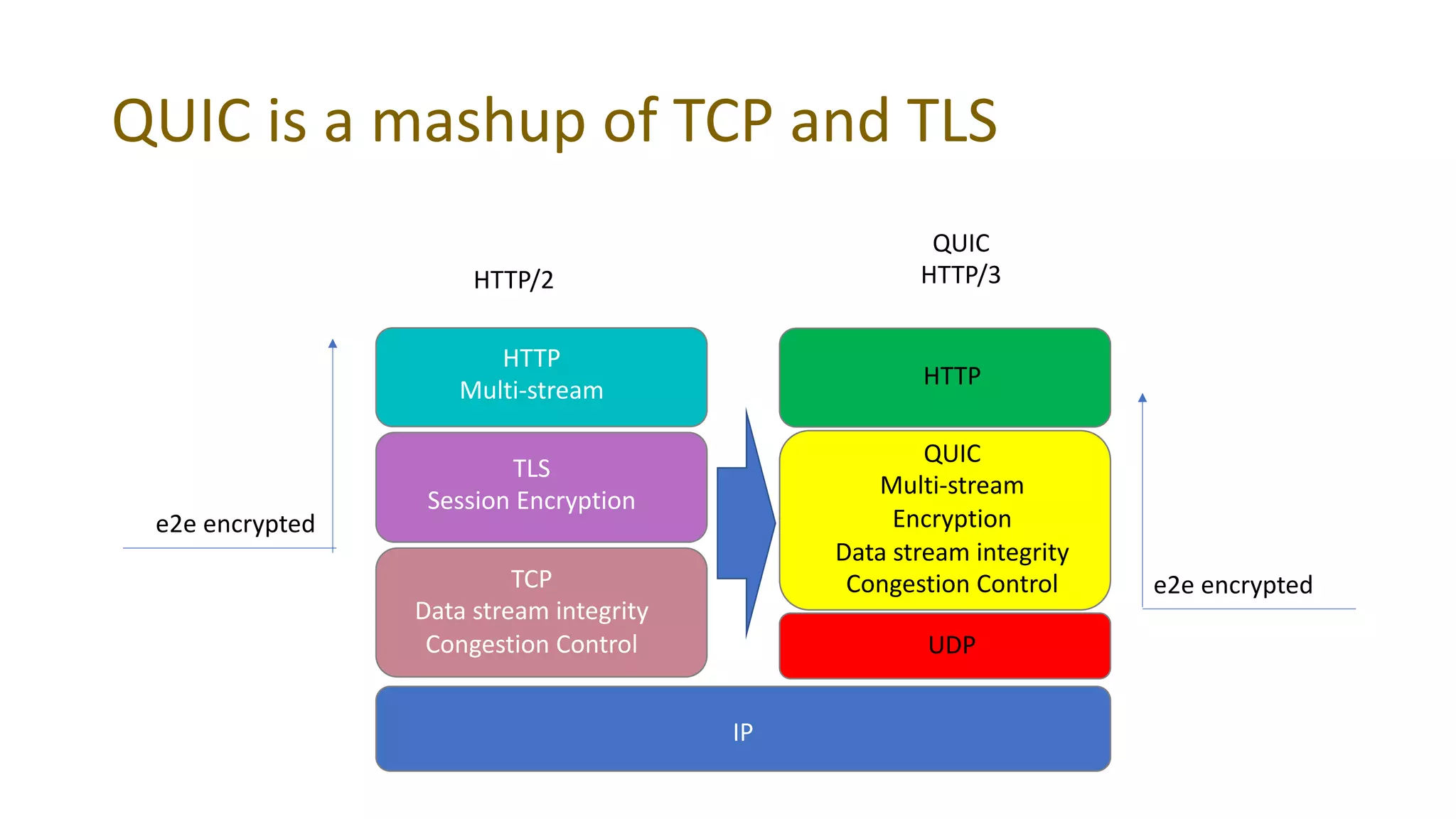
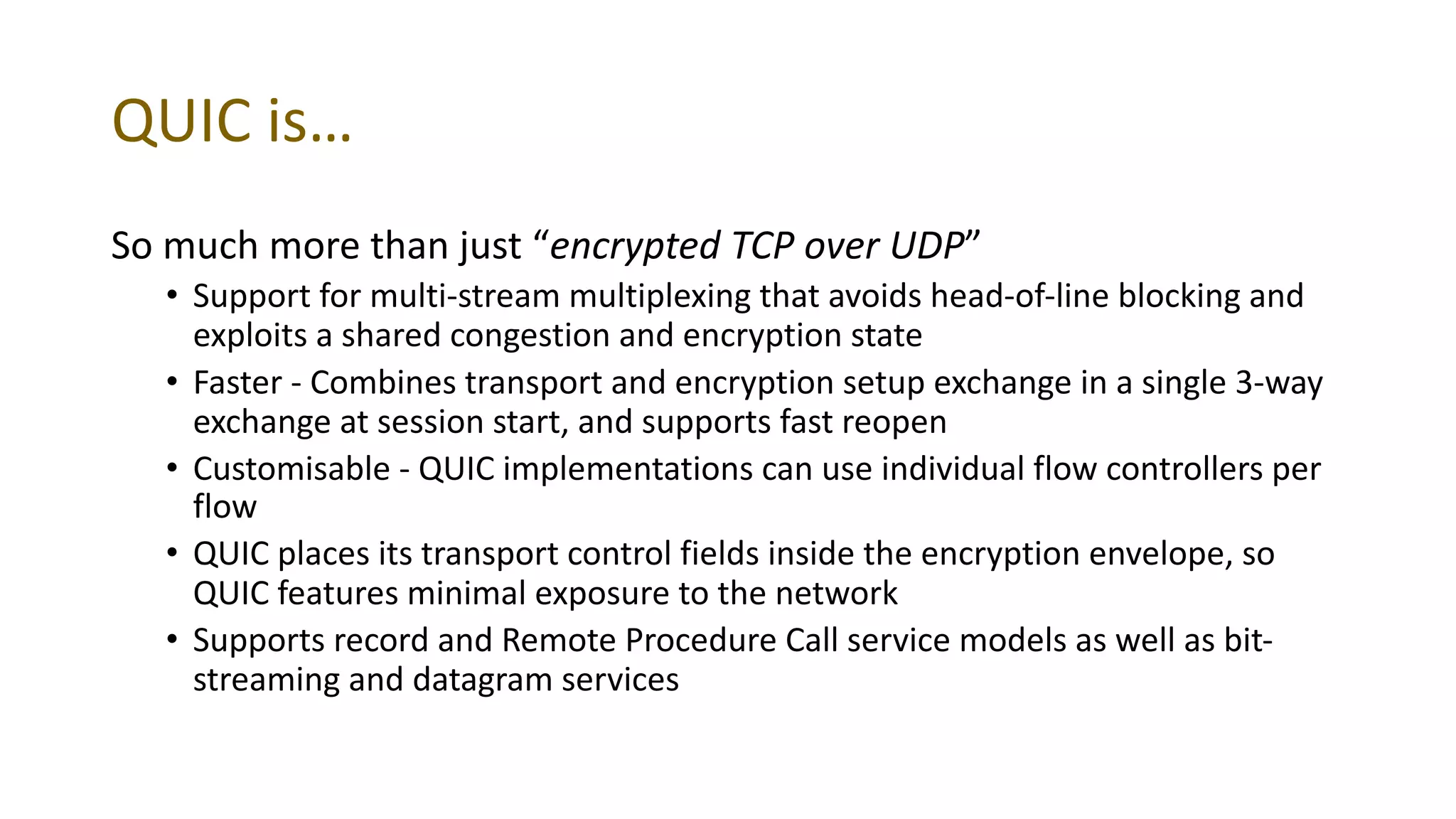
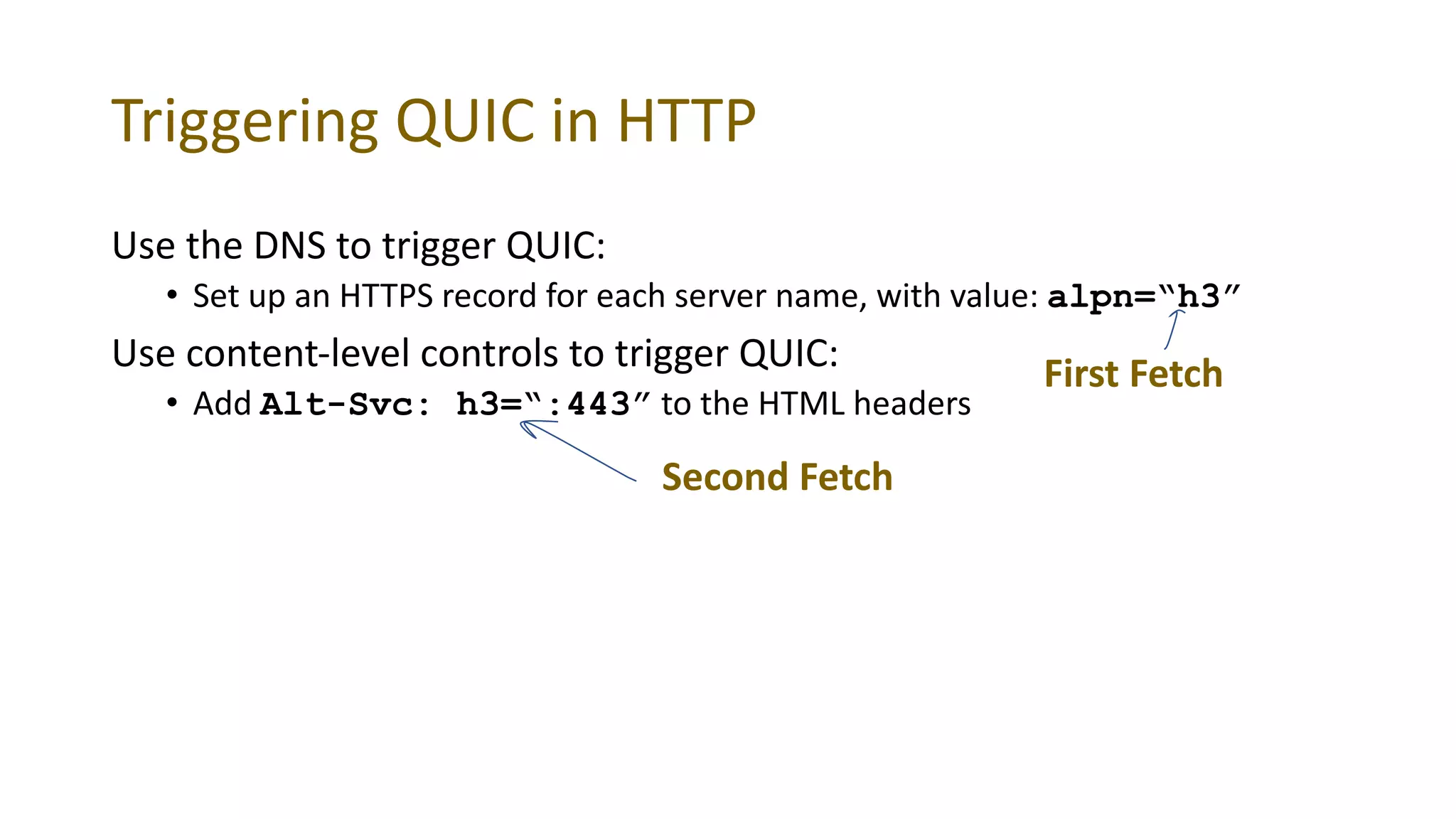
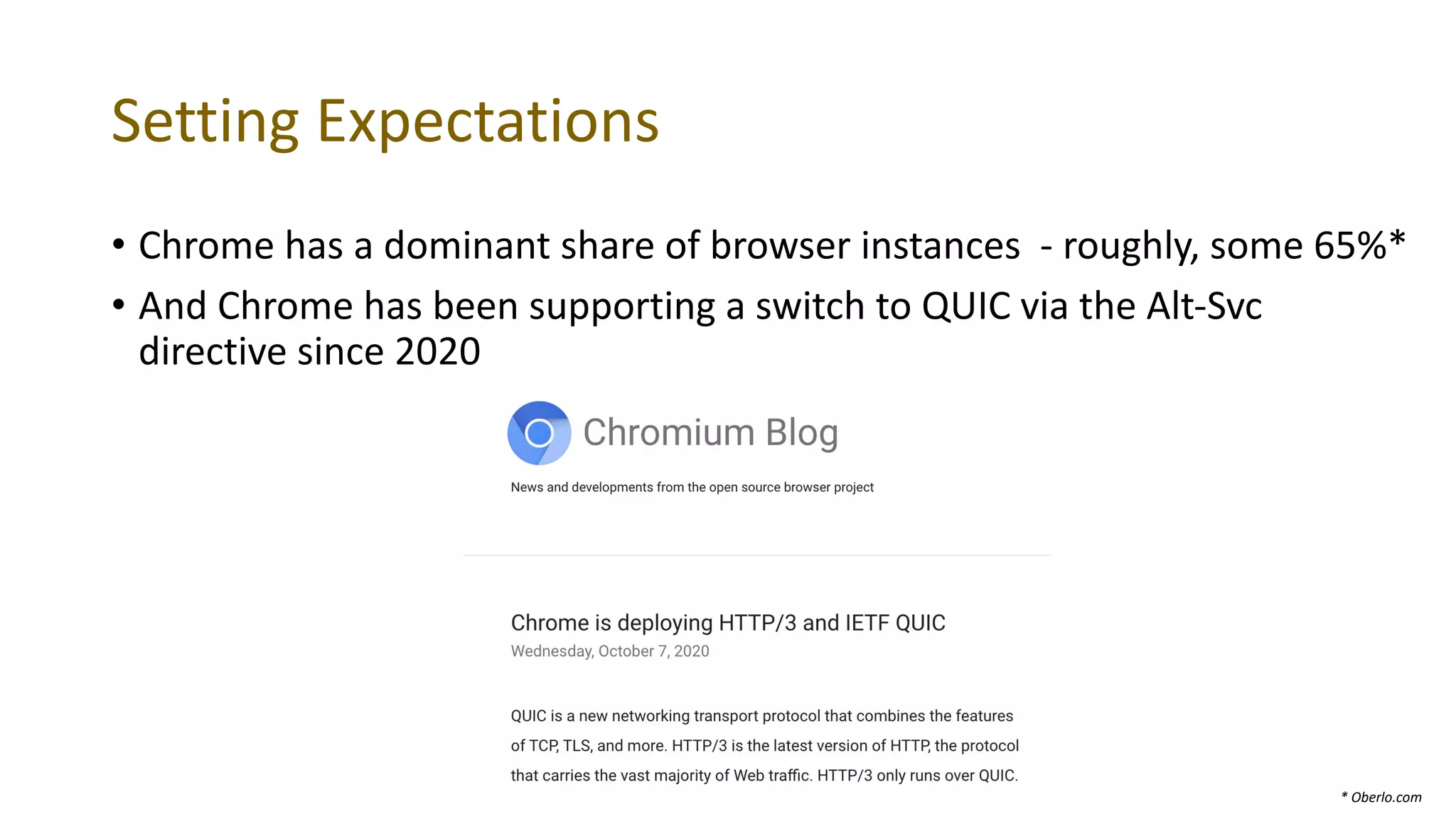
