The document details the development of an 'automated home security system' as part of a B.Tech project in Information Technology by a group of students under the guidance of a professor at Amity University. The system aims to enhance home security by utilizing various sensors and technologies such as GSM, RFID, and PIR to detect fires, gas leaks, and unauthorized access. It includes a comprehensive requirement analysis, system design, coding, and implementation phases, along with a market survey and identification of advantages and limitations of the project.
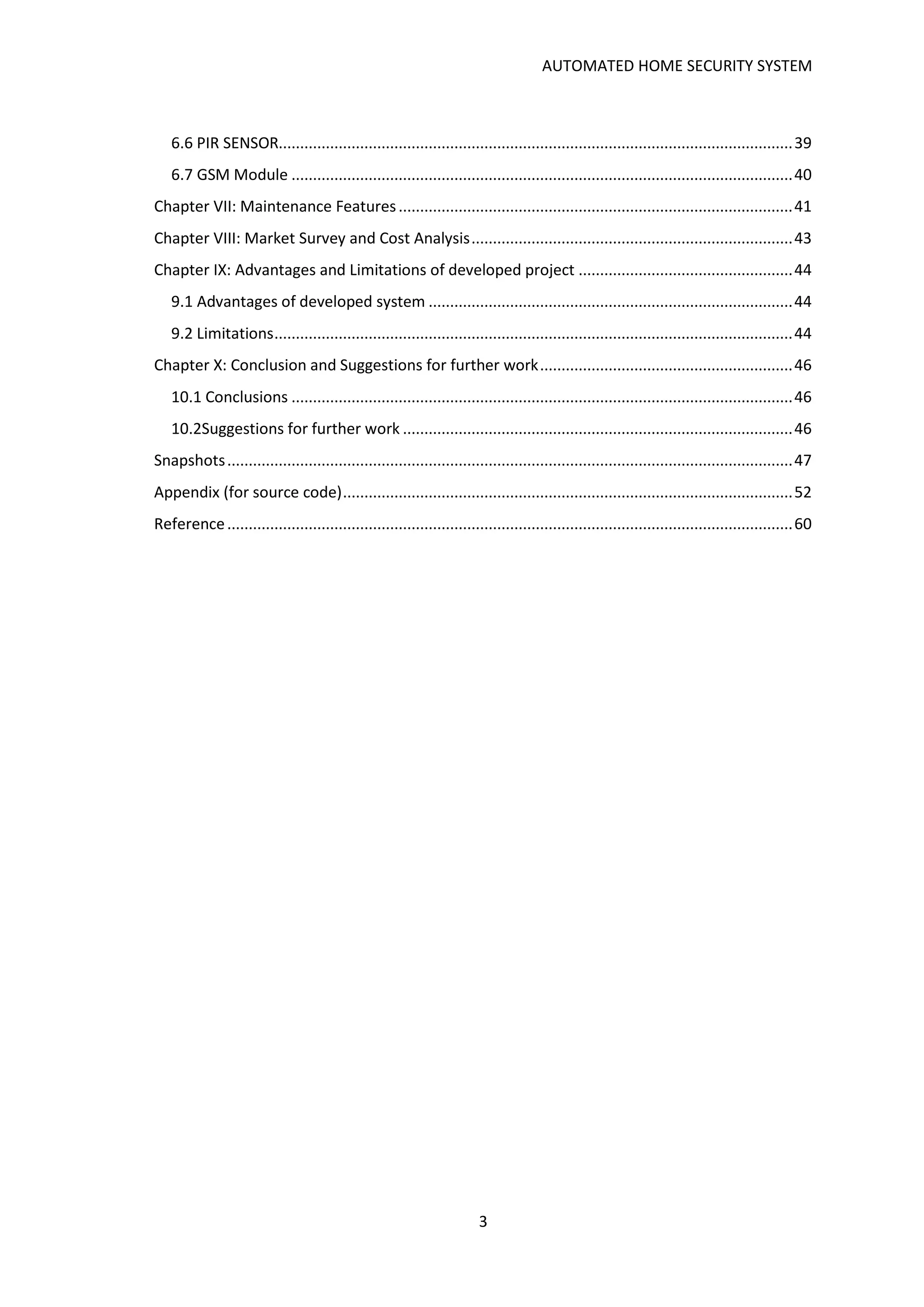

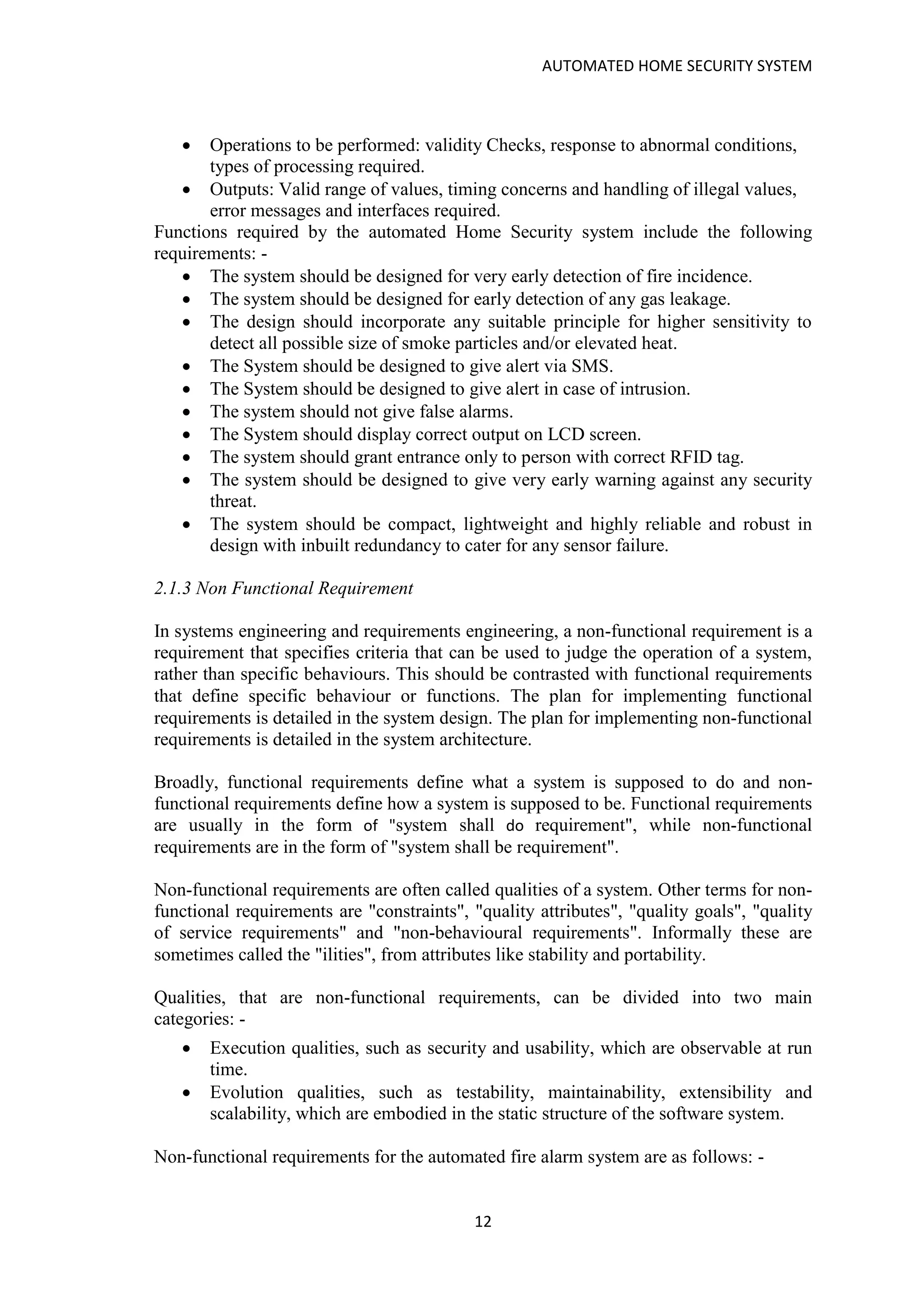






![AUTOMATED HOME SECURITY SYSTEM
53
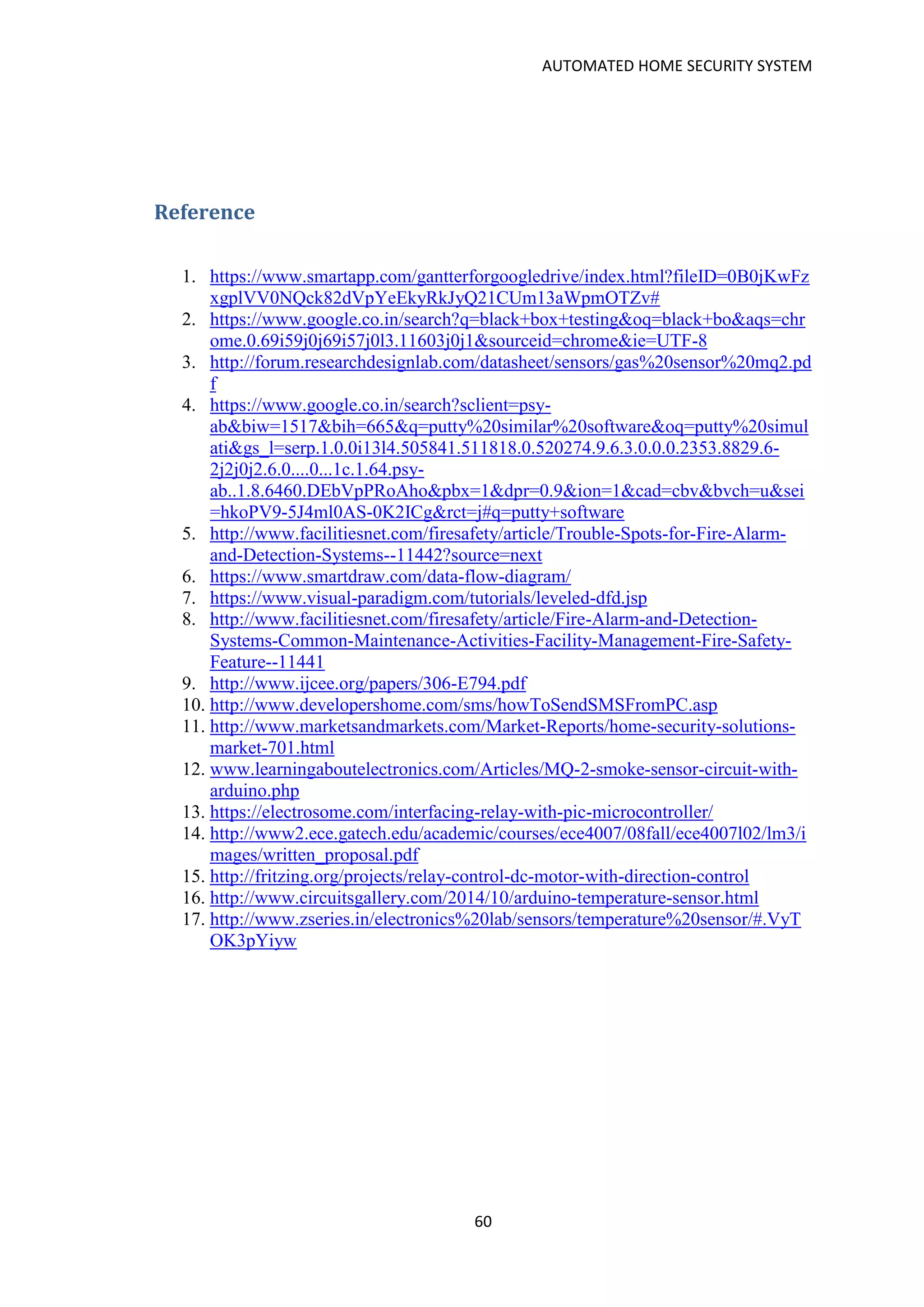
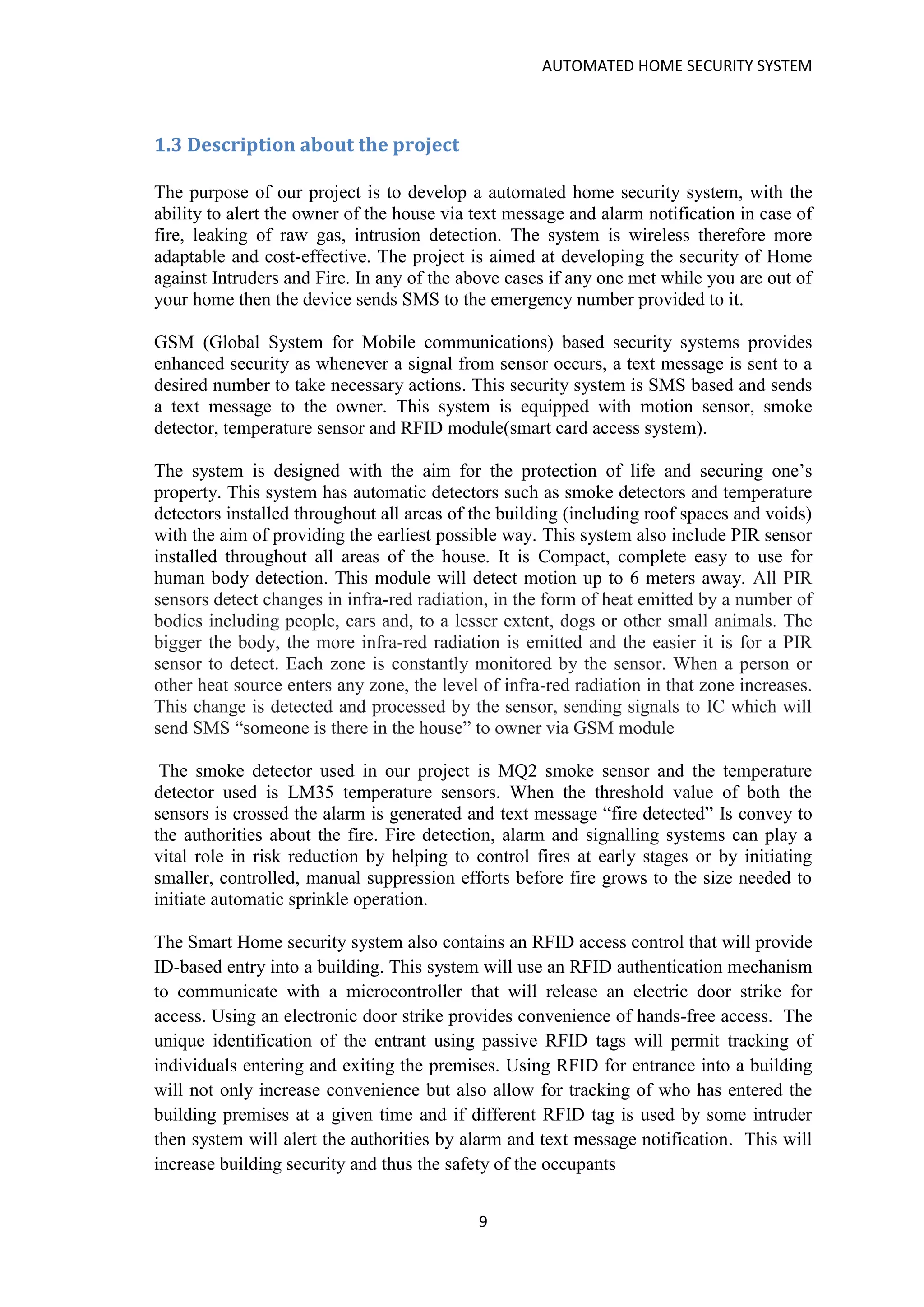
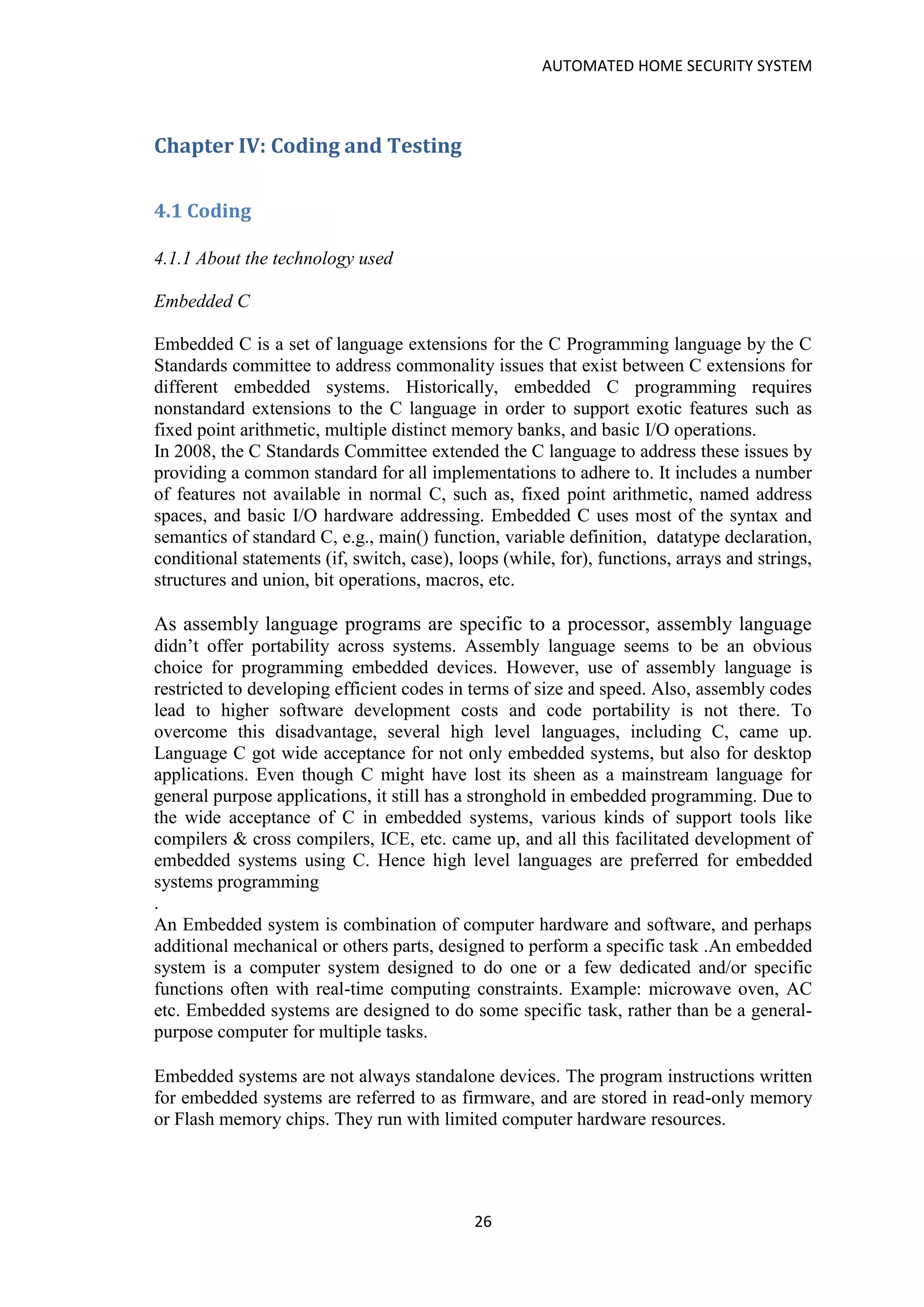
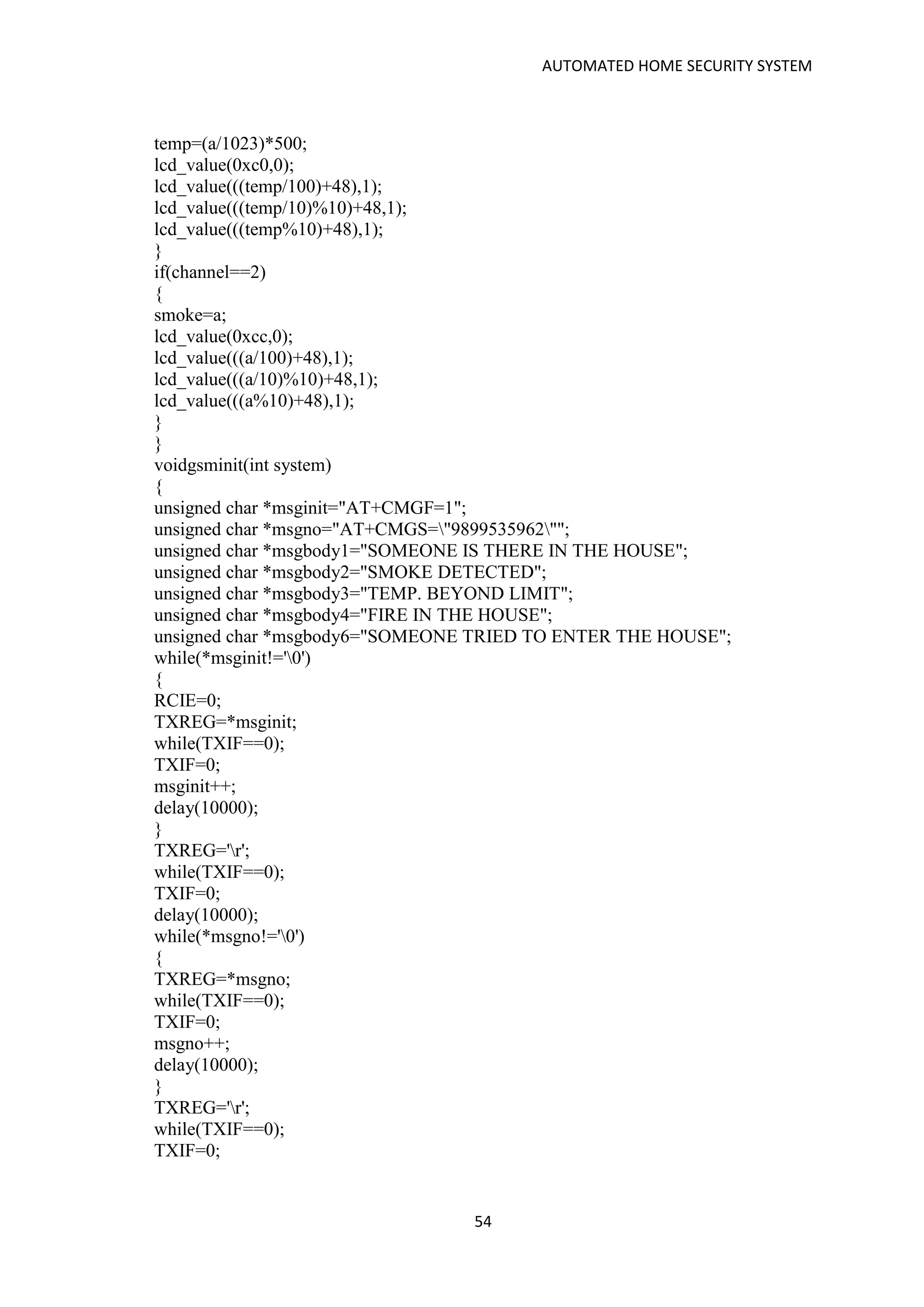
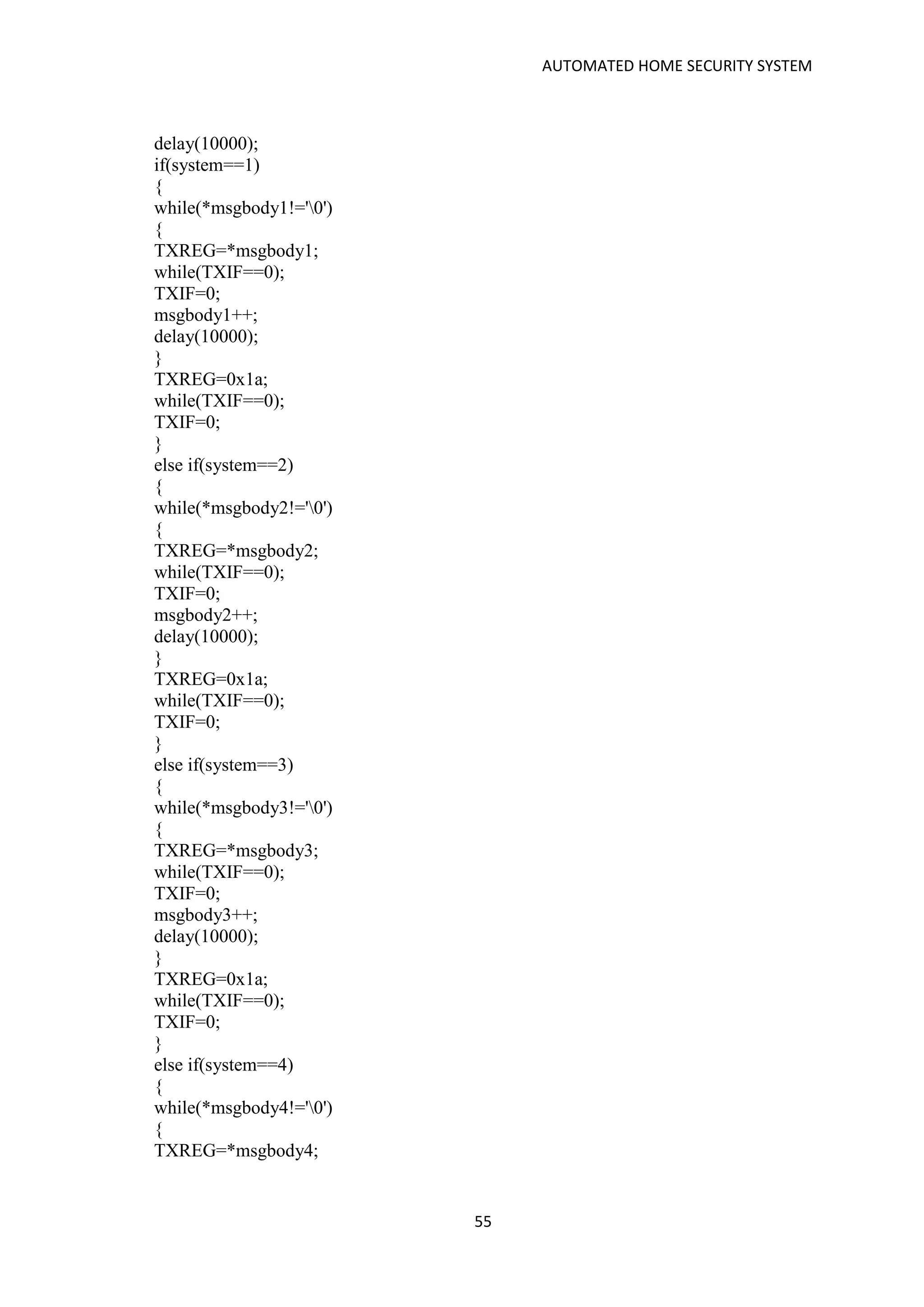
#define RS RD7
#define EN RD6
