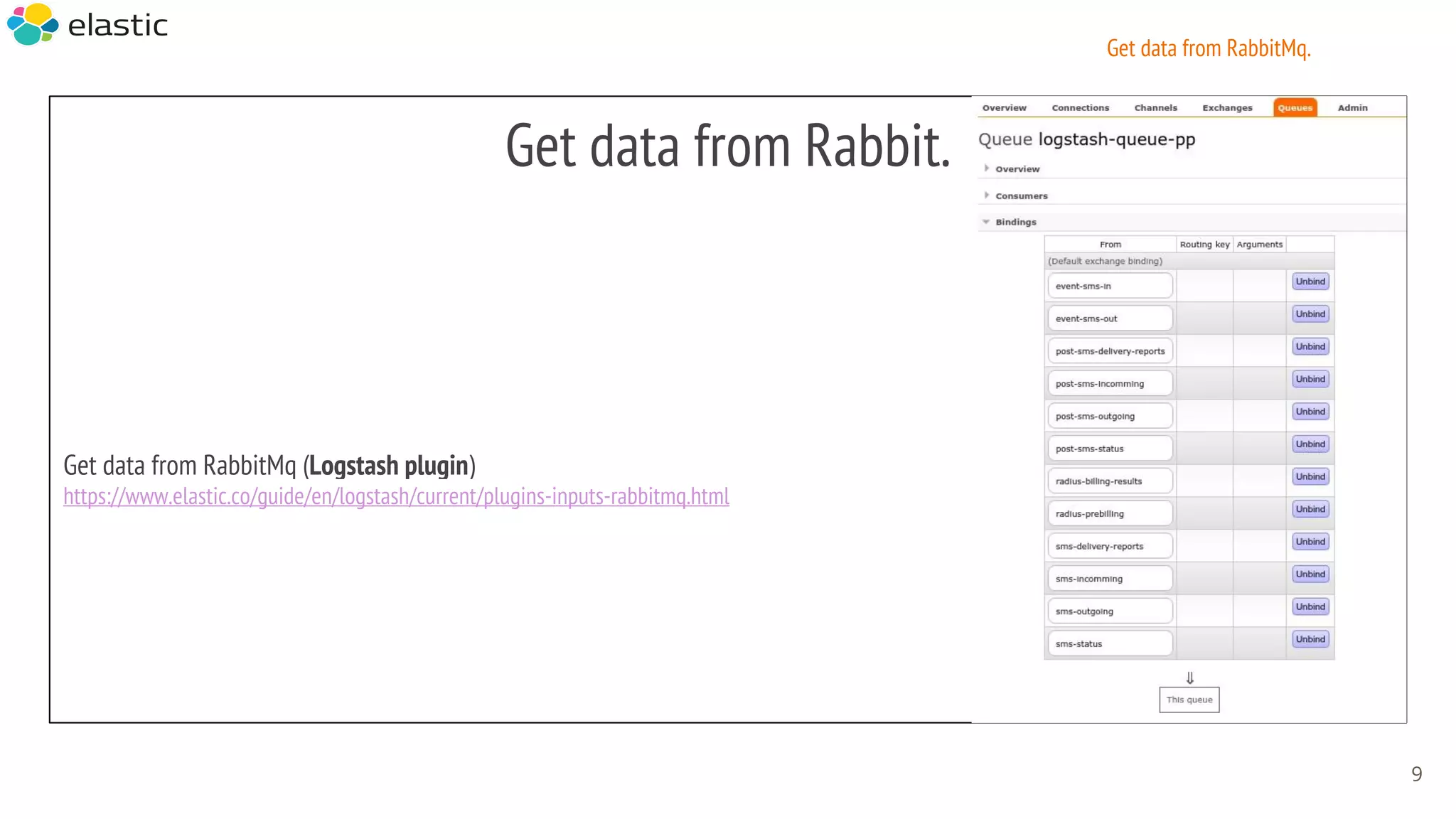
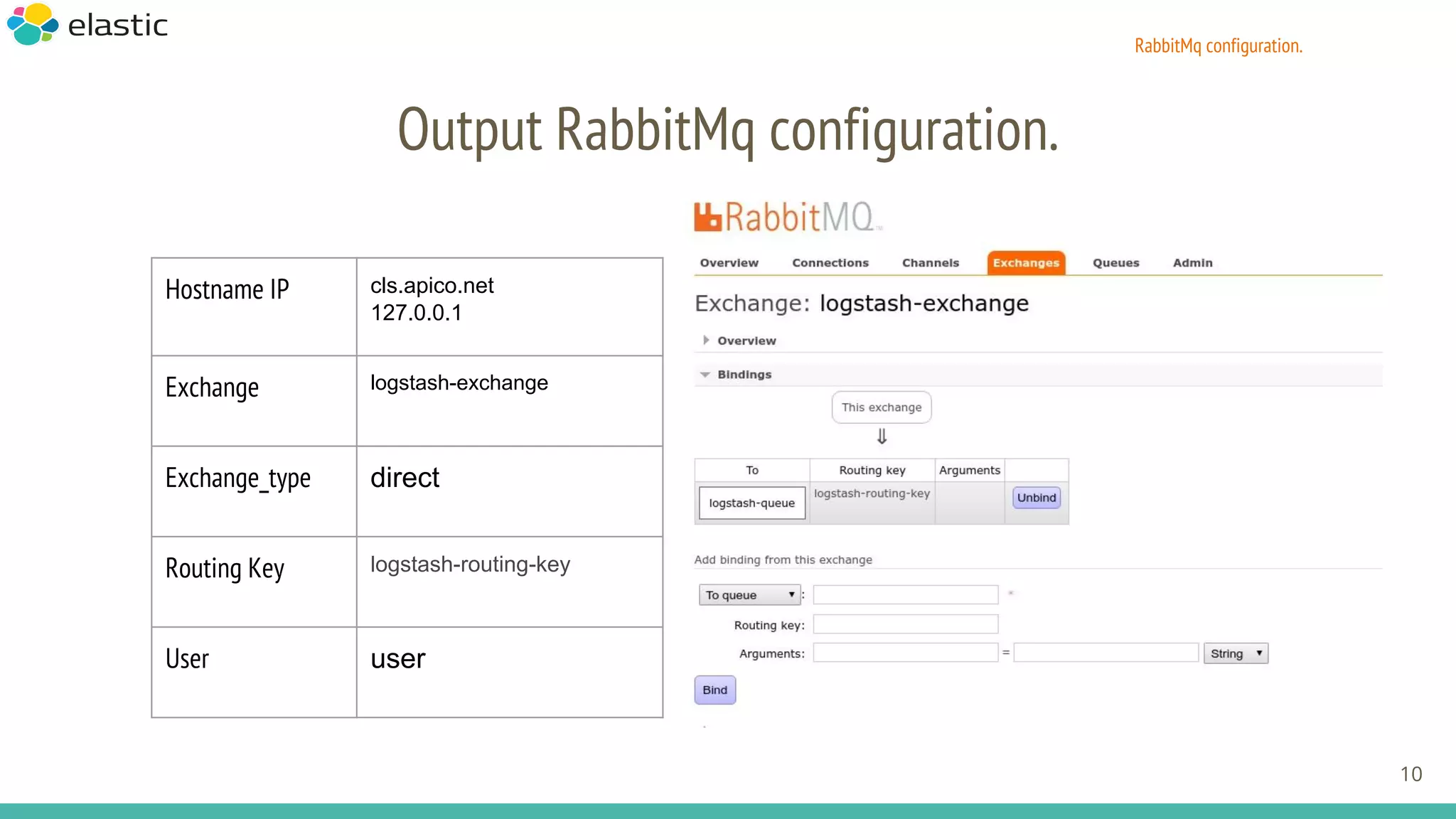
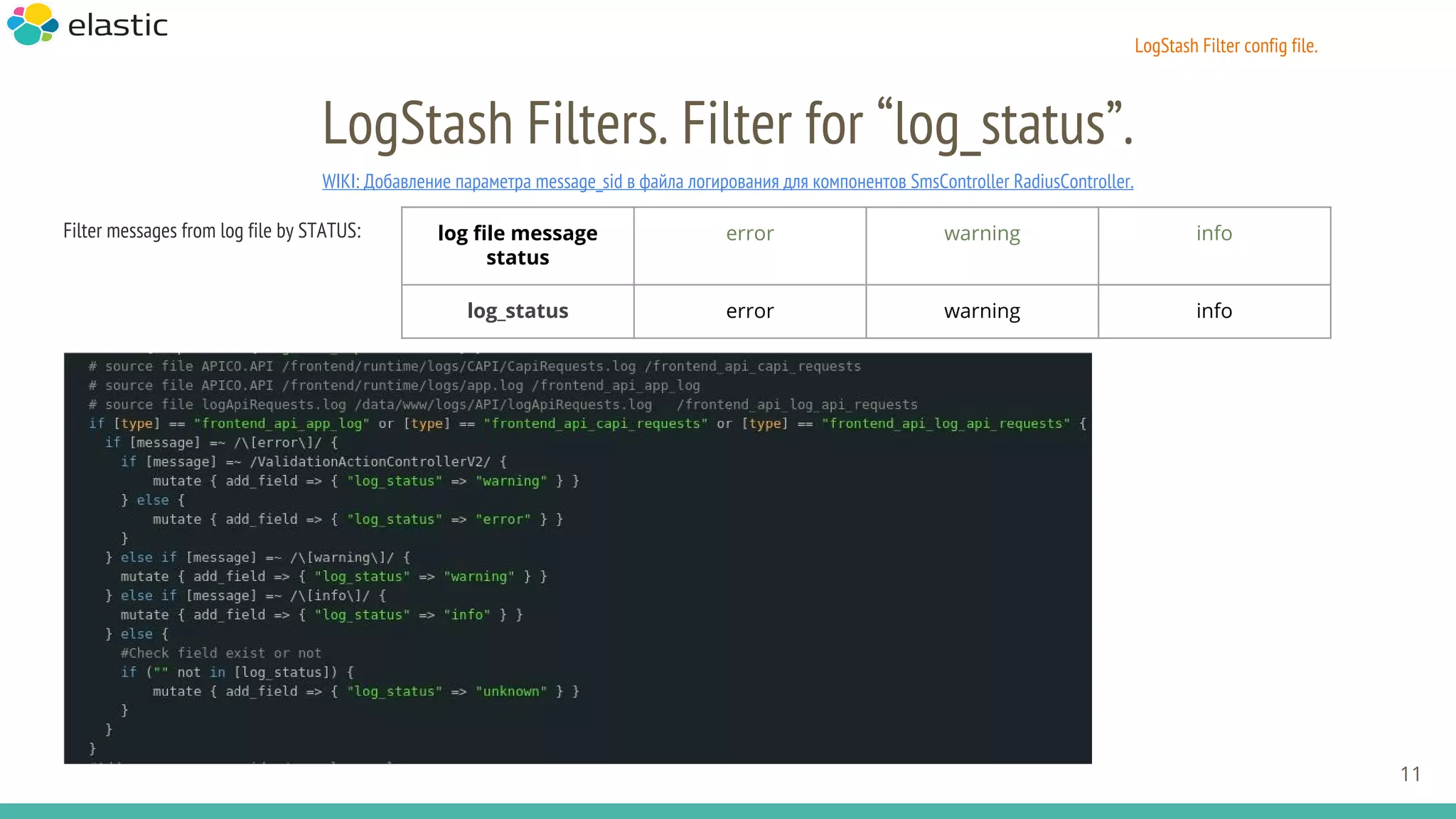
