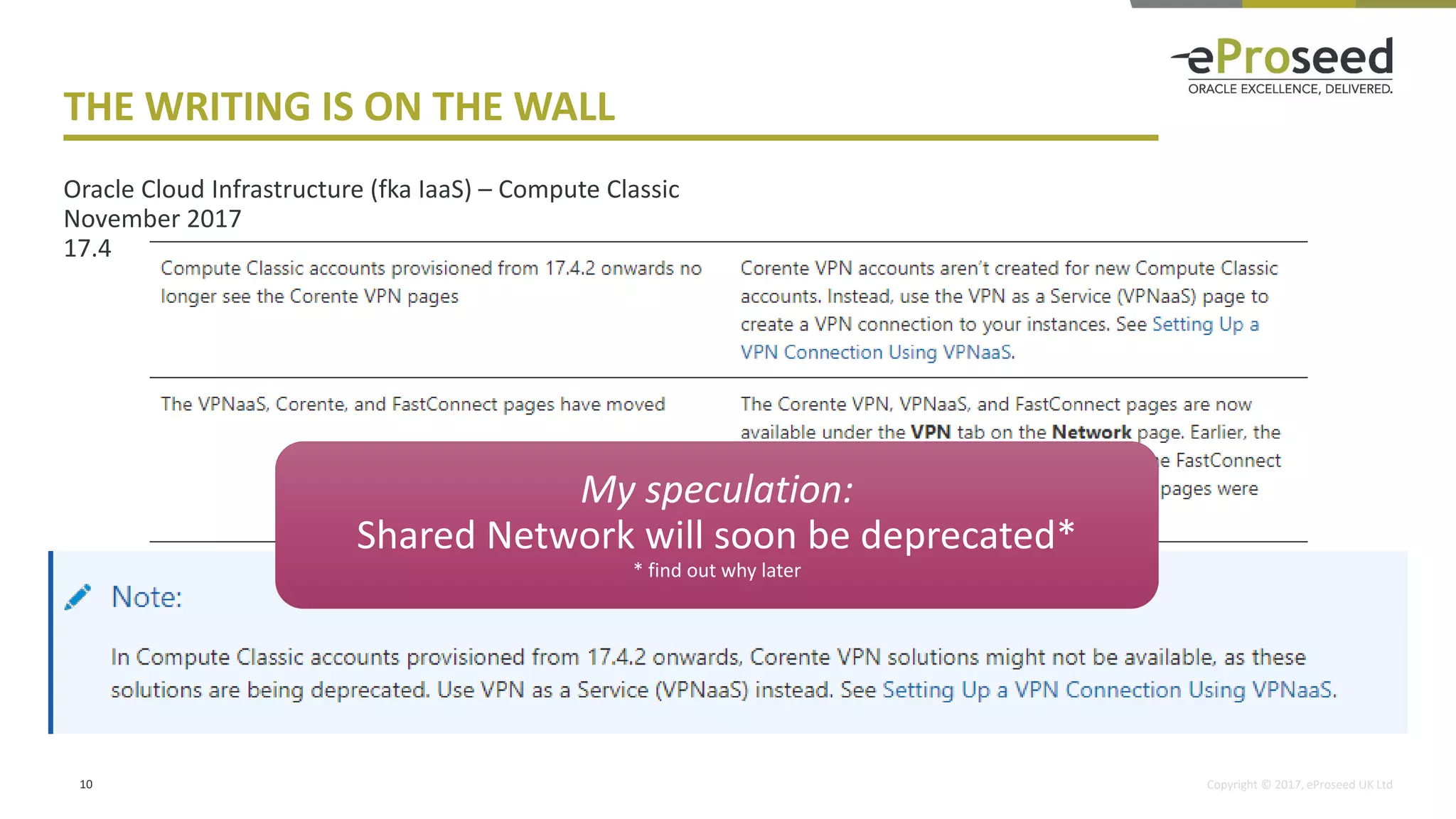
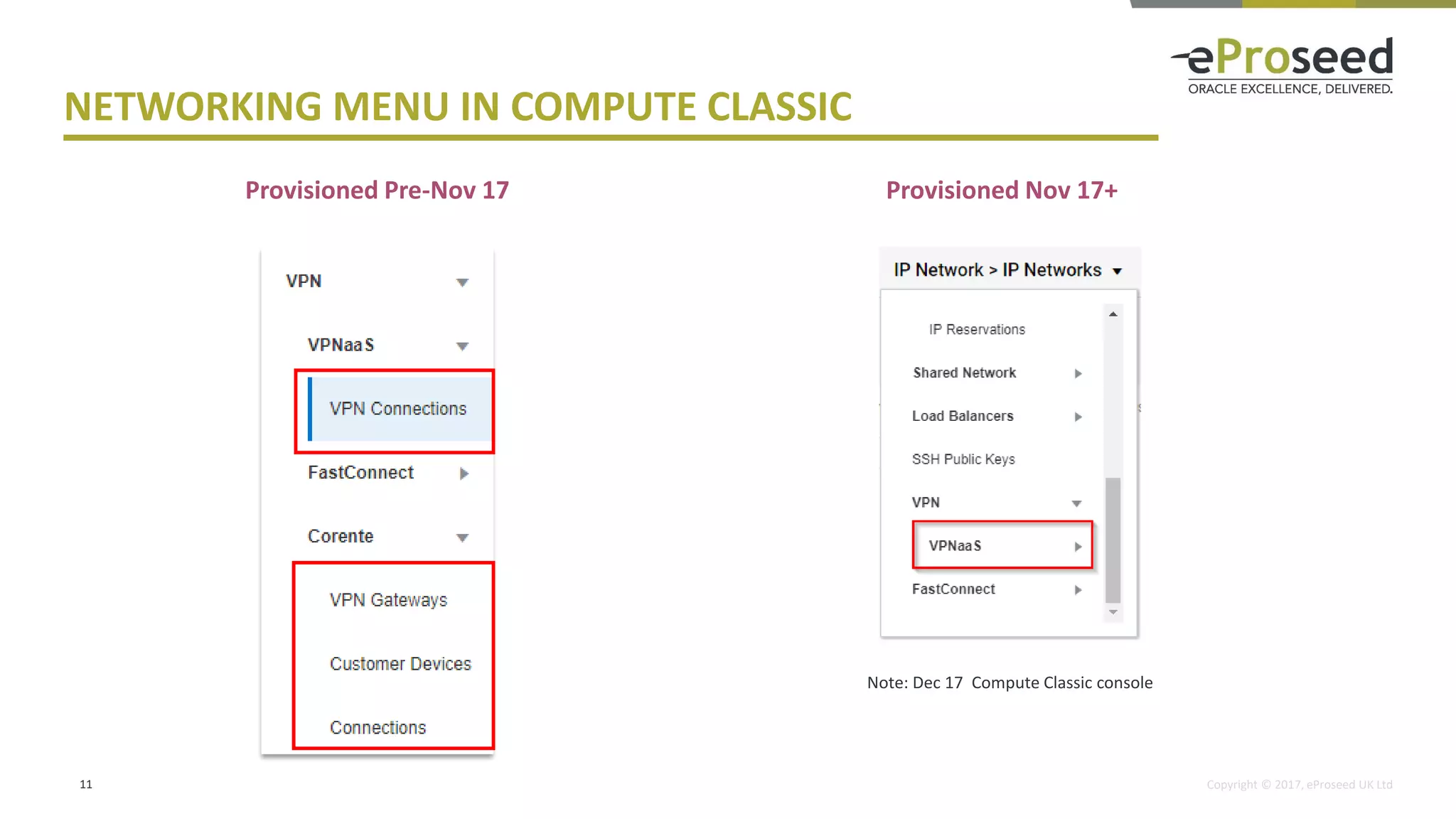
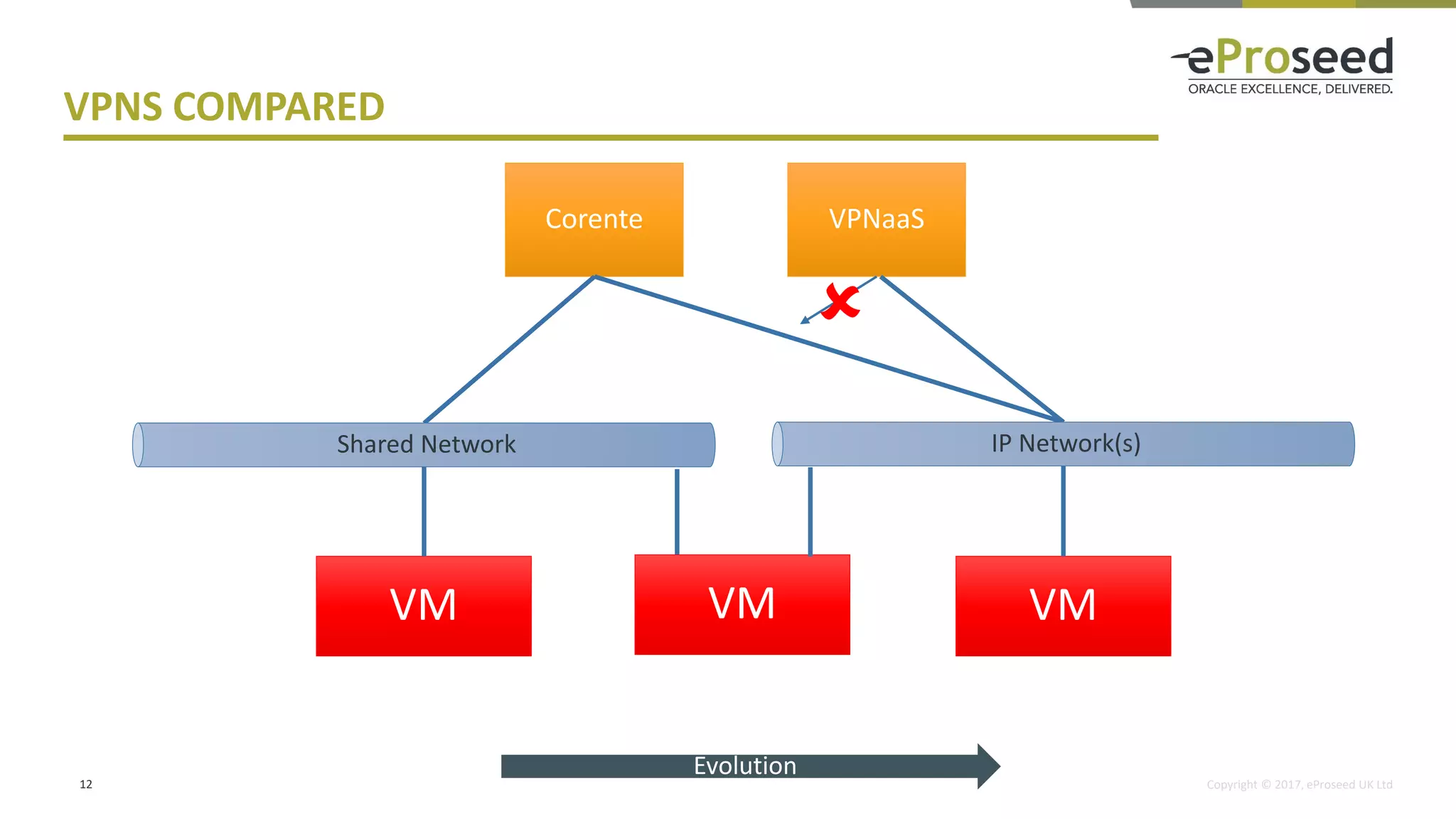
