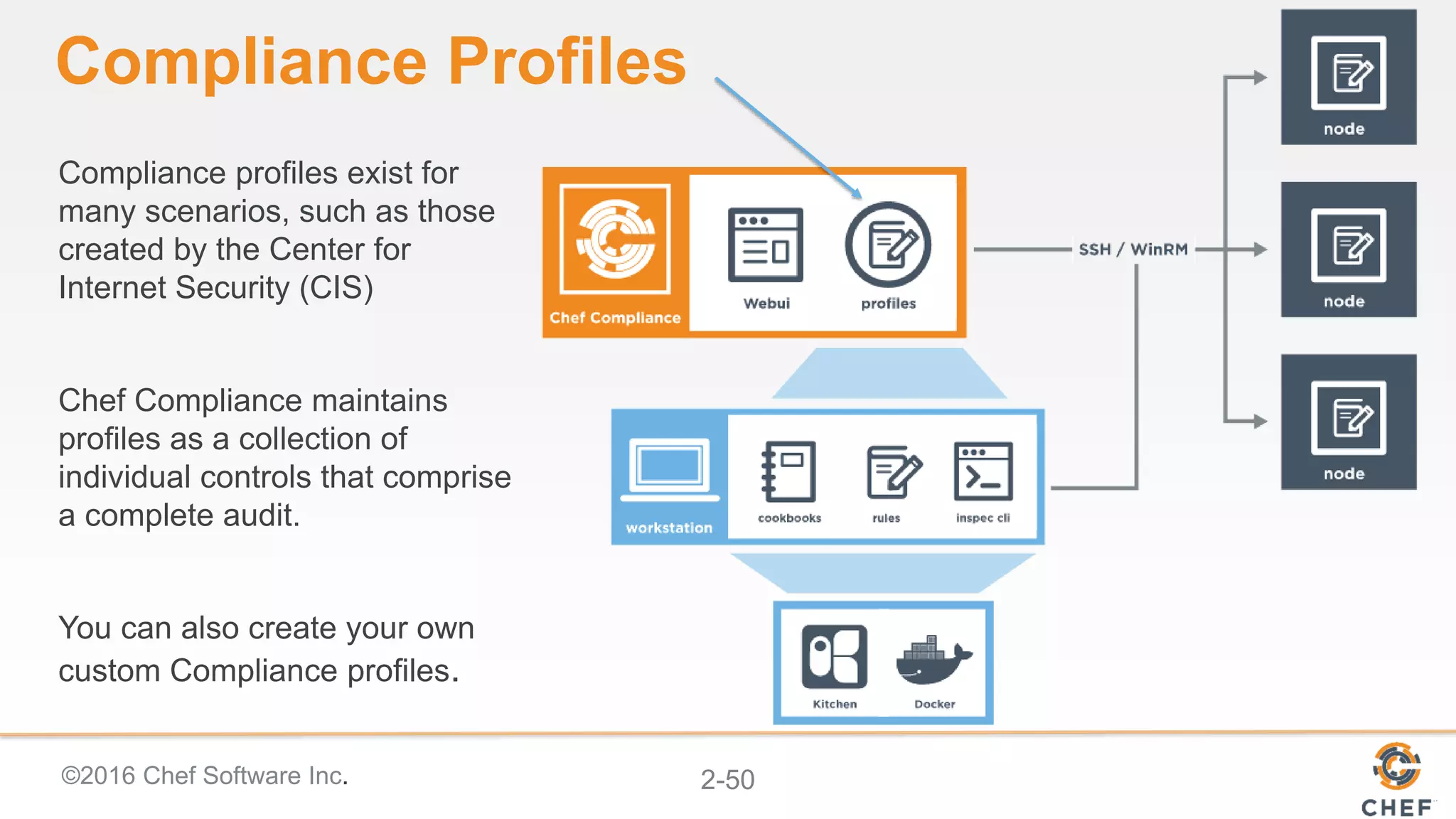
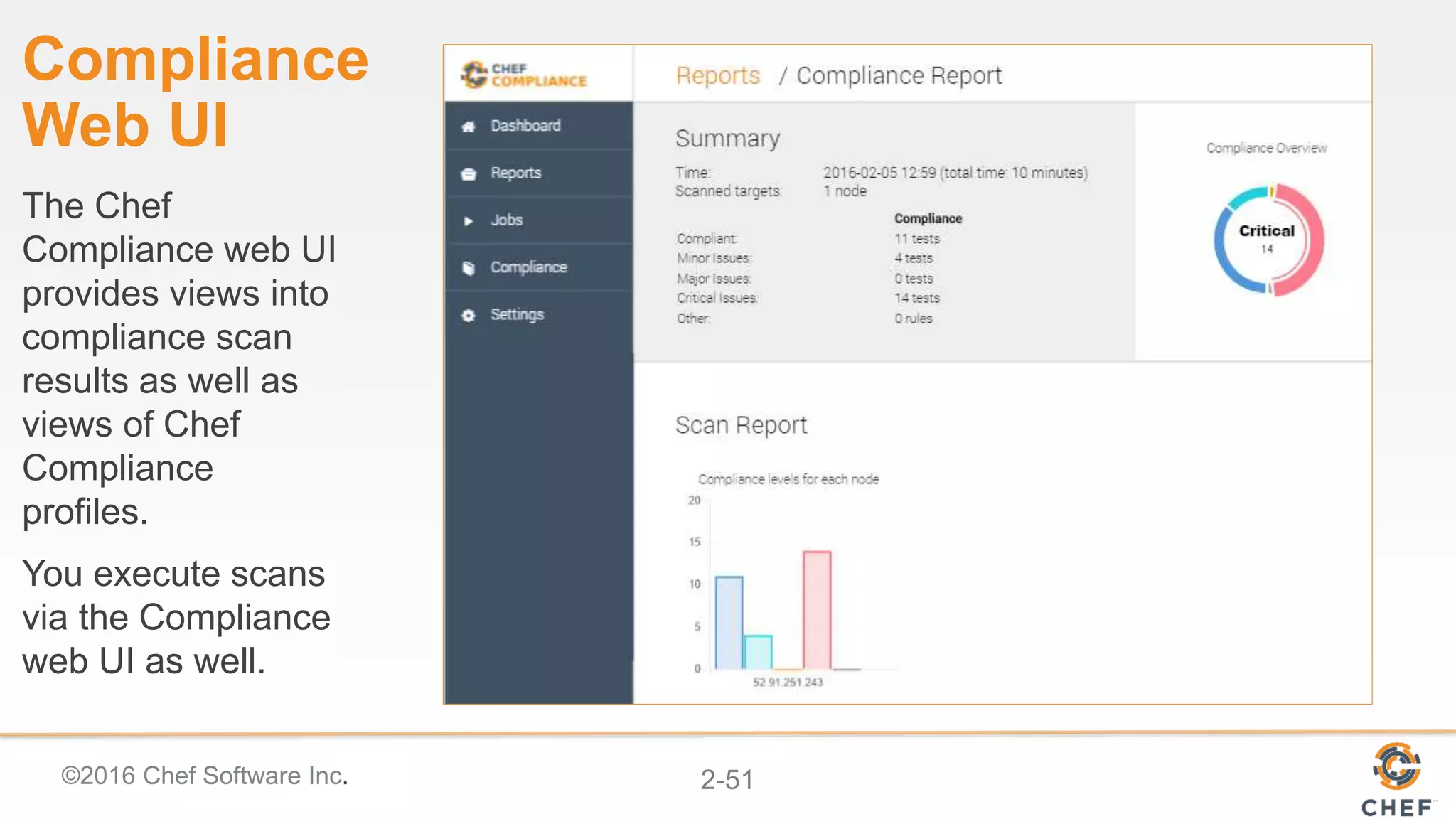
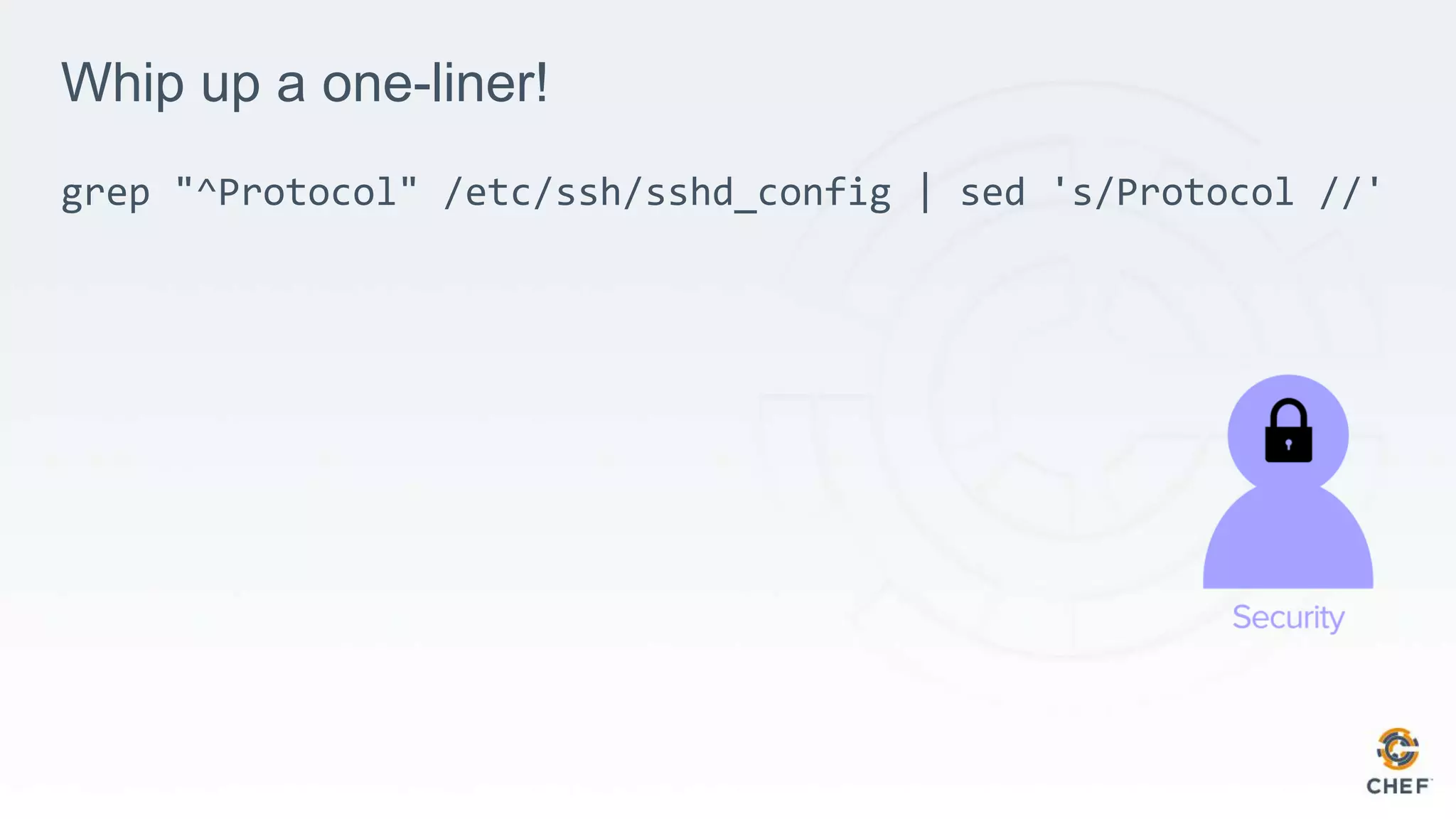
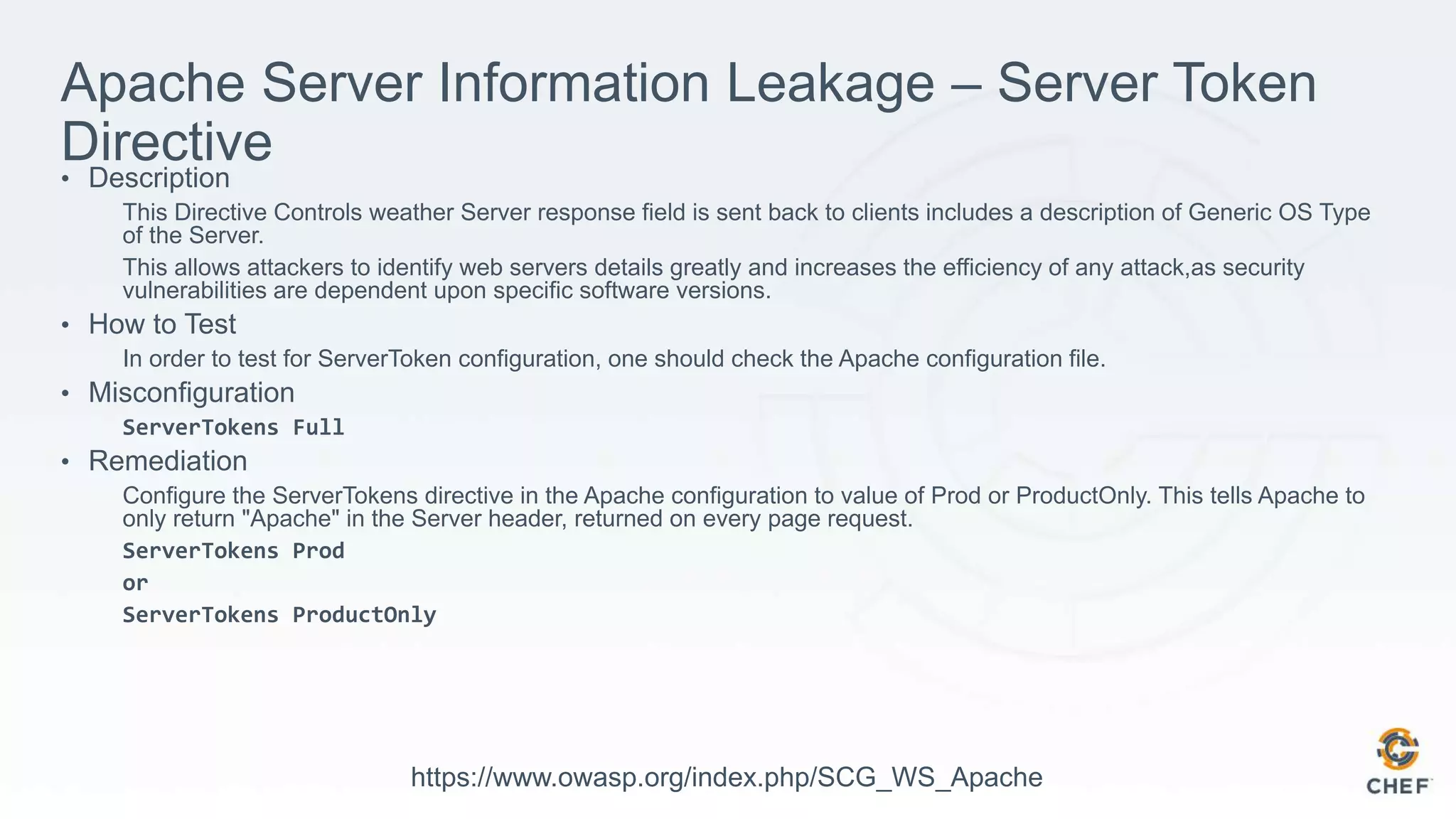
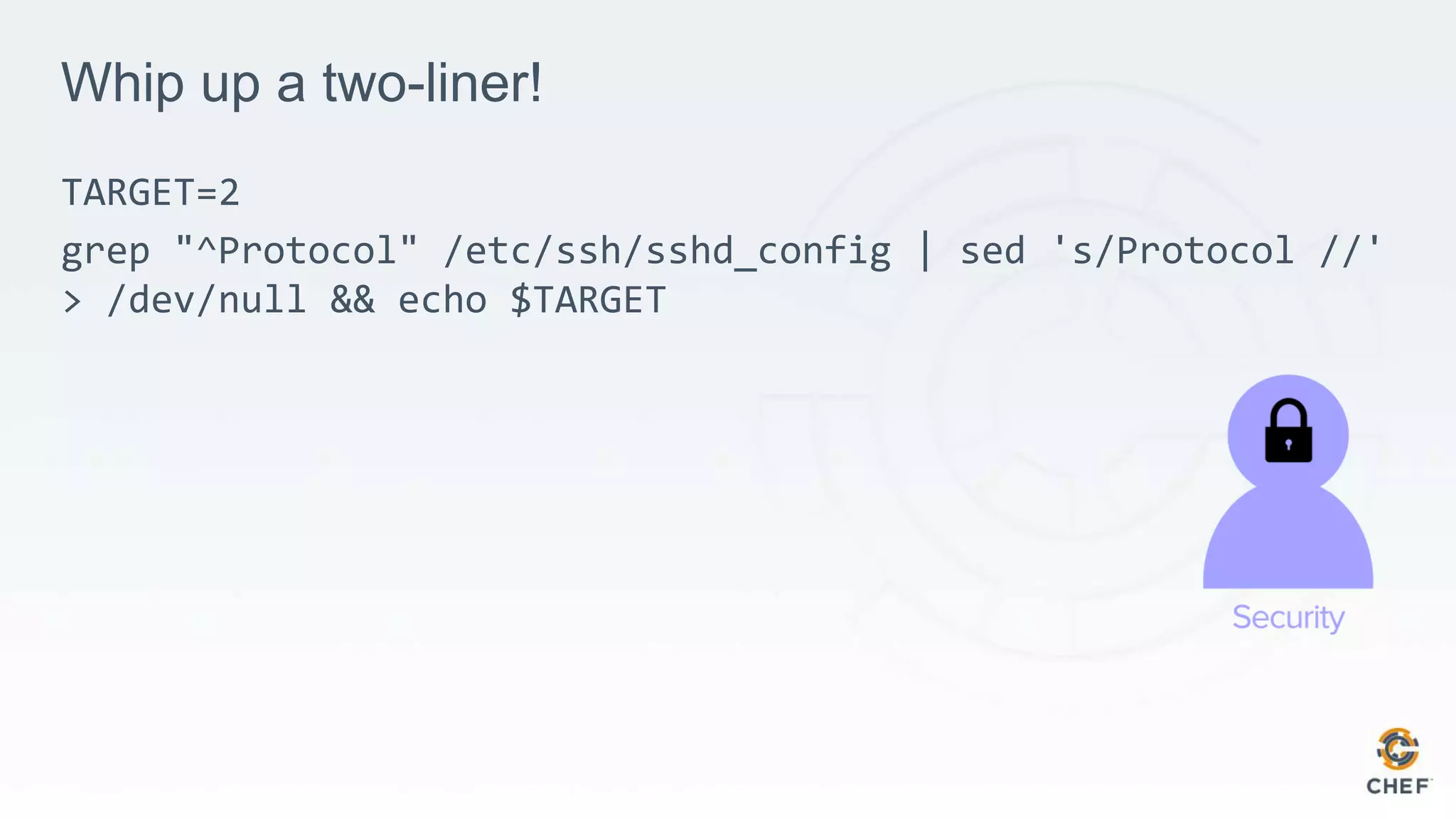