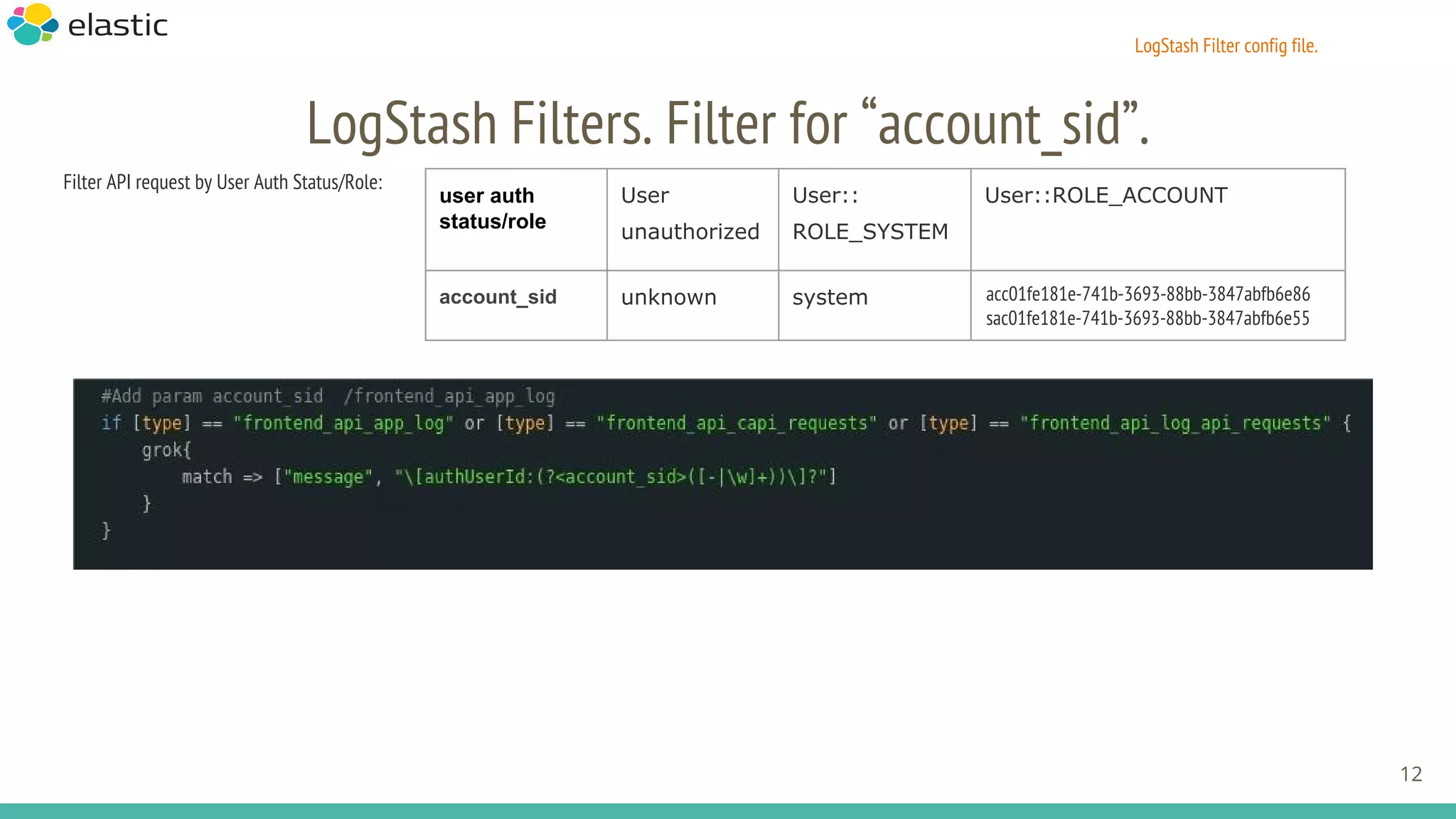
The document outlines the configuration and setup of a central log storage system using the ELK stack (Elasticsearch, Logstash, Kibana) along with Filebeat and RabbitMQ. It includes various configuration files, SSL settings, and troubleshooting steps for monitoring and managing log data. Additionally, it discusses Logstash filters for filtering log messages based on status and user authentication roles.