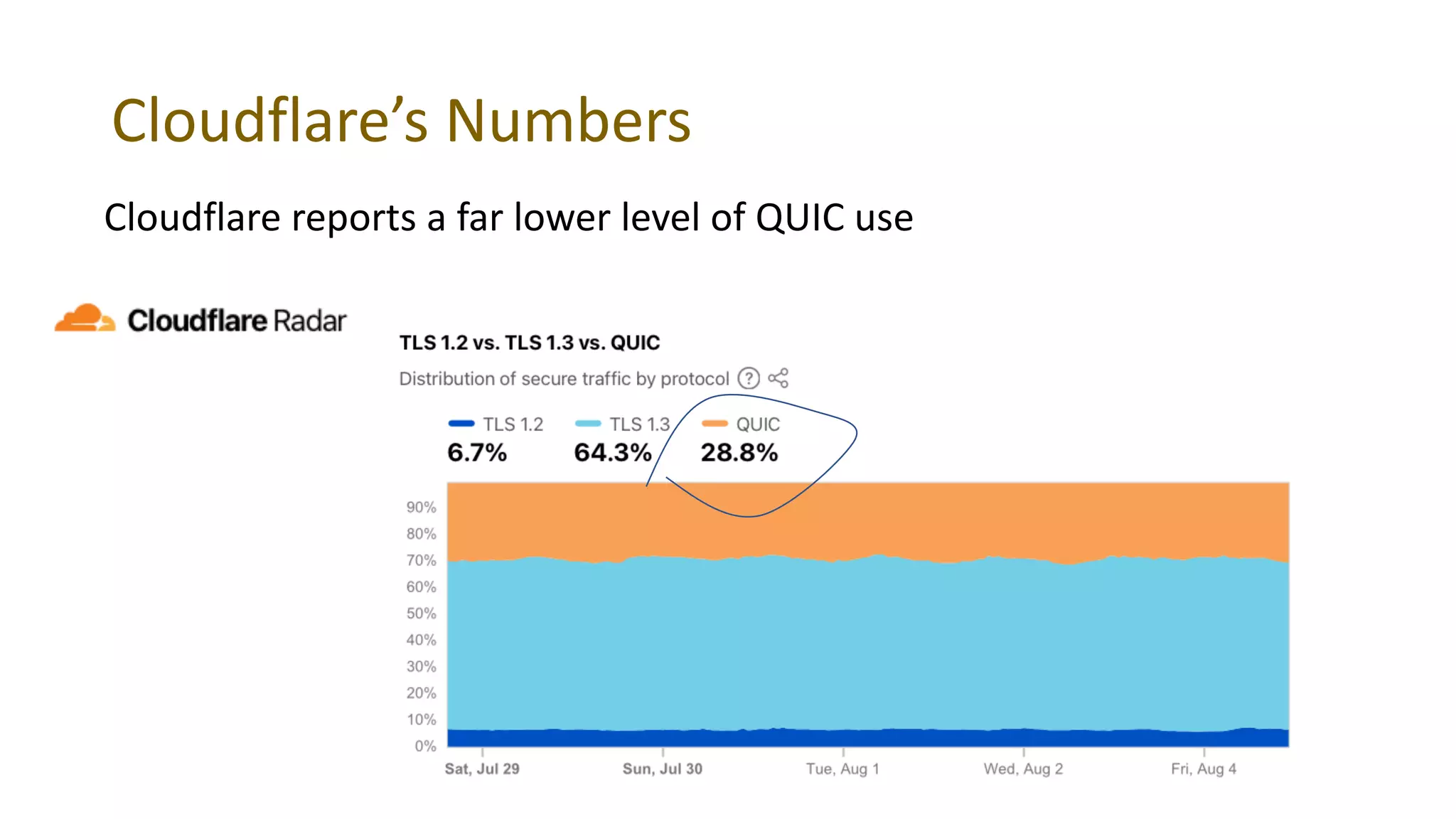
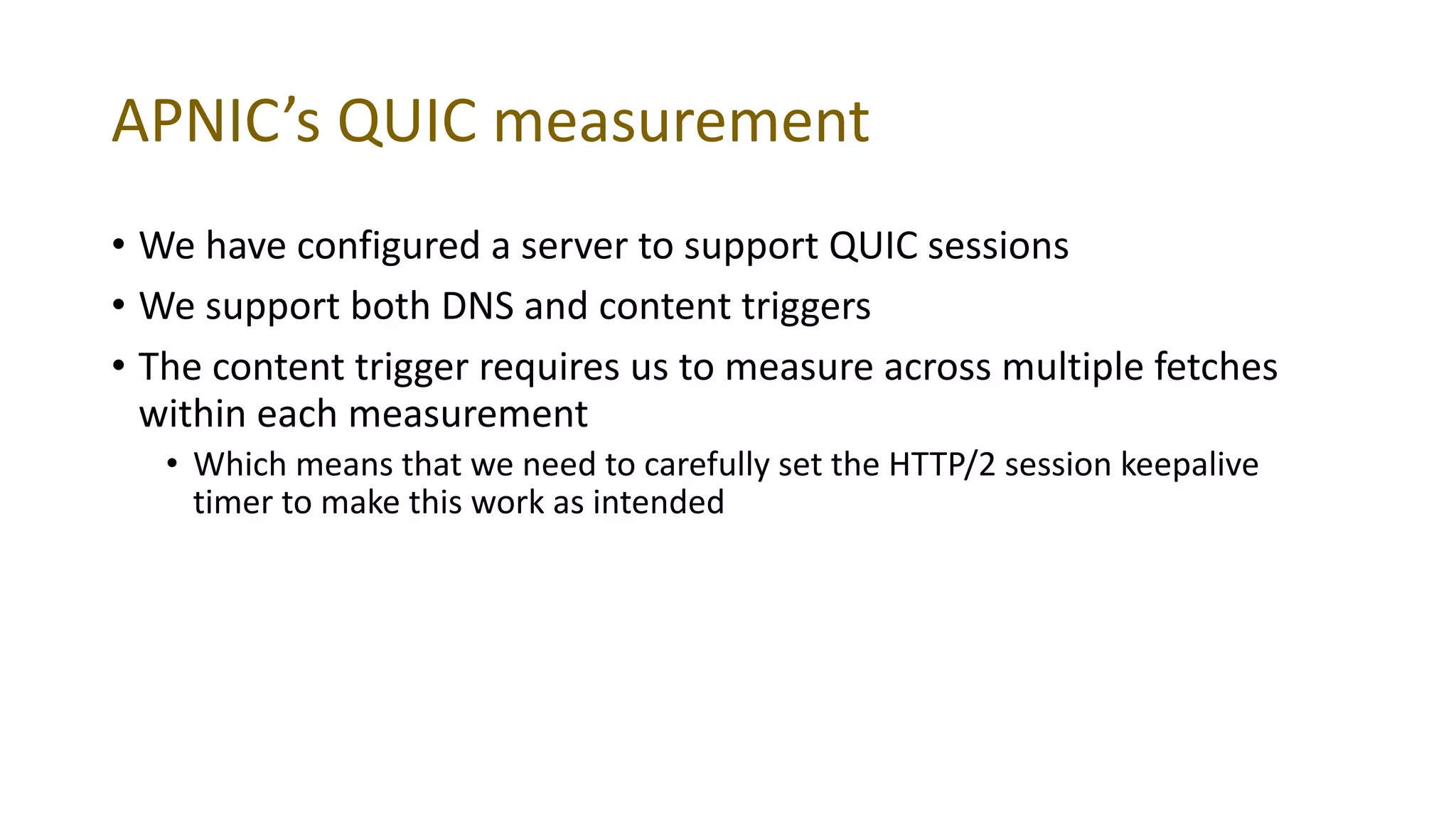
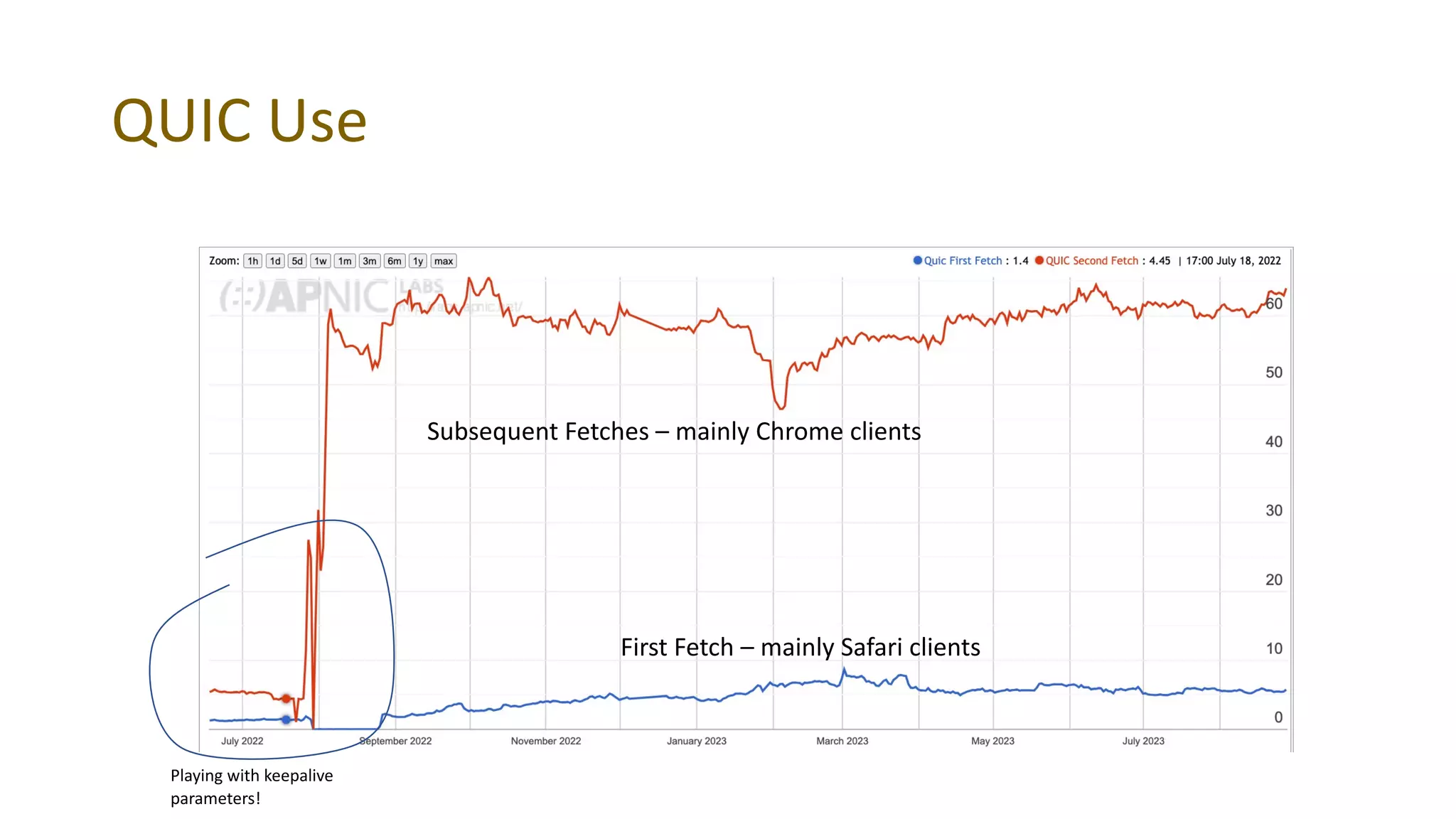
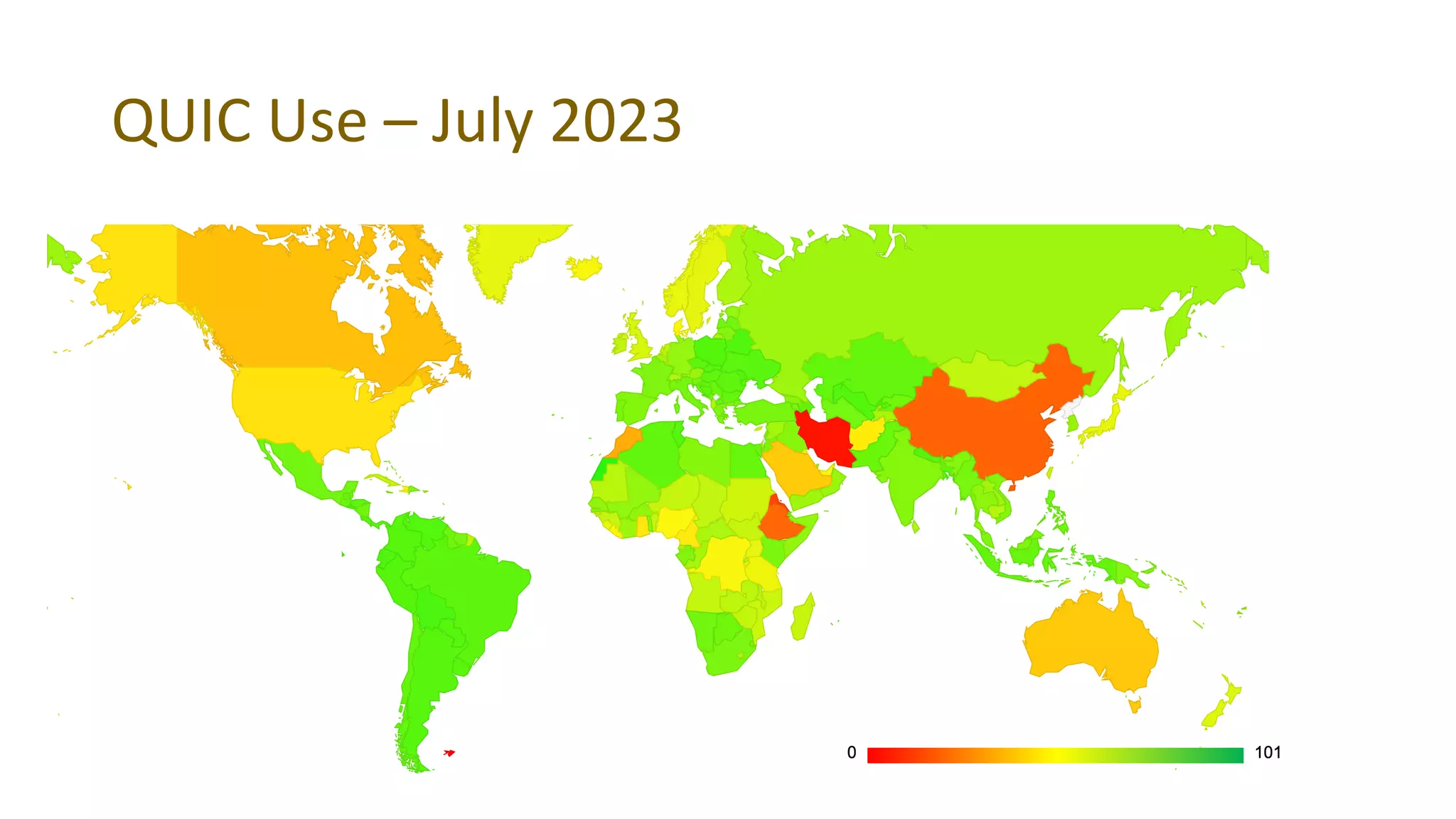
