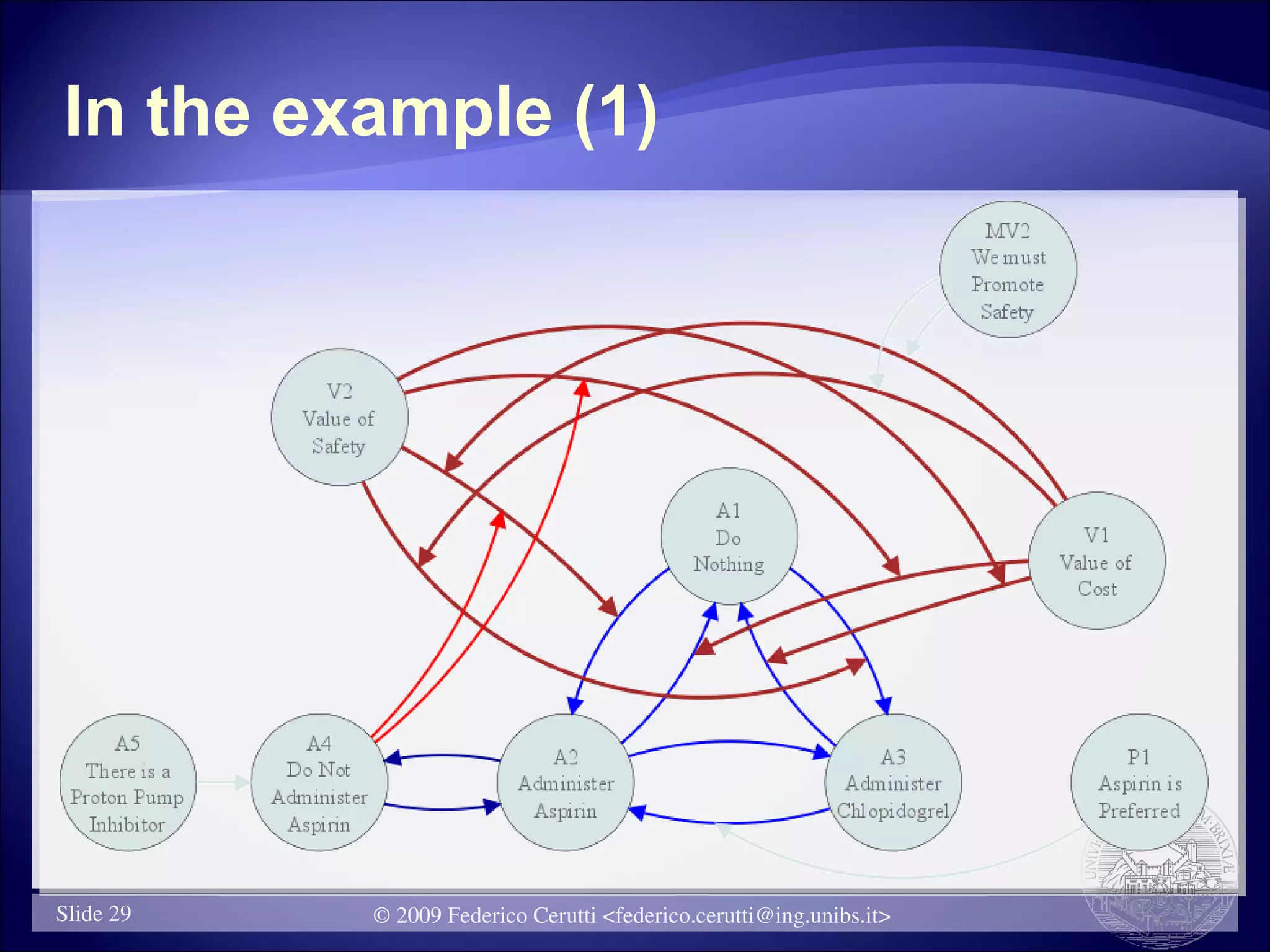
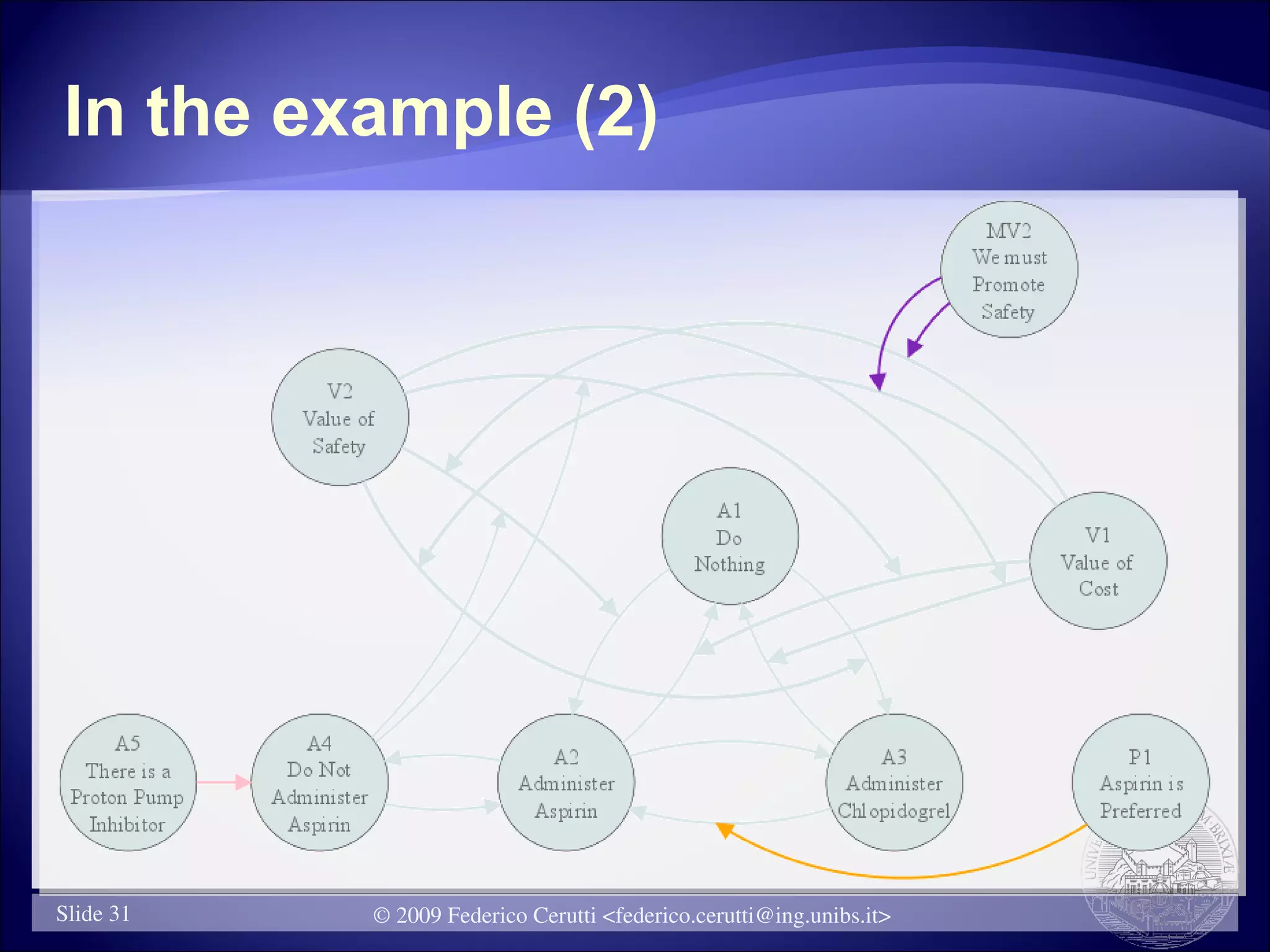
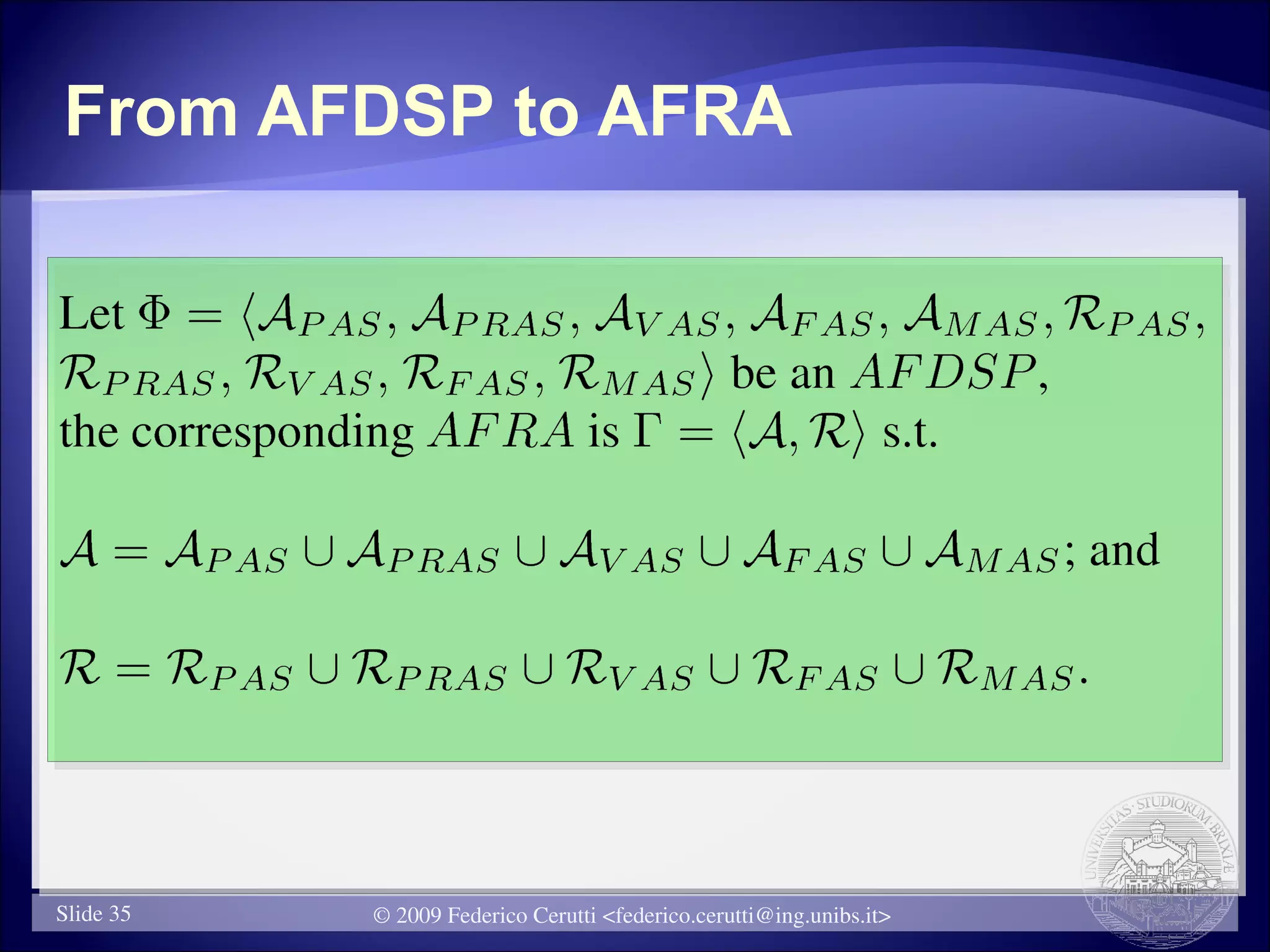
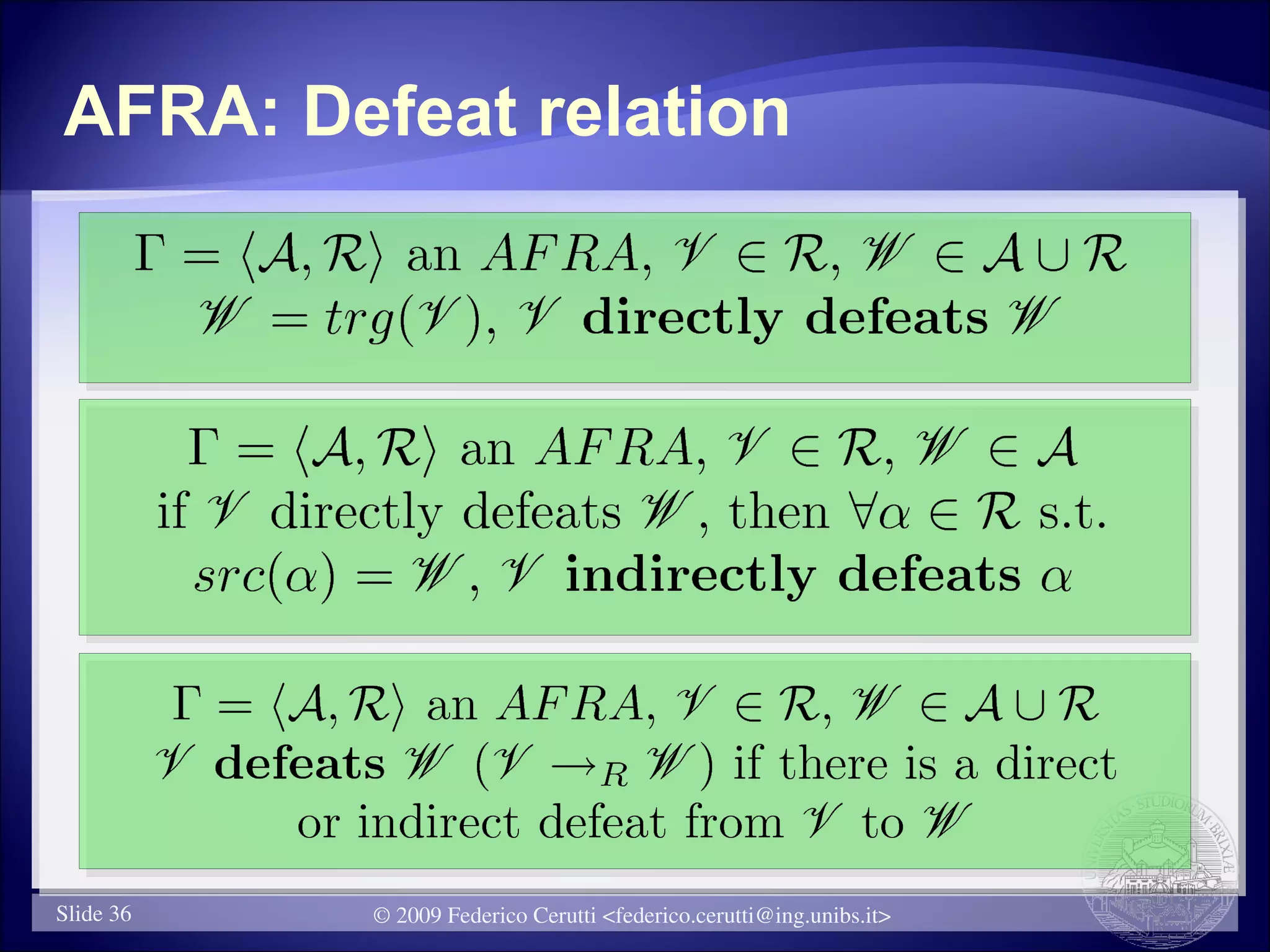
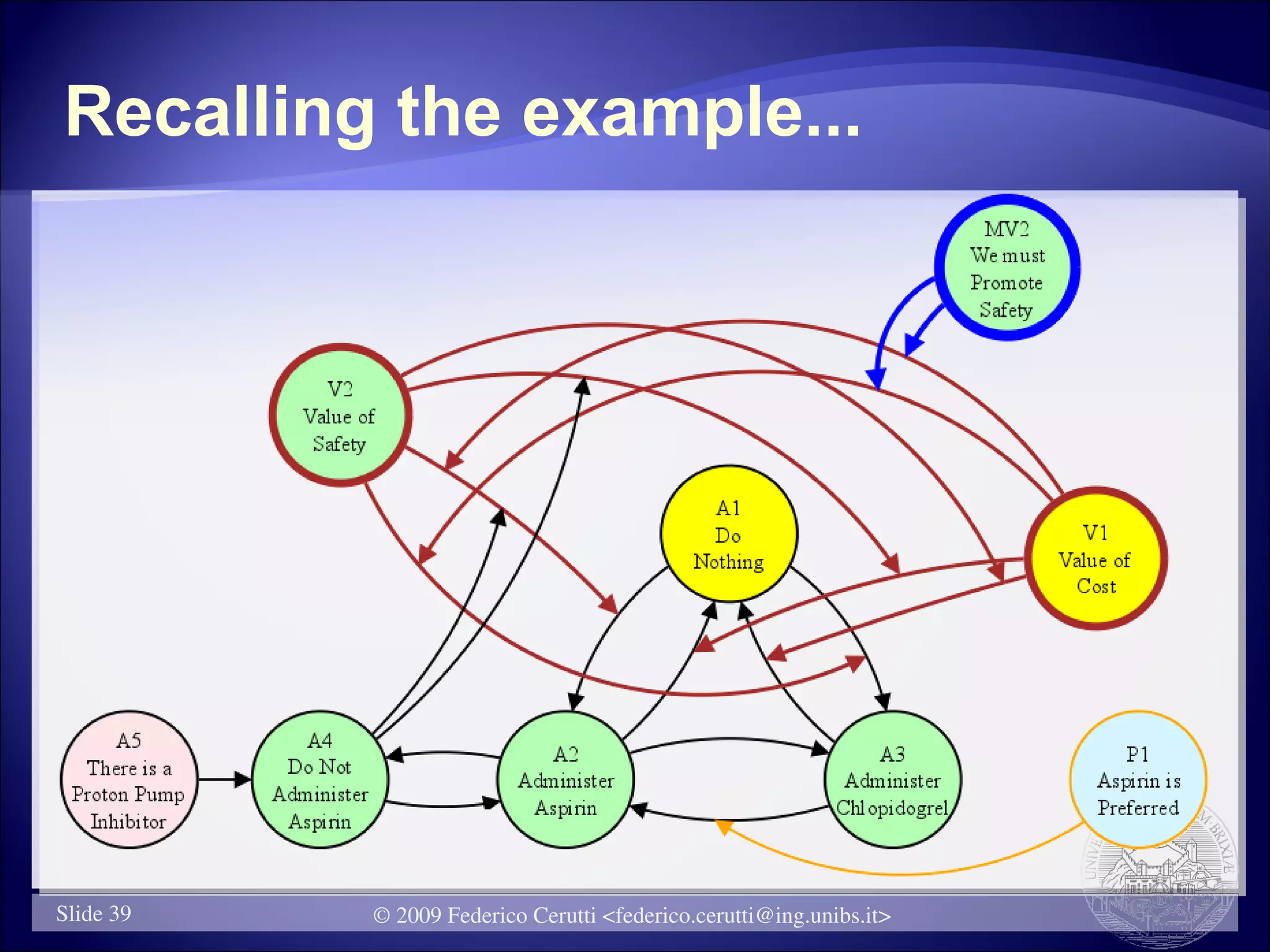
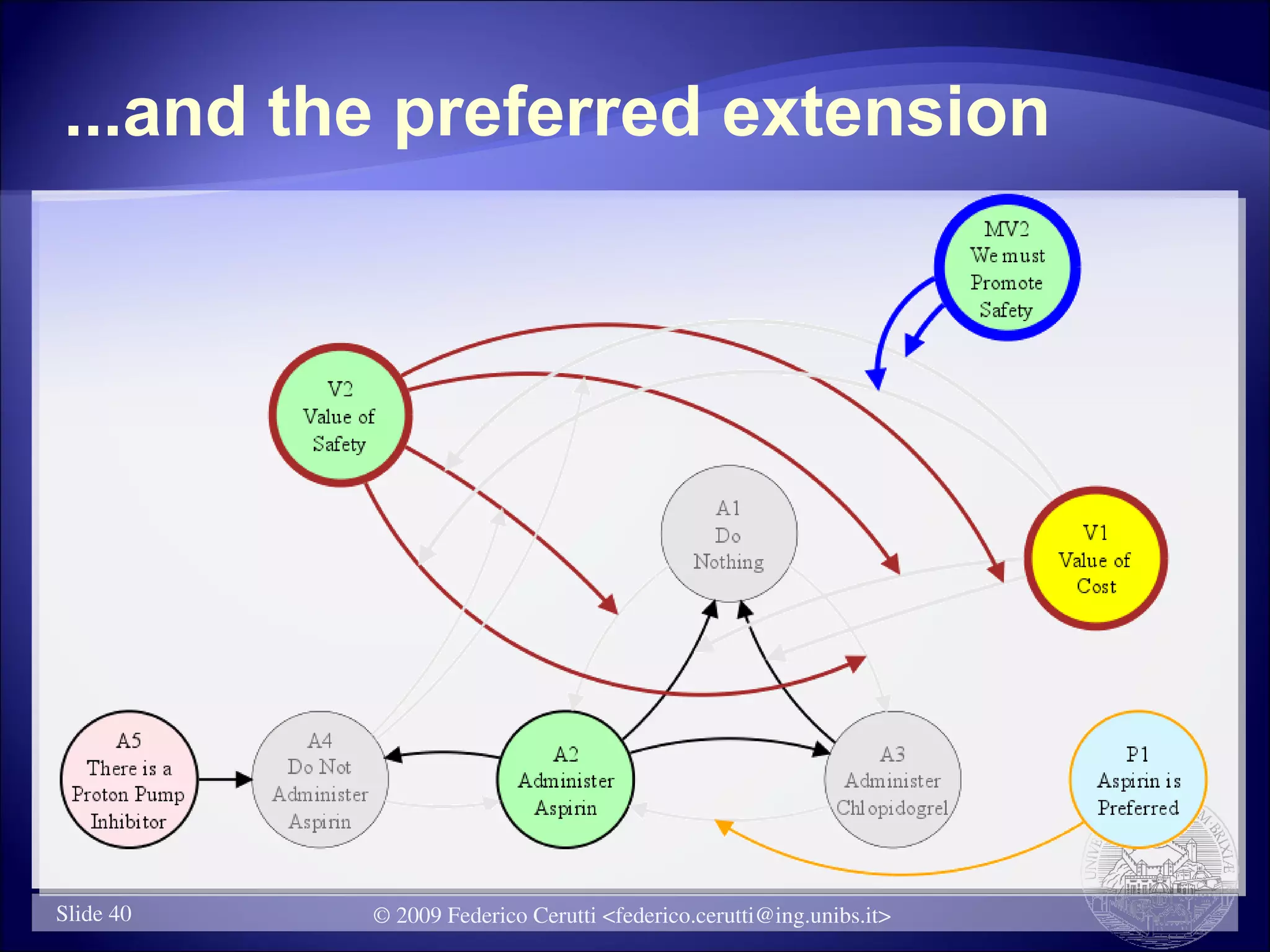
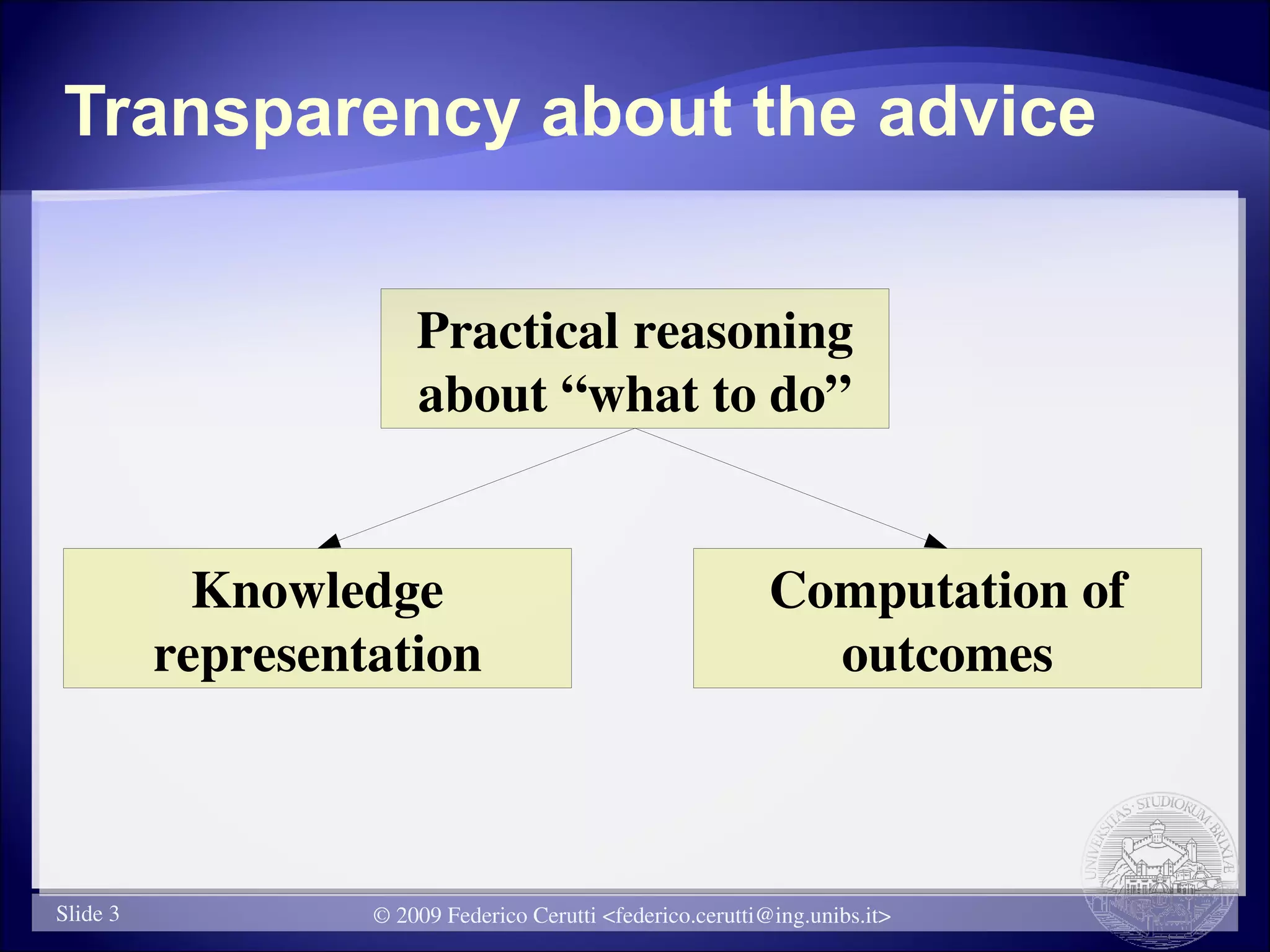
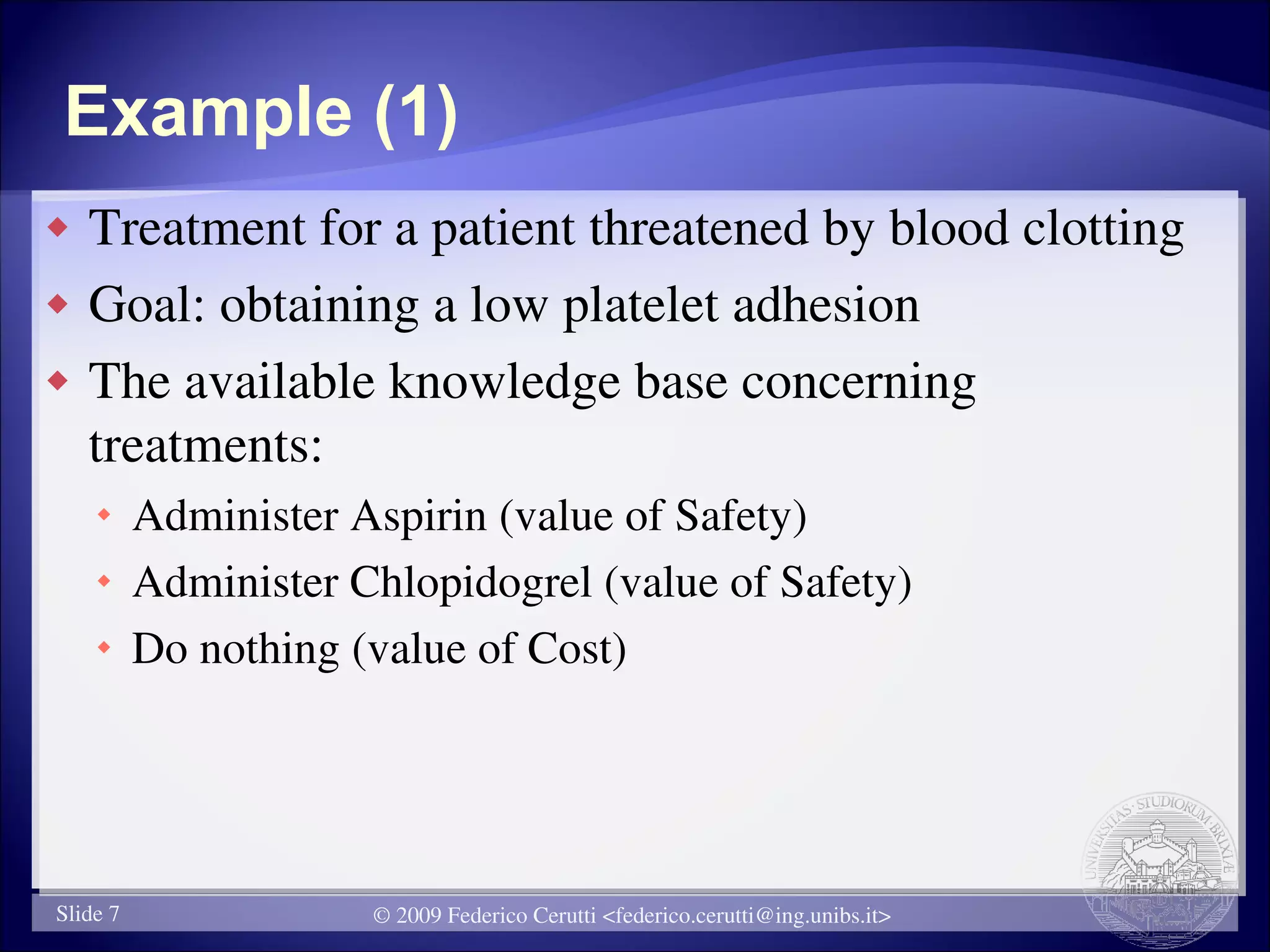