#define lcd PORTB
unsignedinttemp,smoke,i=0,j=0,bytes=0,fstcard=0,scndcard=0;
charuid[12];
unsigned int card1[12]={'3','E','0','0','F','D','5','E','7','E','E','2'};
unsigned int card2[12]={'1','5','0','0','1','C','2','5','F','F','D','2'};
void delay(unsigned int x)
{
while(x--);
}
voidlcd_value(unsigned intdata,unsignedintcmd)
{
RS=cmd;
lcd=data;
EN=1;
delay(10);
EN=0;
delay(100);
}
voiddisp(unsigned char *string,intline,int place)
{
if(line==1)
lcd_value((0x80+place),0);
if(line==2)
lcd_value((0xc0+place),0);
while(*string!='0')
{
lcd_value(*string,1);
string++;
}
}
voidadc(int channel)
{
int a;
if(channel==1)
ADCON0=0x00;
if(channel==2)
ADCON0=0x04;
ADCON1=0x80;
delay(10000);
GO=1;
while(GO==1);
a=(ADRESH*256)+ADRESL;
if(channel==1)
{](https://image.slidesharecdn.com/automatedhomesecuirtyproject-180128222540/75/Automated-home-secuirty-project-53-2048.jpg)
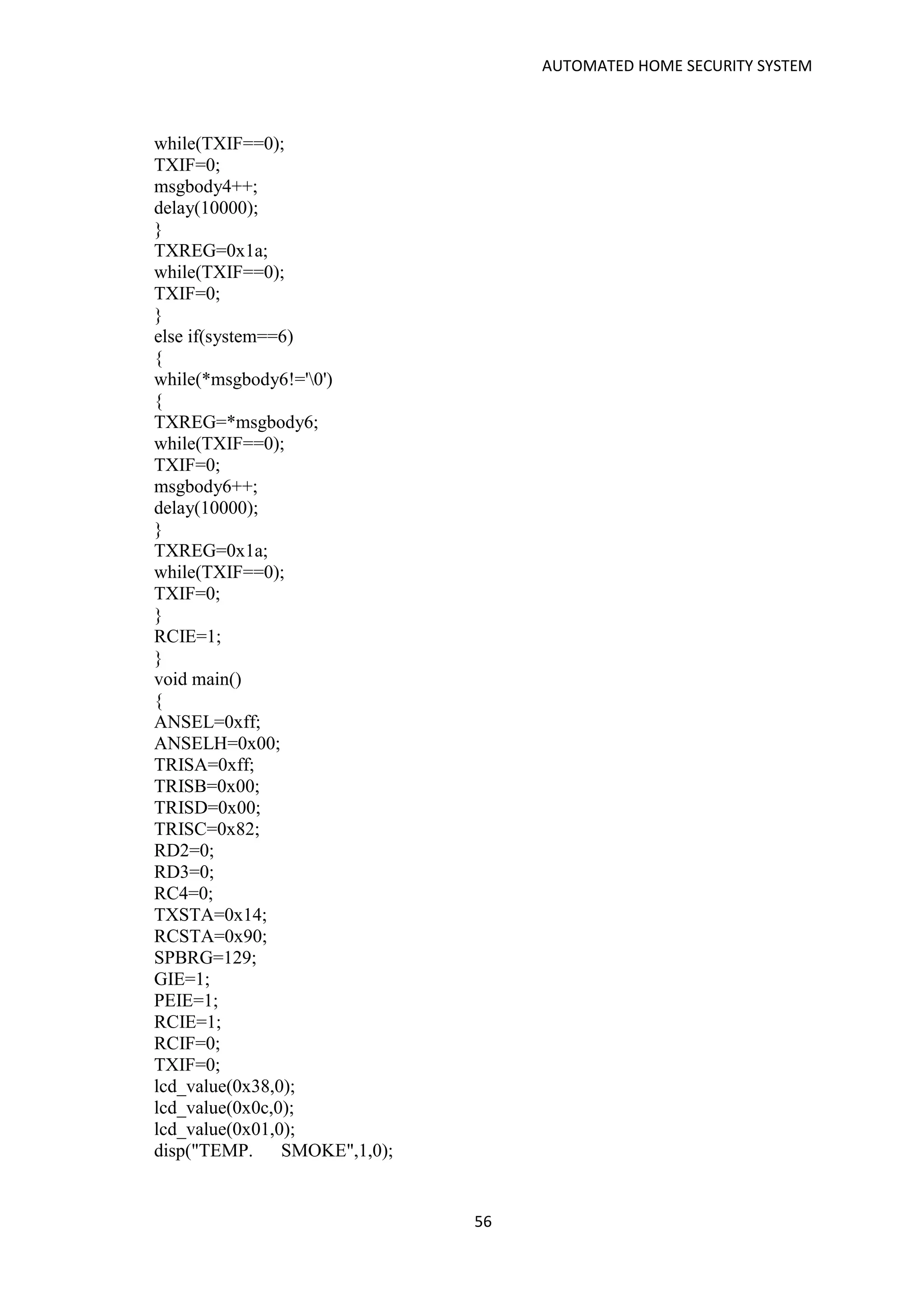
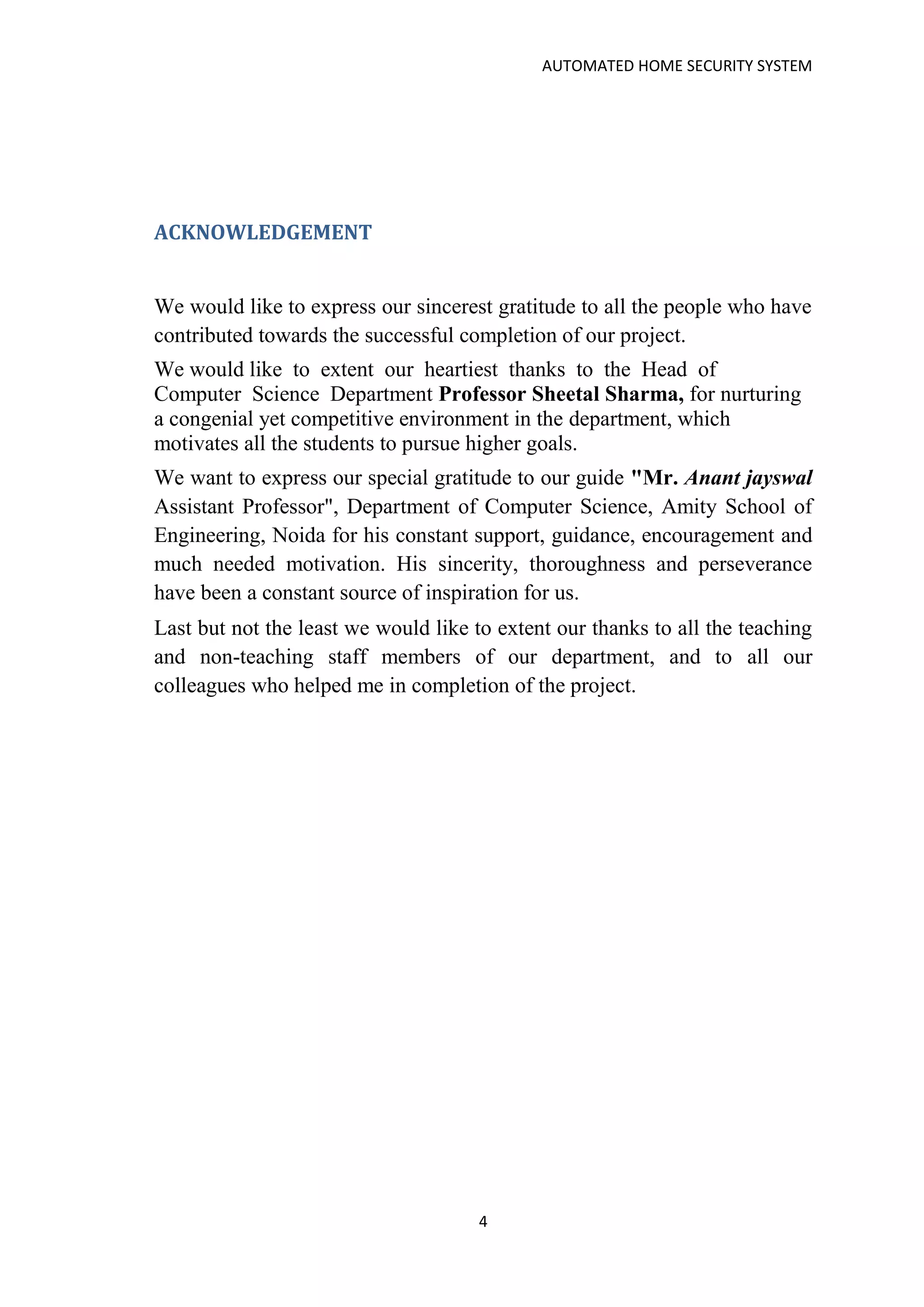
