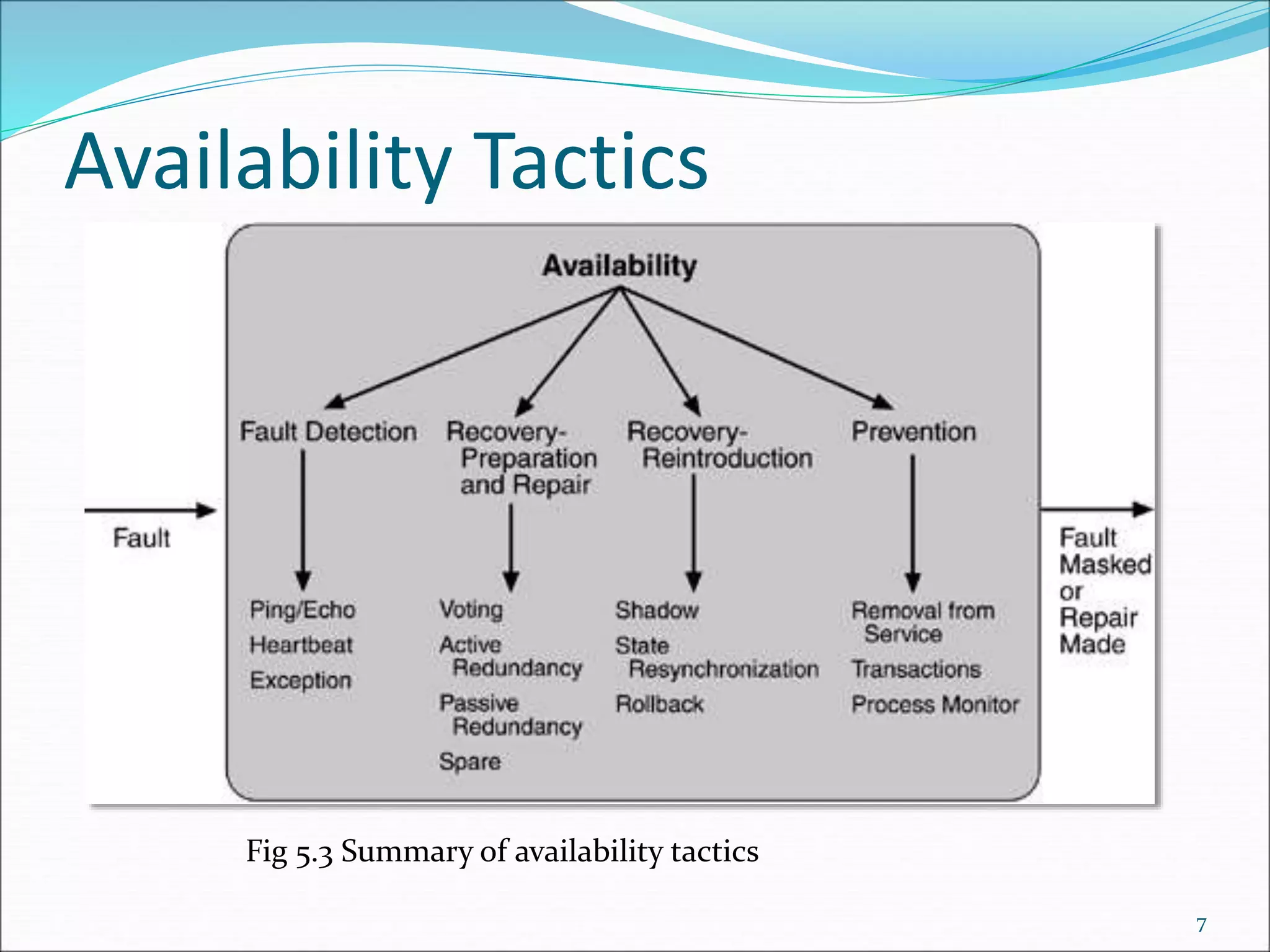
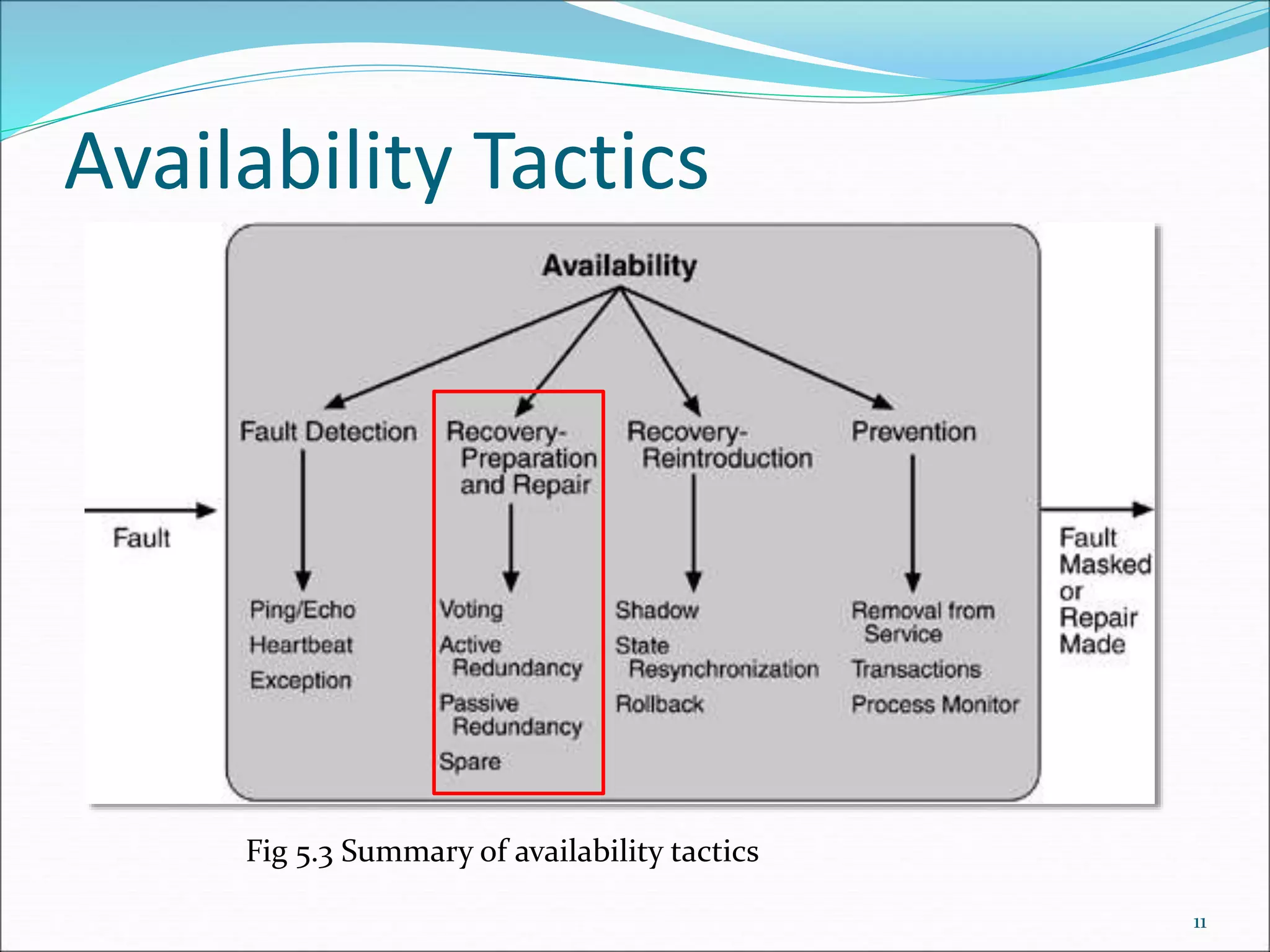
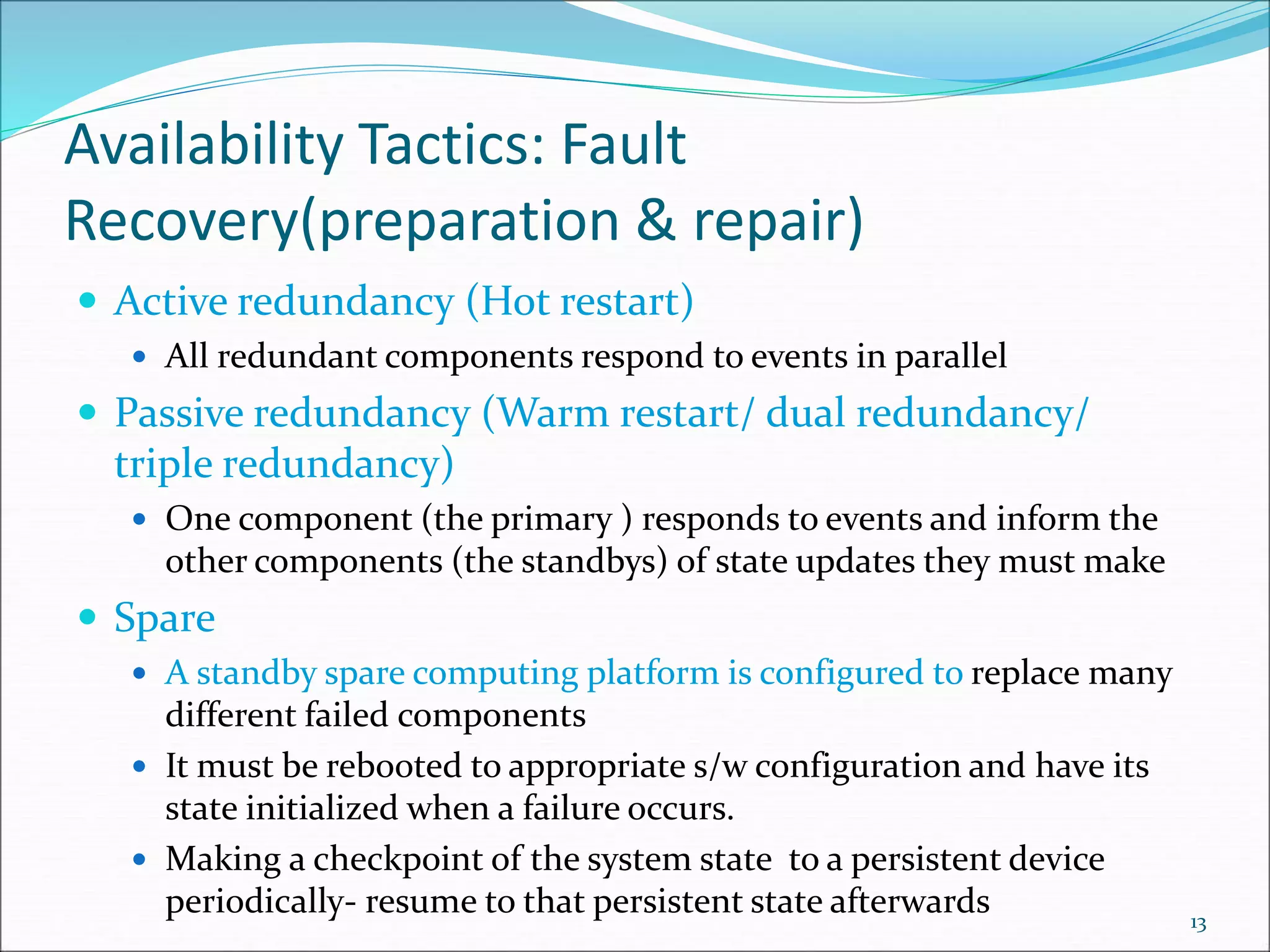
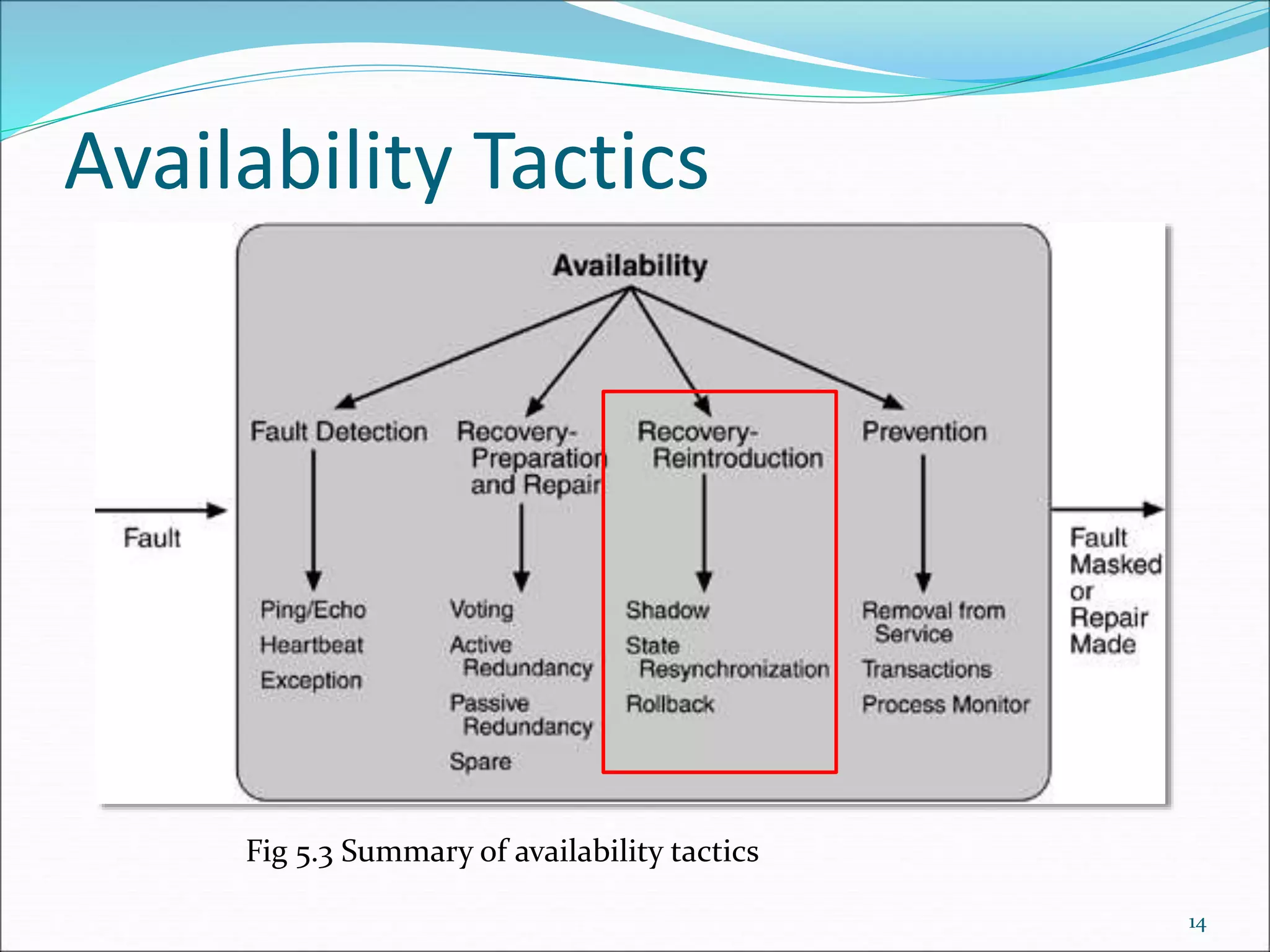