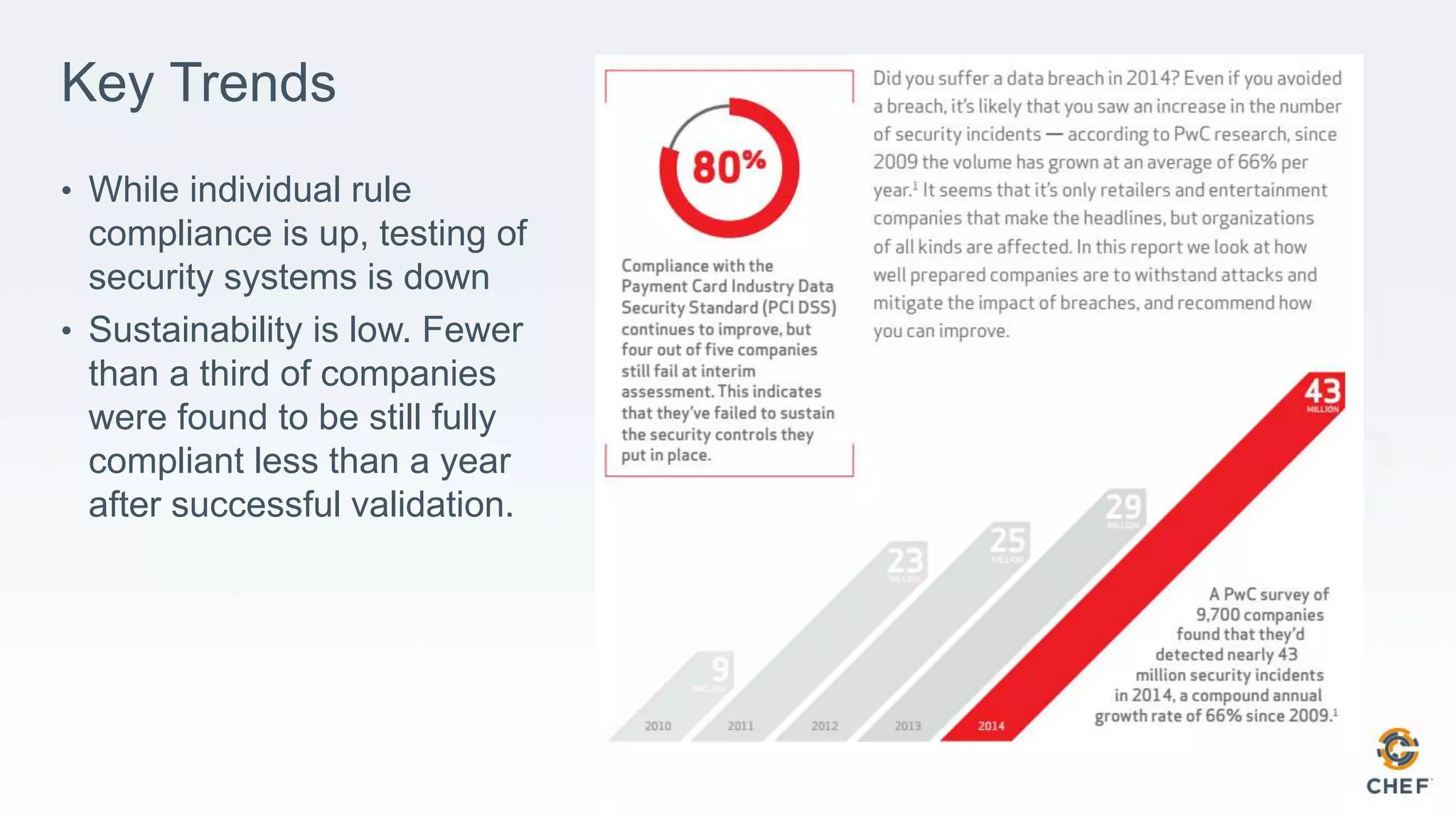
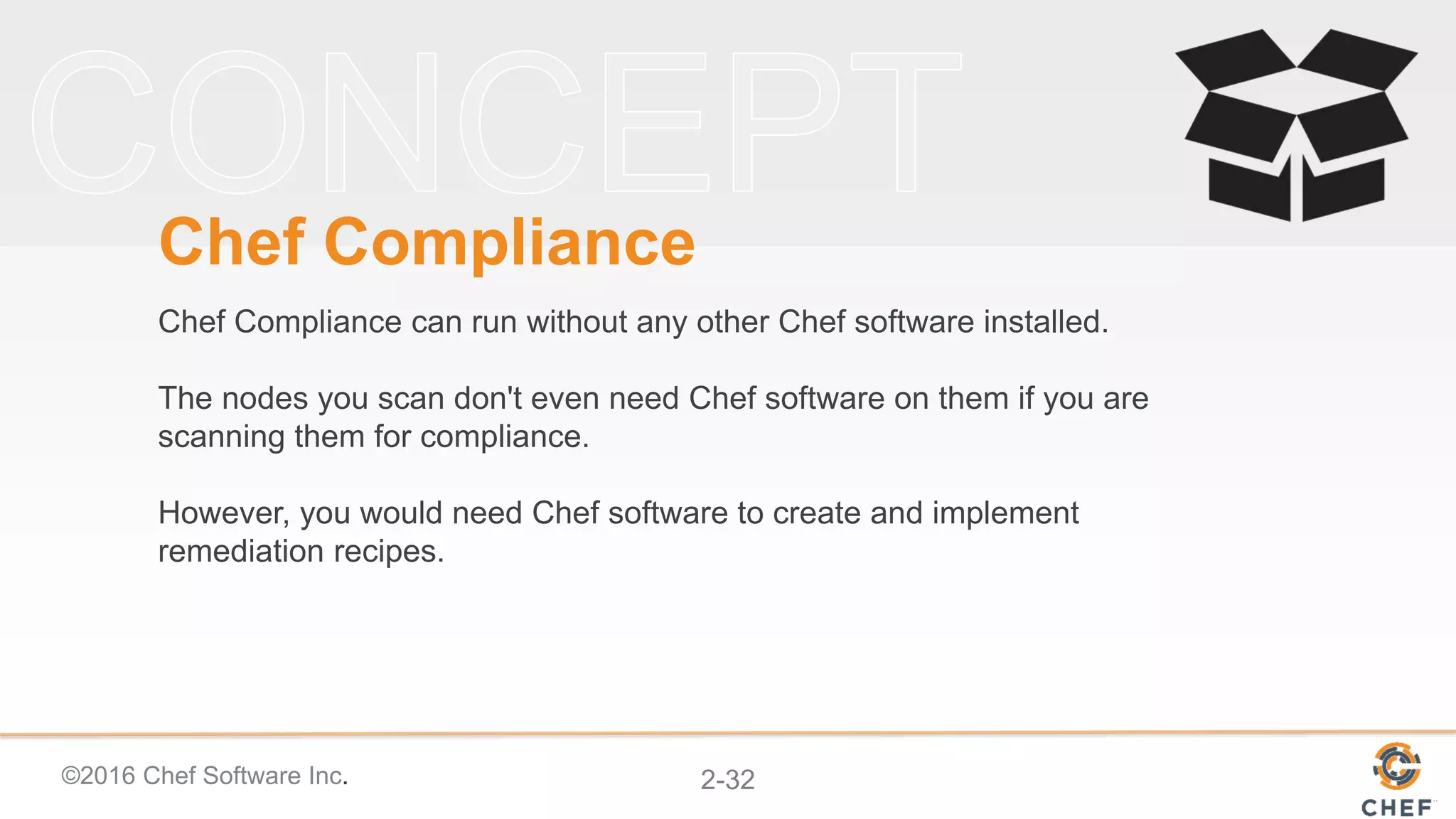
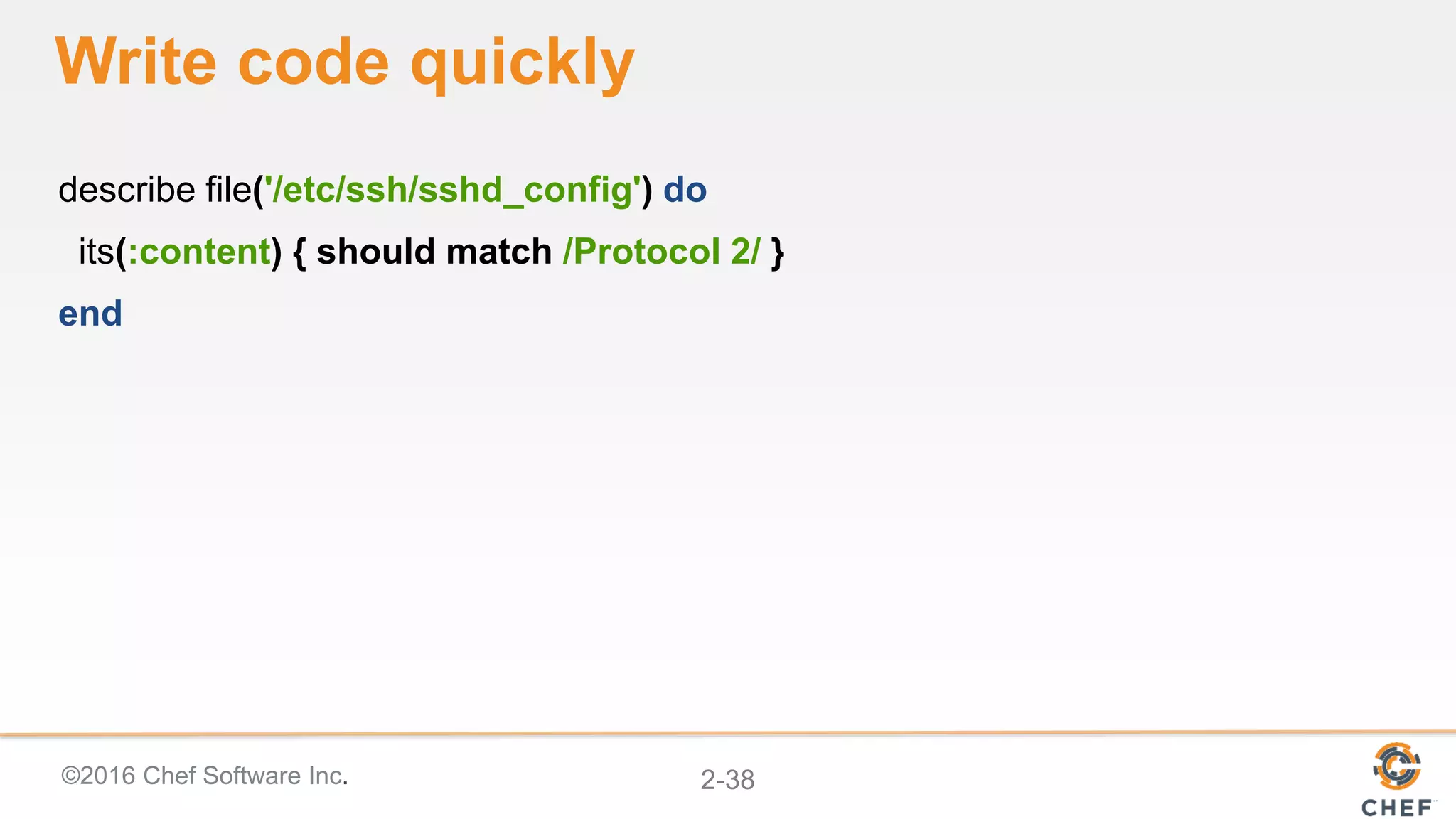
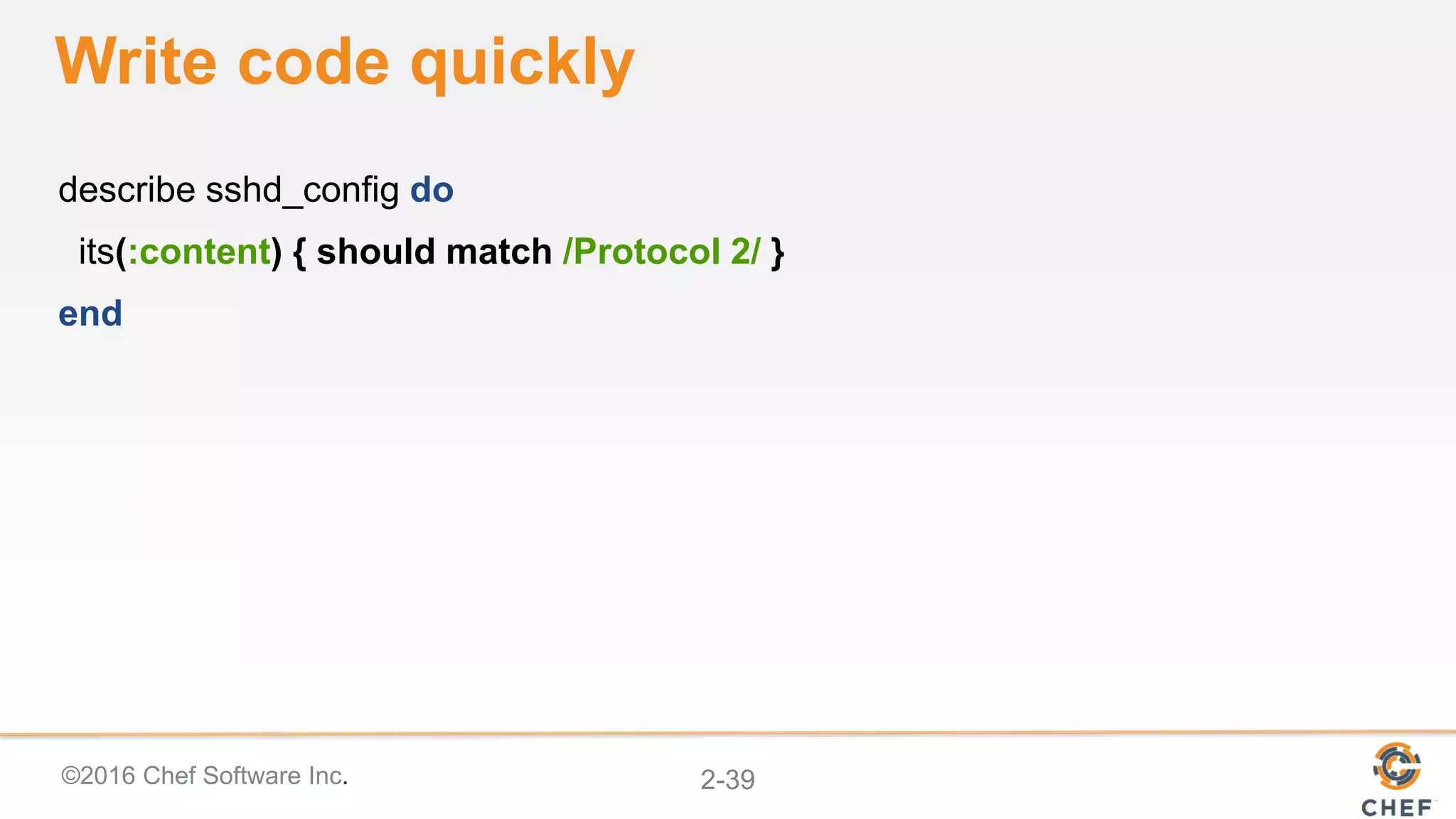
The document discusses compliance automation and the importance of using SSH version 2 to avoid security risks. It highlights the necessity of configuring Apache server settings to conceal server details and emphasizes the low sustainability of compliance among organizations. Additionally, it introduces Chef Compliance, a tool for identifying compliance issues and creating customizable reports using Inspec for compliance testing.





![Infrastructure Code
package 'httpd' do
action :install
end
service 'httpd' do
action [ :start, :enable ]
end](https://image.slidesharecdn.com/02-complianceandinspec-161003144024/75/Compliance-Automation-with-Inspec-Part-2-21-2048.jpg)











![©2016 Chef Software Inc. 2-49
Inspect machines, data, & APIs
control 'sg-1' do
impact 1.0
title 'Security Group: No ingress access to CIDR block 0.0.0.0/0'
desc 'Security Groups must not allow inbound access from anywhere'
Vpc.new(id: ENV['vpc_id']).security_groups.each do |security_group|
describe security_group do
it { should_not have_ingress_rule().with_source('0.0.0.0/0') }
end
end
end](https://image.slidesharecdn.com/02-complianceandinspec-161003144024/75/Compliance-Automation-with-Inspec-Part-2-49-2048.jpg)