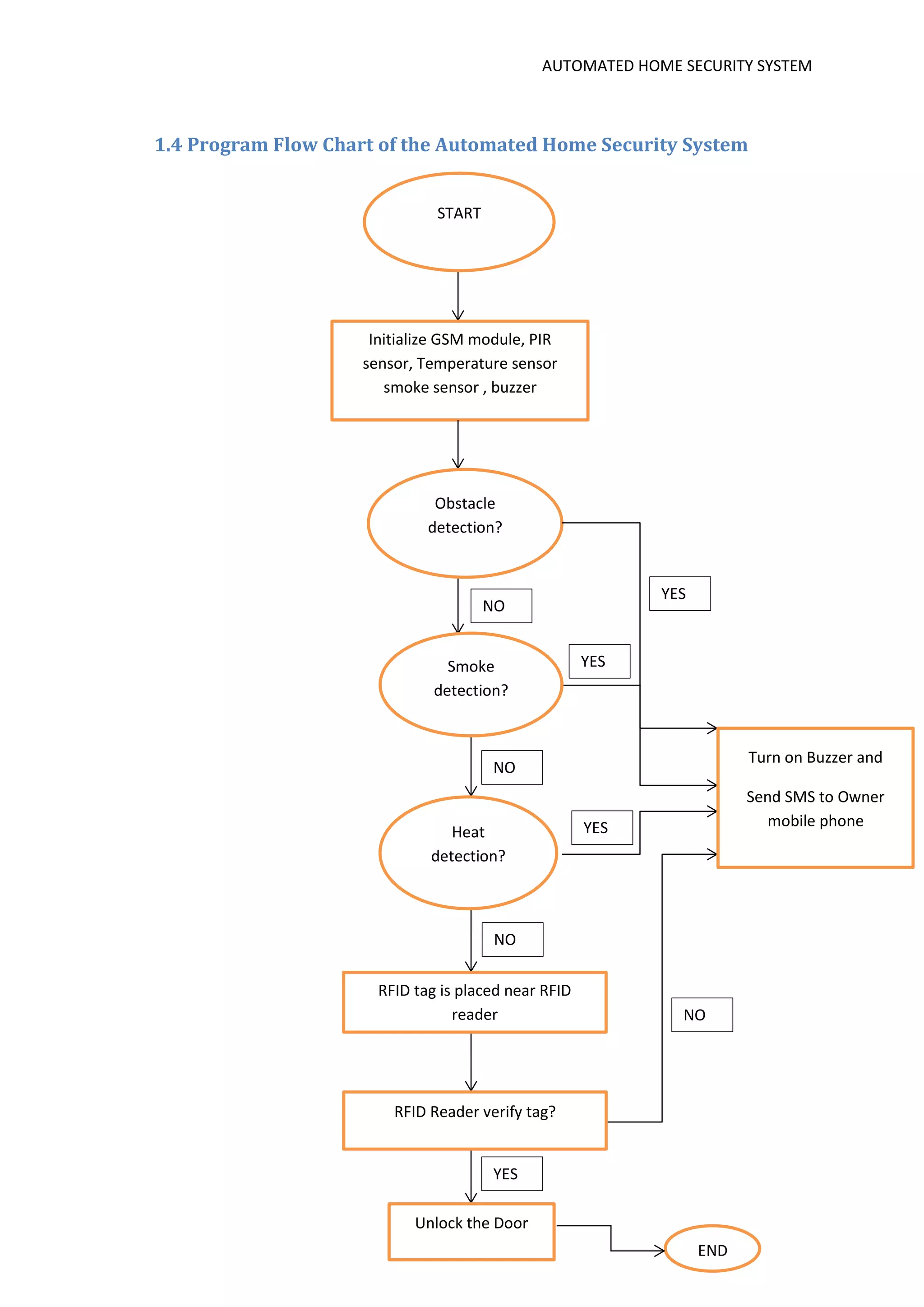
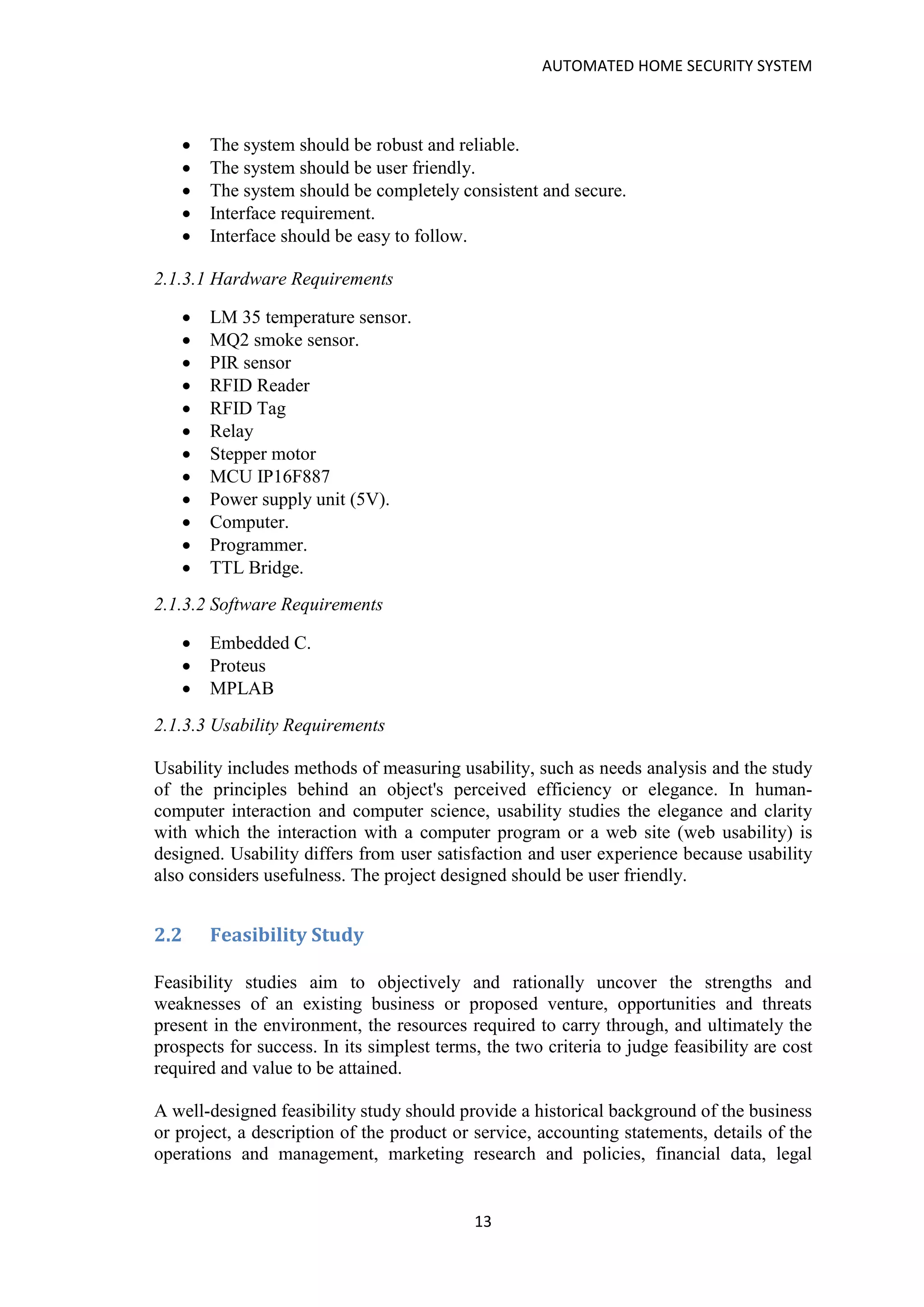
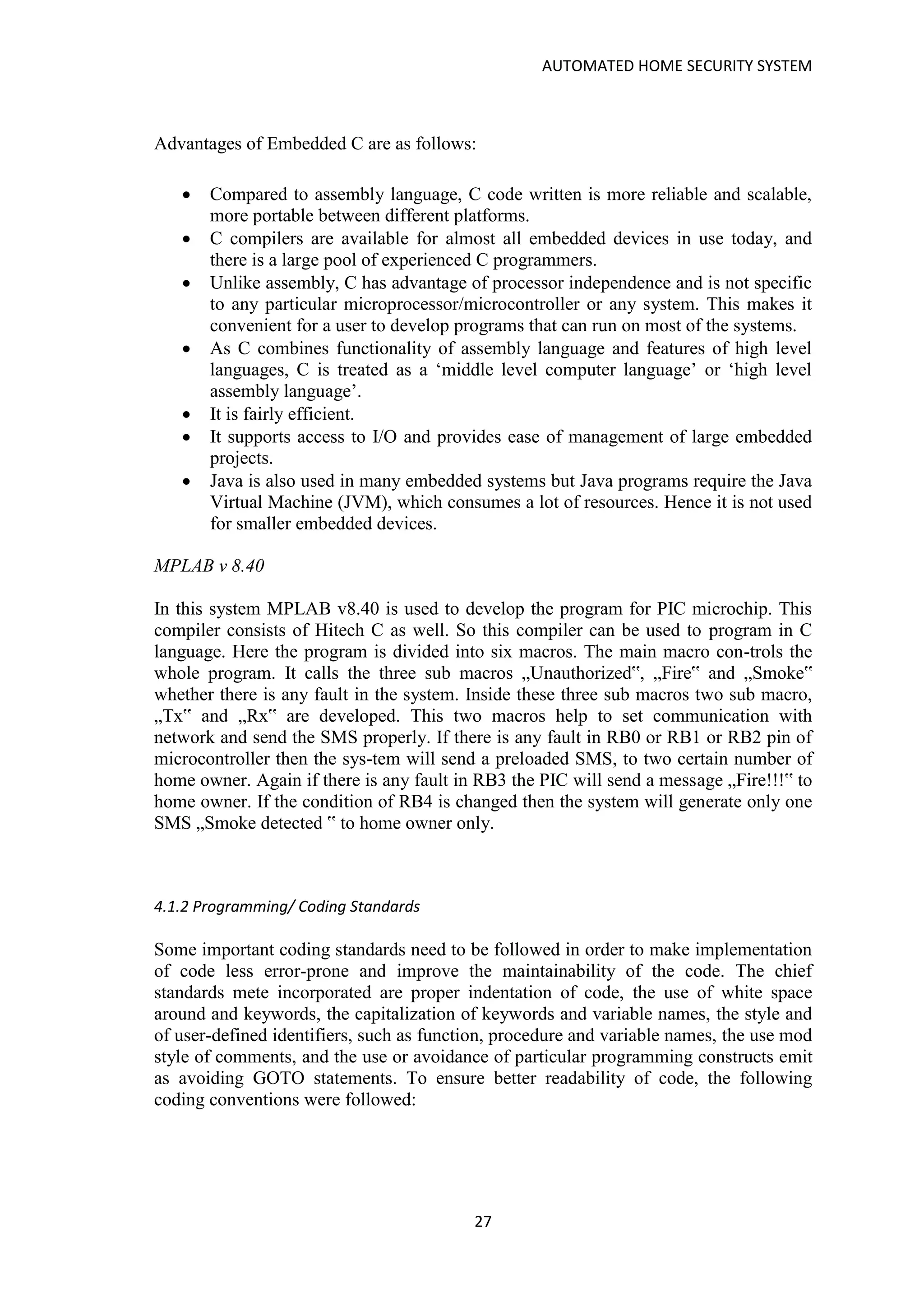
![AUTOMATED HOME SECURITY SYSTEM
58
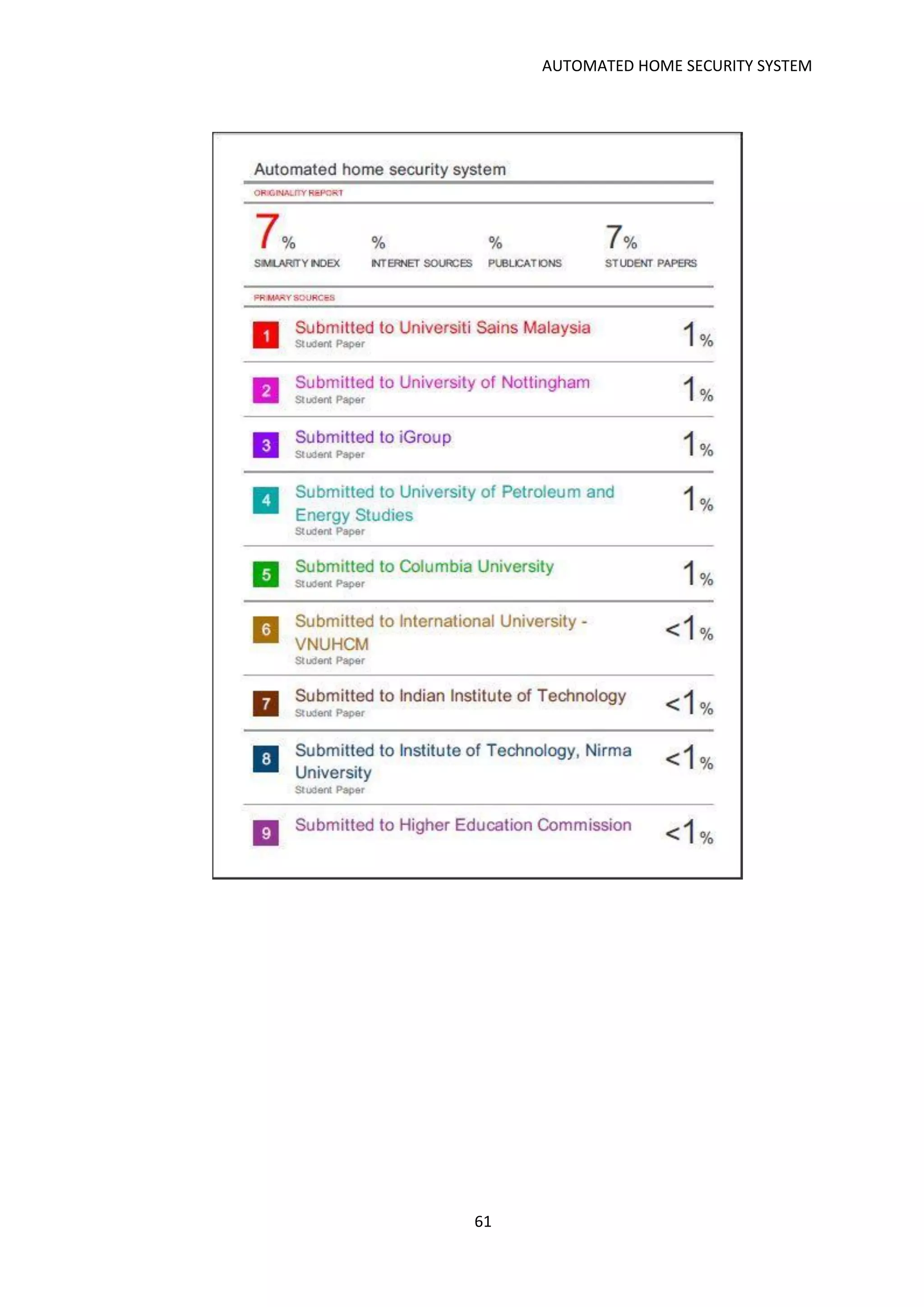
disp("IN THE HOUSE",2,0);
for(i=0;i<=20;i++)
delay(12000);
RC4=0;
gsminit(4);
lcd_value(0x01,0);
disp("TEMP. SMOKE",1,0);
}
if(bytes==12)
{
j=0;
bytes=0;
if(uid[0]==card1[0]&&uid[1]==card1[1]&&uid[2]==card1[2]&&uid[3]==card1[3]&&