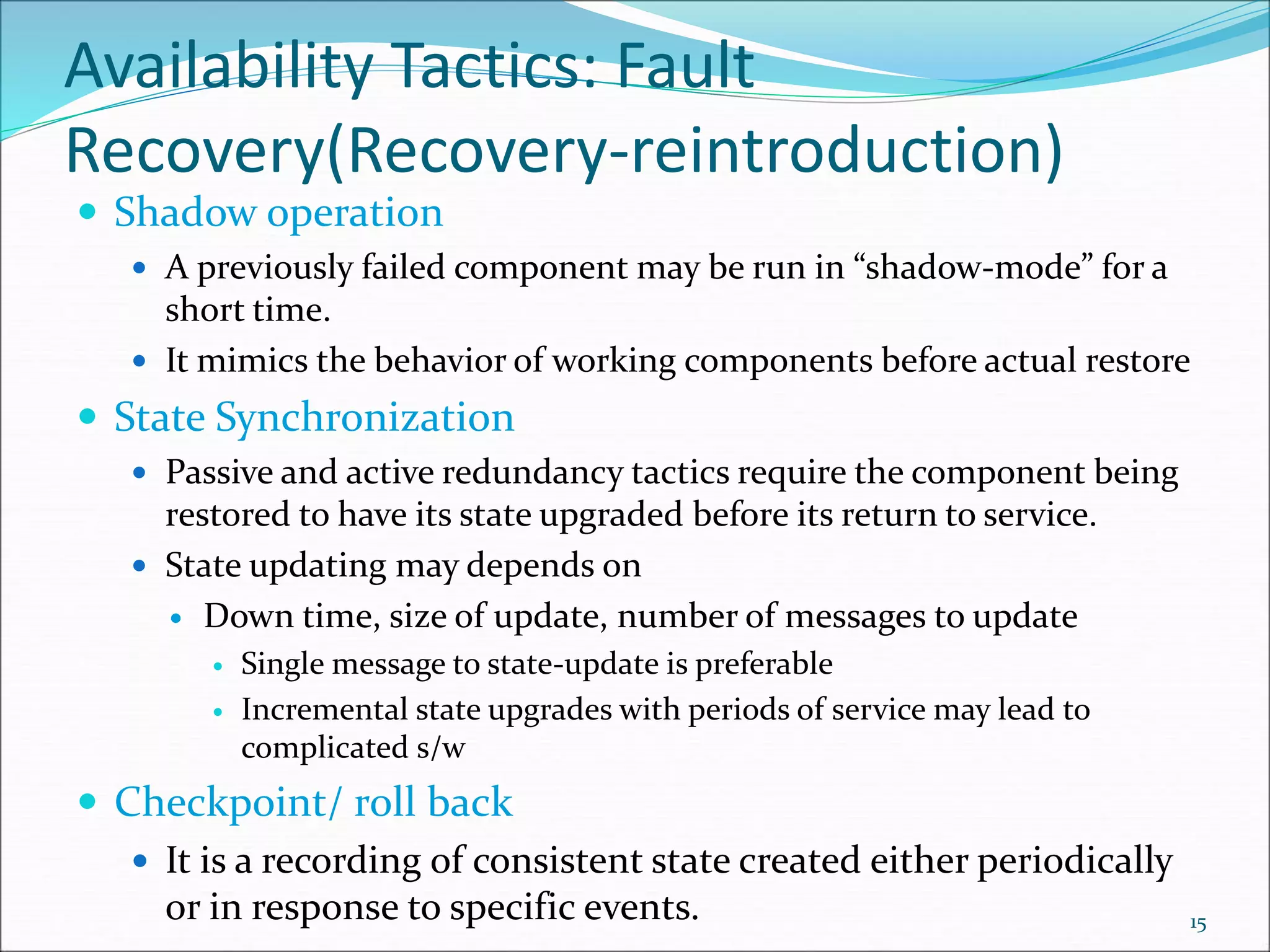
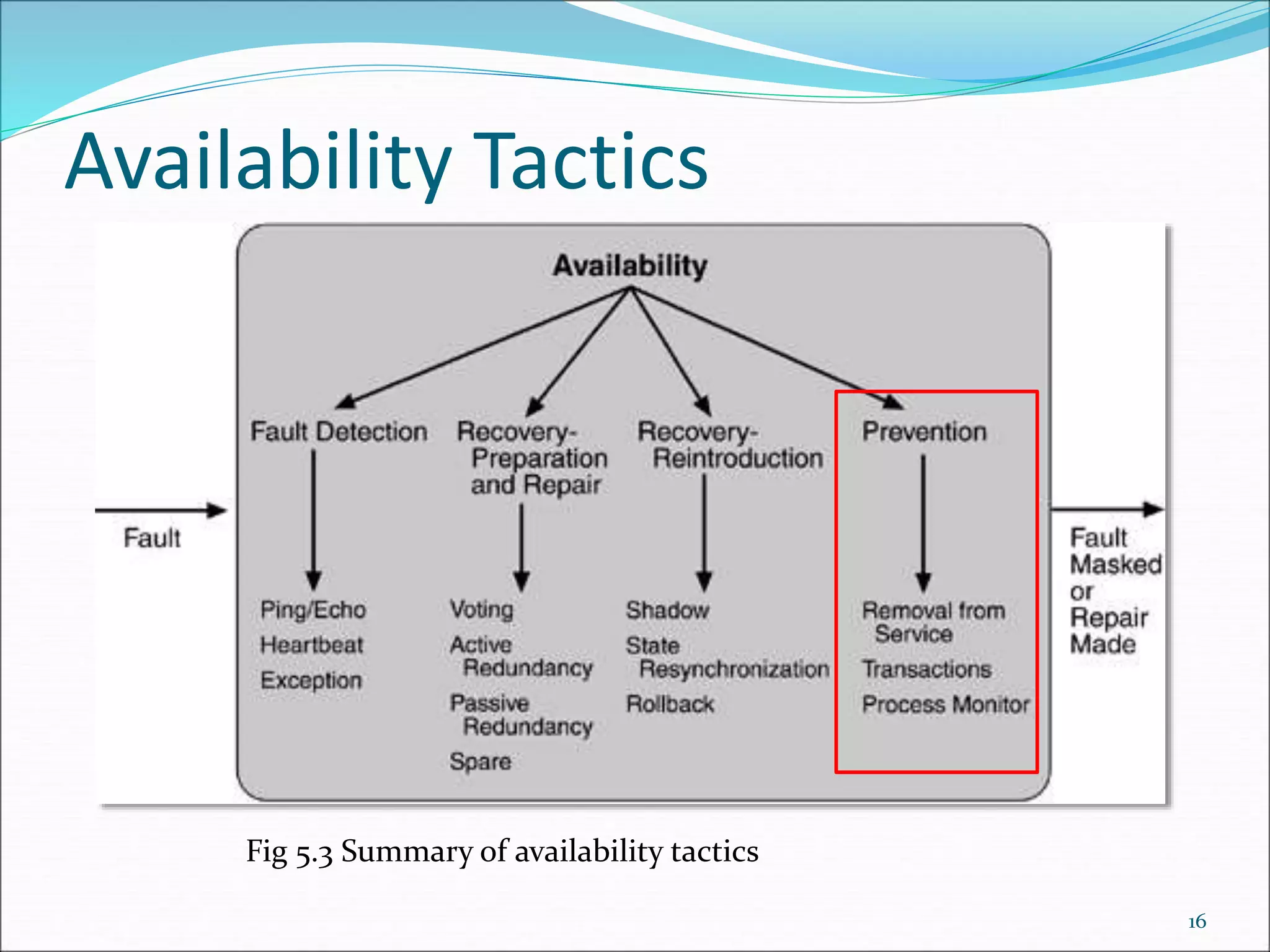
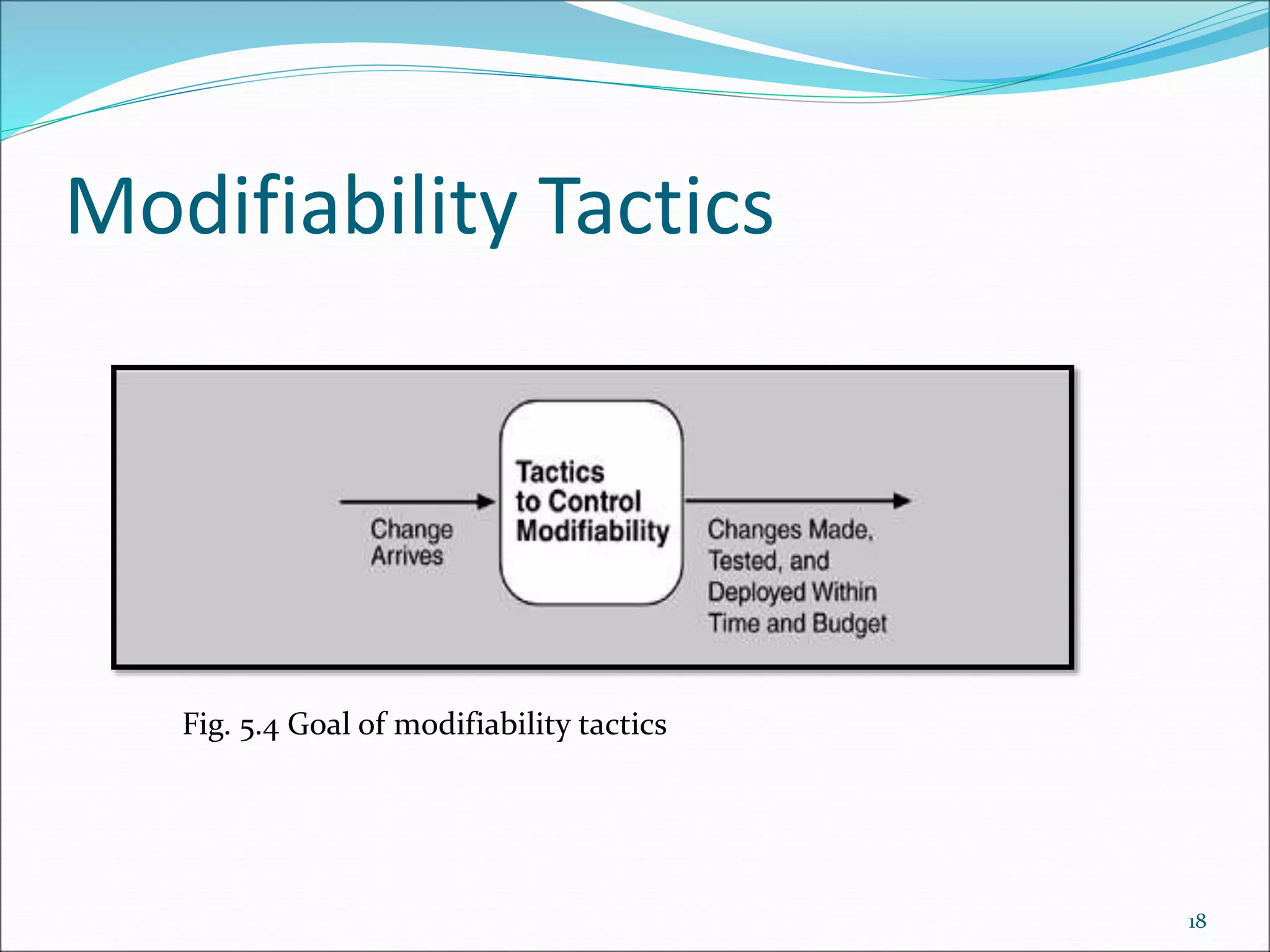
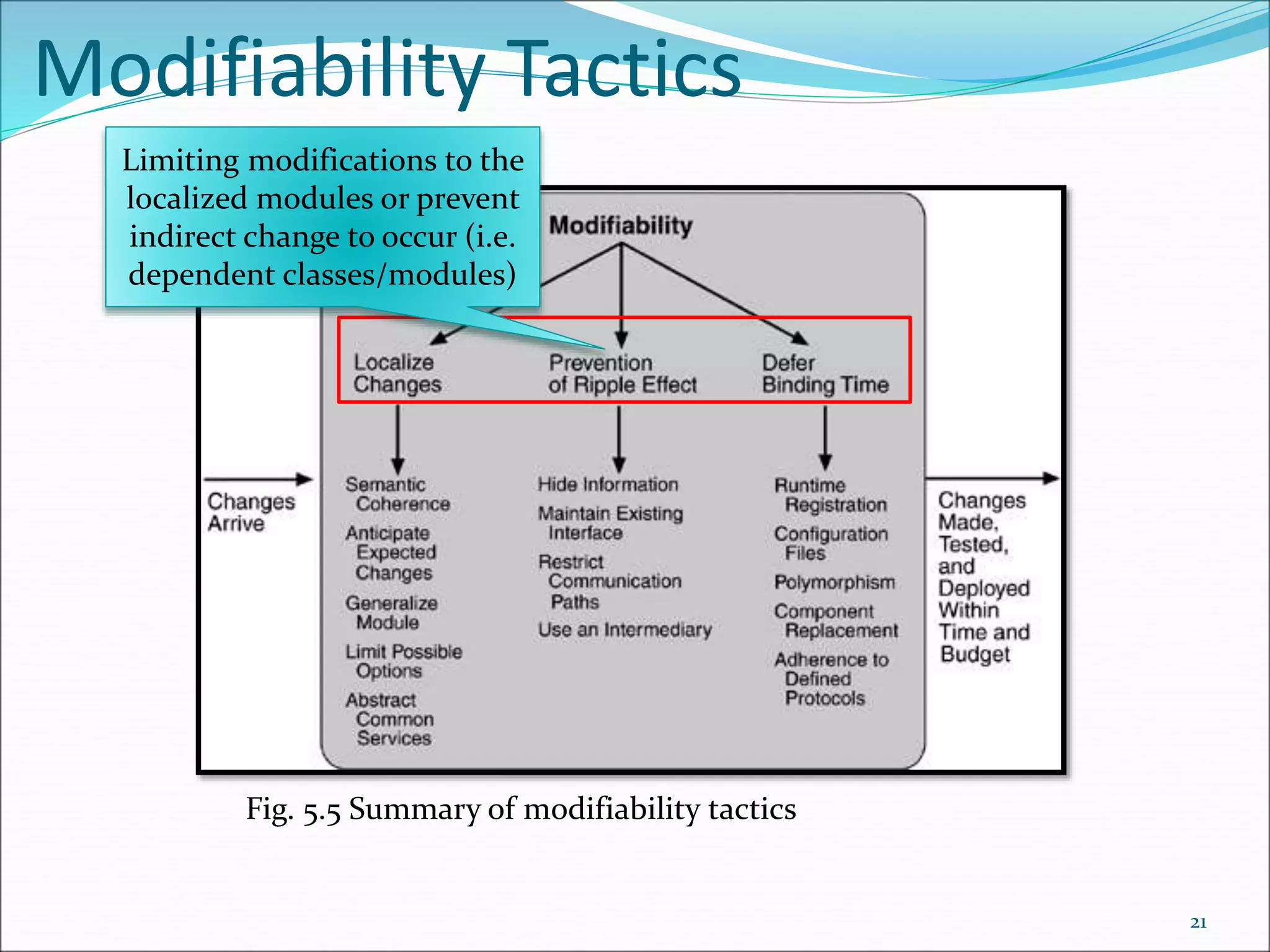