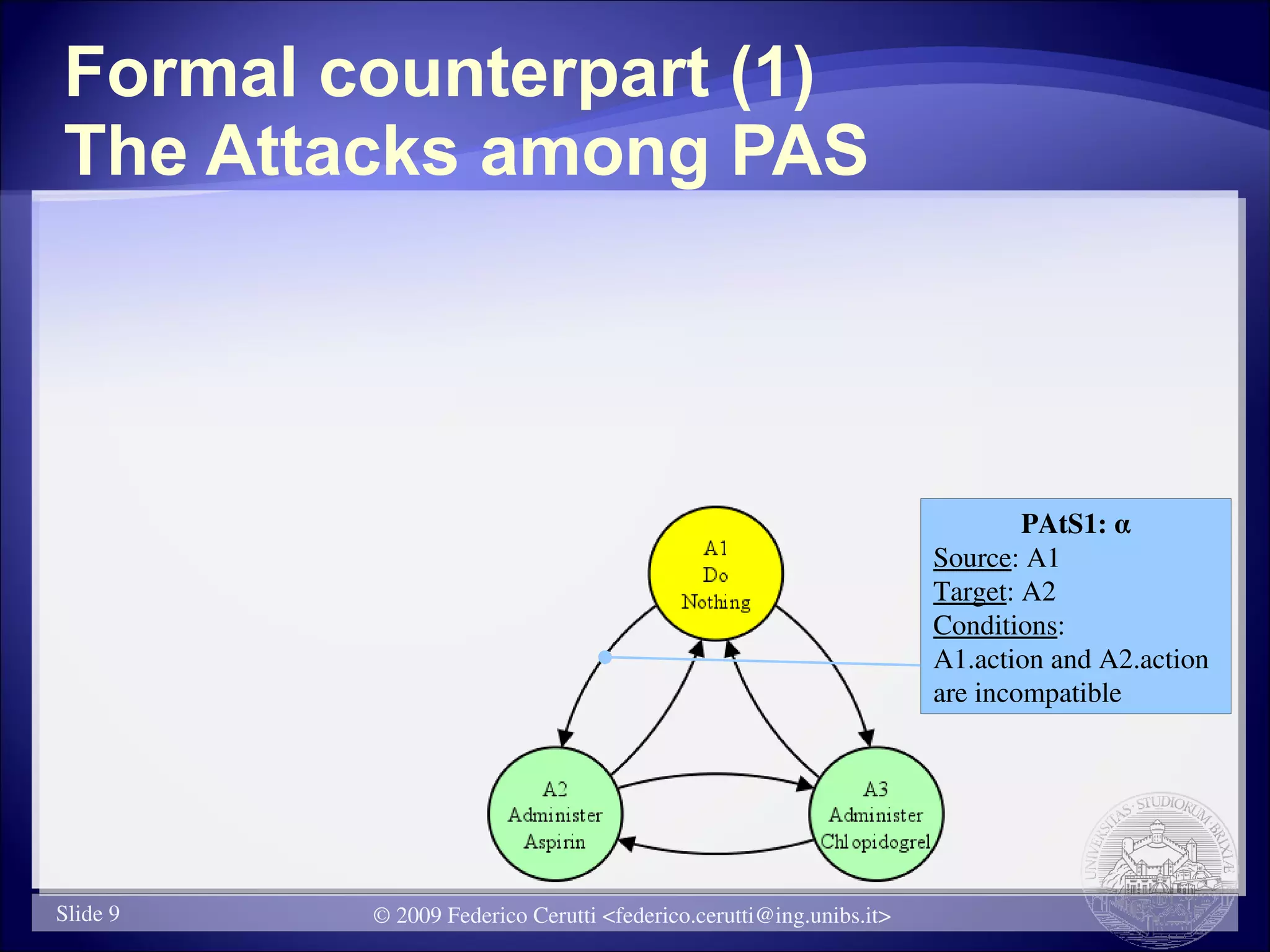
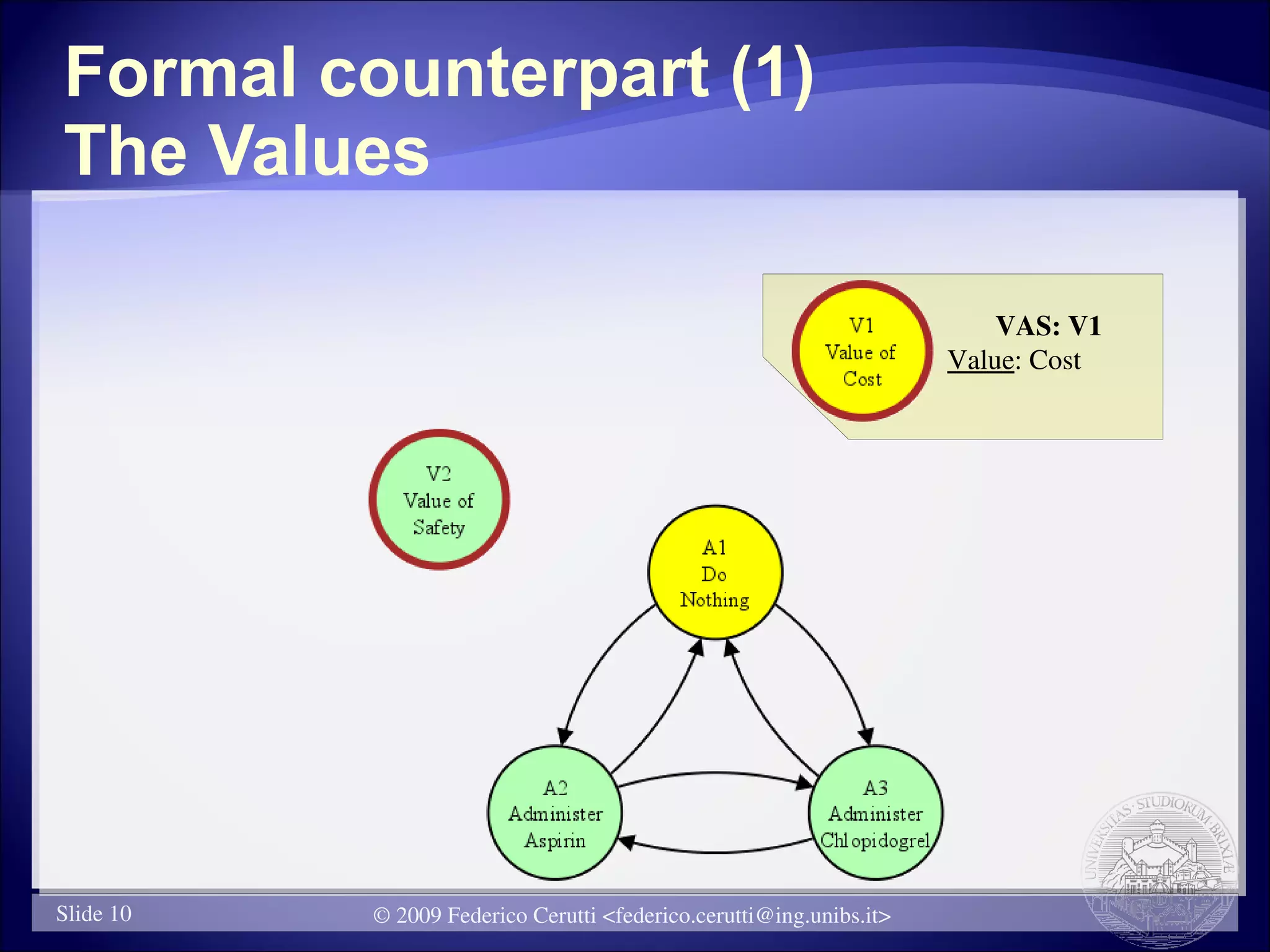
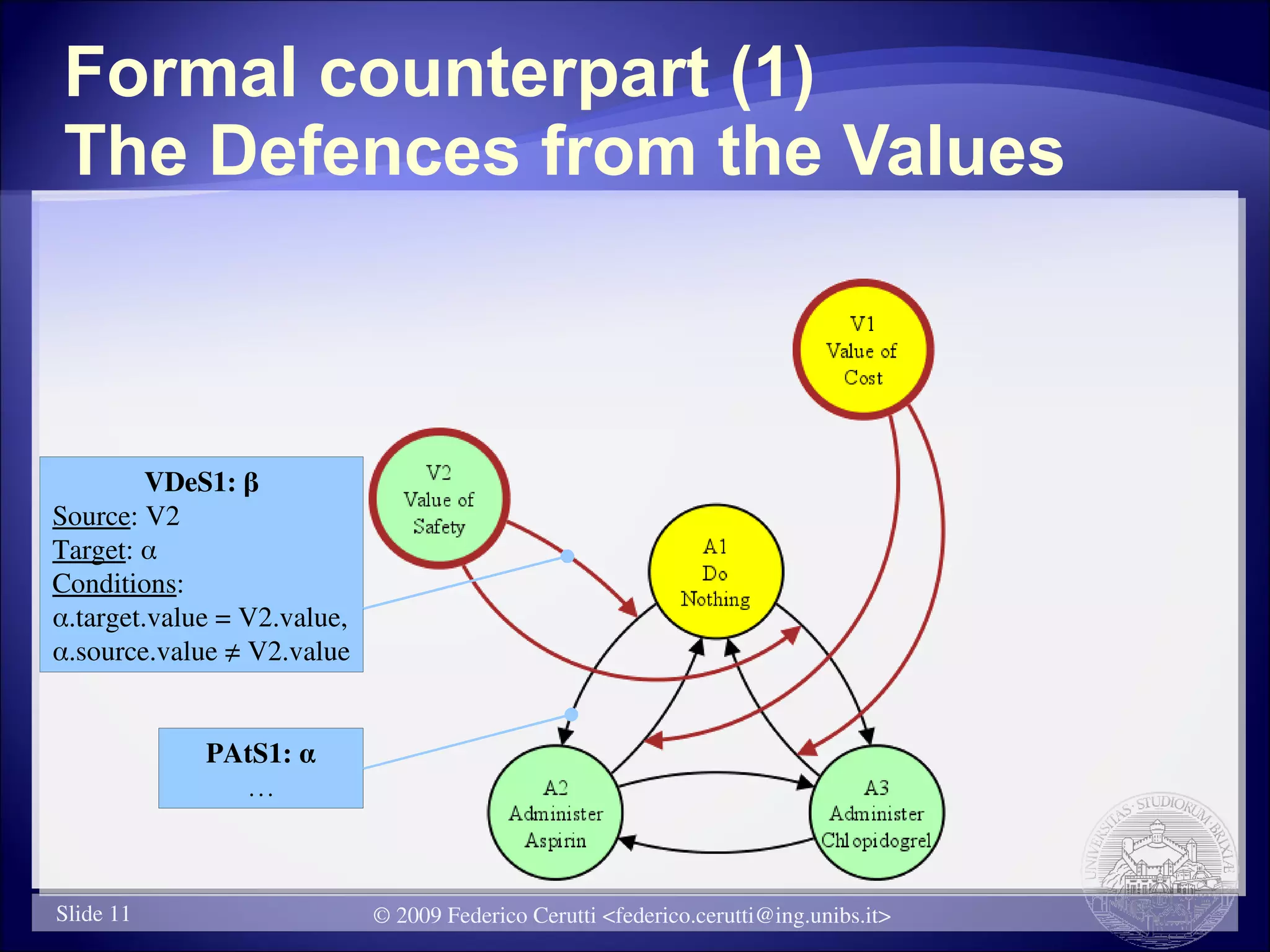
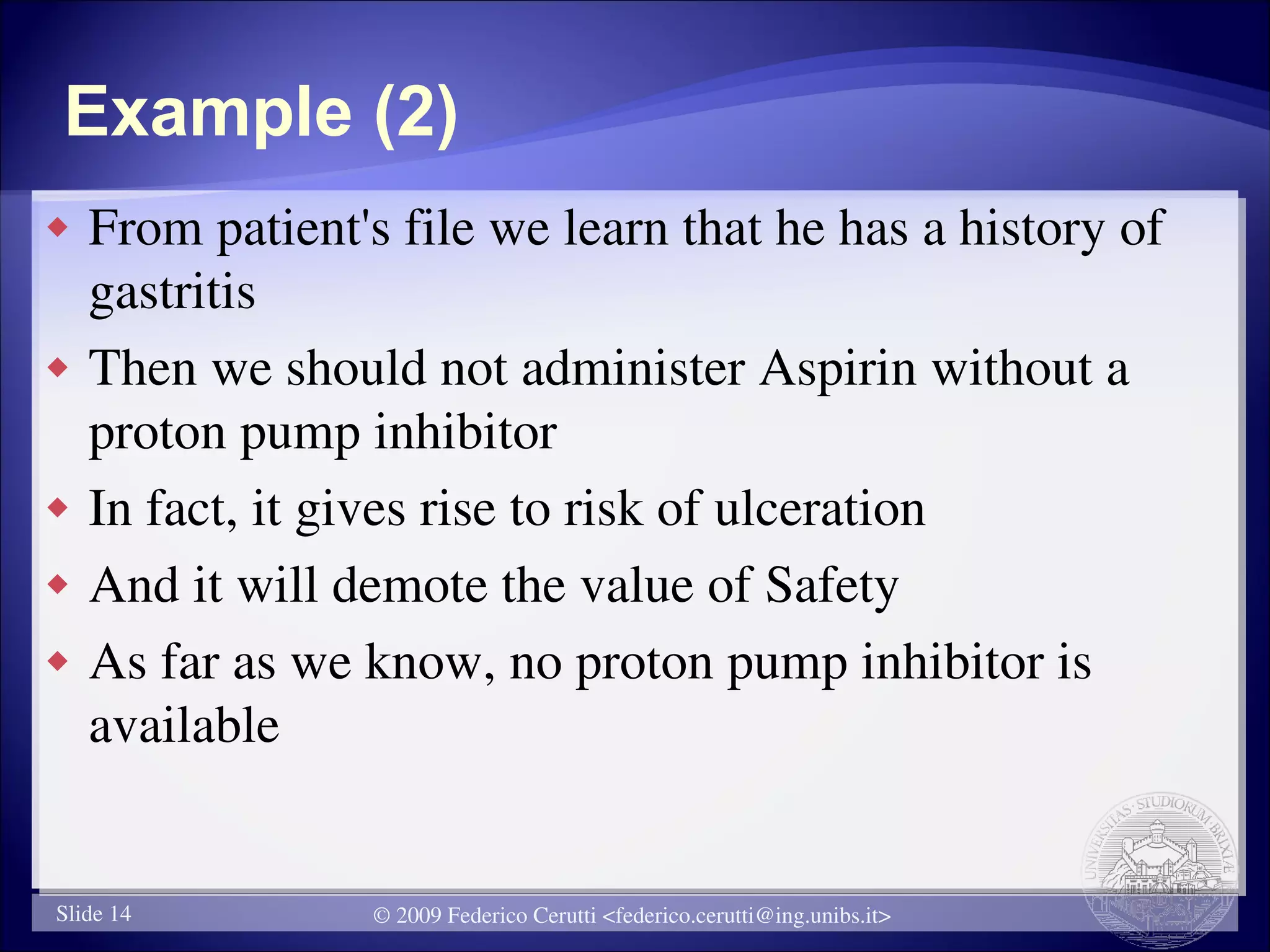
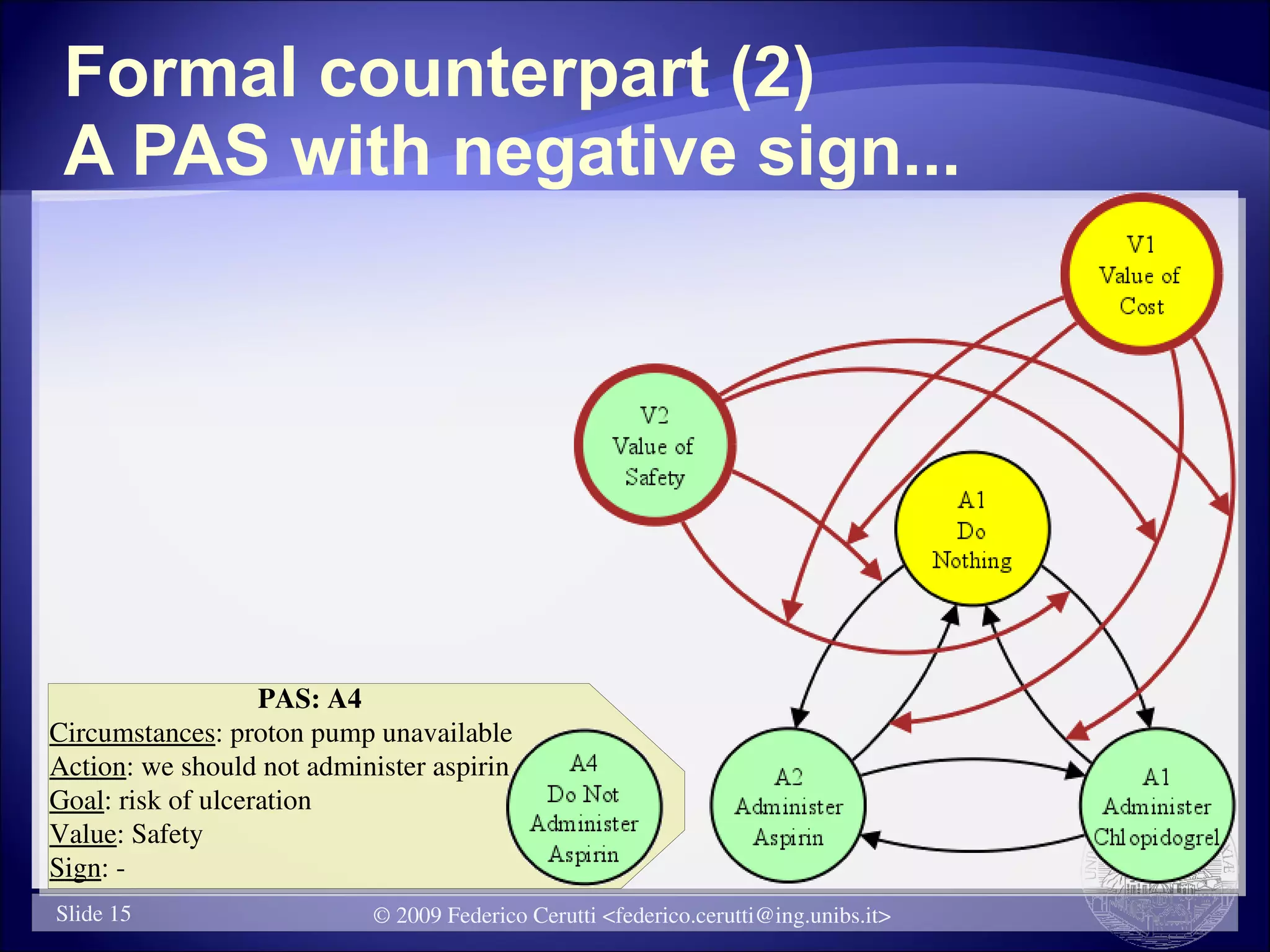
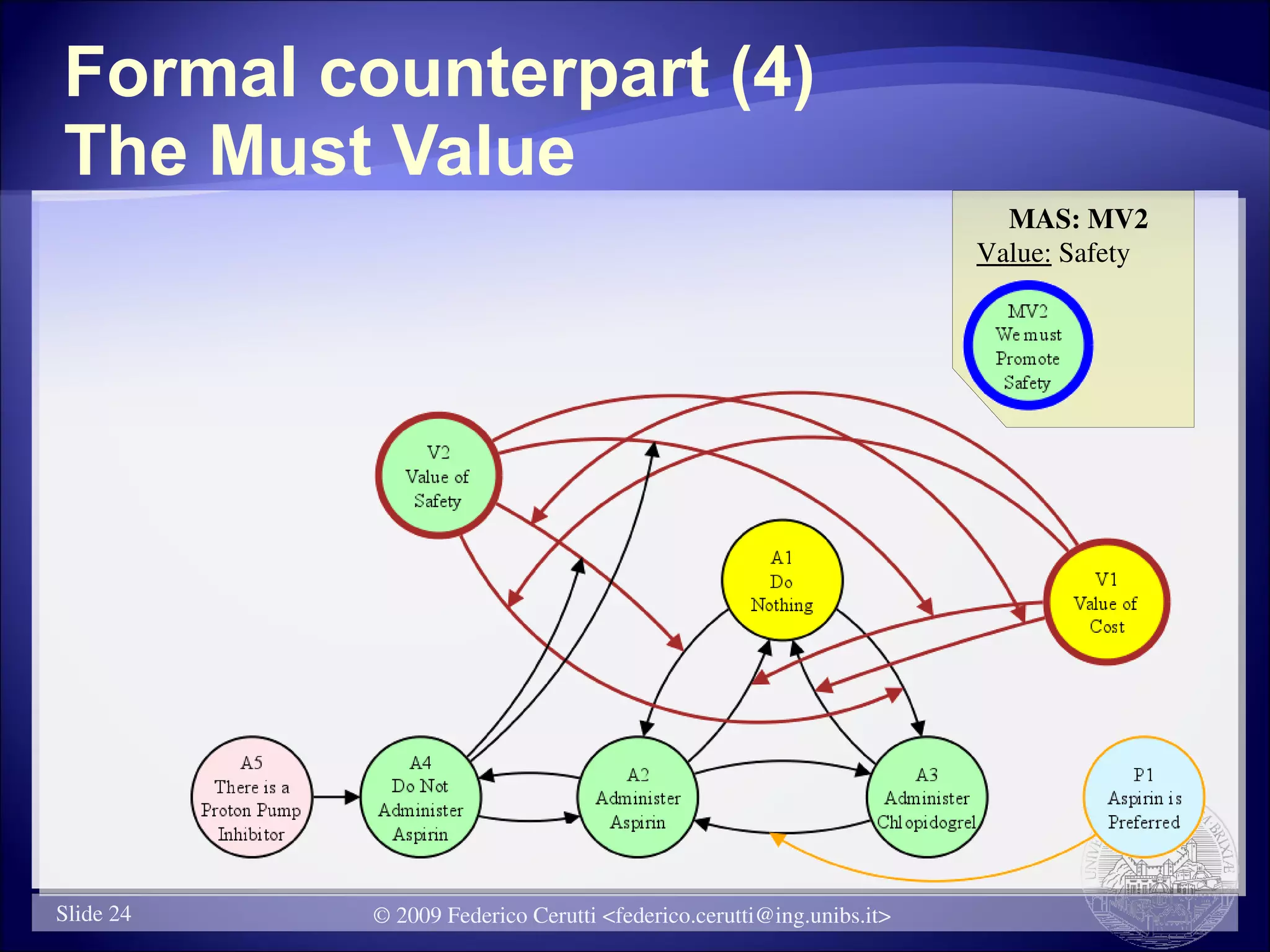
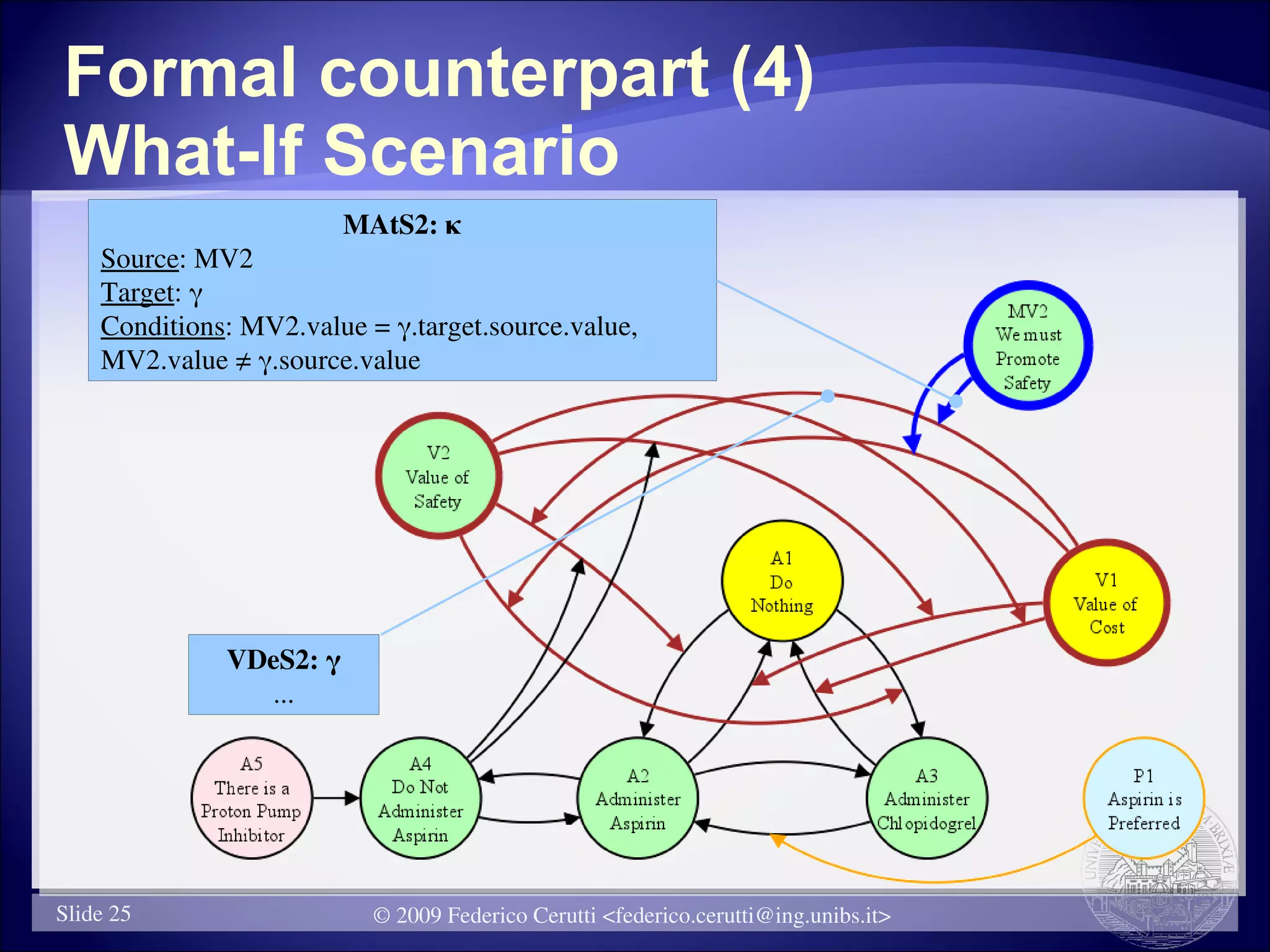
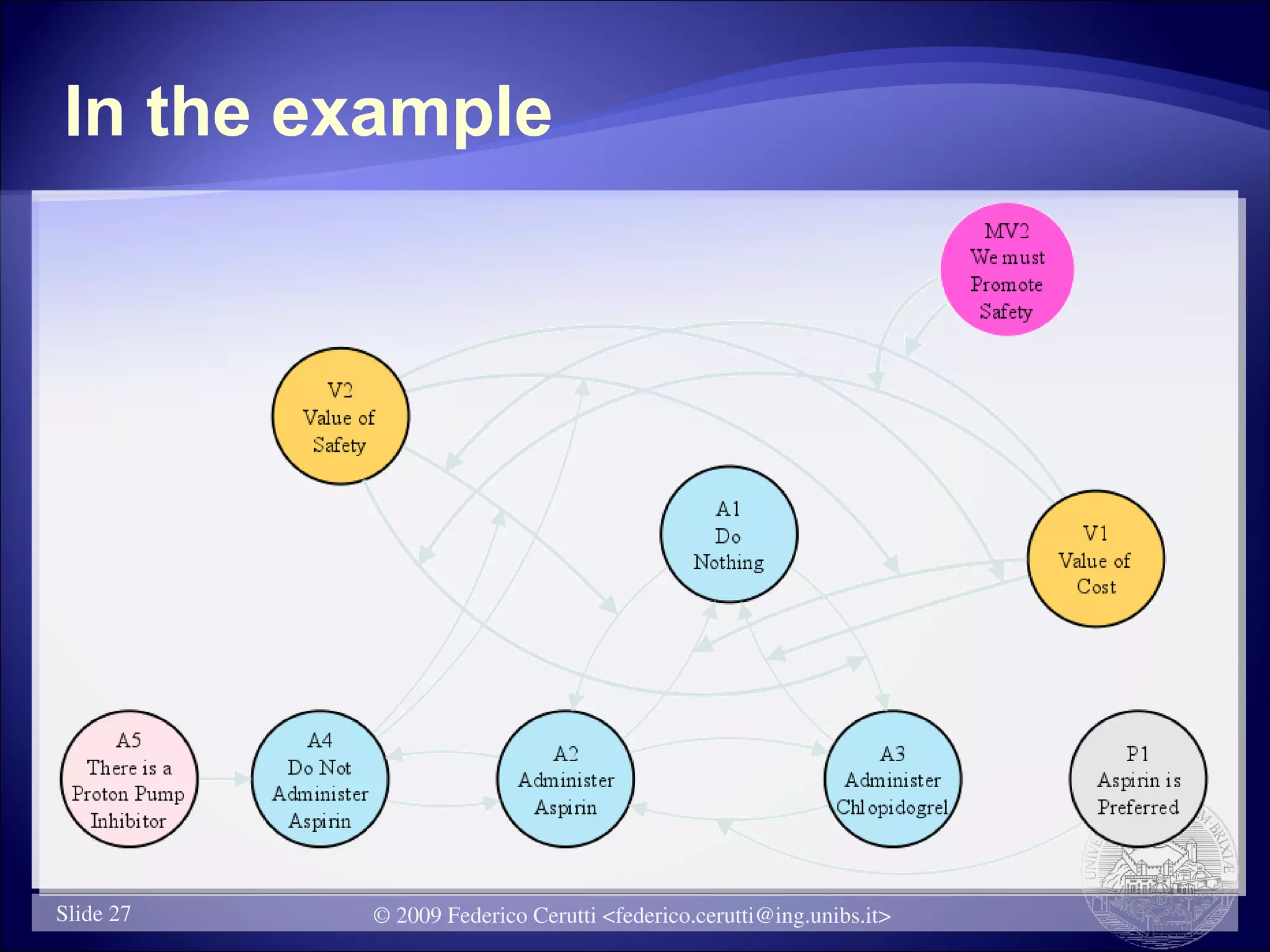