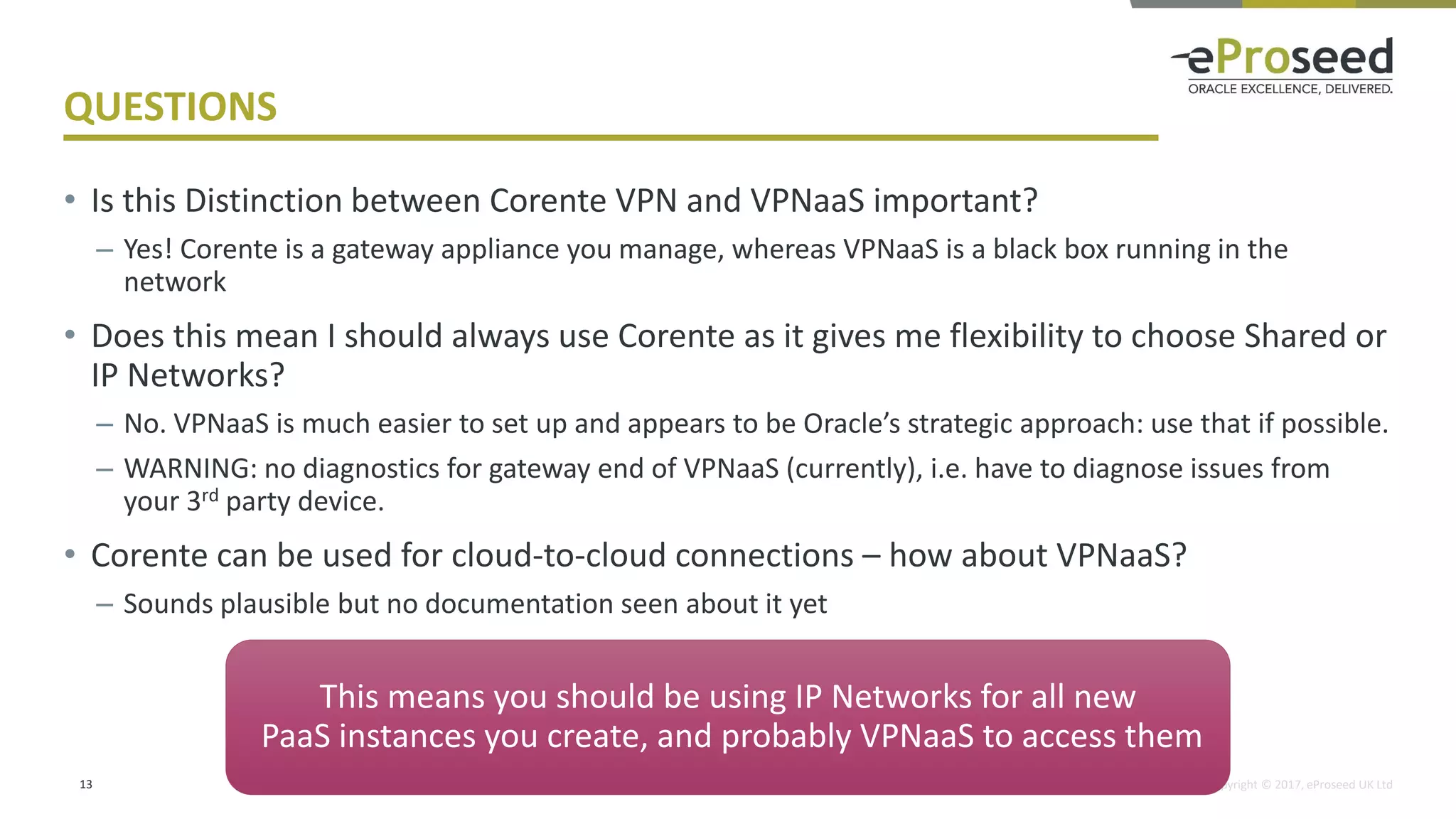
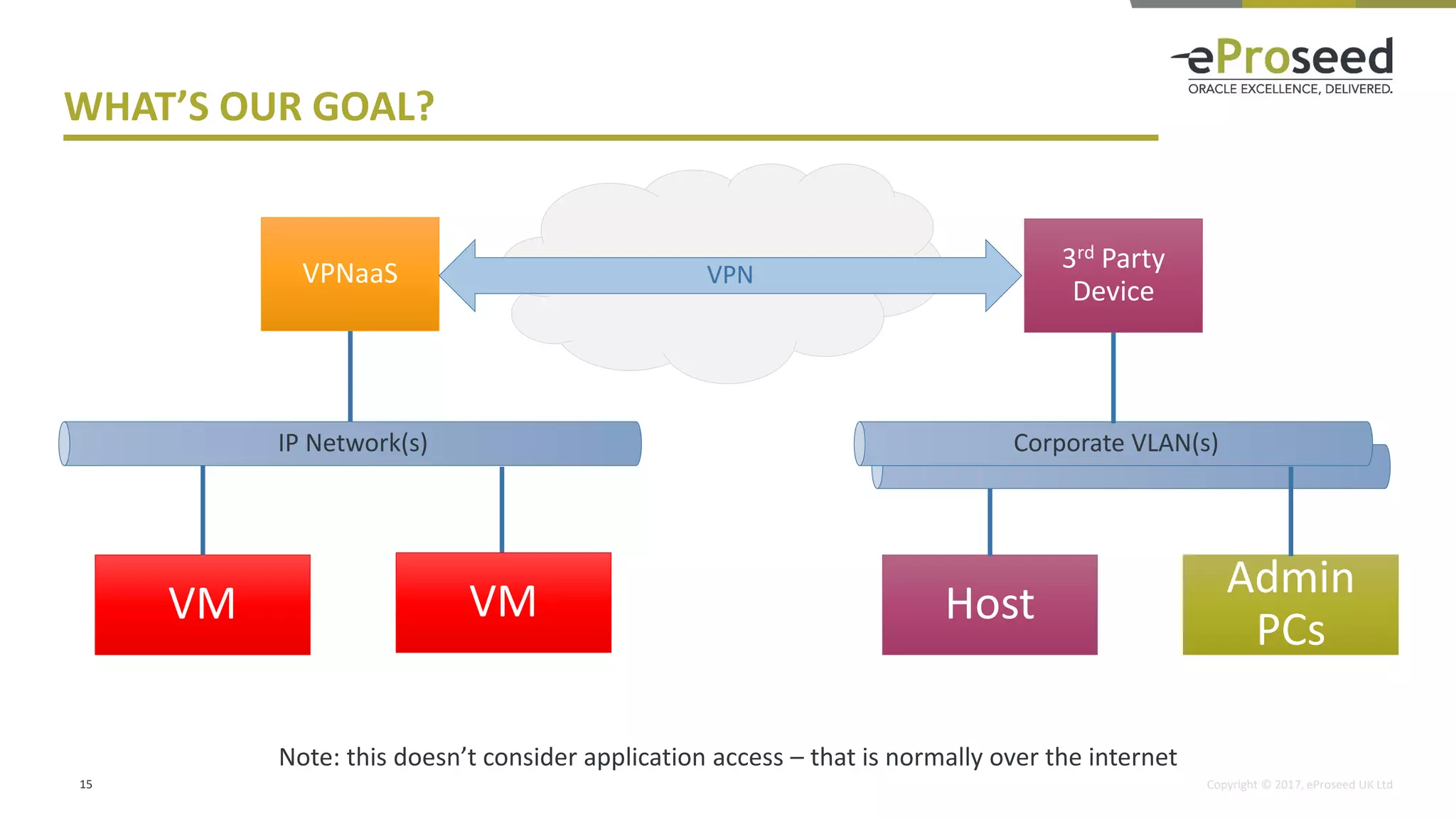
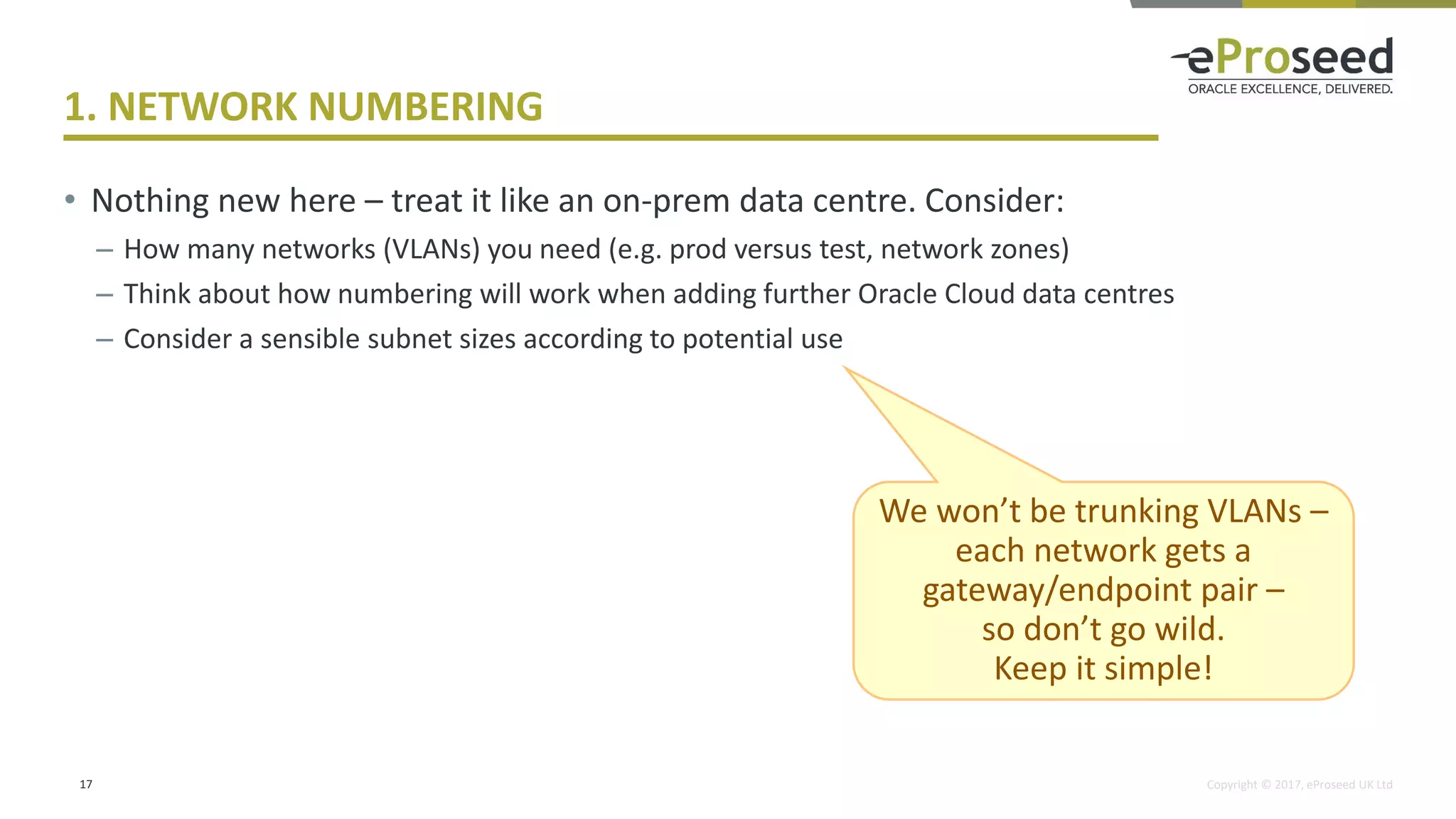
