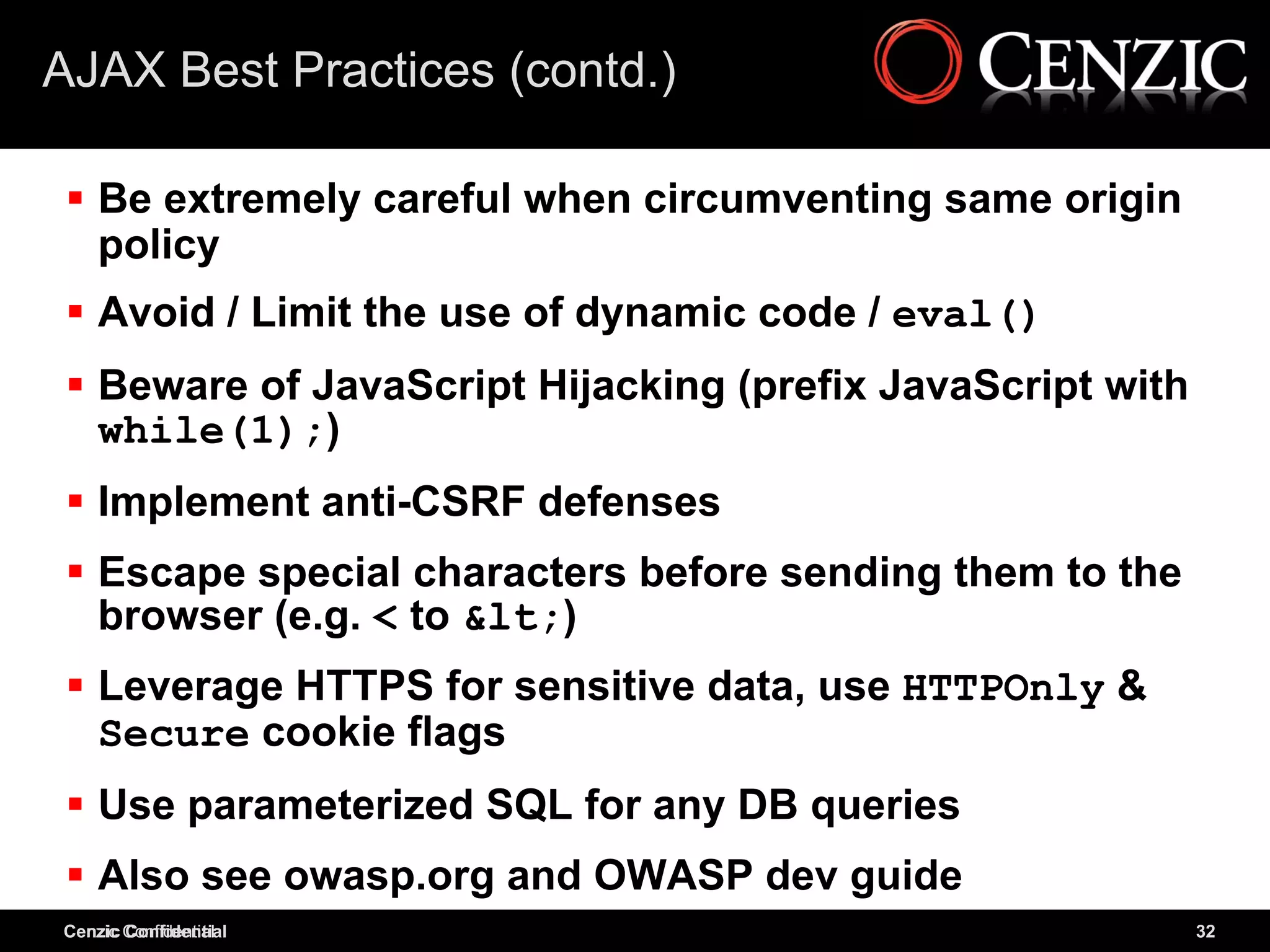
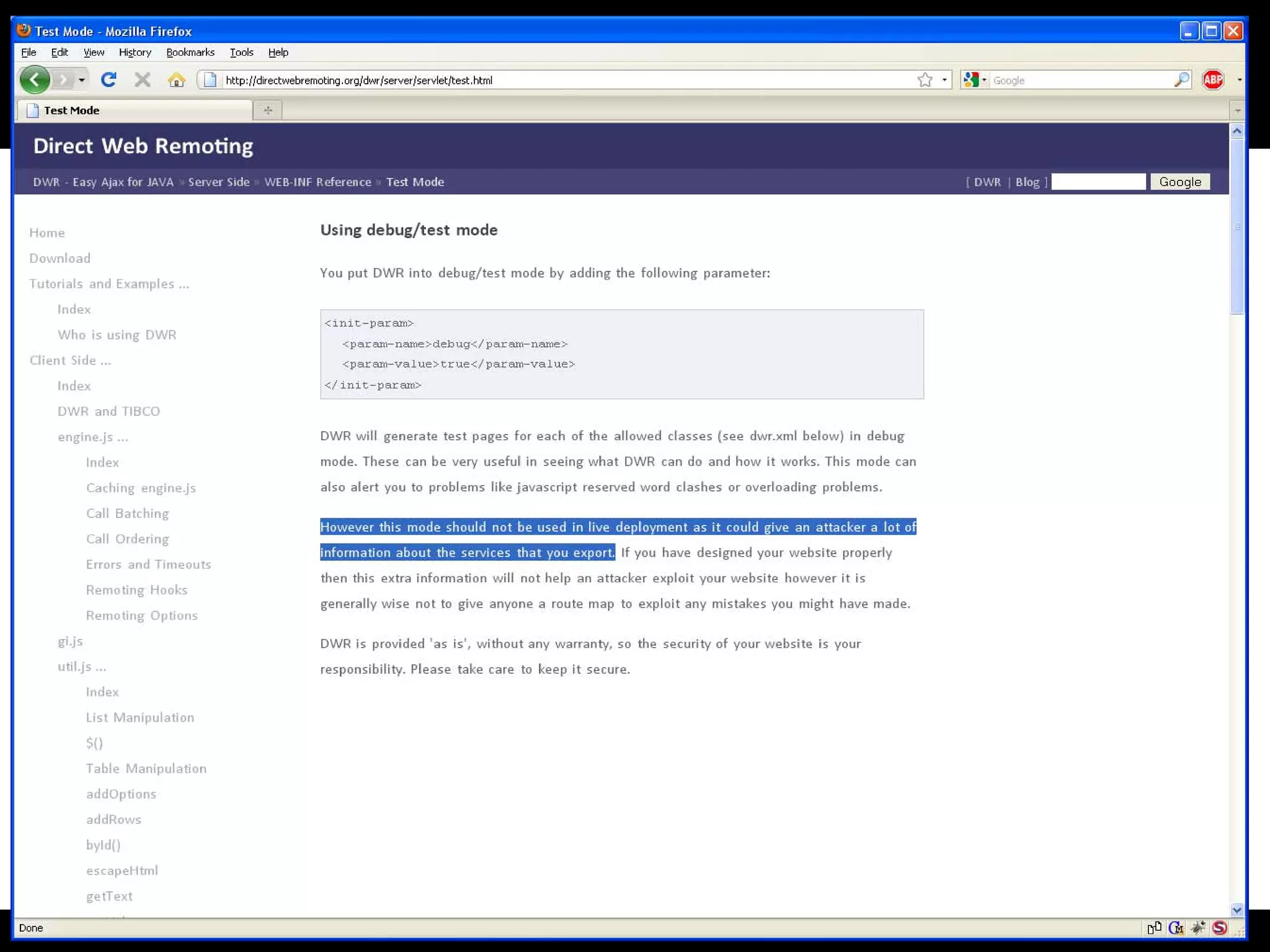
The document discusses AJAX as a method for creating dynamic web applications, highlighting its interaction with the same-origin policy, security vulnerabilities, and automation challenges. It outlines various security risks associated with AJAX, such as Cross-Site Scripting (XSS), SQL Injection, and JavaScript hijacking, along with best practices for mitigating these risks. The presentation also emphasizes the importance of strong server-side validation and caution against relying solely on client-side security measures.