The document presents an argumentation-based approach to modeling decision support contexts with what-if capabilities. It introduces argument schemes to represent knowledge supporting or attacking conclusions. Practical, factual, value, preference, and must argument schemes are defined. Attacks between arguments are also modeled. The approach is demonstrated through an example of treatment options for a patient, where arguments, attacks, values, preferences and a must value are formally represented. The goal is to provide transparent decision support that allows discussion and exploration of details.
![The main concepts
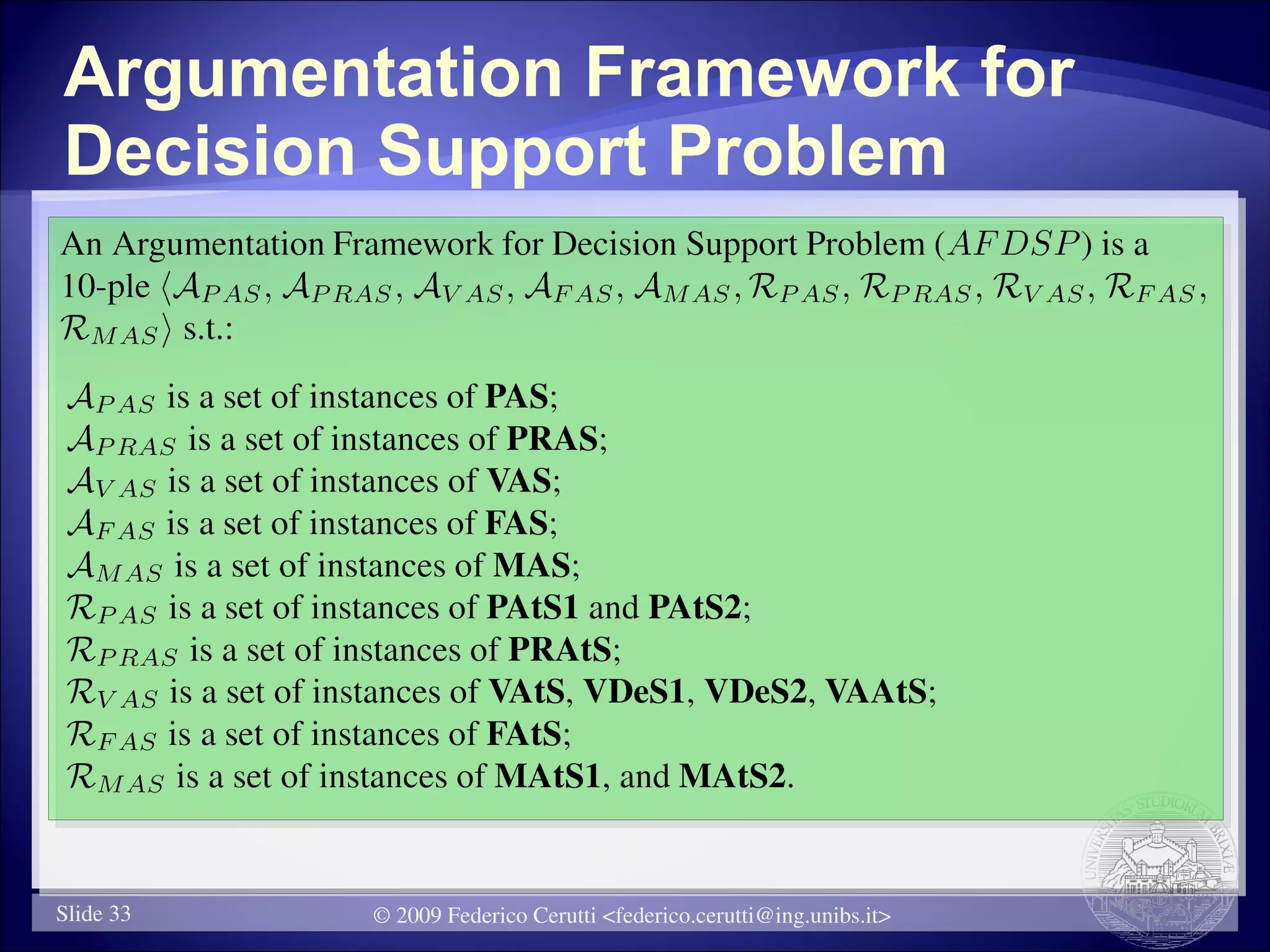
Circumstance: a state of the world
Fact: a particular circumstance assumed to be true
Goal: a state of the world we want to achieve
Action: support for the achievement of a goal
Preference: “[…] a greater liking for one alternative
over another or others […]”
Value: “Worth or worthiness […] in respect of rank