![FileBeat config file. YML standard
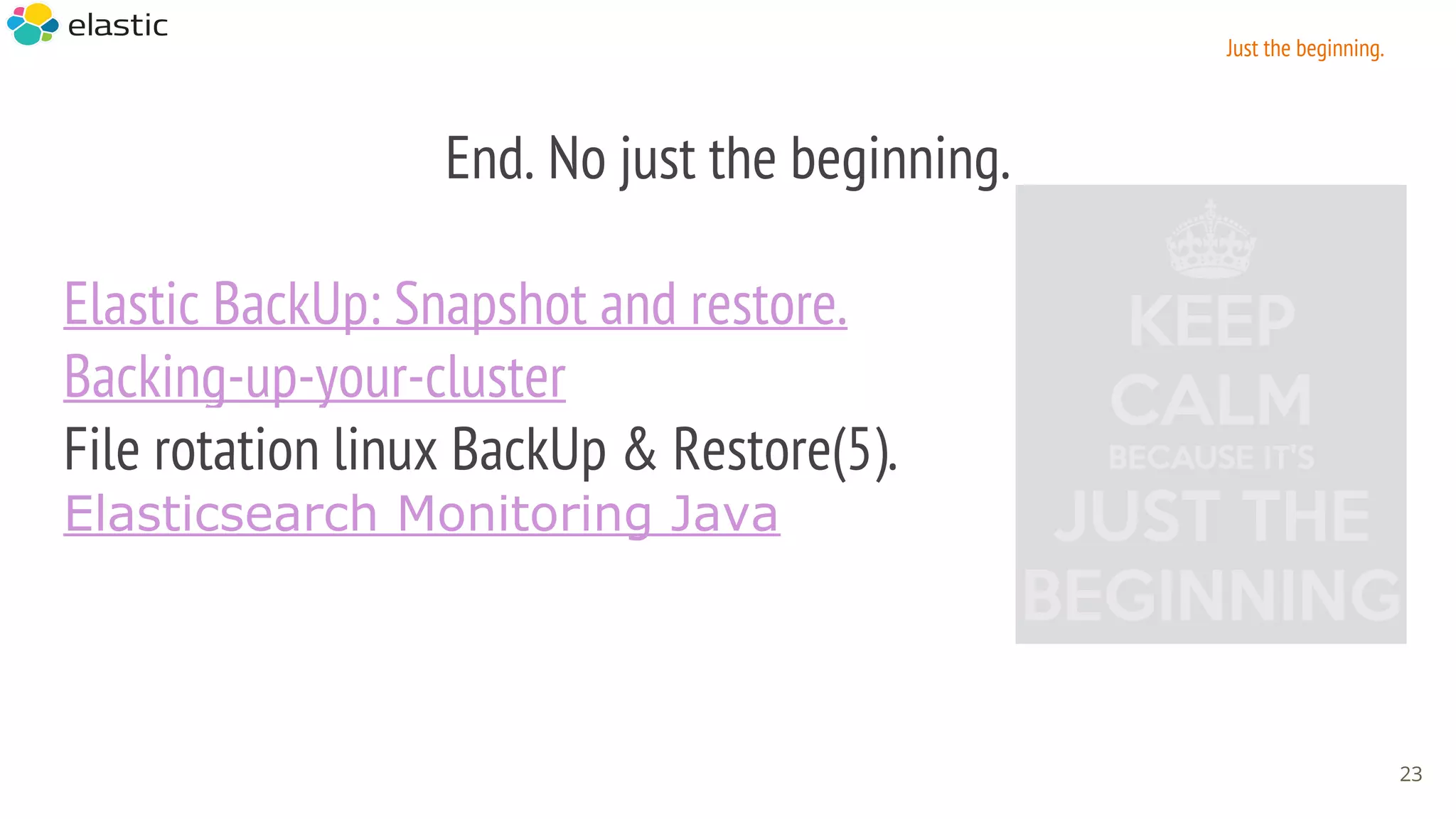
FileBeat config file. YML
4
vim /etc/filebeat/filebeat.yml
-
paths:
- ${API_APP_LOG_PATH}/file.log
encoding: plain
input_type: log
fields:
level: apico_backend
review: 1
fields_under_root: false
ignore_older: 0
document_type: api_backend_requests
scan_frequency: 2s
multiline:
pattern: ^[[:digit:]]{4}
negate: true
match: after
max_lines: 500
timeout: 2s
tail_files: false
### Logstash as output
logstash:
# The Logstash hosts
hosts: ["cls.apico.net:9999"]