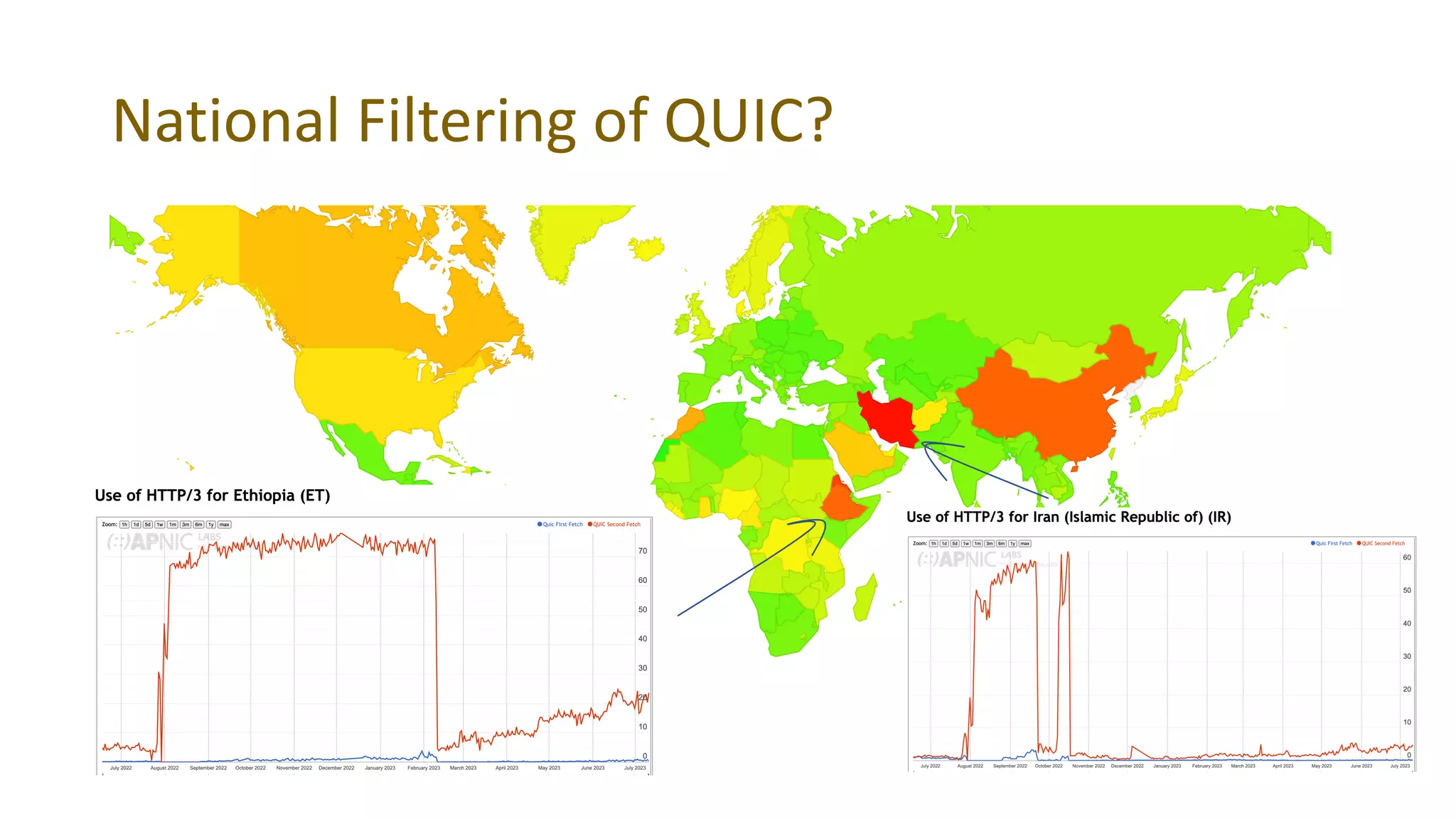
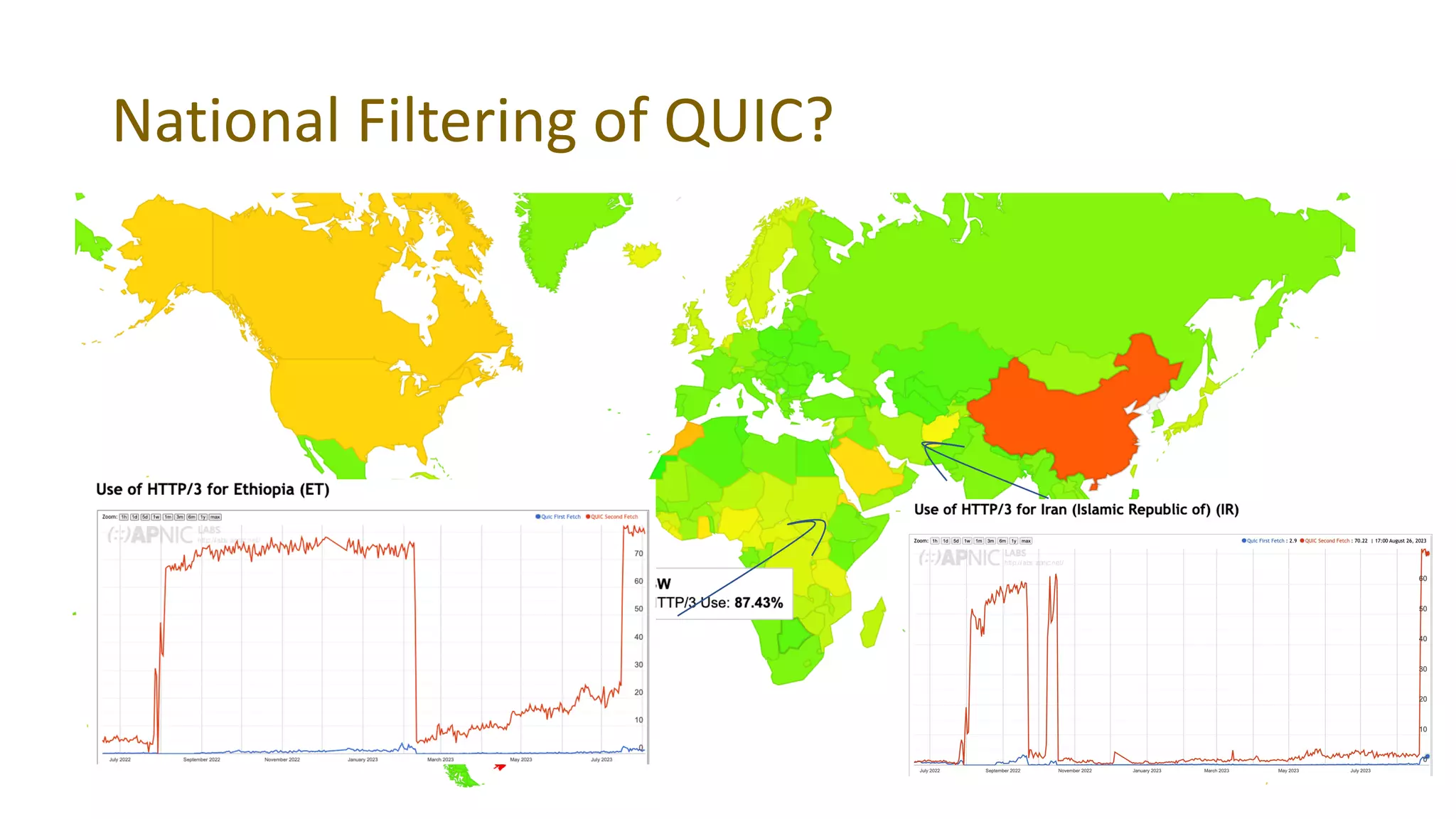
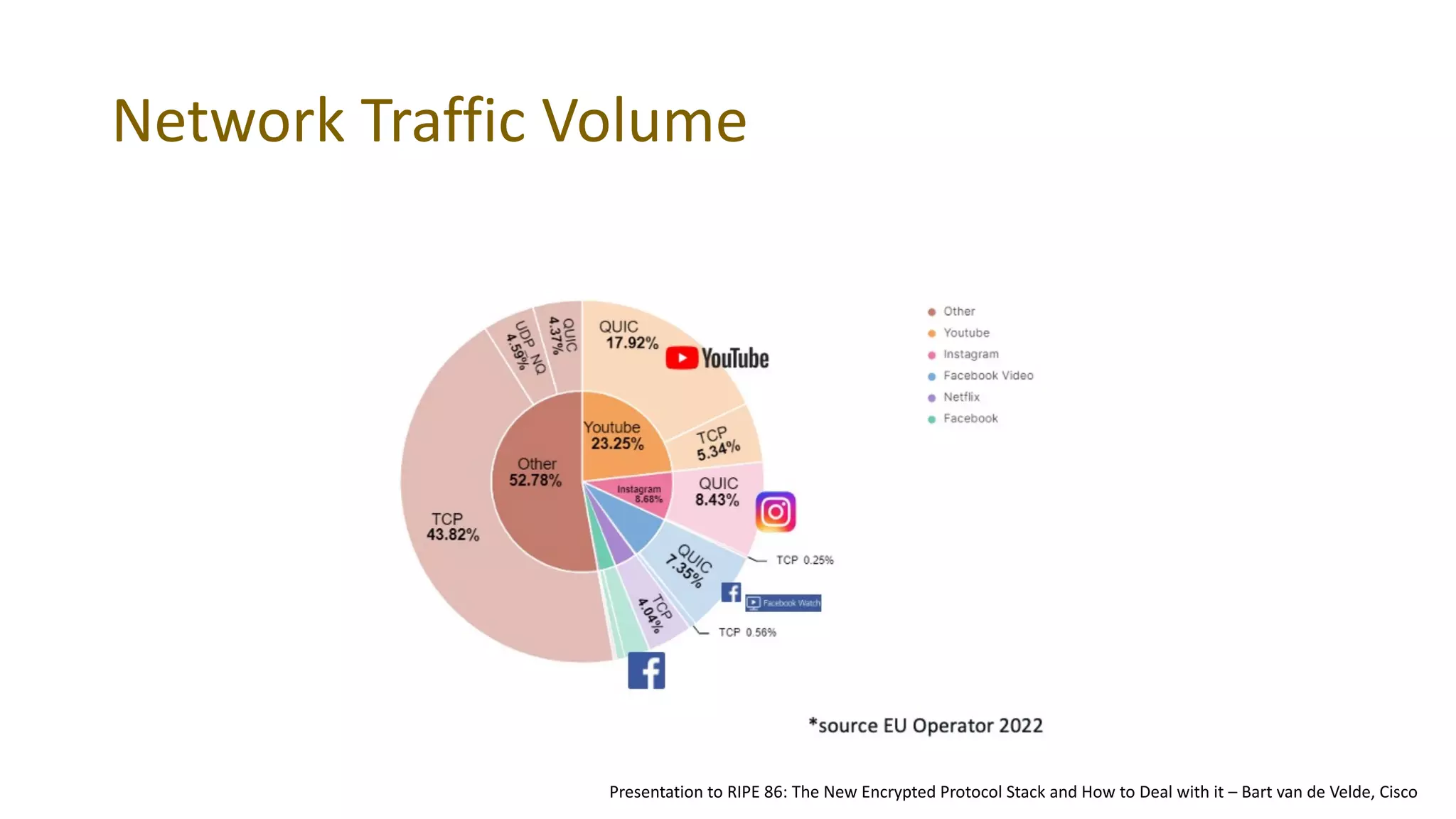