uid[4]==card1[4]&&uid[5]==card1[5]&&uid[6]==card1[6]&&uid[7]==card1[7]&&uid
[8]==card1[8]&&uid[9]==card1[9]&&uid[10]==card1[10]&&uid[11]==card1[11])
fstcard=1;
if(uid[0]==card2[0]&&uid[1]==card2[1]&&uid[2]==card2[2]&&uid[3]==card2[3]&&
uid[4]==card2[4]&&uid[5]==card2[5]&&uid[6]==card2[6]&&uid[7]==card2[7]&&uid
[8]==card2[8]&&uid[9]==card2[9]&&uid[10]==card2[10]&&uid[11]==card2[11])
scndcard=1;
if(fstcard==1||scndcard==1)
{
lcd_value(0x01,0);
fstcard=0;
scndcard=0;
disp("ACCESS GRANTED",2,0);
RD2=1;
RC4=1;
for(i=0;i<=20;i++)
delay(12000);
RC4=0;
RD2=0;
delay(25000);
RD3=1;
for(i=0;i<=20;i++)
delay(12000);
RD3=0;
lcd_value(0x01,0);
disp("TEMP. SMOKE",1,0);
}
else
{
lcd_value(0x01,0);
disp("ACCESS DENIED",2,0);
RC4=1;
for(i=0;i<=20;i++)
delay(12000);
RC4=0;](https://image.slidesharecdn.com/automatedhomesecuirtyproject-180128222540/75/Automated-home-secuirty-project-58-2048.jpg)
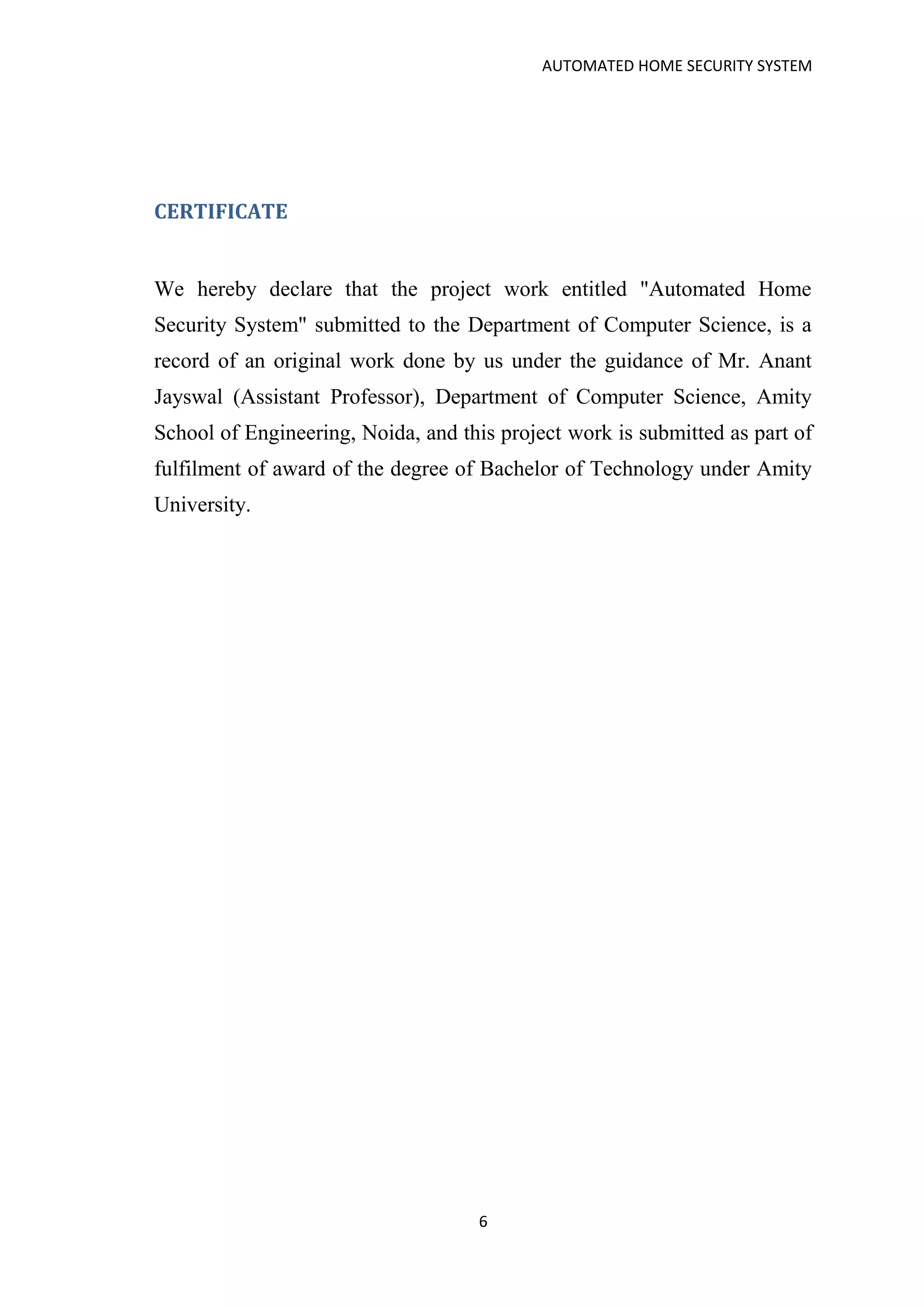
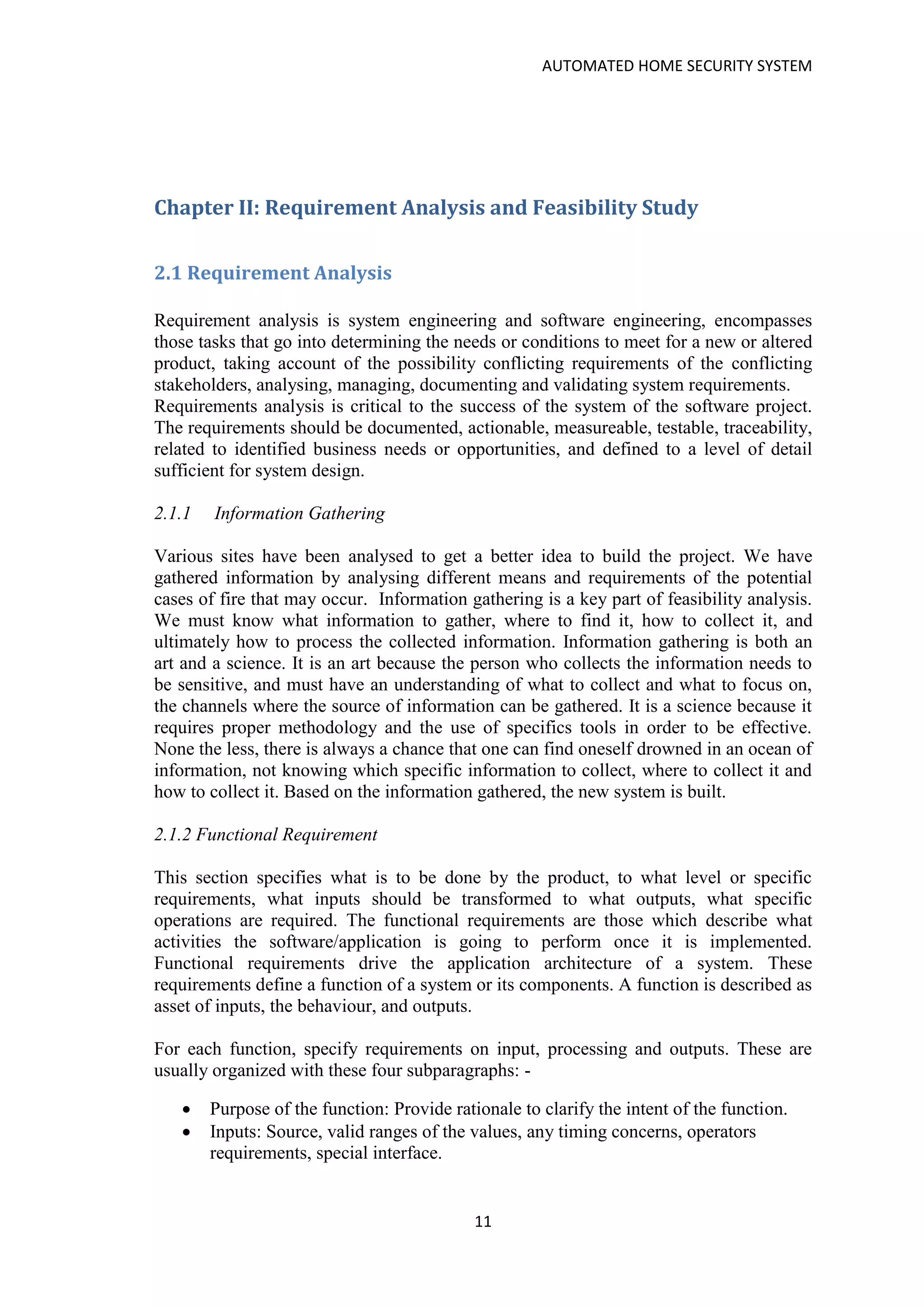