or personal qualities”
Must Value: a value that we commit to promote
© 2009 Federico Cerutti <federico.cerutti@ing.unibs.it>](https://image.slidesharecdn.com/ceruttiaaai09-12829138979833-phpapp02/75/Cerutti-AAAI-Fall-Symposia-2009-6-2048.jpg)

![Small Summary
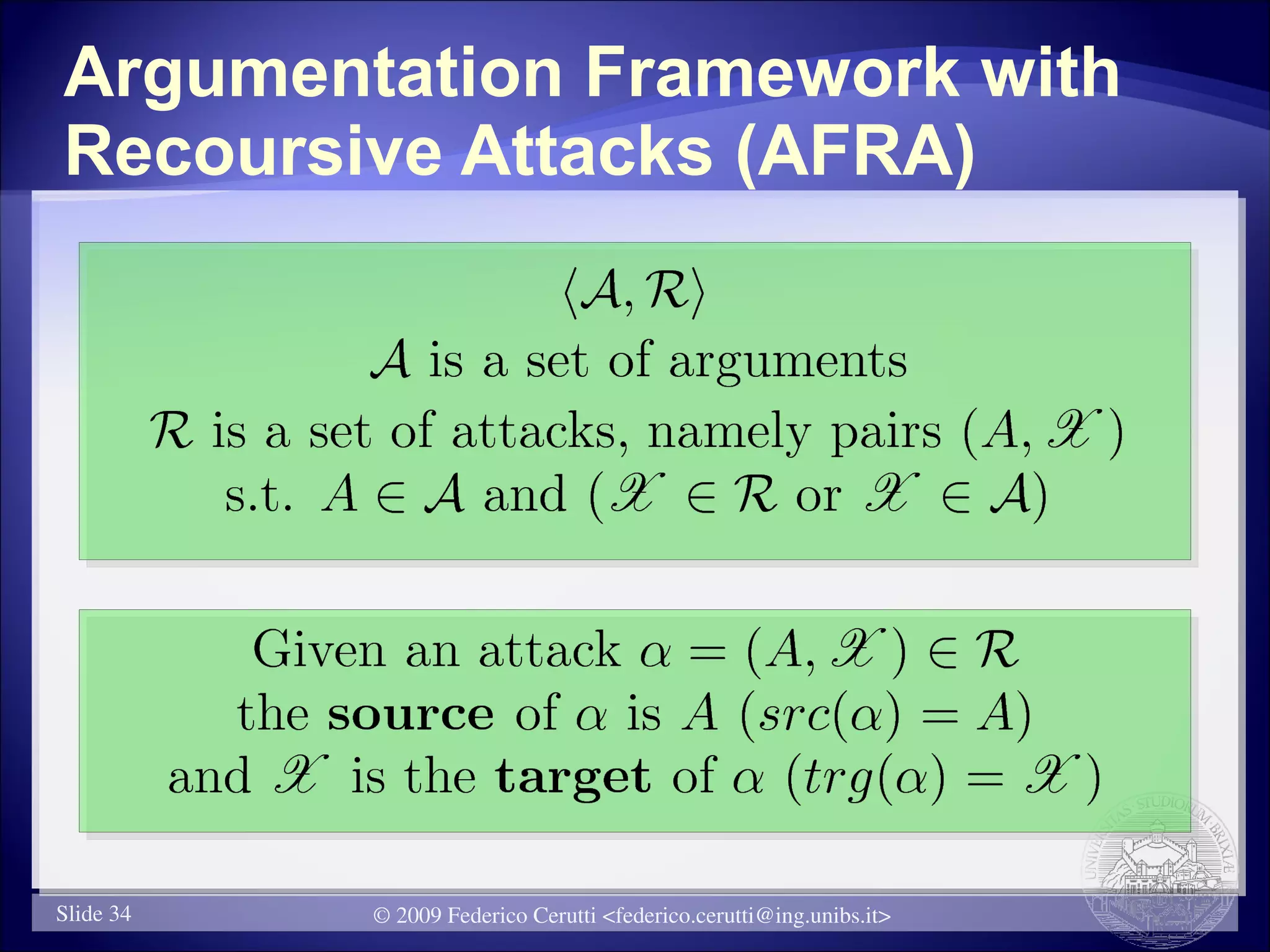
Attack Scheme Taxonomy (1)