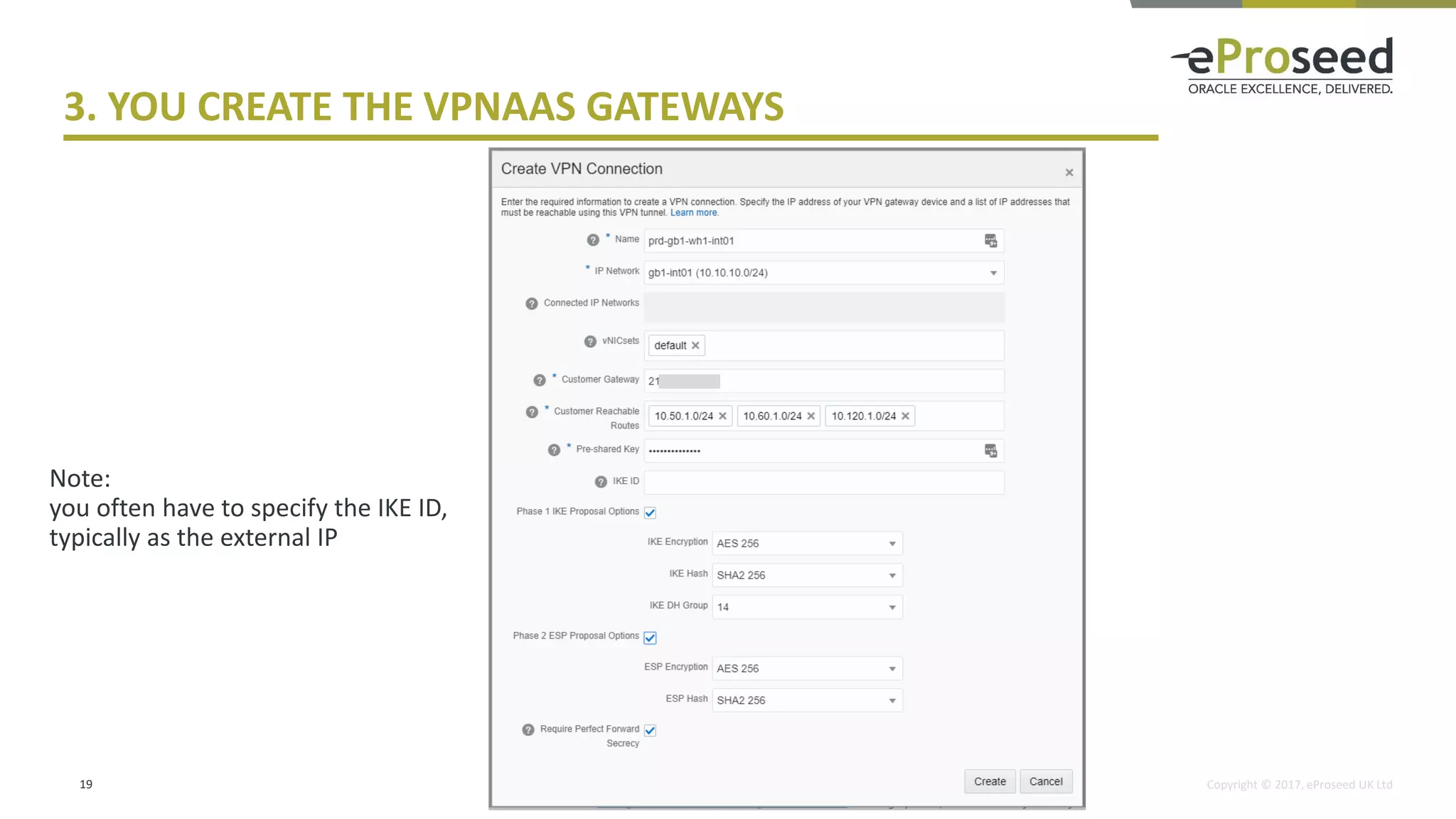
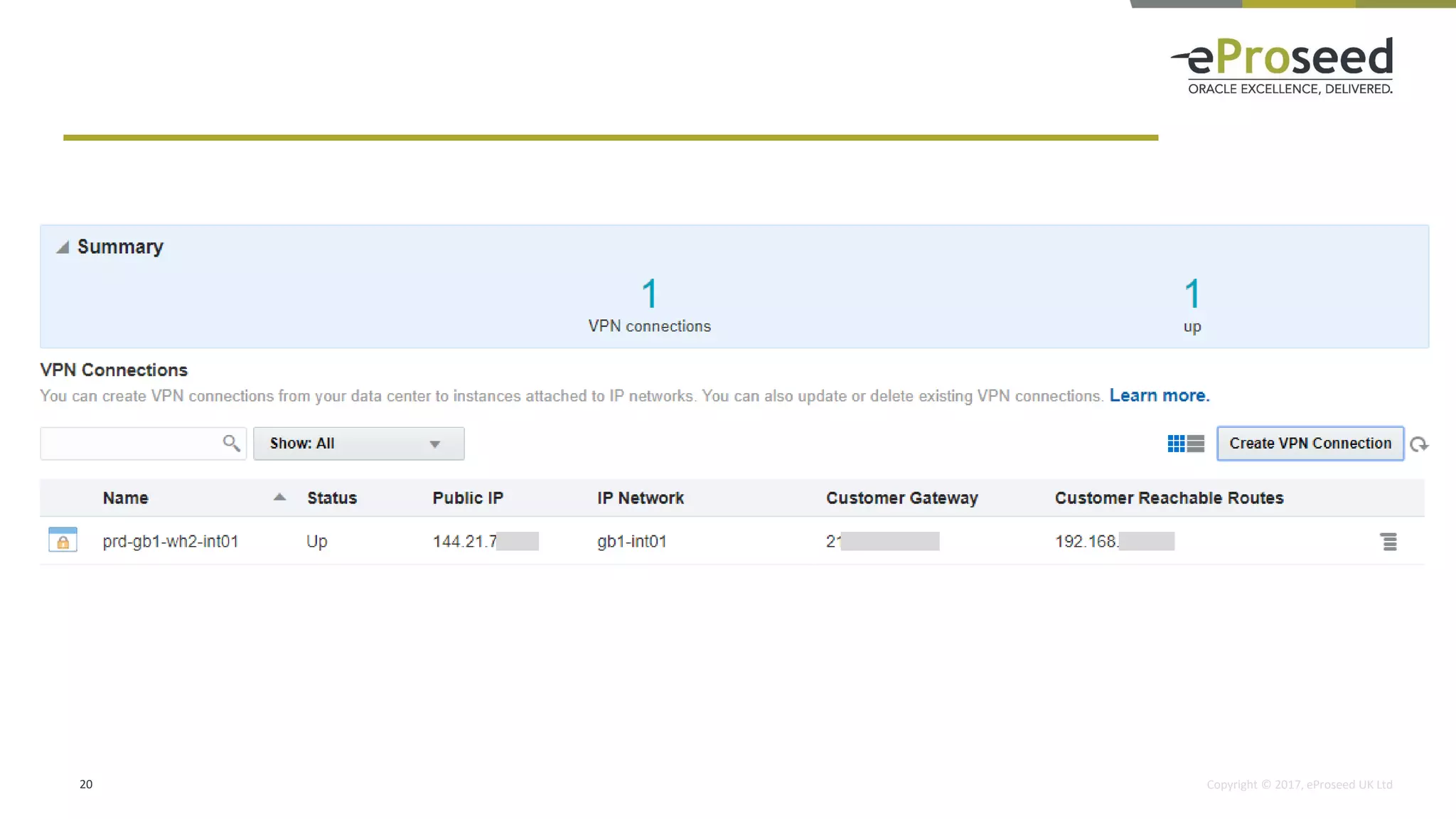
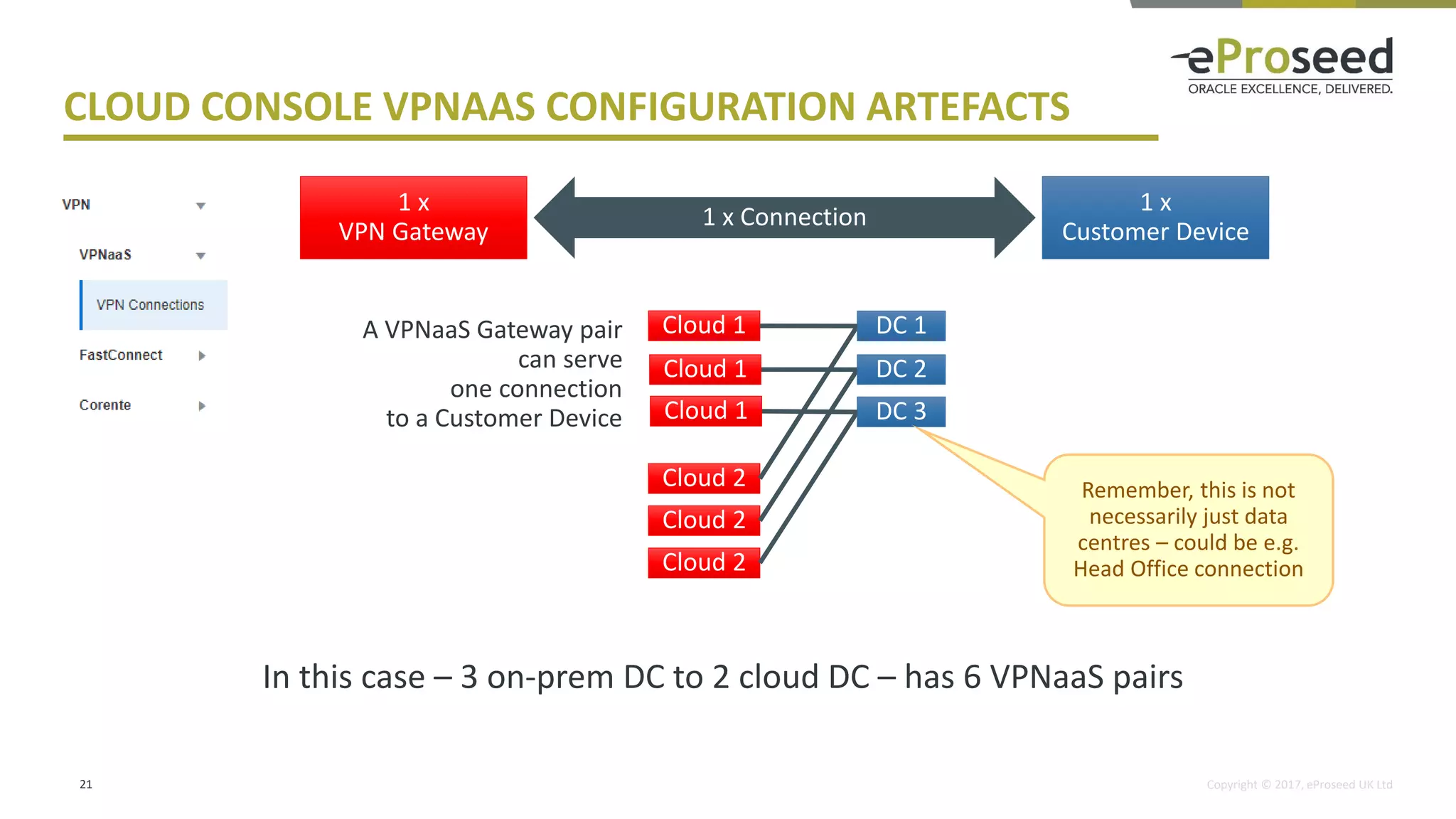