# Number of workers per Logstash host.
worker: 2
# Optional TLS. By default is off.
tls: certificate_authorities:["/etc/ssl/certs/rootCA.crt"]
insecure: false](https://image.slidesharecdn.com/centrallogstorage-160430164049/75/Central-LogFile-Storage-ELK-stack-Elasticsearch-Logstash-and-Kibana-4-2048.jpg)

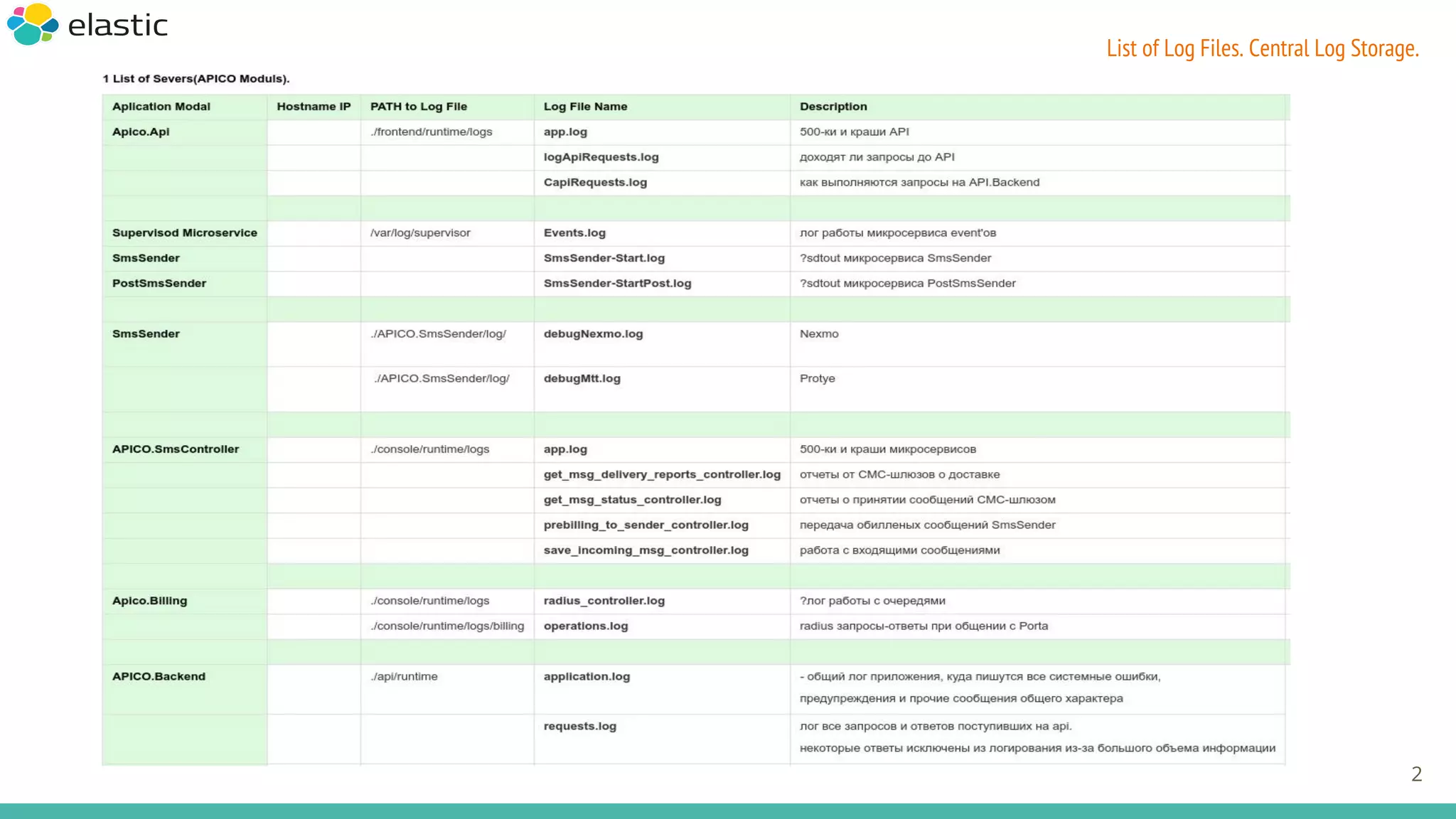
![SSL Certificate Authority
Certificate Authority — в 5 OpenSSL команд
https://habrahabr.ru/post/192446/
Using TLS between Beats and Logstash
https://gist.github.com/andrewkroh/fdc7e5f3f0f0ed63a11c
Validate crt key:
[root@MSG-predprod lostash_pp]# pwd
/etc/ssl/certs/lostash_pp
[root@MSG-predprod lostash_pp]# curl -v --cacert rootCA.crt https://cls.apico.net:9999
* Rebuilt URL to: https://cls.apico.net:9999/
* Connected to cls.apico.net (172.31.13.49) port 9999 (#0)
* CAfile: rootCA.crt
* Server certificate:
* subject: E=kh.airat14@gmail.com,CN=cls.apico.net,OU=ITY,O=Default Company Ltd,L=Moscow,ST=Moscow,C=MT
* start date: Apr 19 11:59:50 2016 GMT
* expire date: Sep 05 11:59:50 2043 GMT
* common name: cls.apico.net
