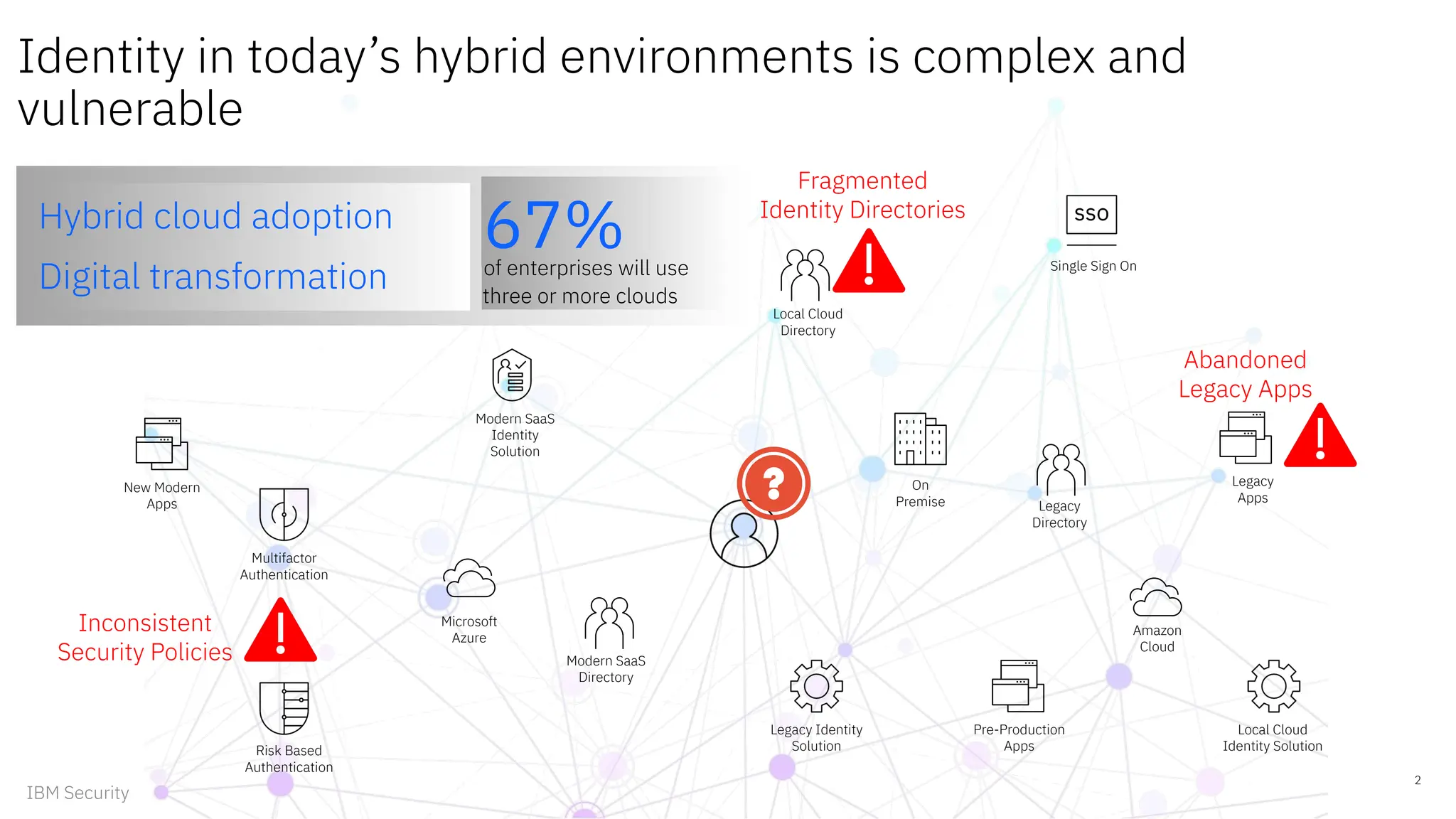
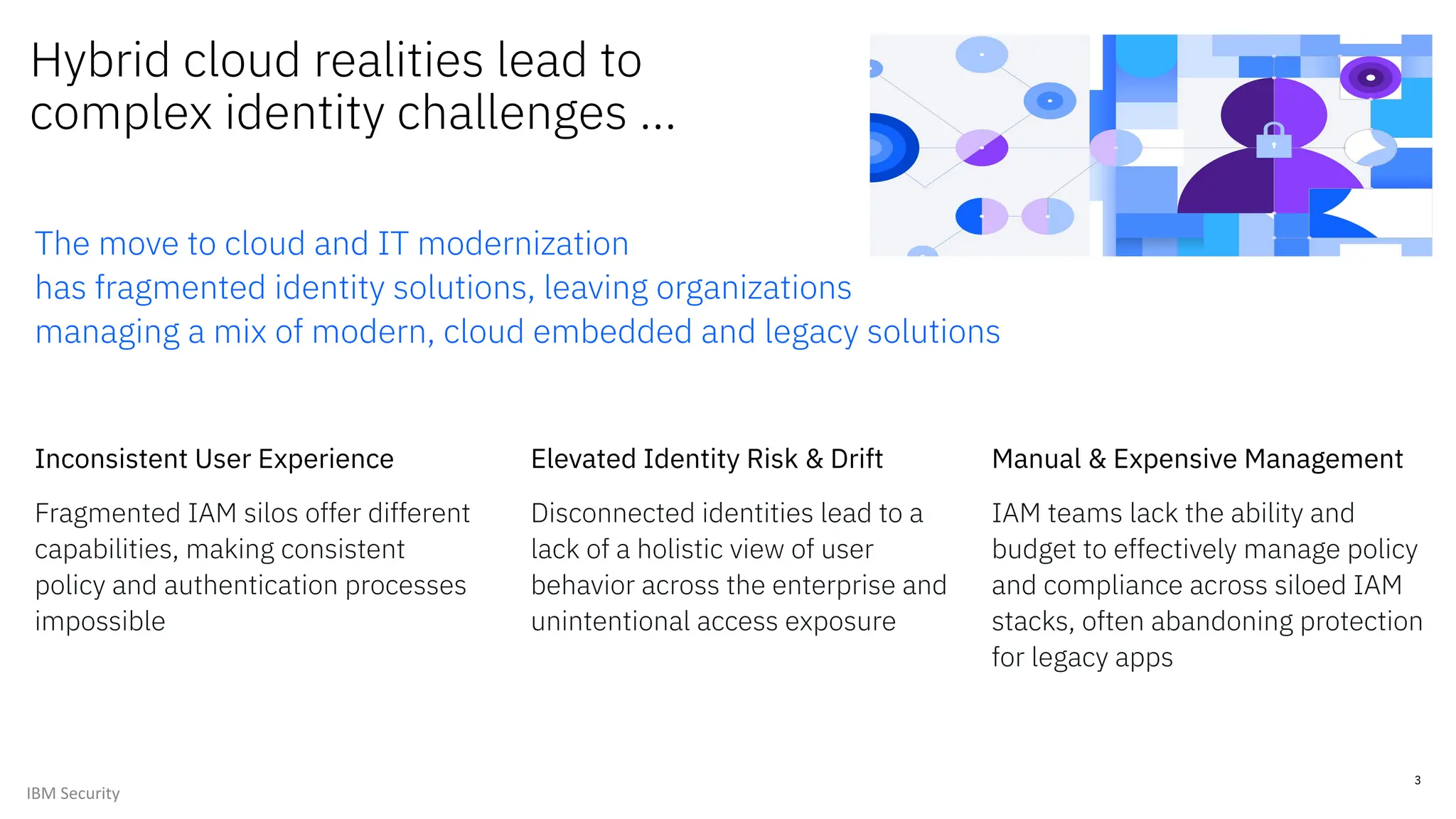
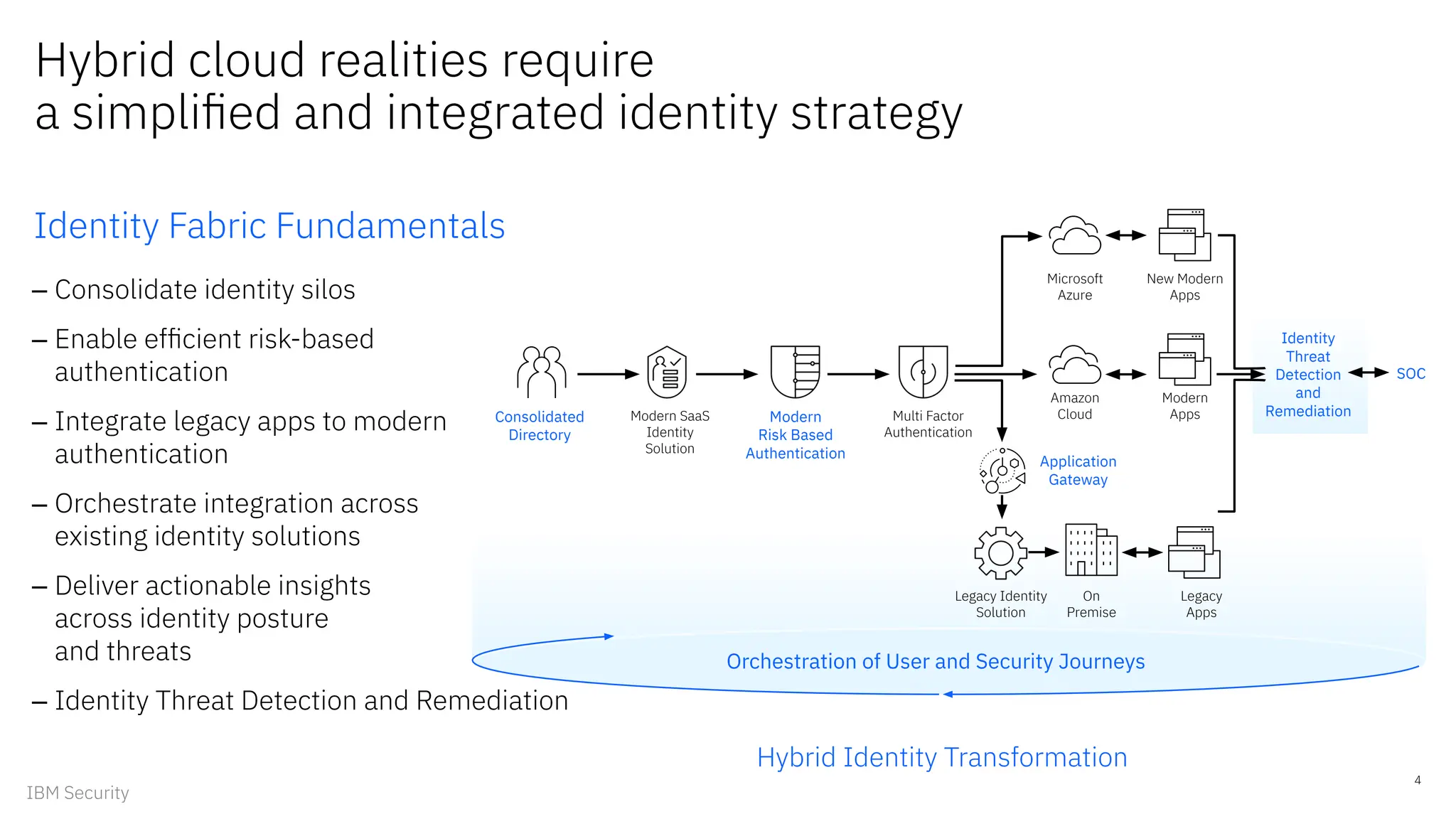
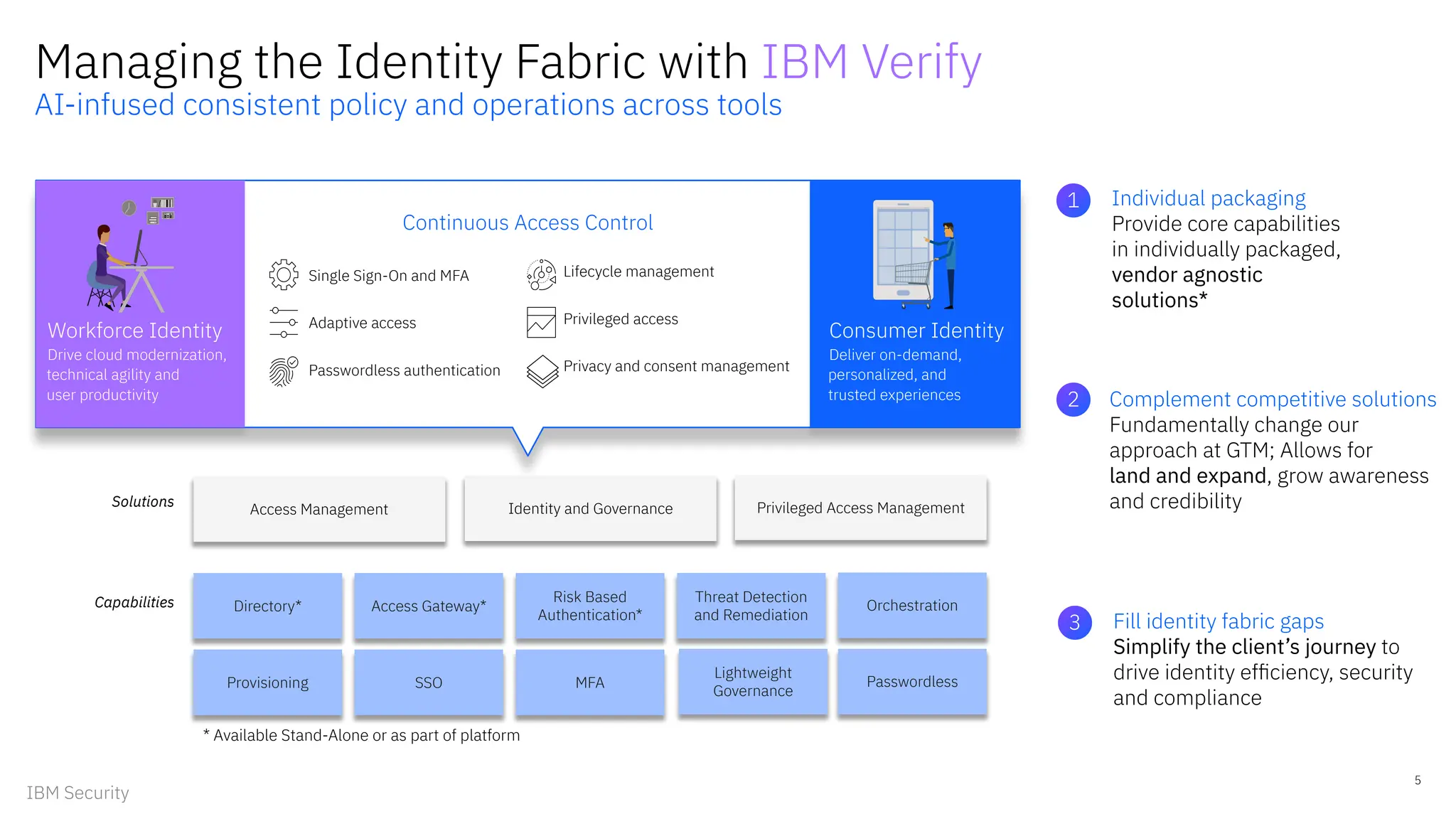
