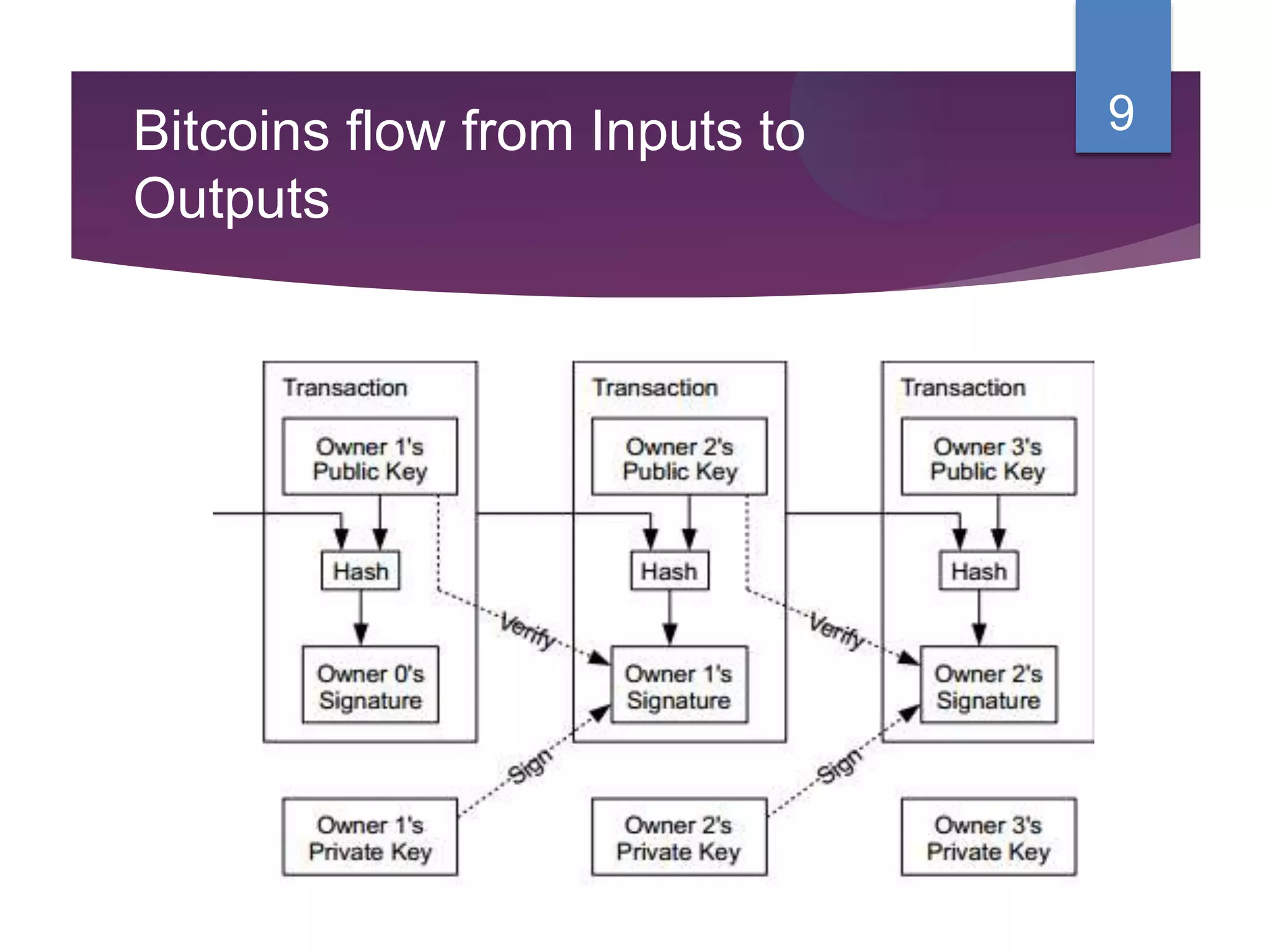
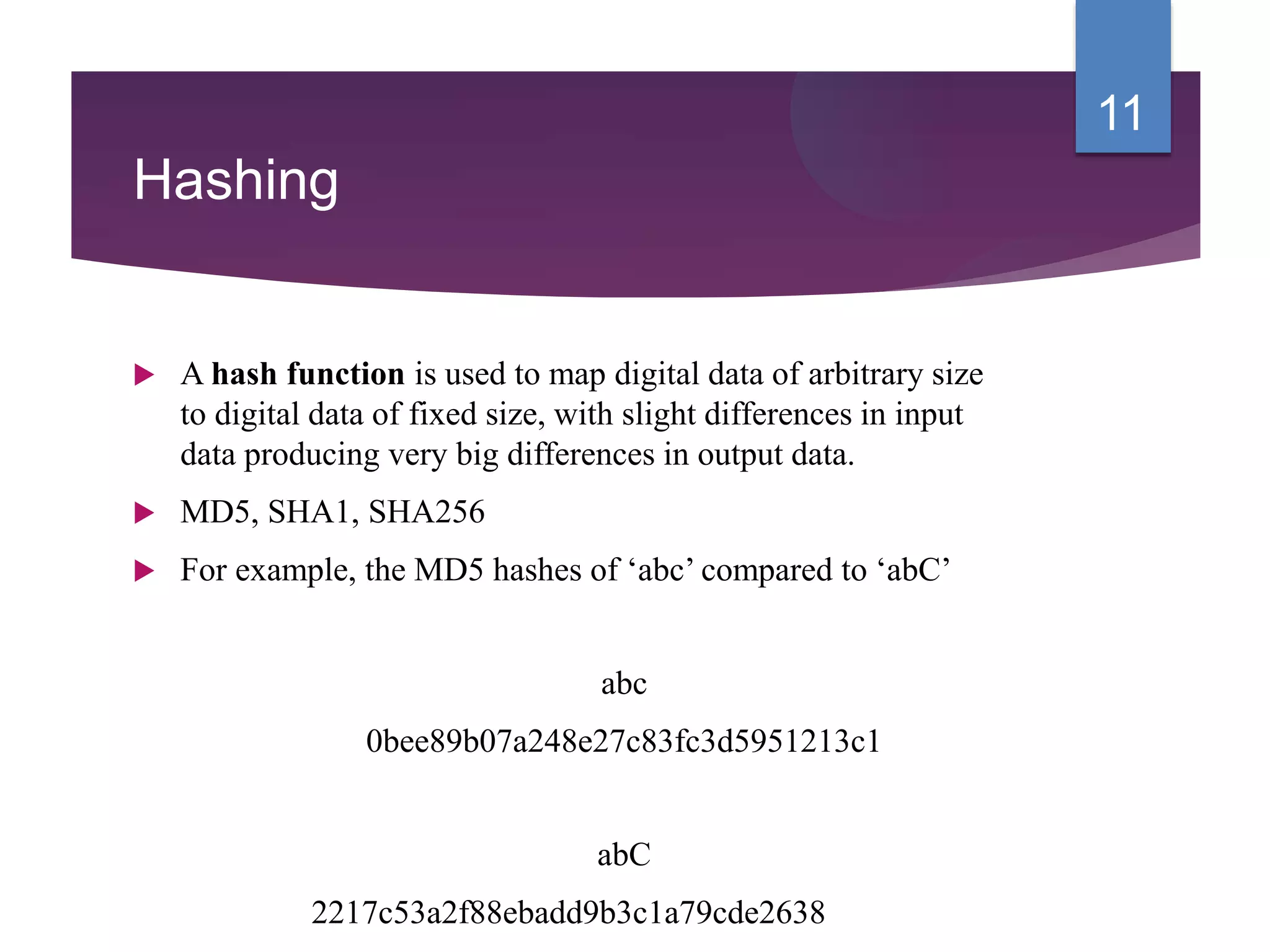
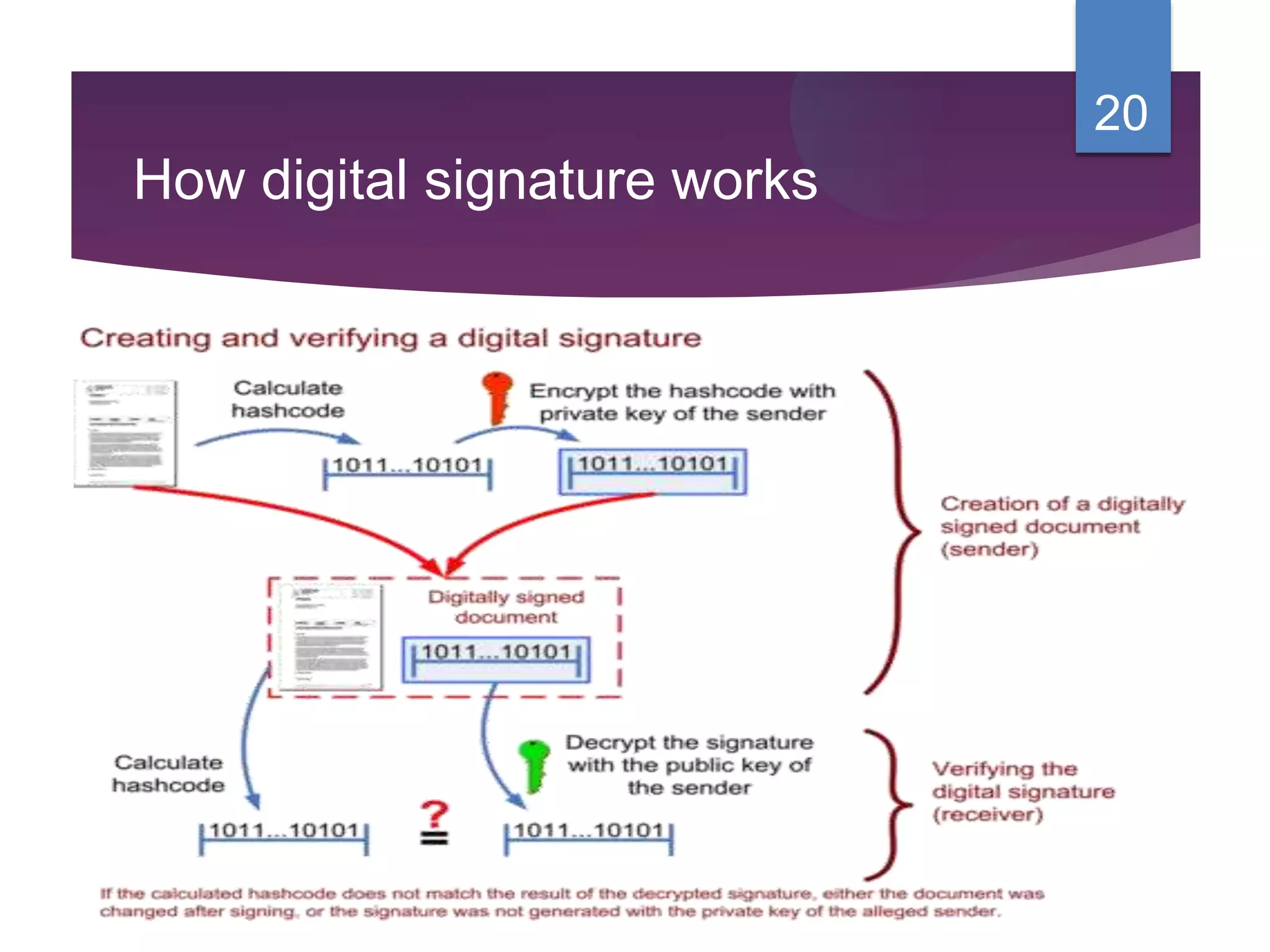
This document provides an overview of blockchain technology, bitcoin, hashing, and digital signatures. It defines blockchain as a growing list of transaction records linked using cryptography. Blockchains typically contain financial transactions that are replicated across peer-to-peer networks and use cryptography to prove identity and access rights. Bitcoin is described as a virtual currency where a record of coin ownership is kept instead of physical money. The document also summarizes hashing, proof of work, Hyperledger, and how digital signatures authenticate messages.