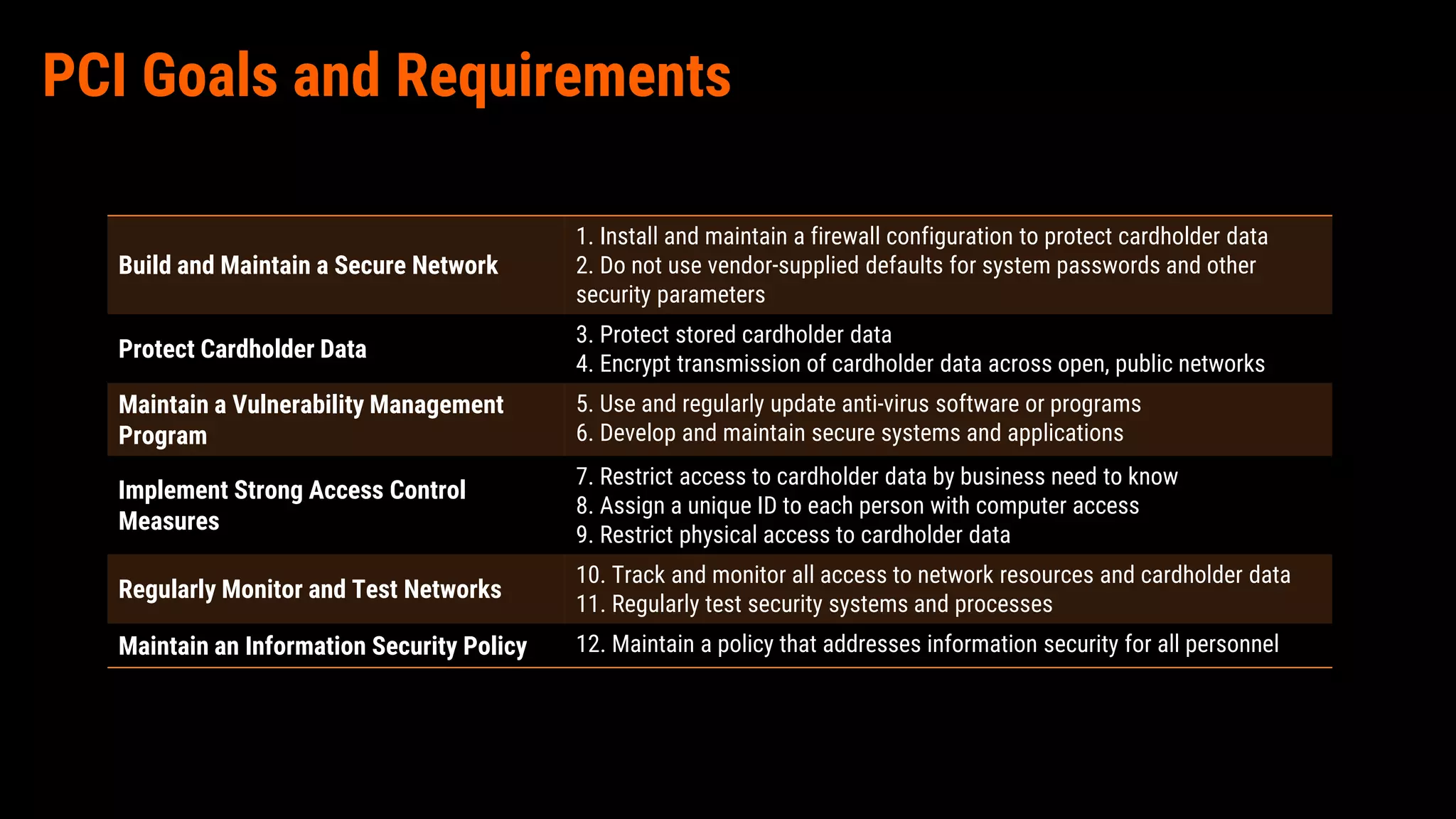
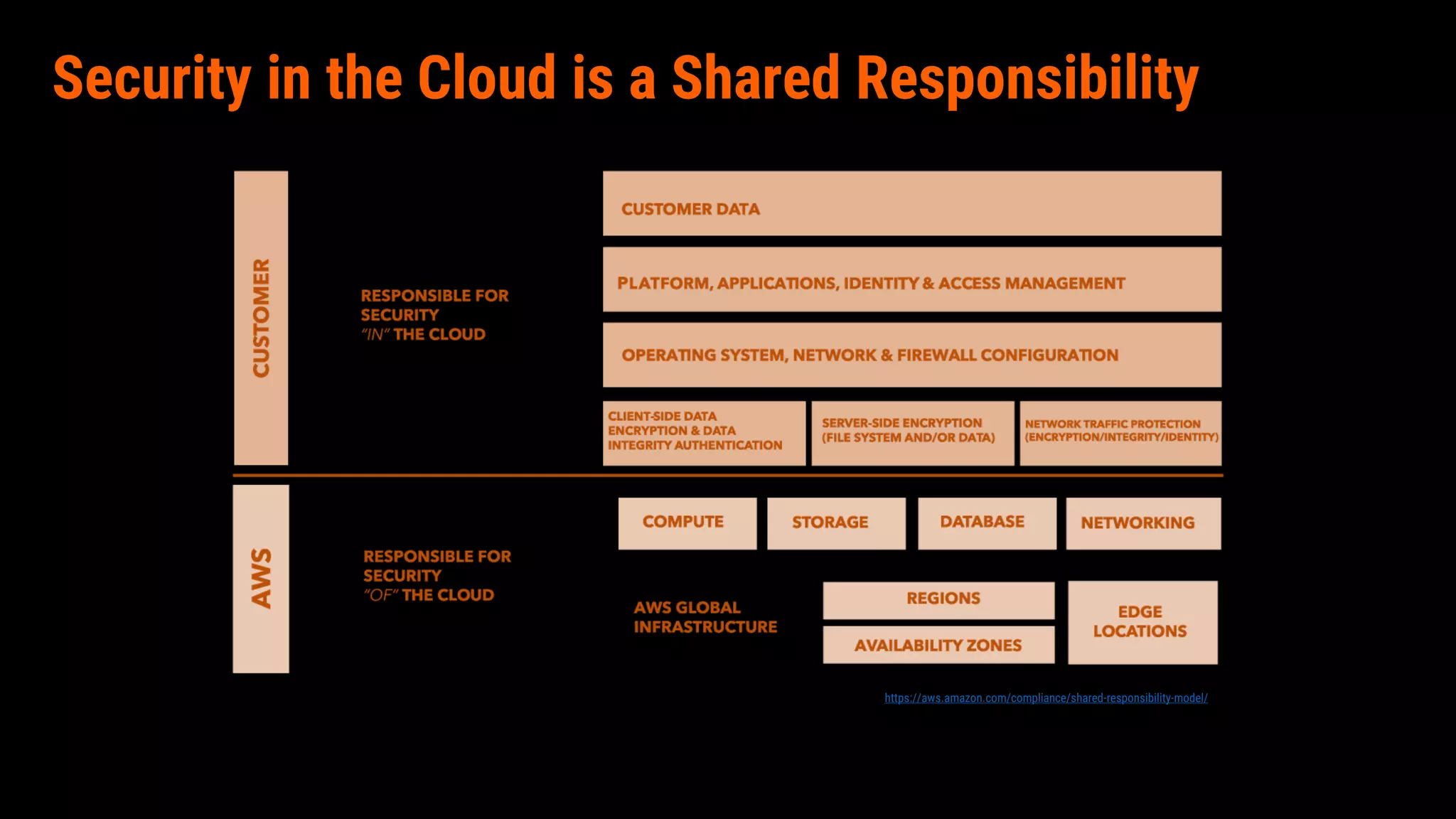
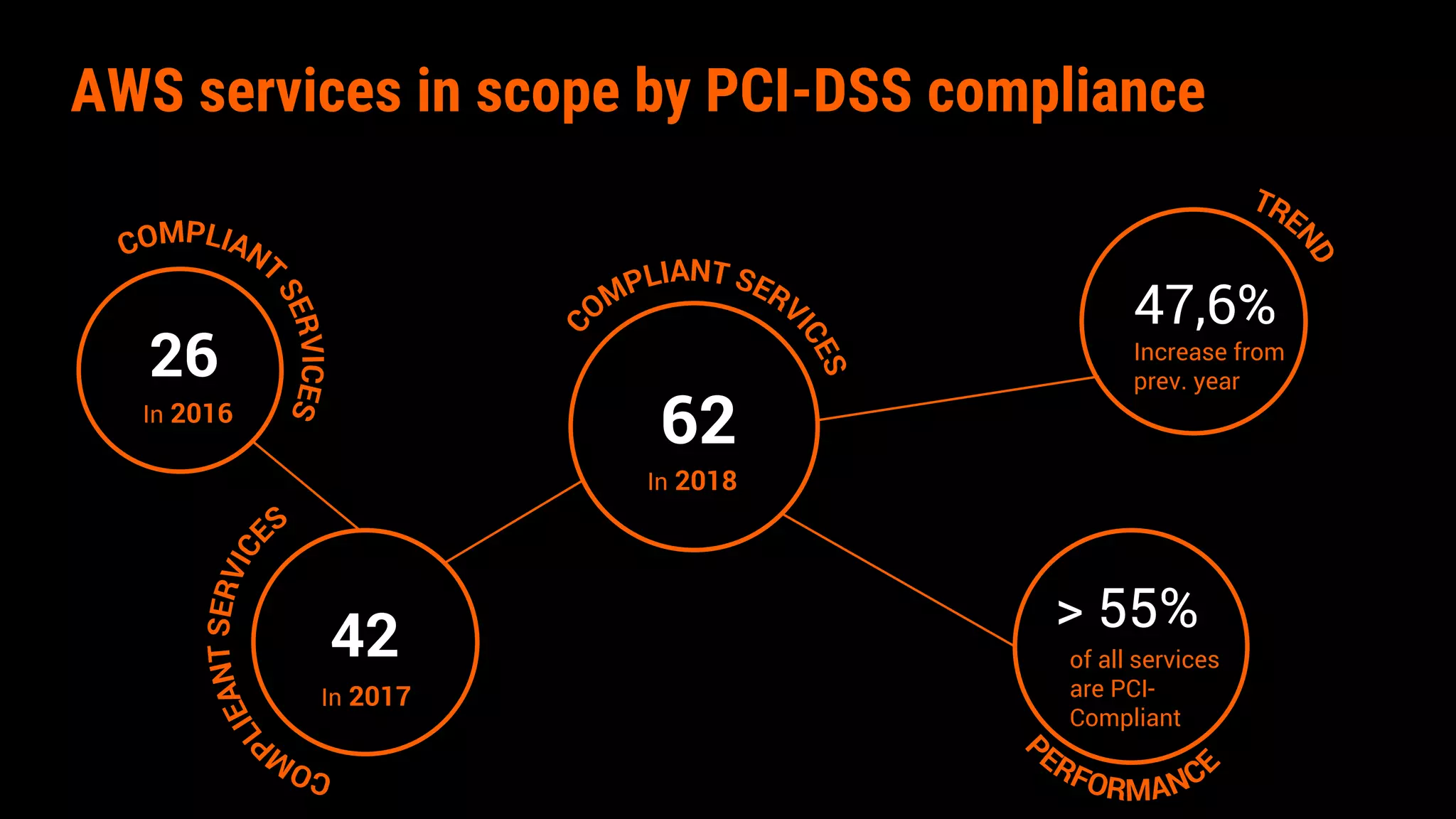