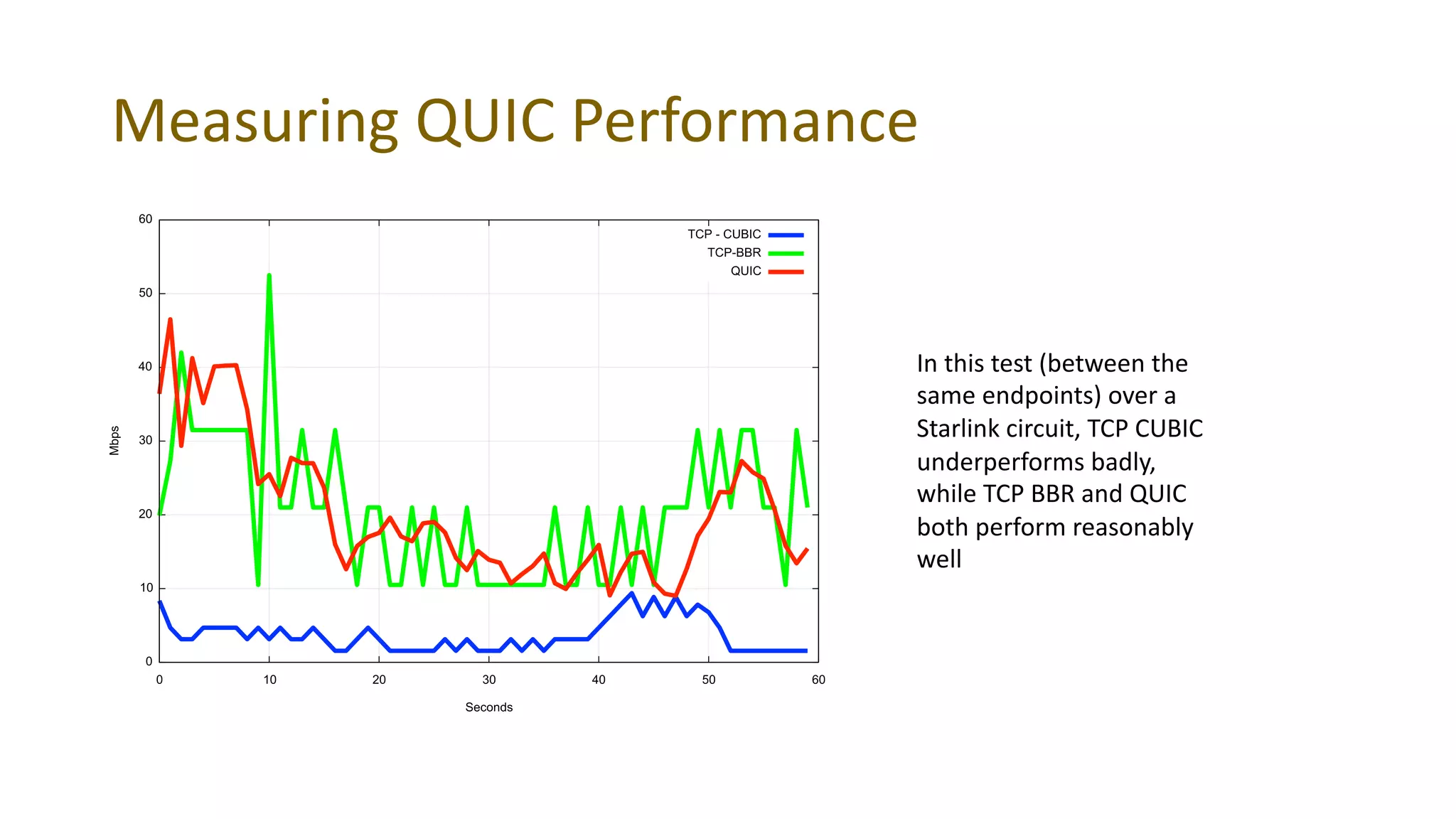
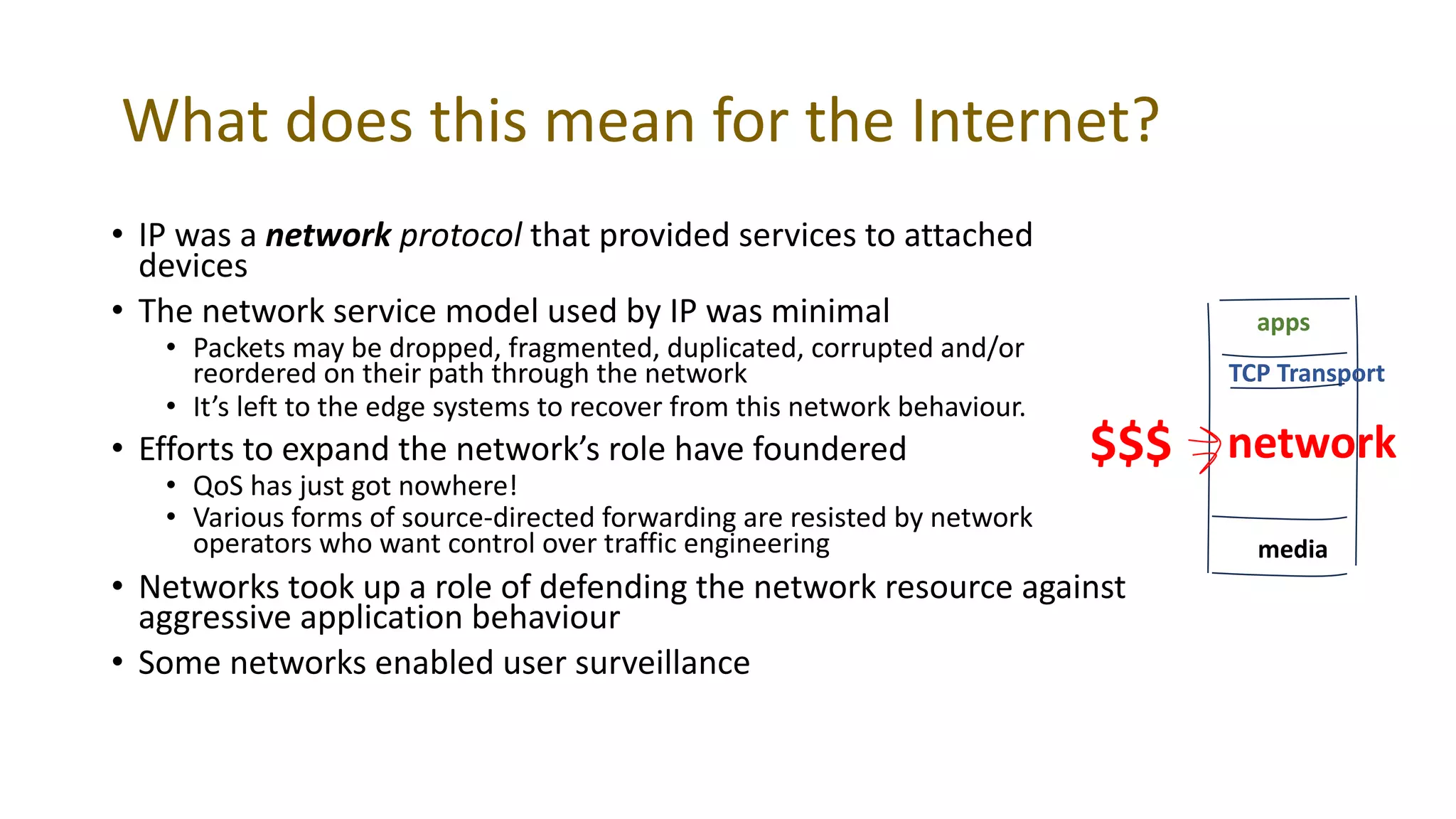
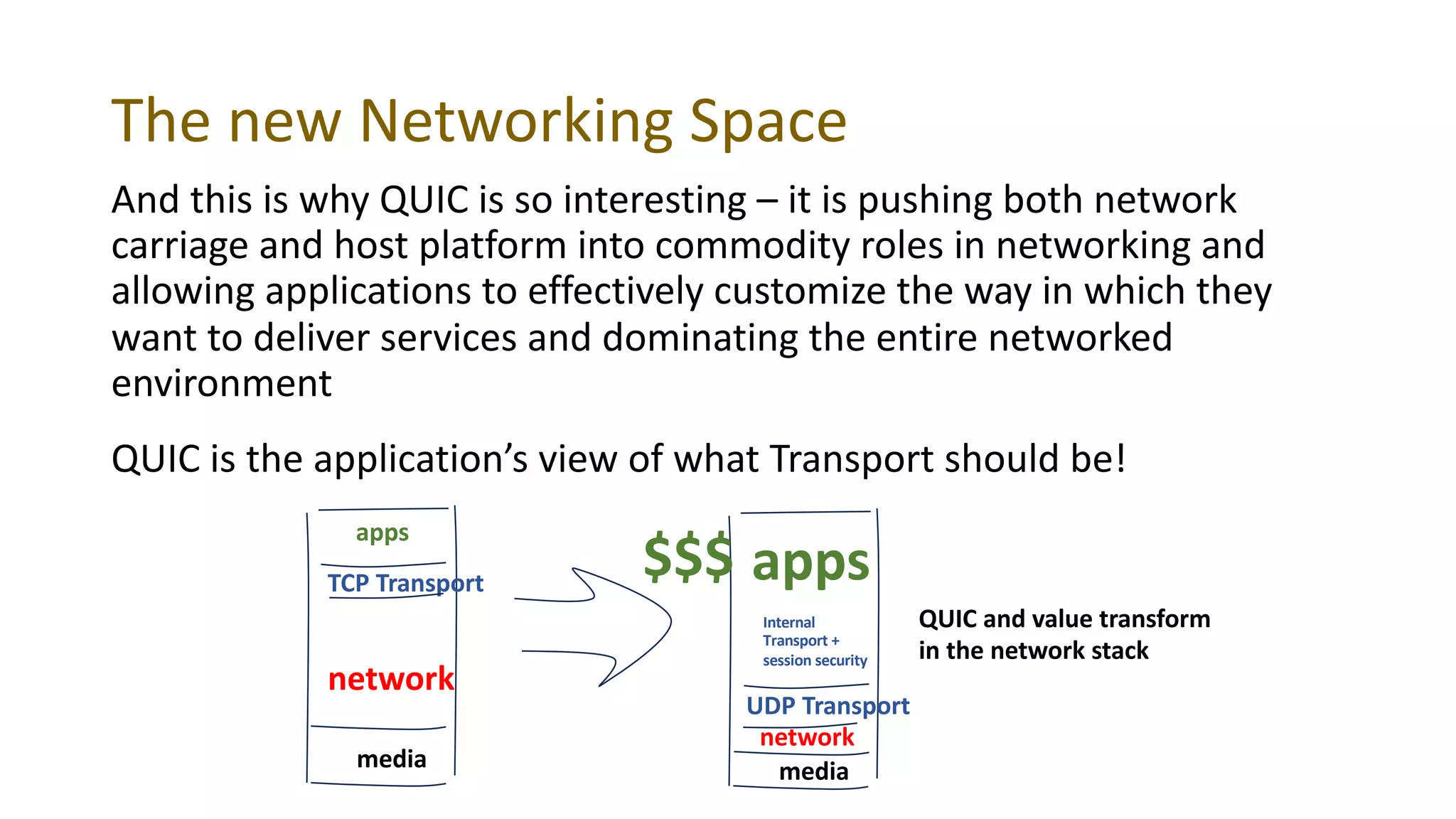
This document discusses QUIC, a new transport protocol that combines aspects of TCP and TLS. It summarizes what QUIC is, how widely it has been adopted, and why the author finds it interesting. QUIC merges TCP and TLS to provide encrypted connections with faster setup times than TCP and support for features like streams and multipath. While some browsers support QUIC, actual usage remains lower than expected. The author measures QUIC usage and discusses factors like server configurations and national filtering that may impact adoption. He concludes QUIC is important because it is fast, encrypts all communication, and gives applications more control over transport.