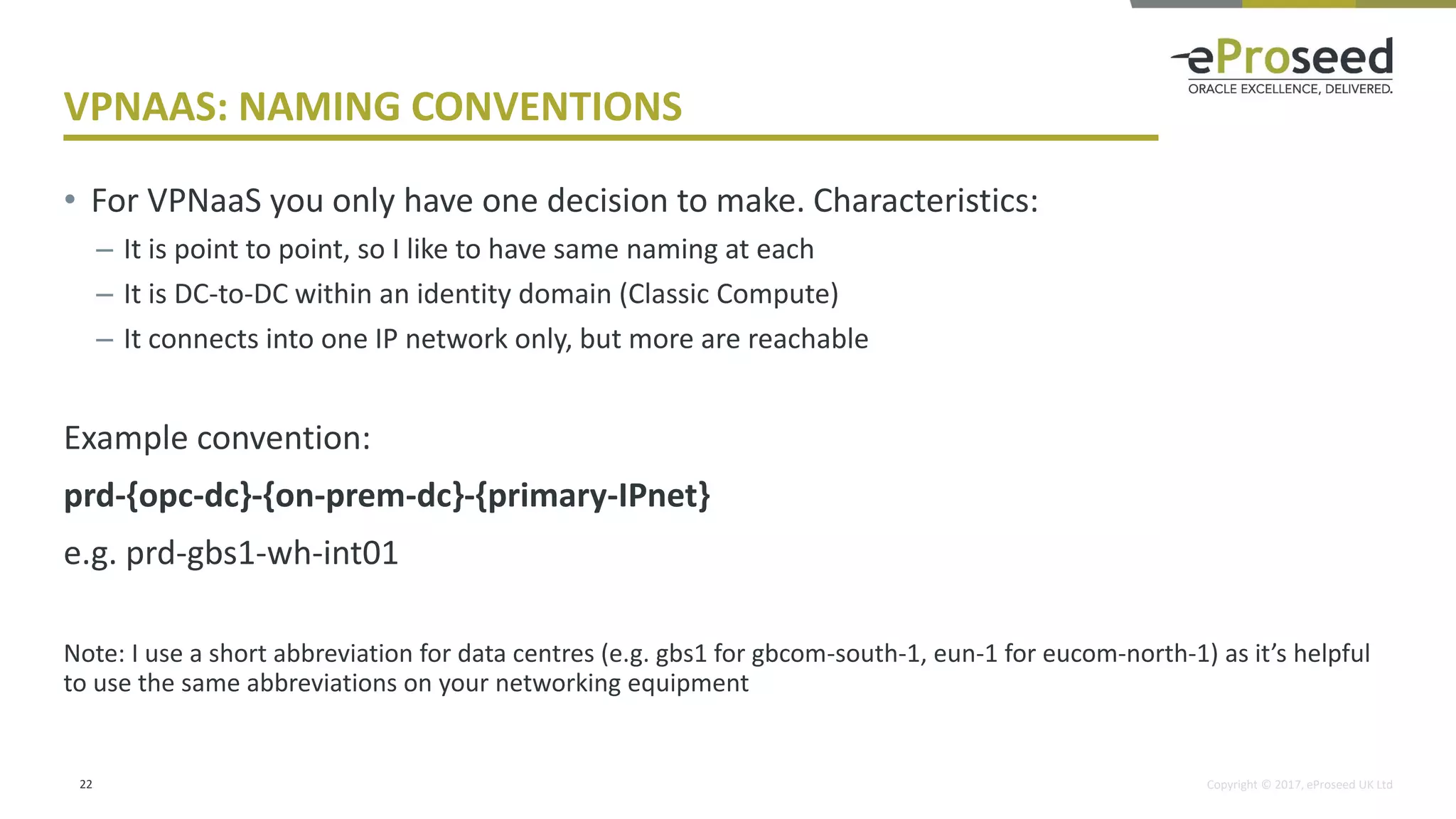
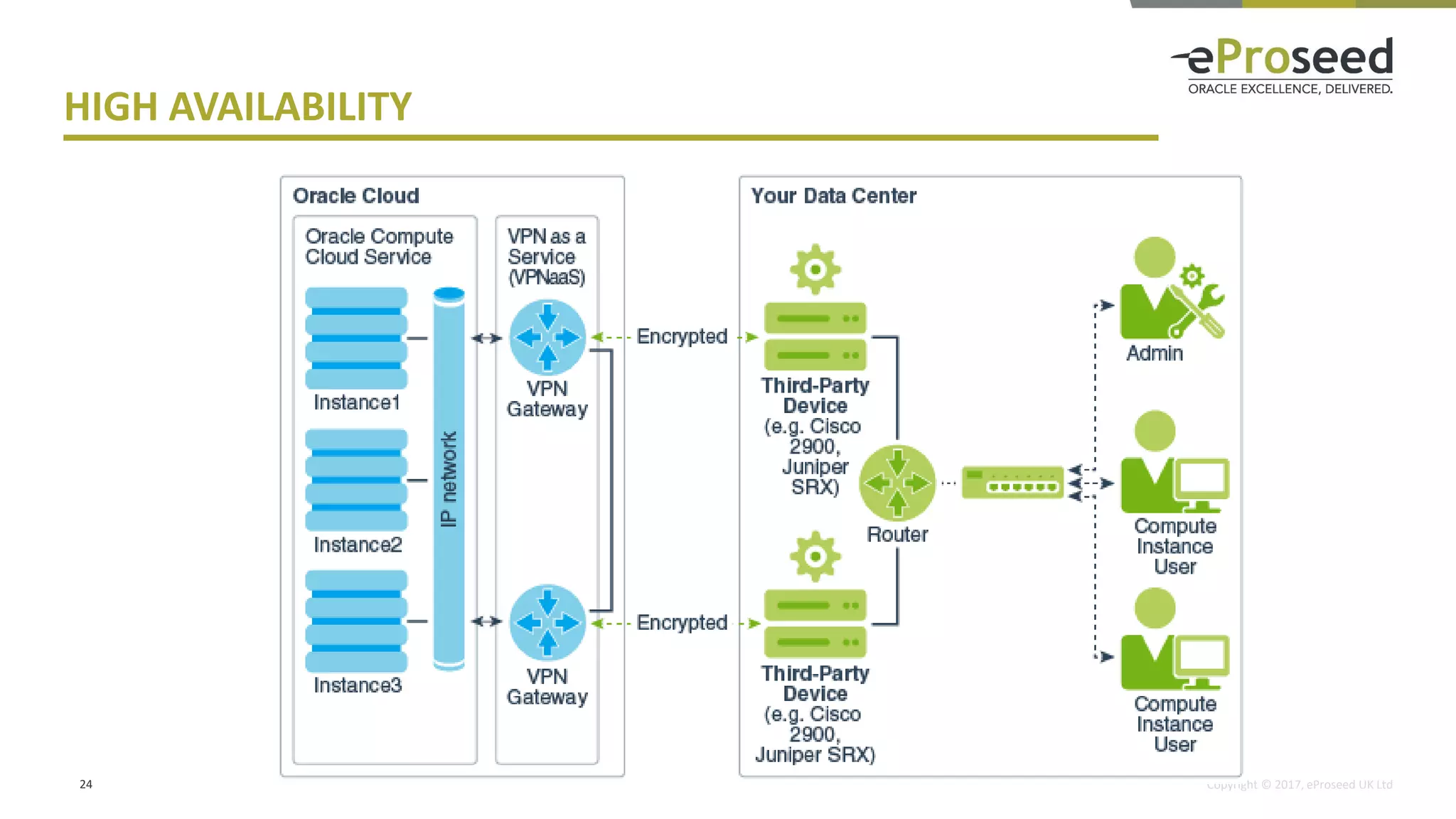
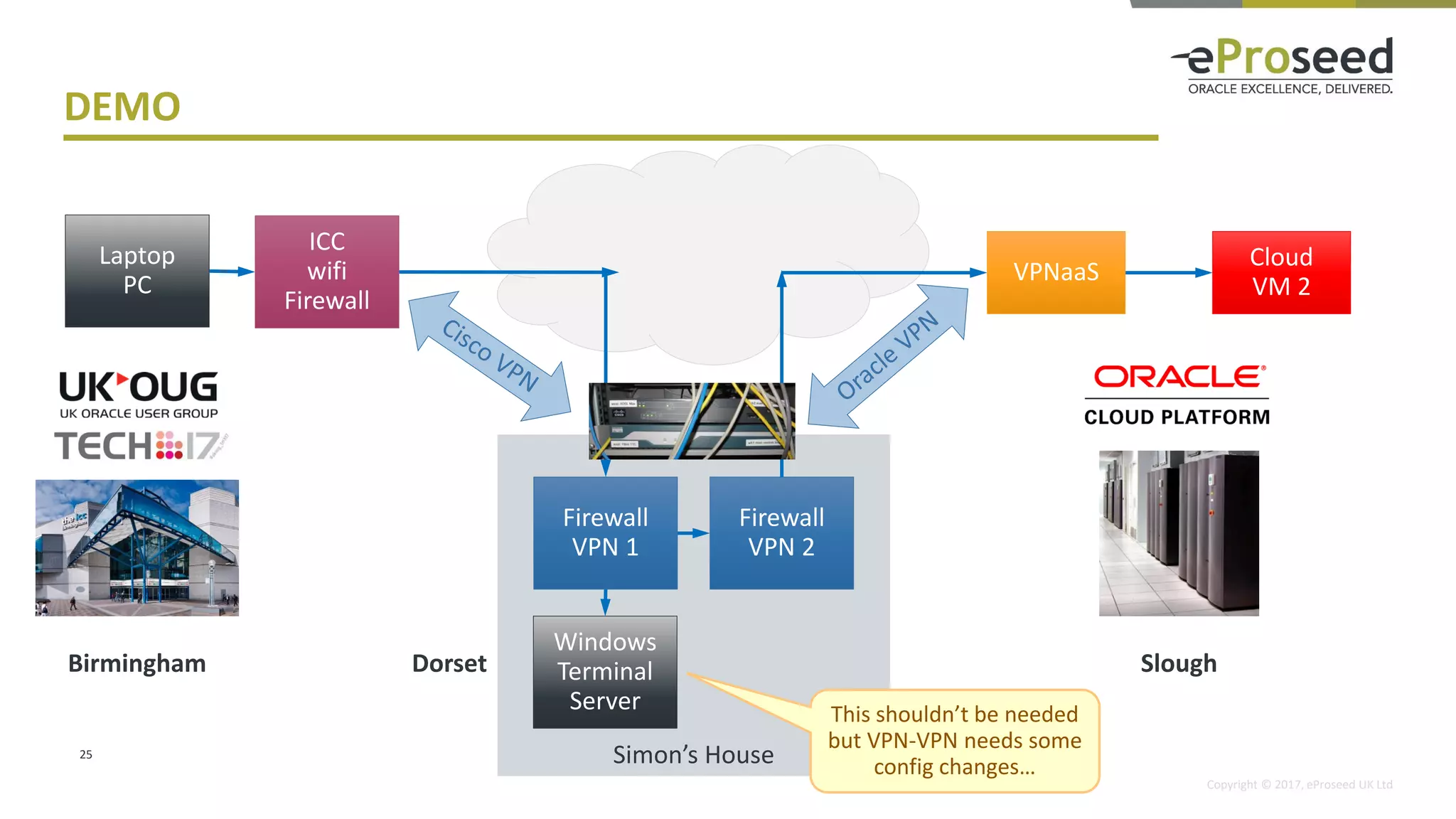
The document provides a detailed overview of connecting Oracle Cloud to data centers, including the evolution of VPN services and networking options such as shared networks, IP networks, and virtual cloud networks. It discusses Oracle's strategic approach towards VPNaas and emphasizes the importance of collaboration with network teams for successful implementation. Recommendations are provided for setting up new instances, focusing on IP networks and VPNaas.