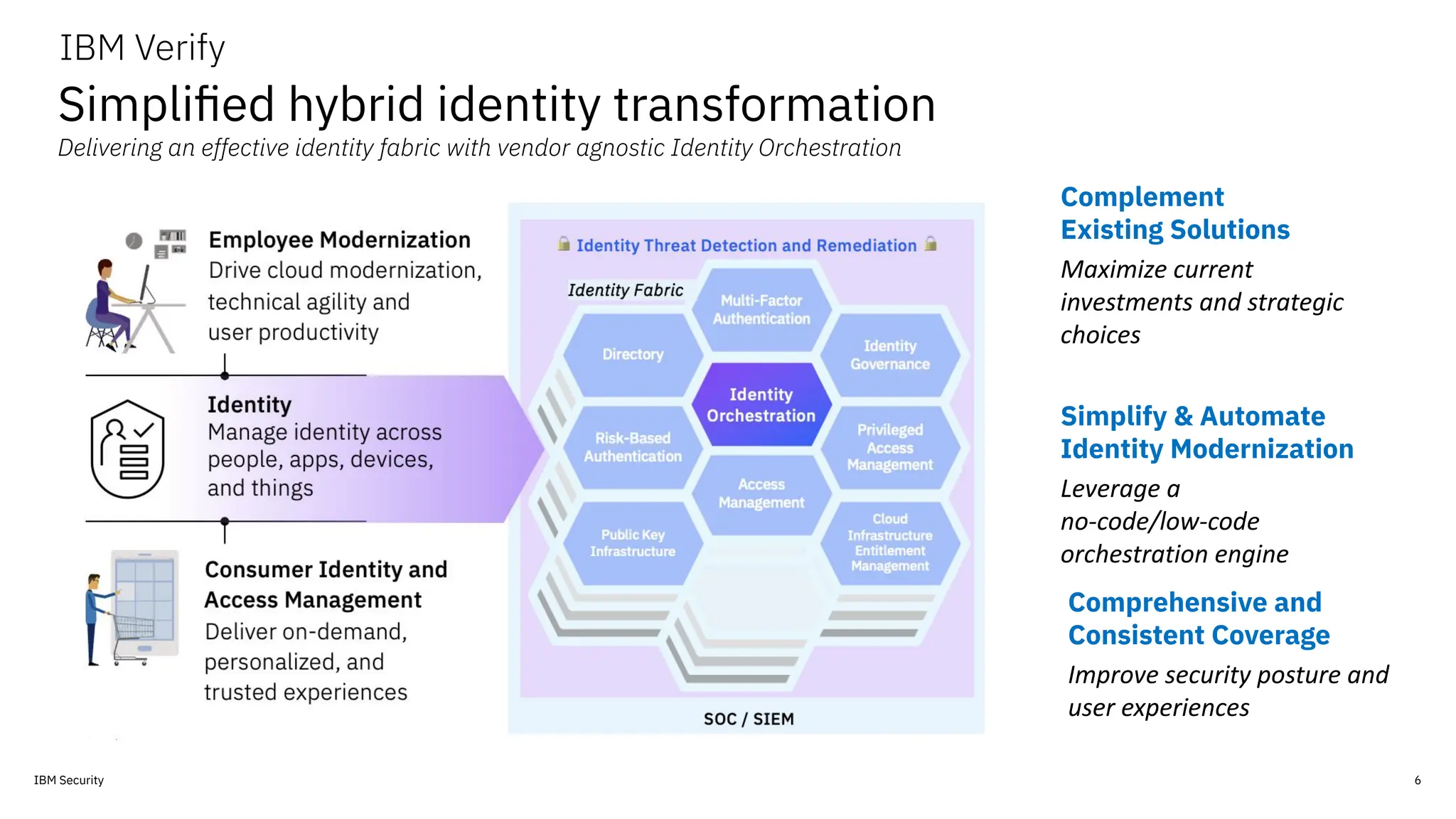
The document discusses the complexities and challenges of managing digital identities in hybrid cloud environments, emphasizing the fragmentation of identity solutions and the risks associated with inconsistent security policies. It proposes an integrated identity strategy using IBM Verify, which includes modern authentication methods, identity orchestration, and threat detection to enhance security and user experience. Additionally, it outlines a no-cost workshop to help organizations identify gaps in their identity management capabilities and improve their security posture.