> GET / HTTP/1.1
> Host: cls.apico.net:9999
> Accept: */*
* Empty reply from server
[root@MSG-predprod lostash_pp]#
6
Security:SSL Certificate AUthority.](https://image.slidesharecdn.com/centrallogstorage-160430164049/75/Central-LogFile-Storage-ELK-stack-Elasticsearch-Logstash-and-Kibana-6-2048.jpg)

![LogStash Filter config file.
LogStash Filters. Filter for “message_sid”.
Filter SmsController RadiusController
SmsSender by message_sid:
13
Source Consoler_app: [MessageSid:msgXXX] SmsSender_app:"message_sid":"msgXXX"
message_sid msgXXX msgXXX](https://image.slidesharecdn.com/centrallogstorage-160430164049/75/Central-LogFile-Storage-ELK-stack-Elasticsearch-Logstash-and-Kibana-13-2048.jpg)
![LogStash Filter config file.
LogStash Filters. Filter for “message_sid”.
Filter SmsController RadiusController
SmsSender by message_sid:
14
Source Consoler_app: [MessageSid:msgXXX] SmsSender_app:"message_sid":"msgXXX"
message_sid msgXXX msgXXX](https://image.slidesharecdn.com/centrallogstorage-160430164049/75/Central-LogFile-Storage-ELK-stack-Elasticsearch-Logstash-and-Kibana-14-2048.jpg)