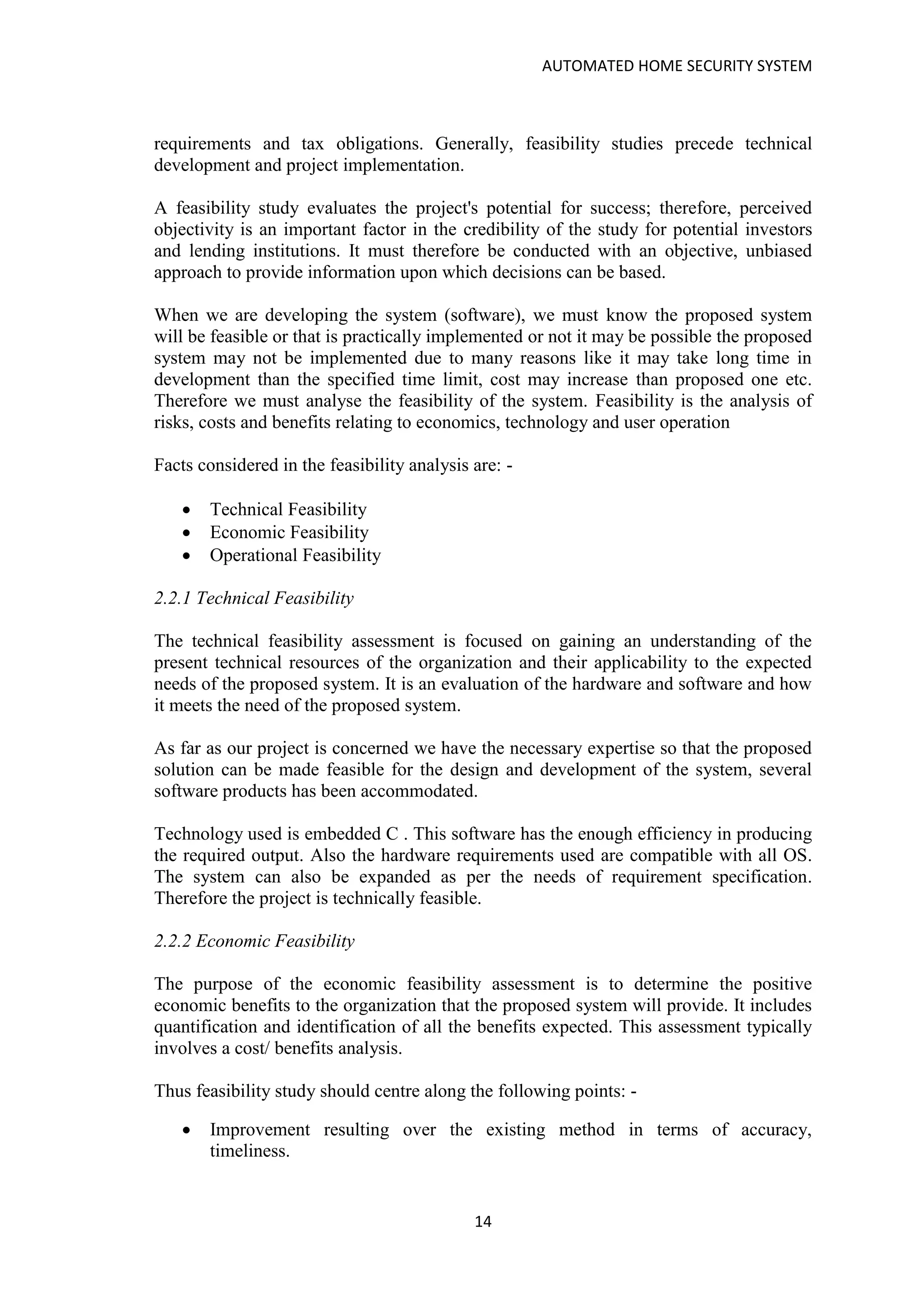
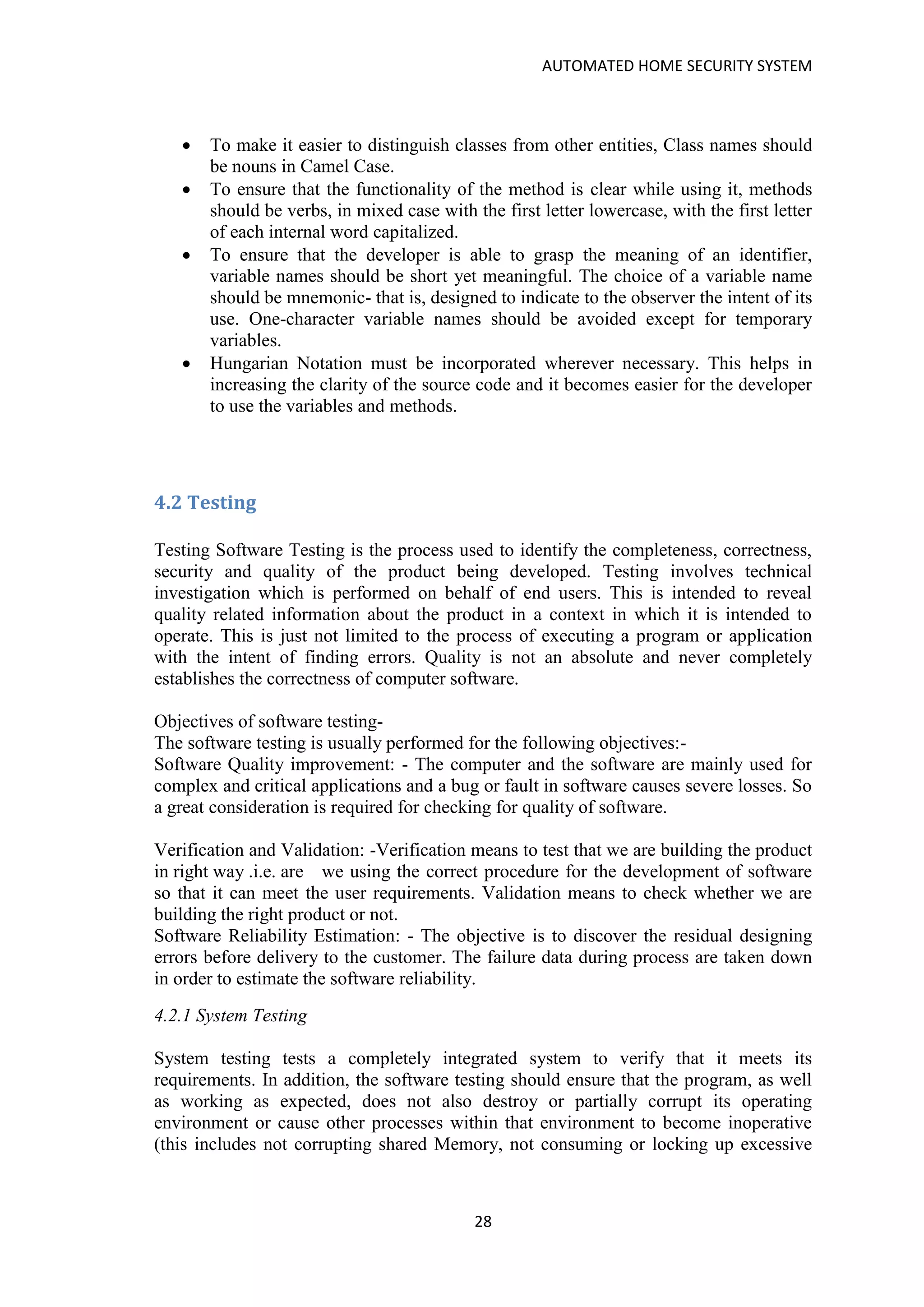
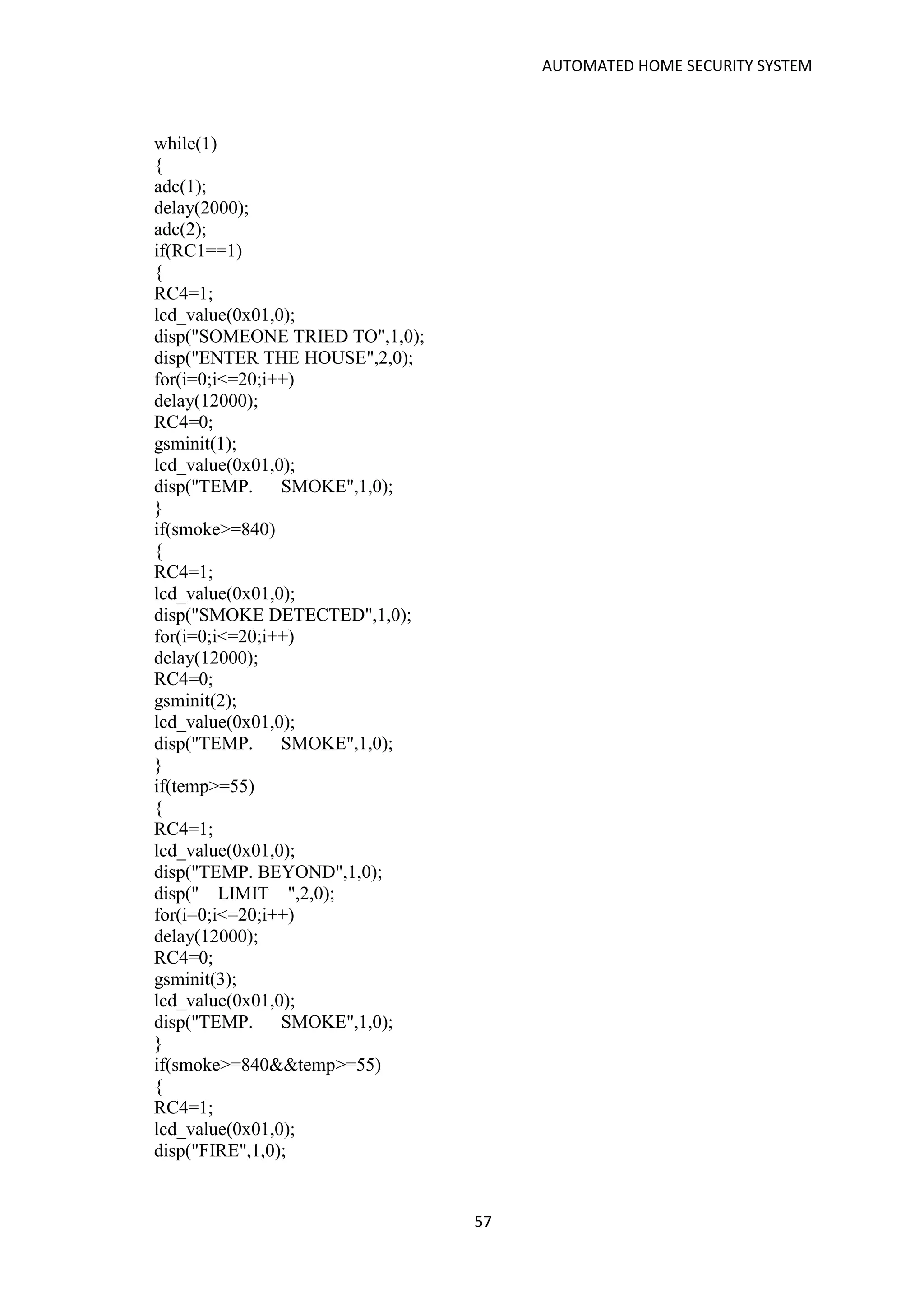
![AUTOMATED HOME SECURITY SYSTEM
59
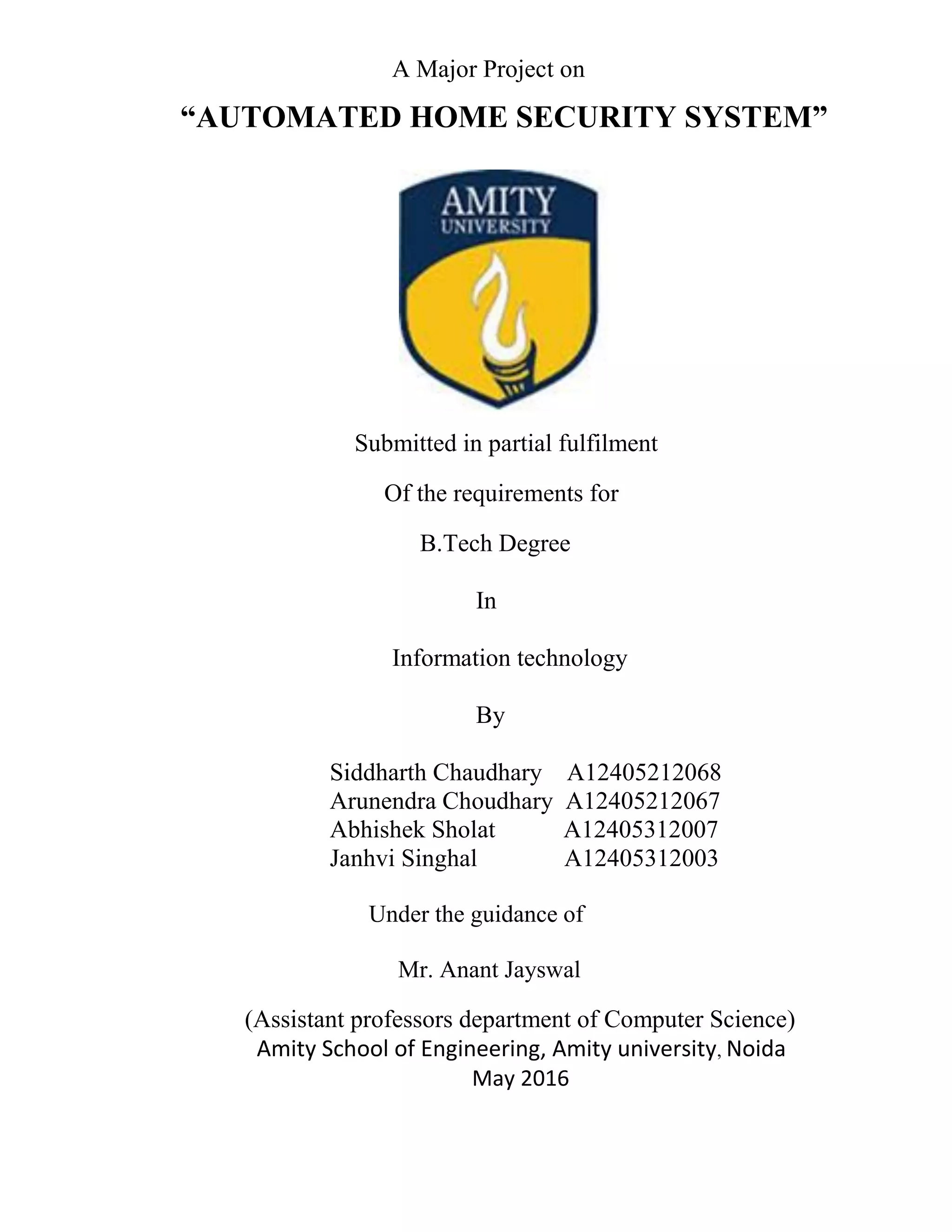
gsminit(6);
lcd_value(0x01,0);
disp("TEMP. SMOKE",1,0);
}
}
}
}
void interrupt isr()
{
RCIF=0;
j++;
bytes++;
uid[j]=RCREG;
}](https://image.slidesharecdn.com/automatedhomesecuirtyproject-180128222540/75/Automated-home-secuirty-project-59-2048.jpg)