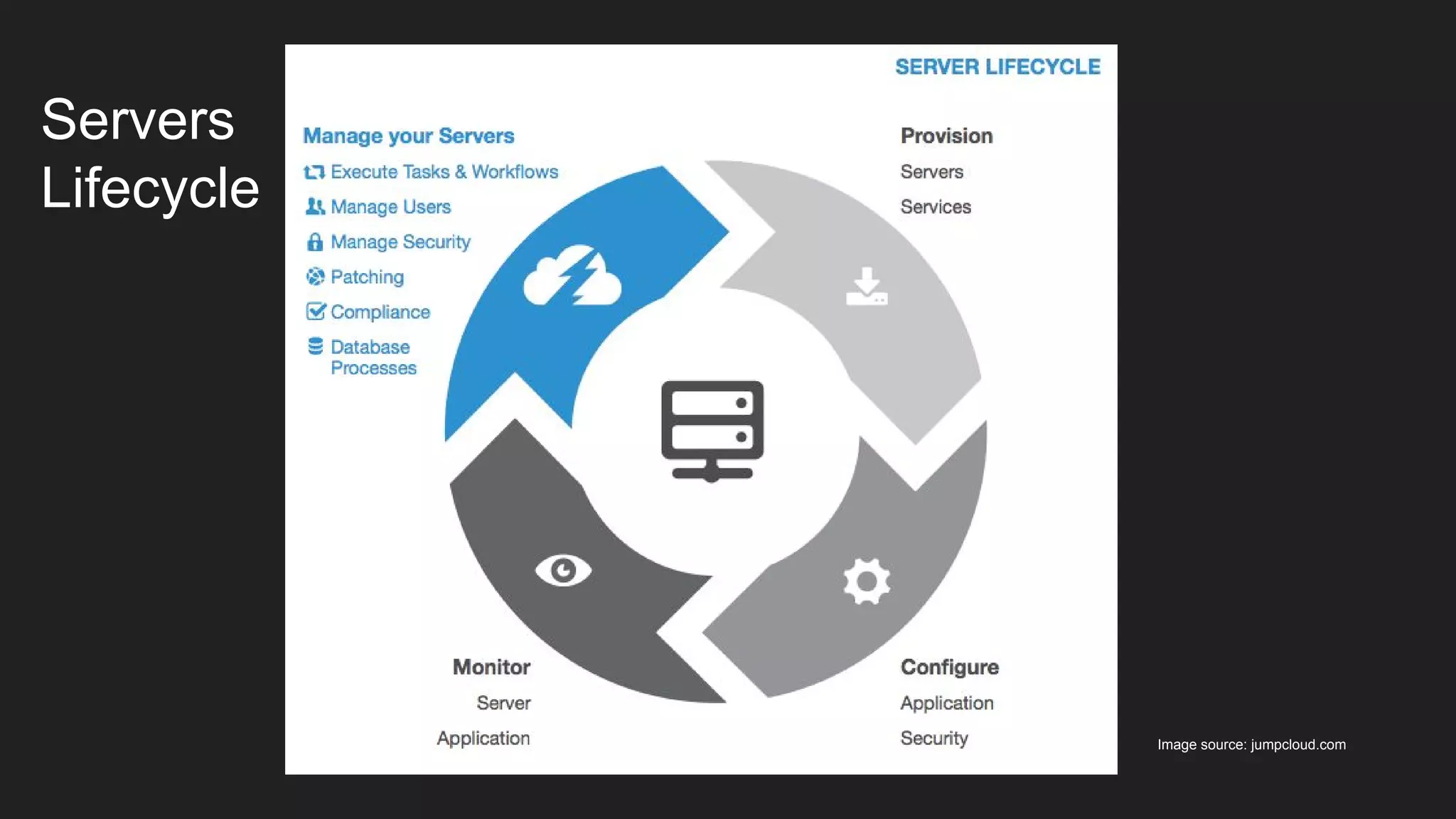
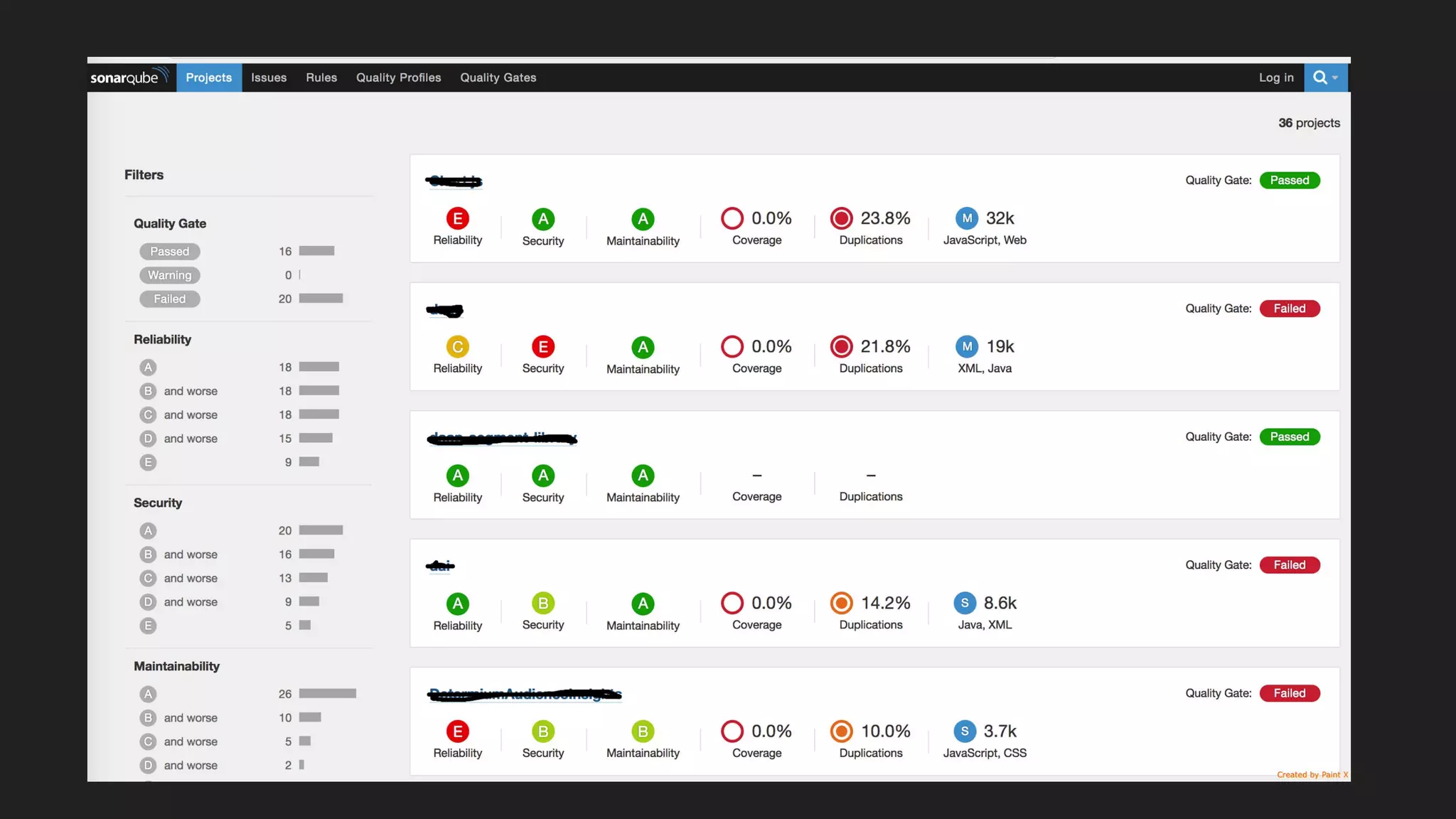
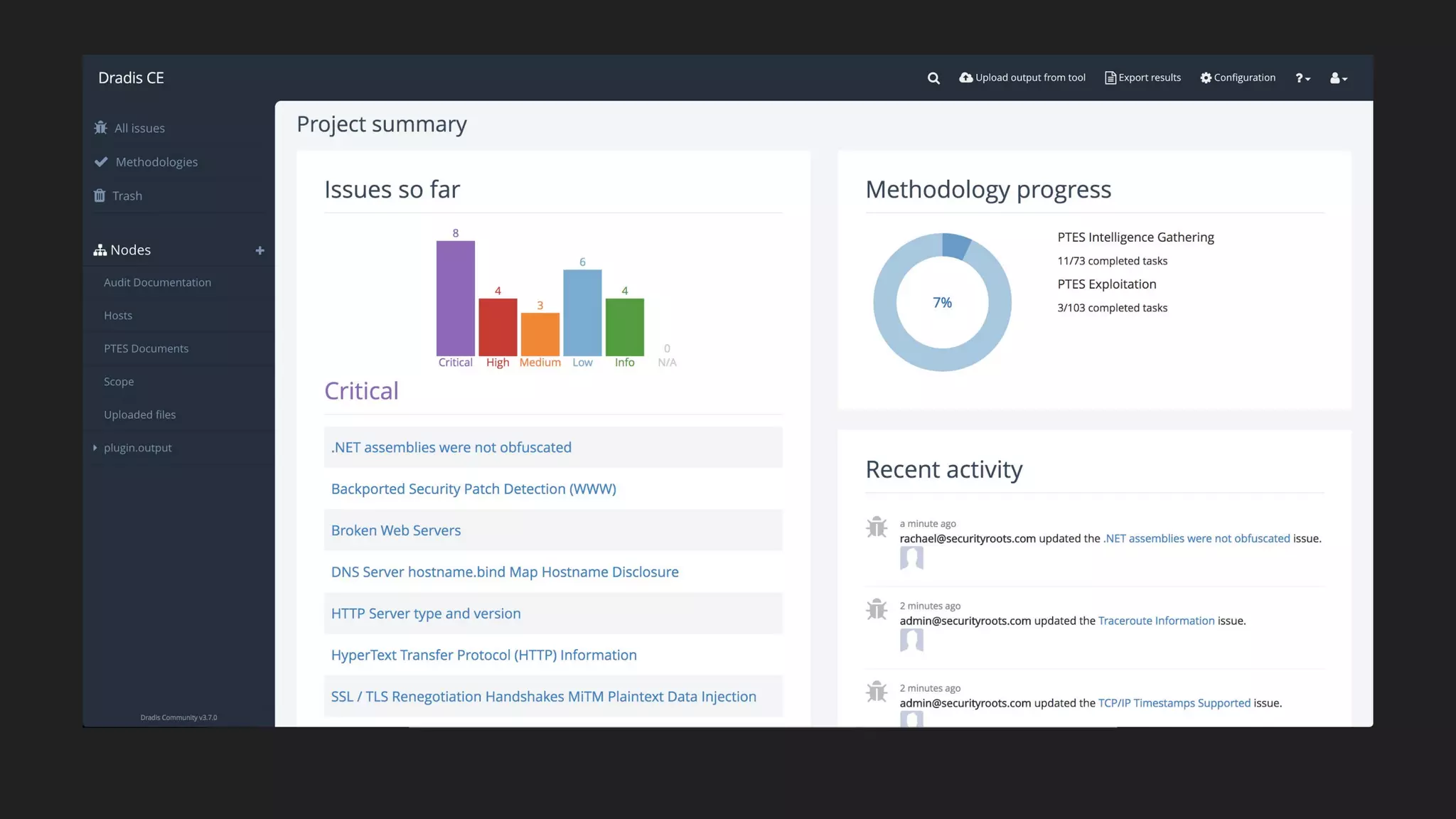
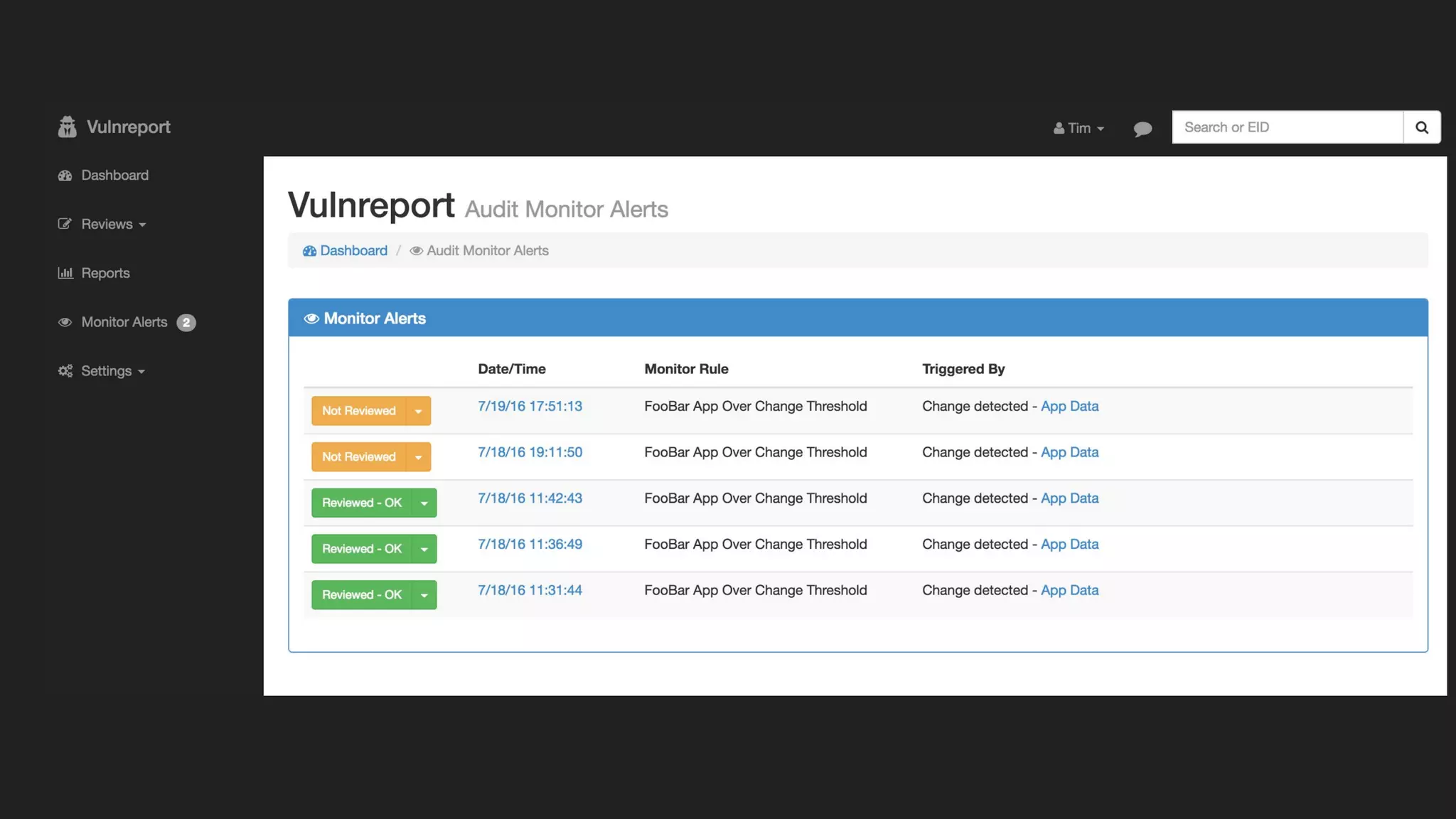