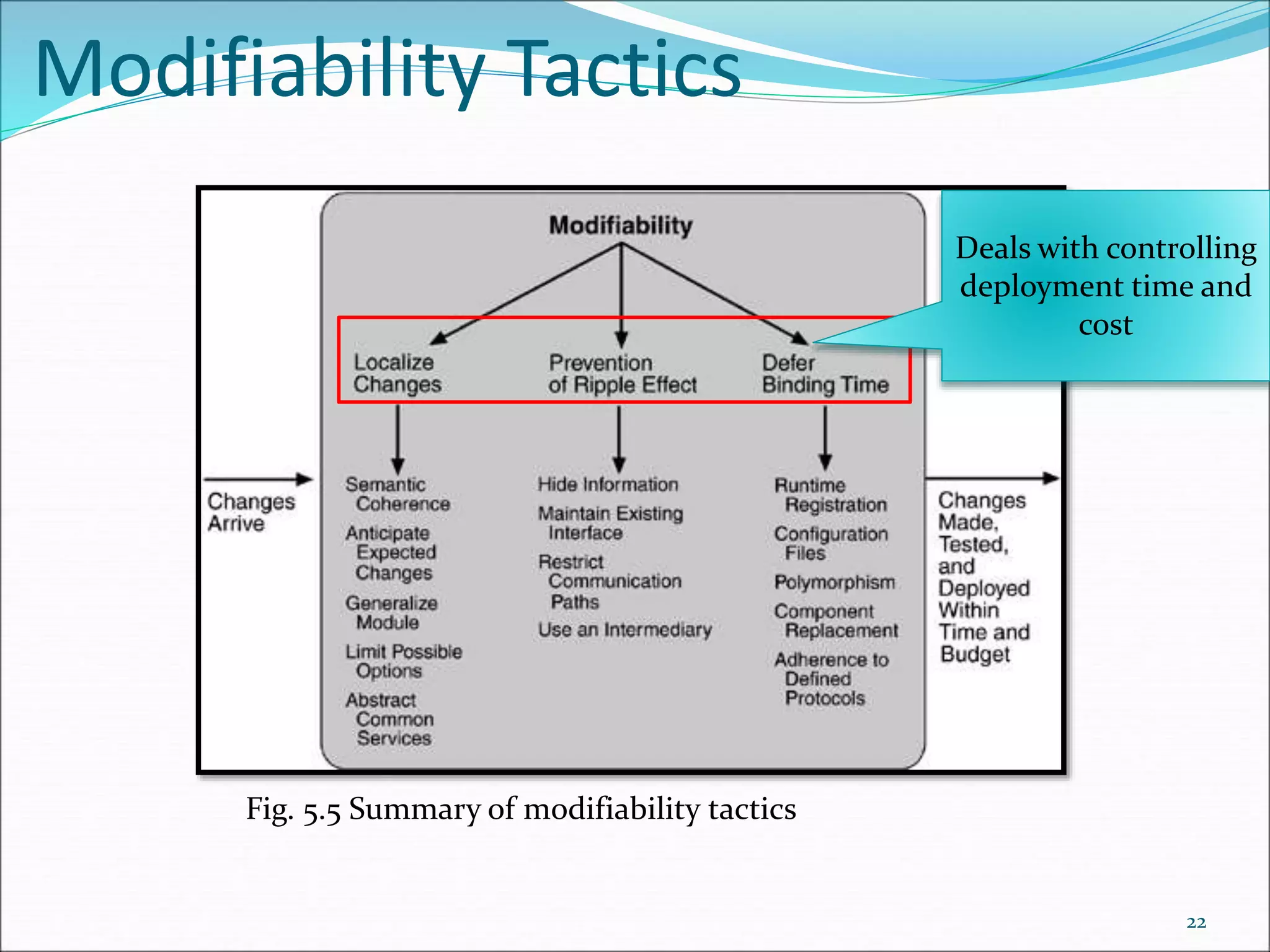
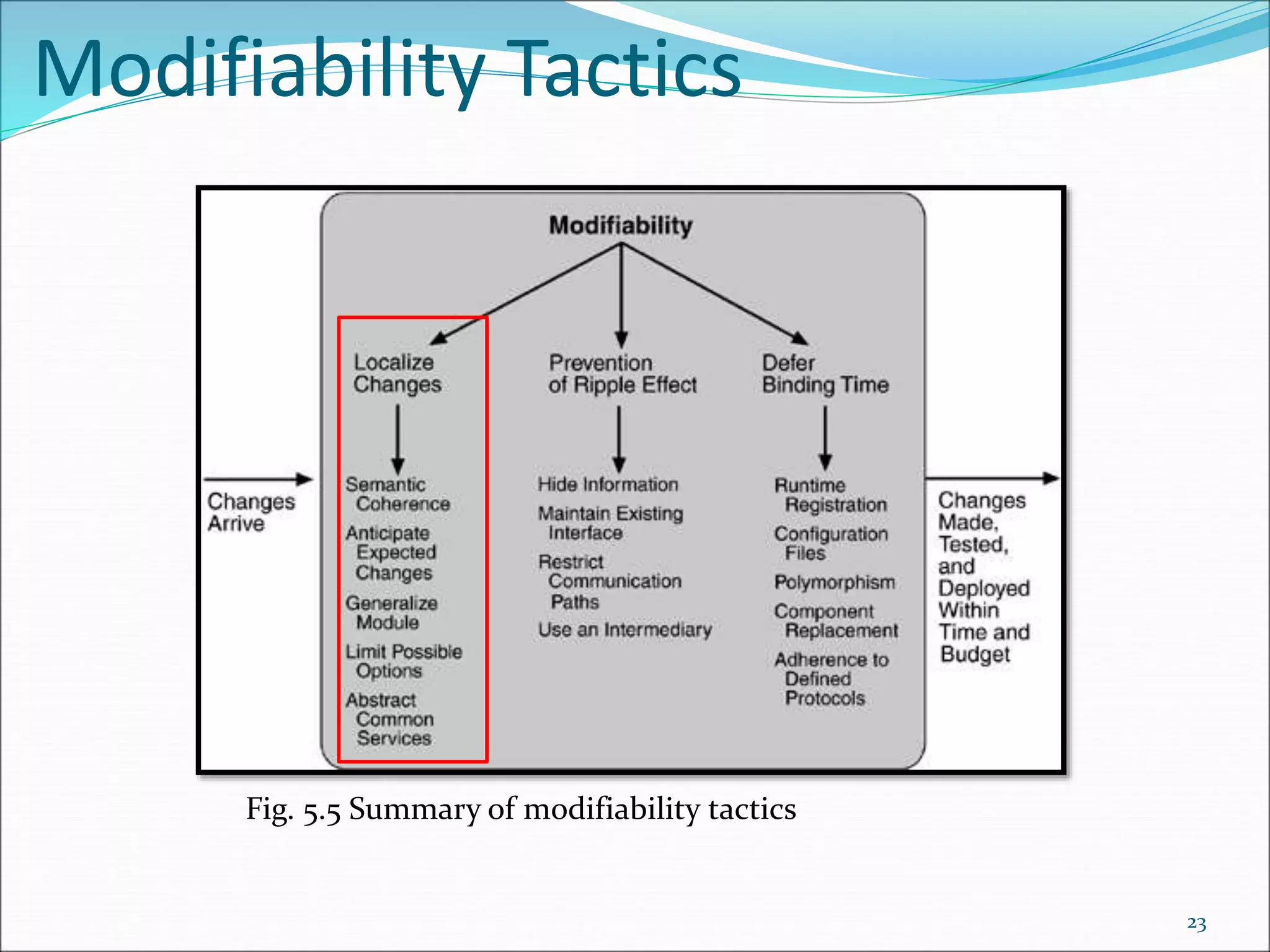
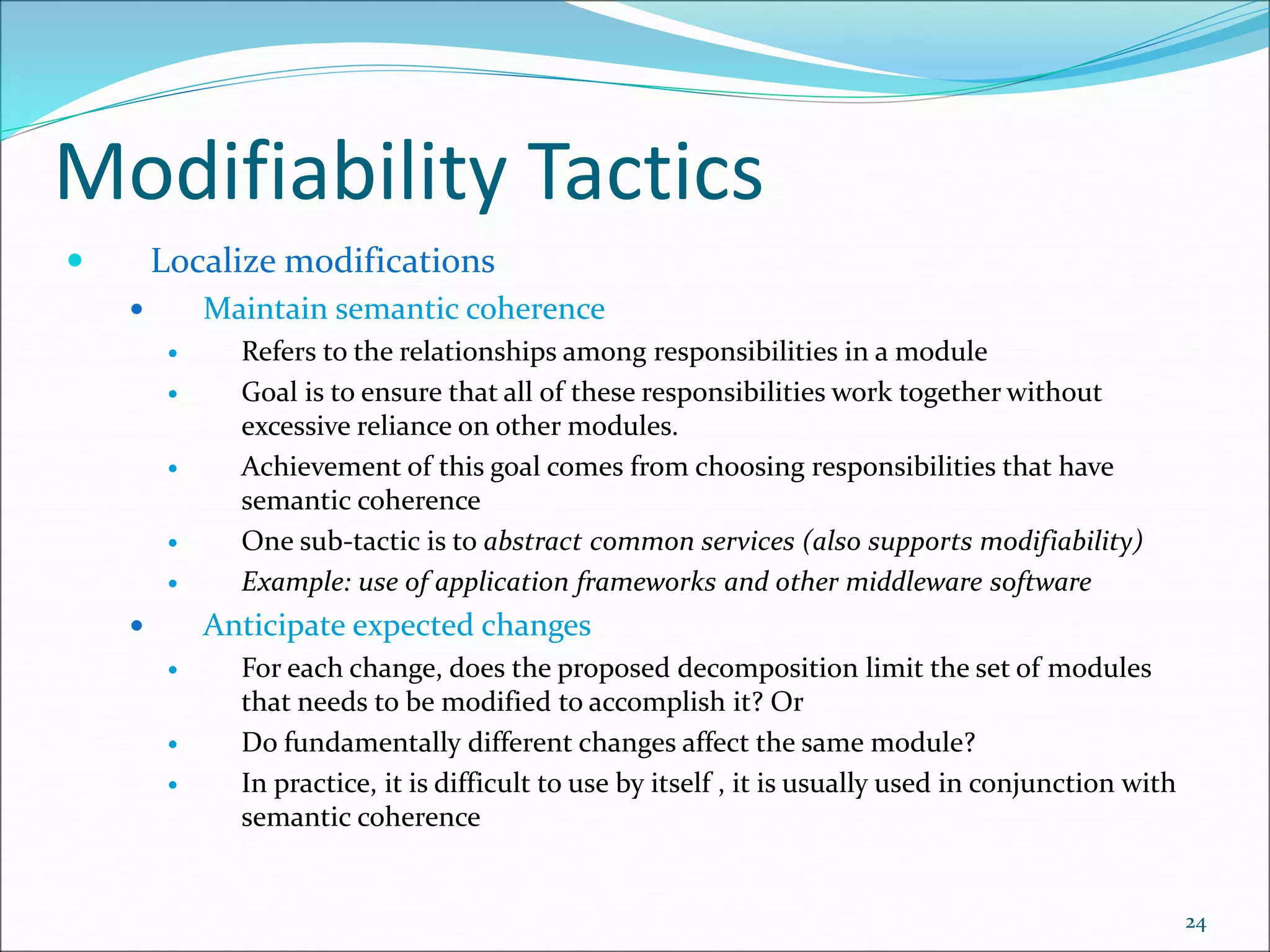
