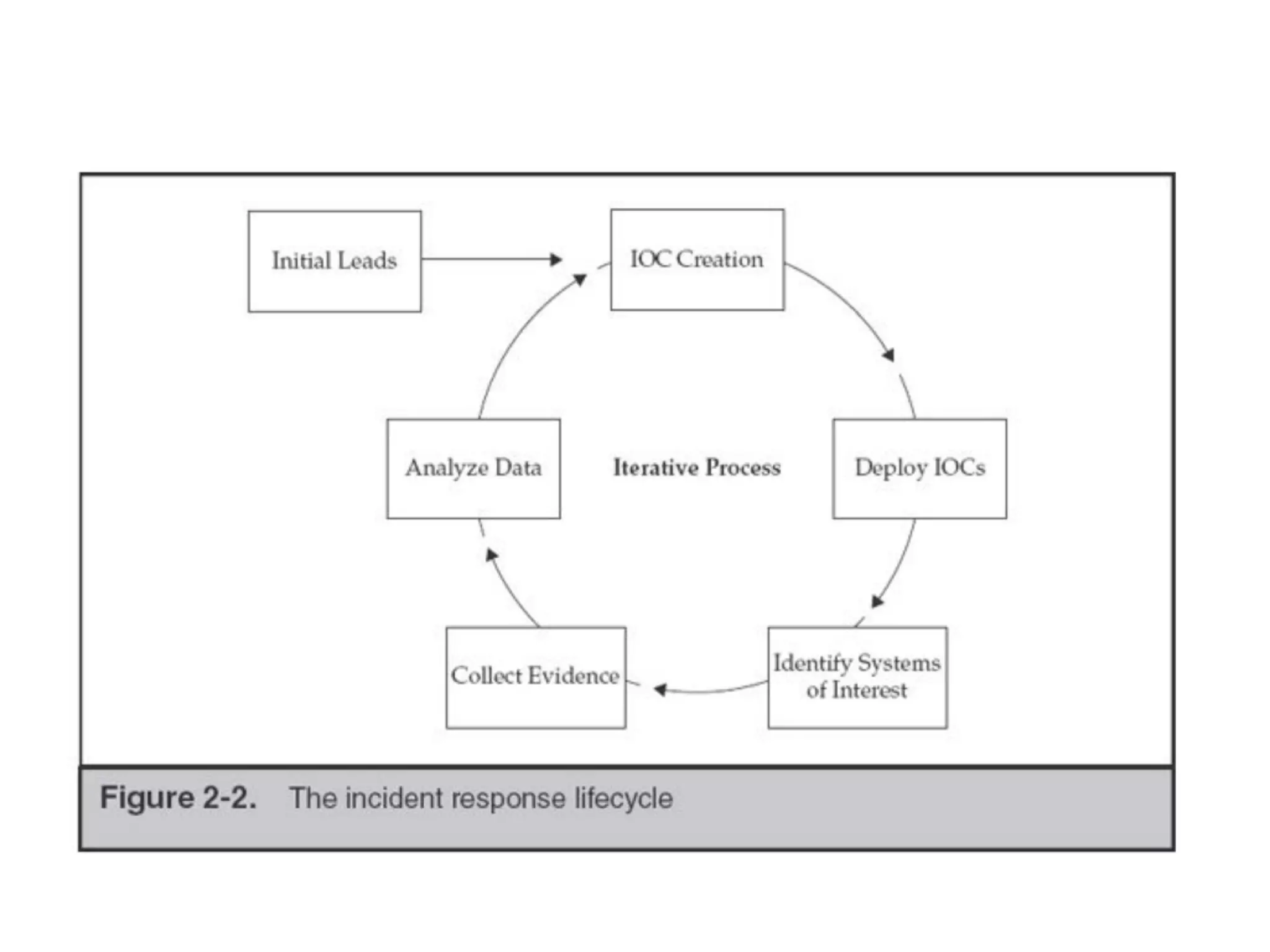
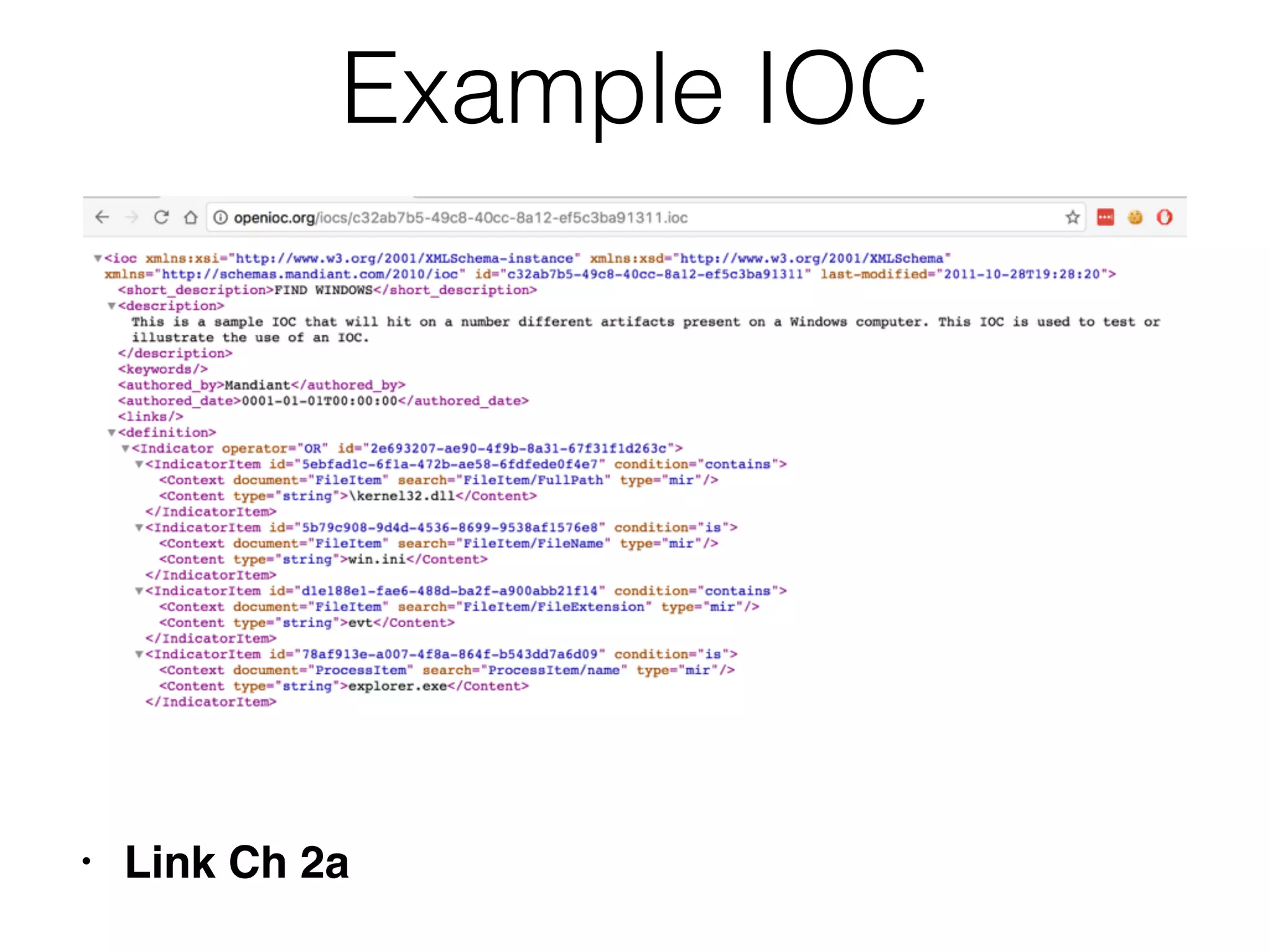
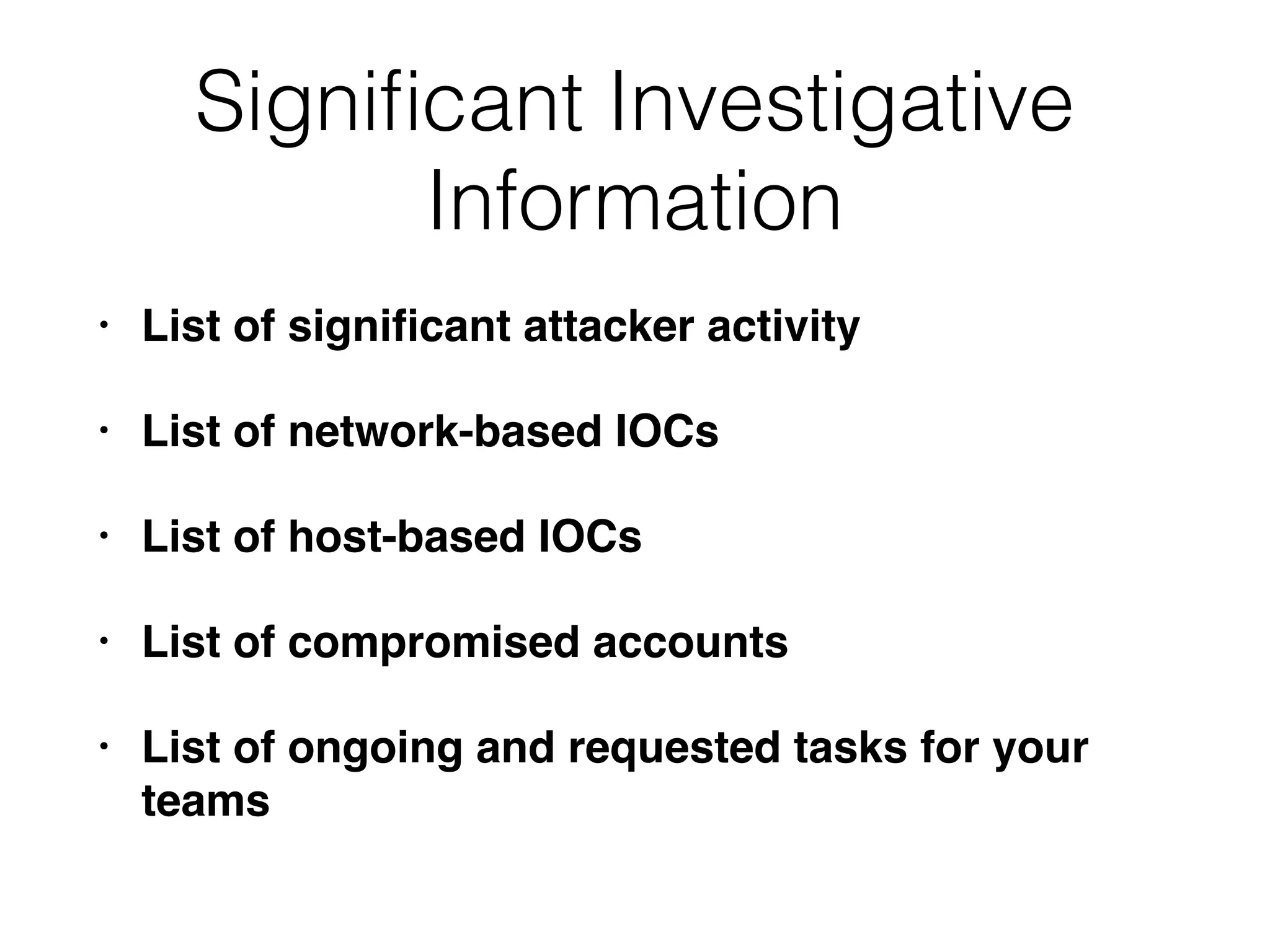
This document discusses the roles and responsibilities involved in incident response (IR). It describes the incident manager who leads the investigation team, and the remediation team leader who coordinates remediation activities. It outlines the IR process including initial response, investigation, and remediation phases. It provides guidance on hiring IR talent, preserving evidence, analyzing data, developing indicators of compromise, and creating reports.