PAtS1: incompatible actions
PAtS2: “rebuttal”
VAtS : incompatible values
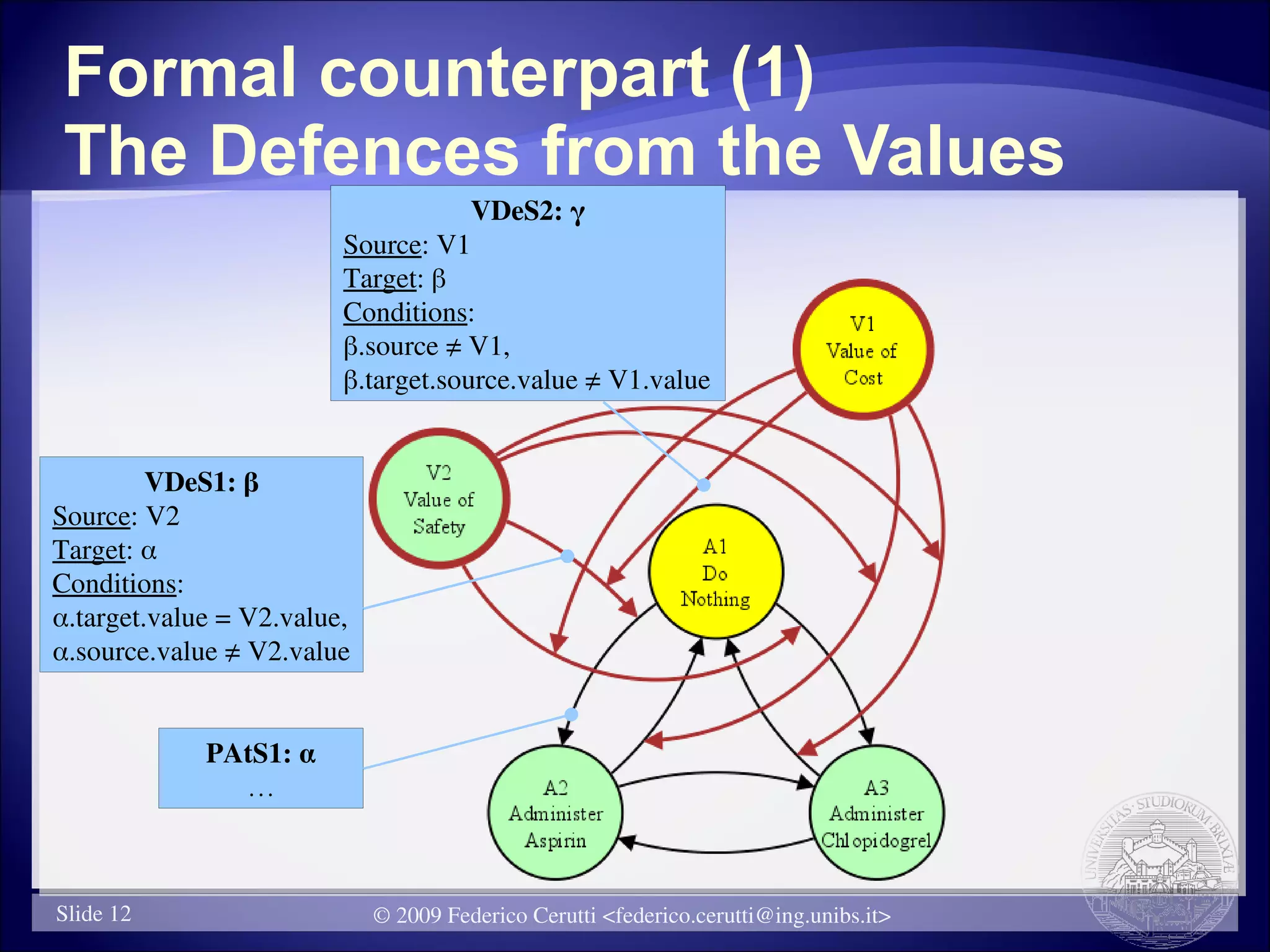
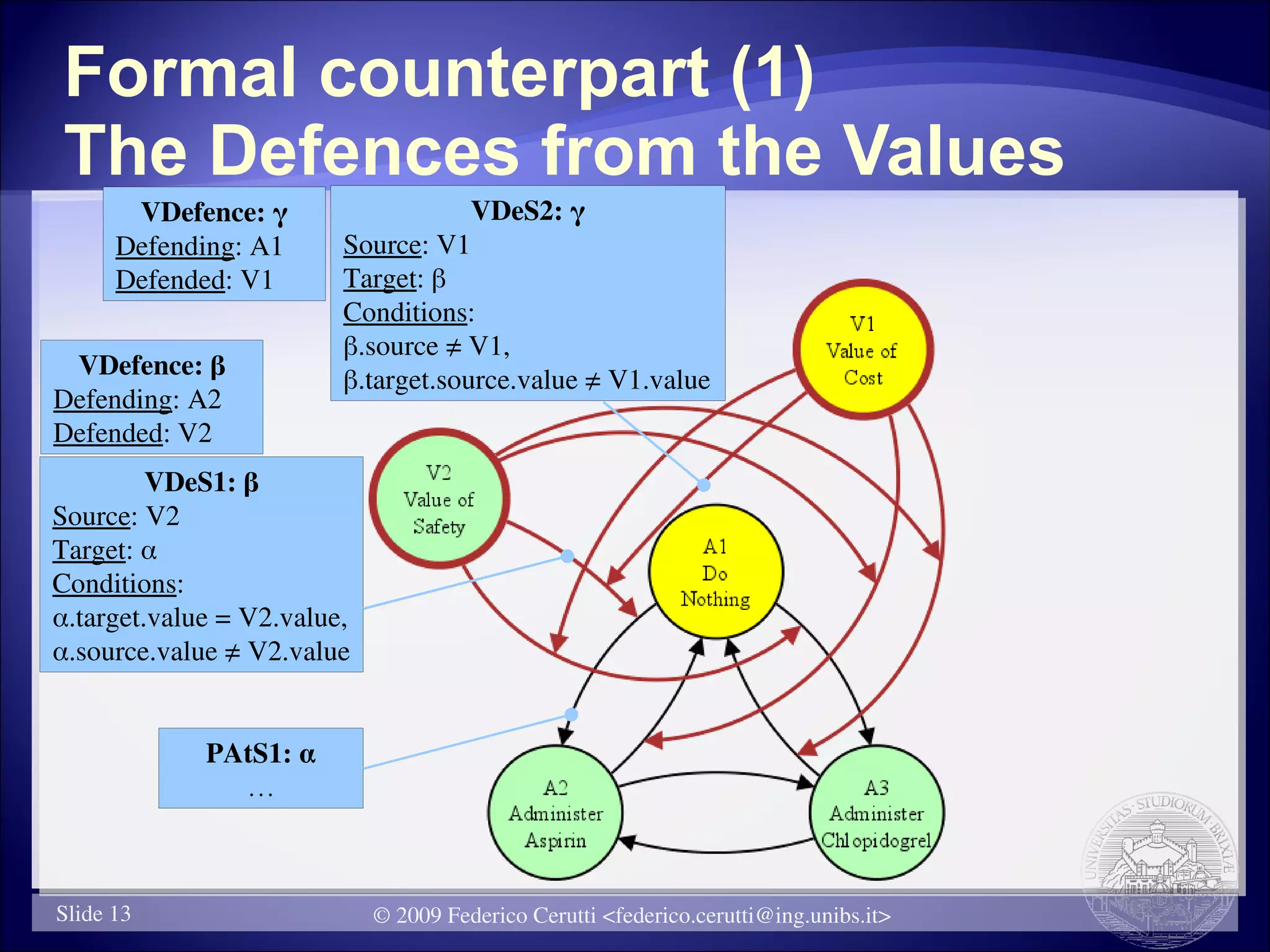
VDefence (VDeS[1-2]): a value protects both the
arguments which promote it and the attacks sourced
from that arguments
VAAtS: if a practical argument P suggests not to
perform an action A since it demotes a value V, if P
will be considered acceptable, then V cannot defend
the argument whose action is A
Slide 28 © 2009 Federico Cerutti <federico.cerutti@ing.unibs.it>](https://image.slidesharecdn.com/ceruttiaaai09-12829138979833-phpapp02/75/Cerutti-AAAI-Fall-Symposia-2009-28-2048.jpg)