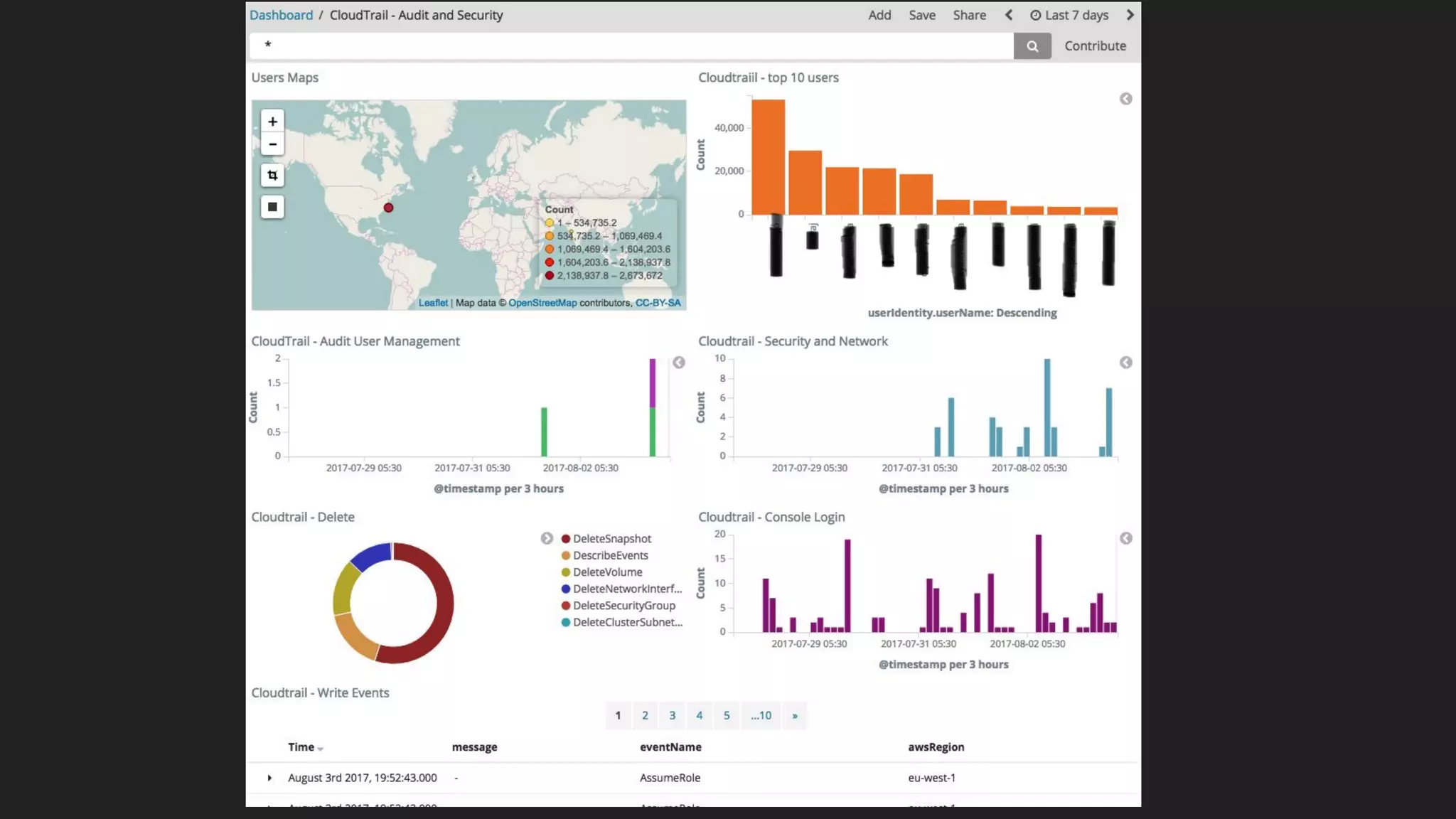
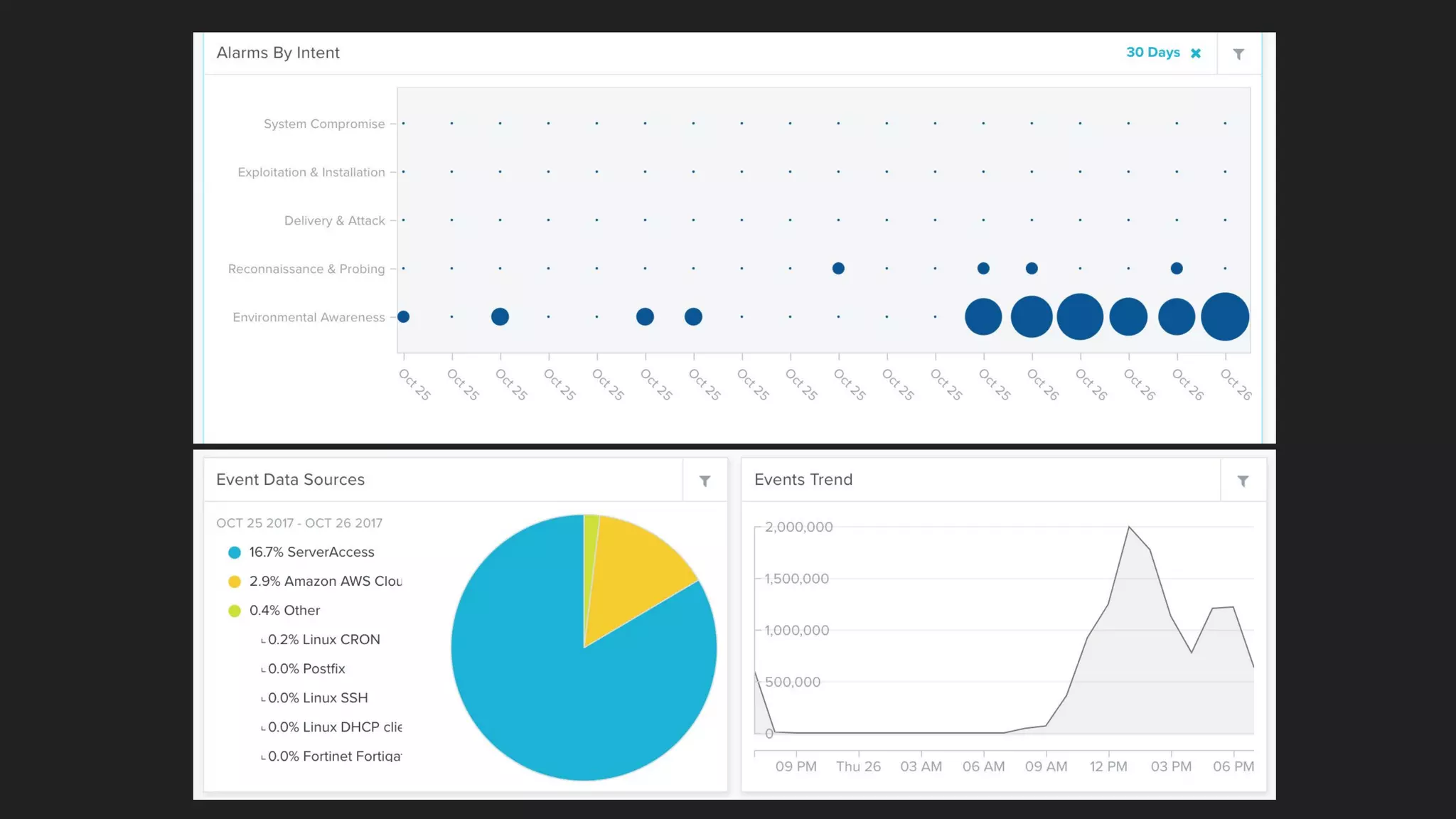
Suraj Pratap discusses security automation for red and blue teams. He outlines how he automates the server and application lifecycles using open source tools to address challenges around human capacity, tool selection, time, and cost when managing 600+ servers and 10+ applications across cloud infrastructures. Some areas he has automated include infrastructure security using Ansible and CloudFormation, security auditing using Scout2 and Prowler, offensive security tests using OpenVAS and Jenkins, vulnerability management with Dradis and Vulnreport.io, and security information and event monitoring with Alienvault and ELK.