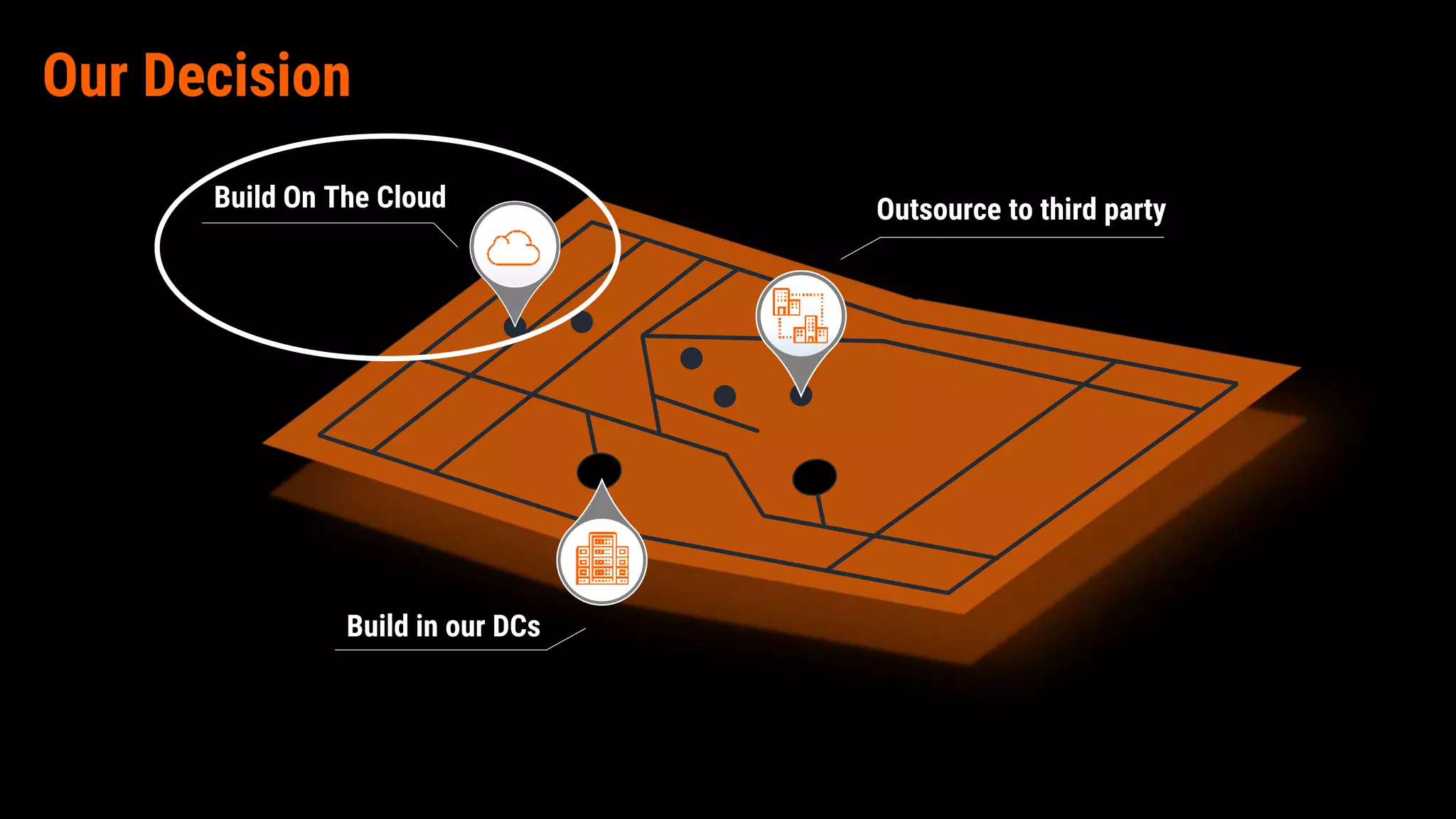
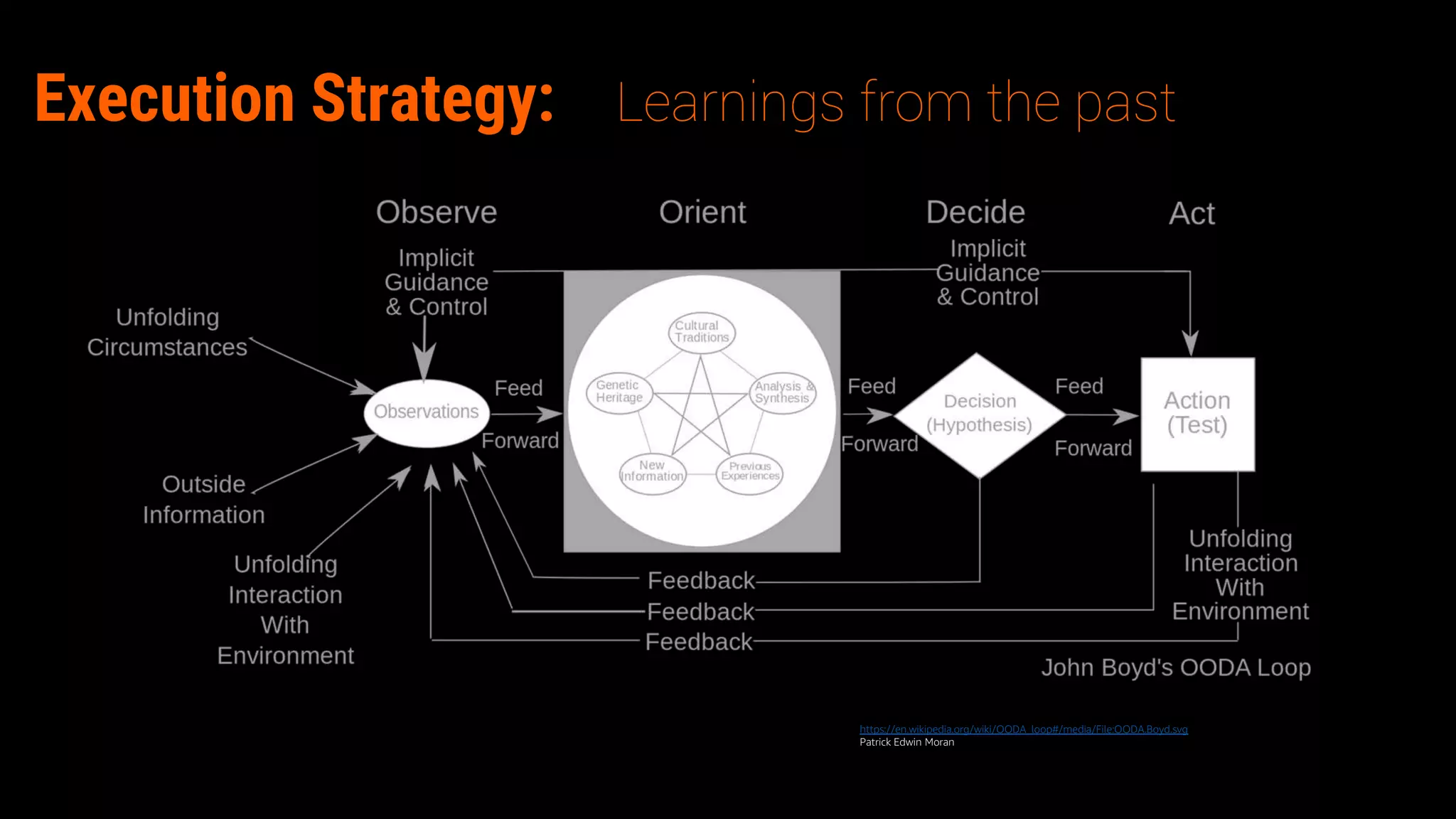
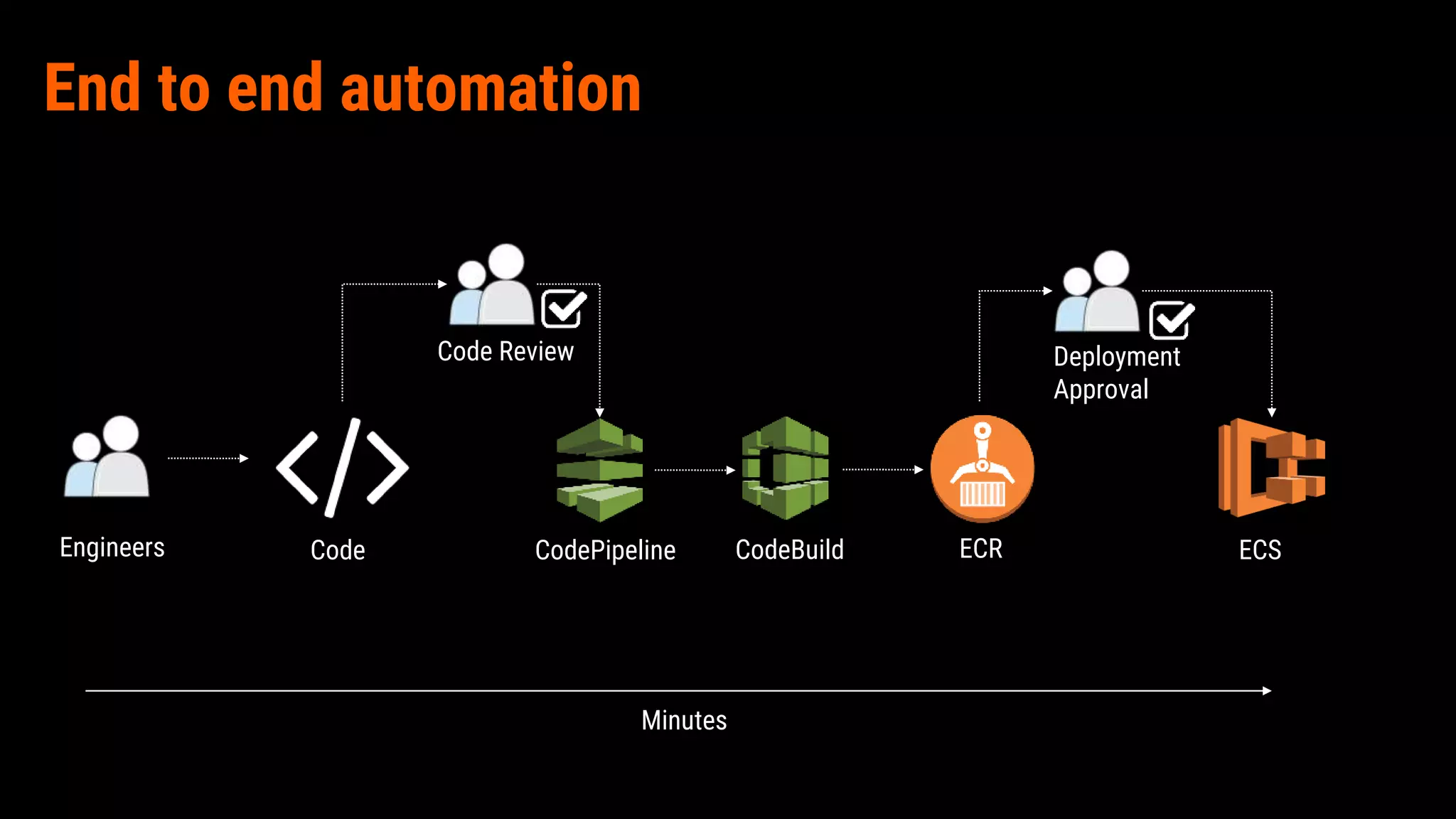
The document outlines the implementation of a highly secure and compliant omnichannel payment platform on AWS, achieved through strategic decision-making and adherence to PCI-DSS standards. Key learnings emphasize the importance of collaboration, continuous adaptation, incremental project management, and team care. The successful integration enhances security through various AWS services while improving compliance metrics significantly.