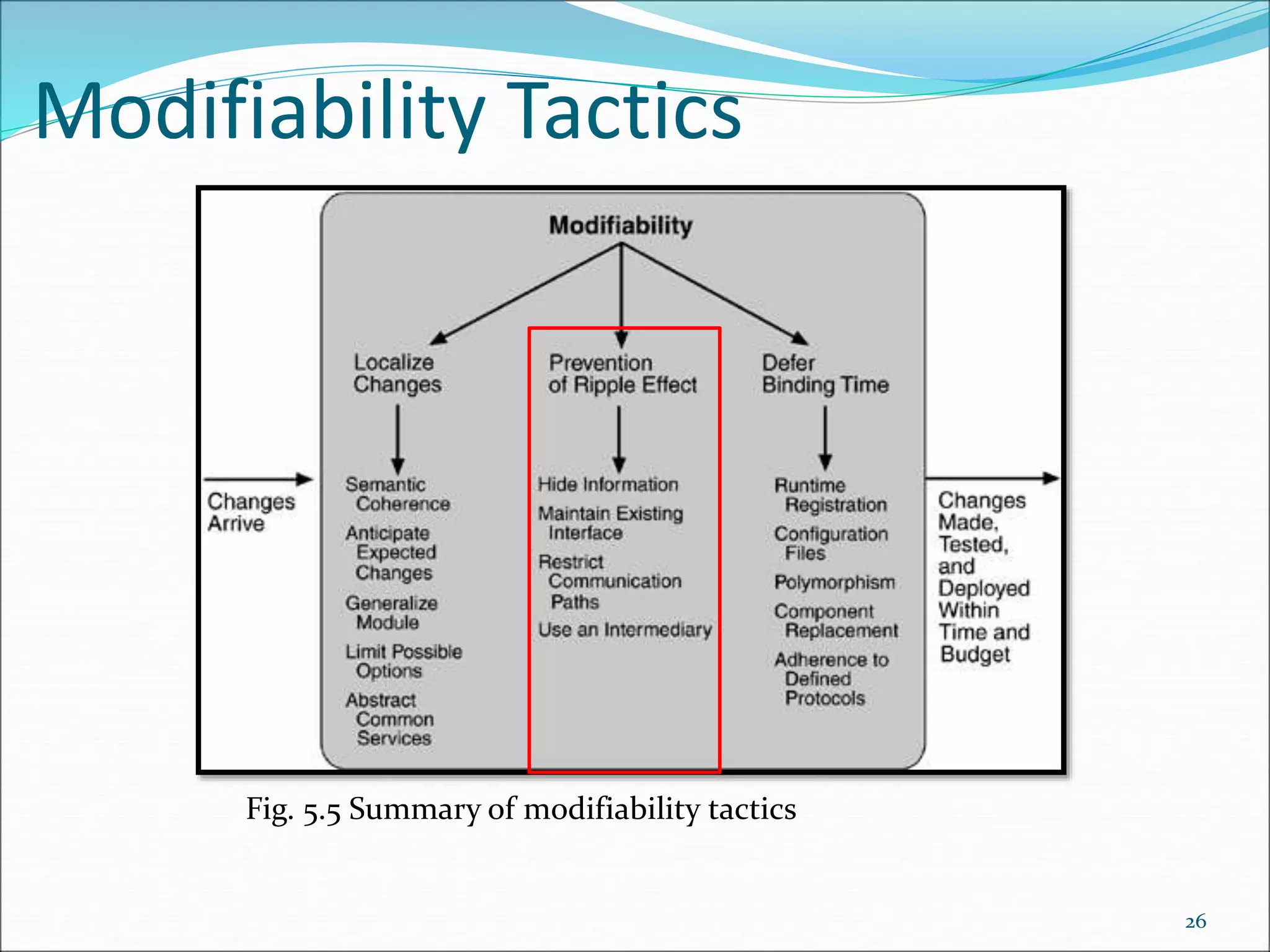
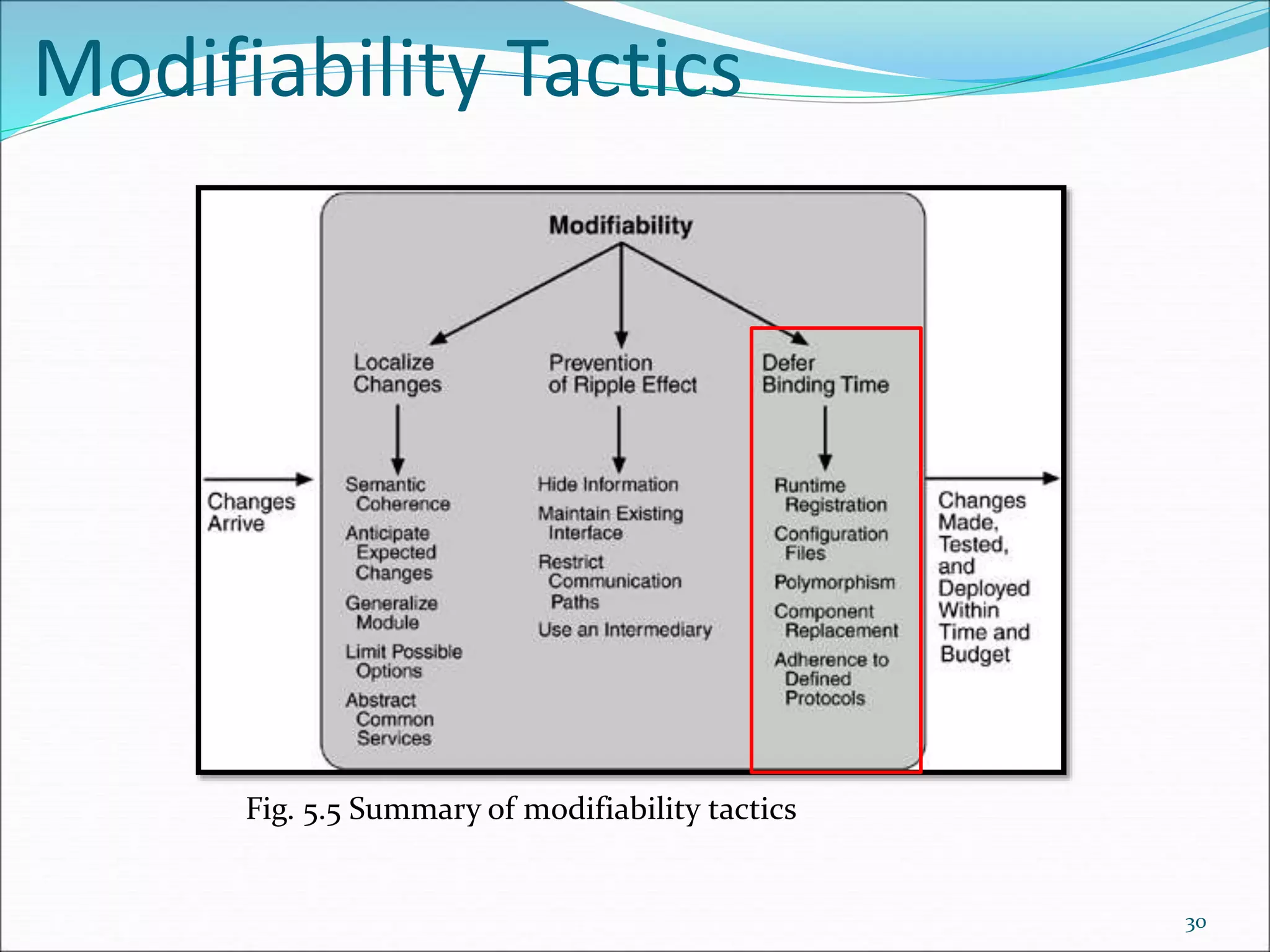
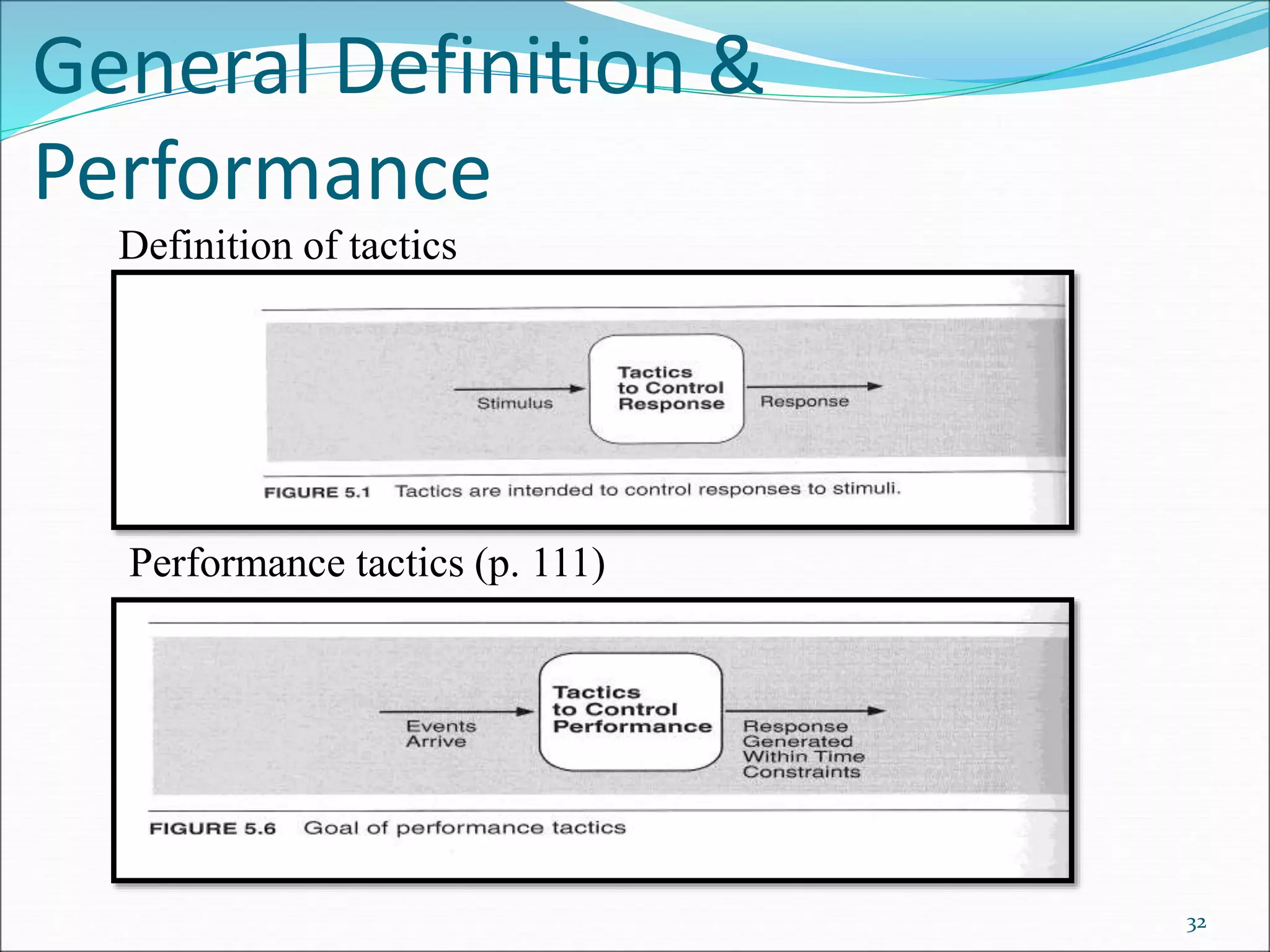
The chapter discusses tactics for achieving qualities like availability and modifiability in software architectures. It defines tactics as design decisions that influence quality attribute responses. For availability, common tactics include redundancy, fault detection using techniques like heartbeat monitoring, and fault recovery through approaches such as voting and state synchronization. Modifiability tactics aim to control the time and cost of changes and include localizing modifications, limiting ripple effects, and techniques for managing dependencies between modules. Performance tactics focus on generating responses to events within time constraints.