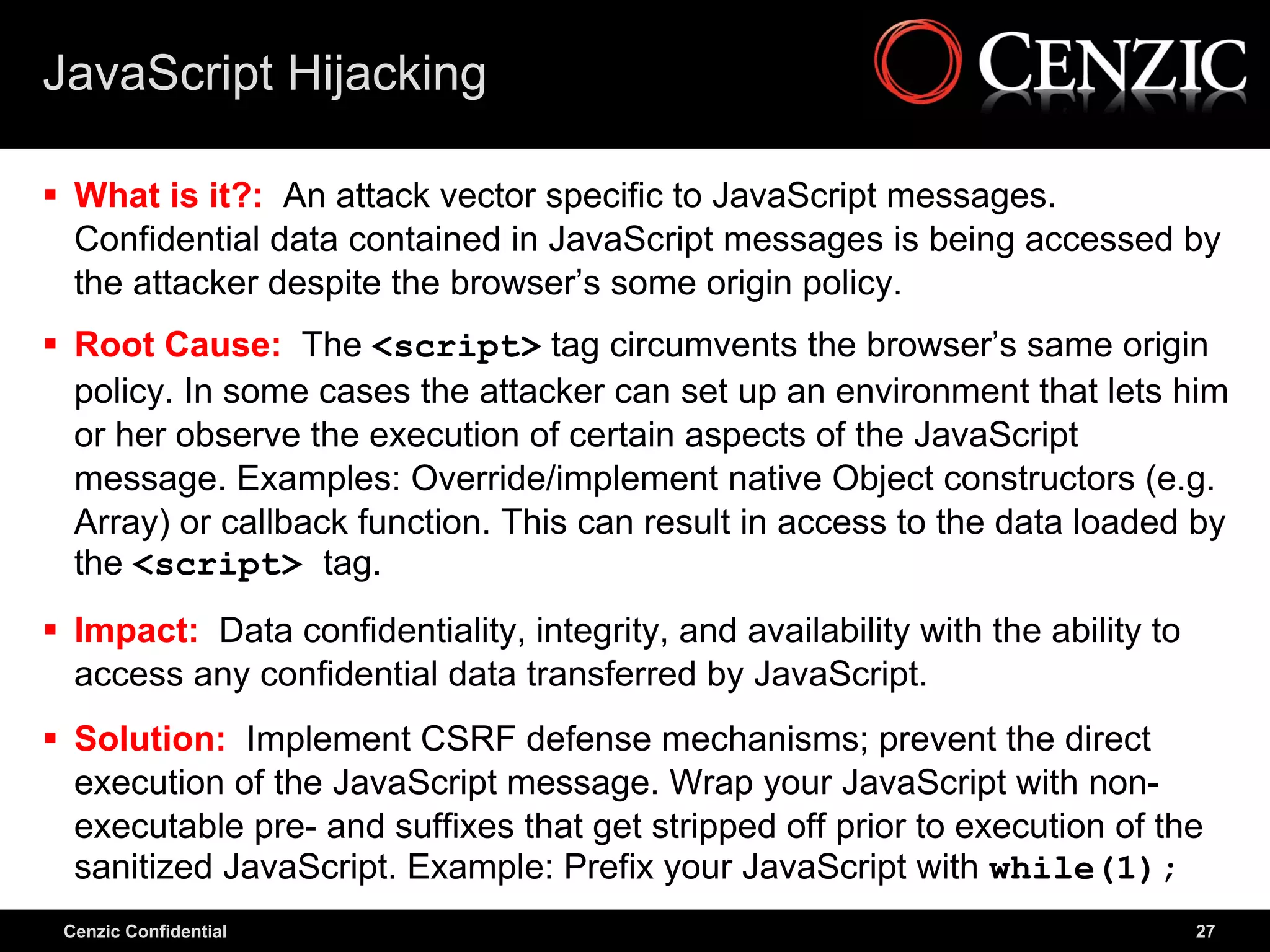
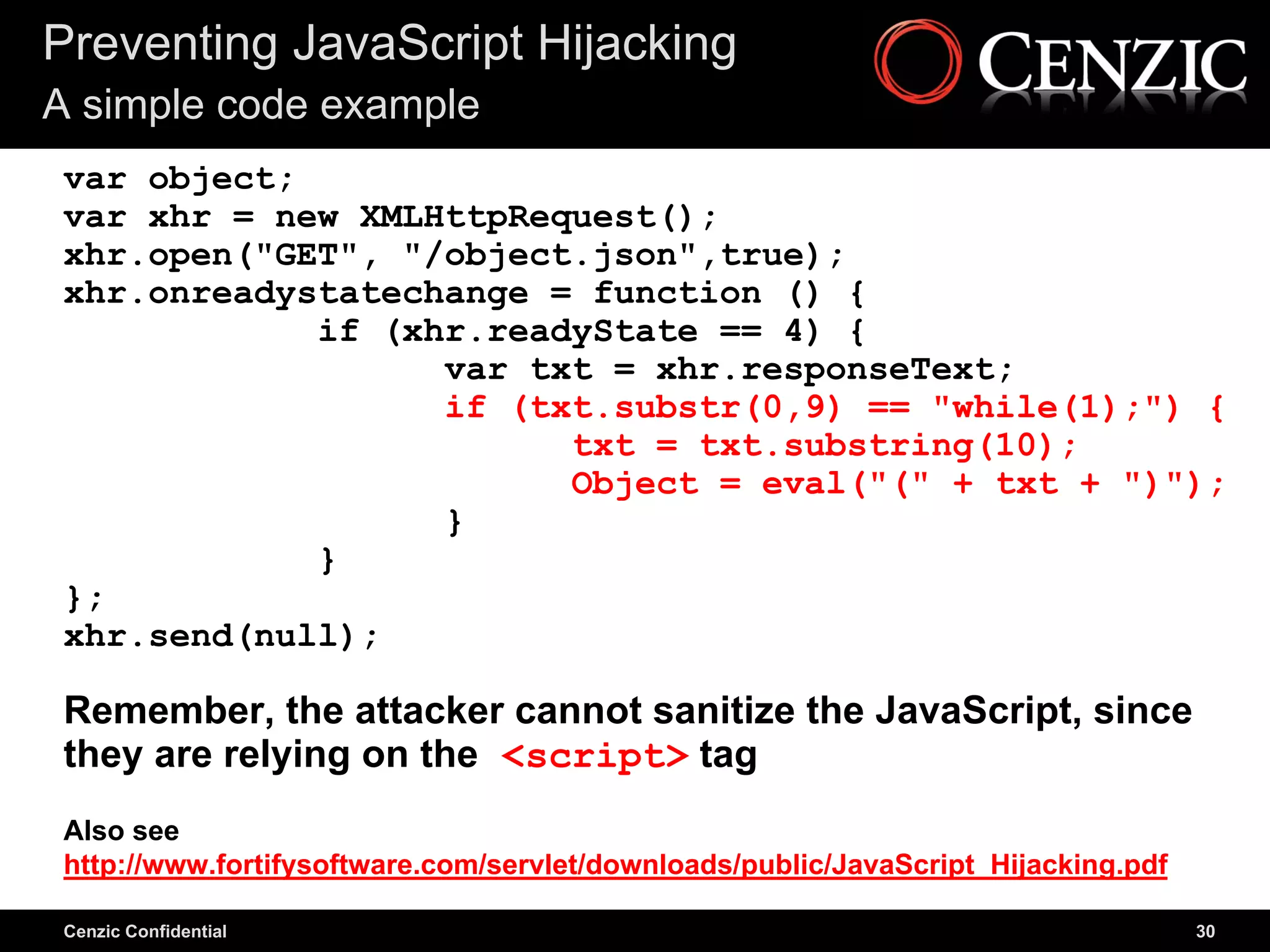
![JavaScript Hijacking Examples
Example #1: Override Array Constructor
Attacker code (override Array constructor)
<script>
function Array(){
/* Put hack to access Array elements here */
}
</script>
AJAX Call
<script src="http://put_AJAX_call_here"
type="text/javascript"></script>
Example AJAX response
["foo1","bar1"],["foo2","bar2"]
Cenzic Confidential 28](https://image.slidesharecdn.com/ajaxsecuritysans-100816170712-phpapp02/75/AJAX-How-to-Divert-Threats-28-2048.jpg)
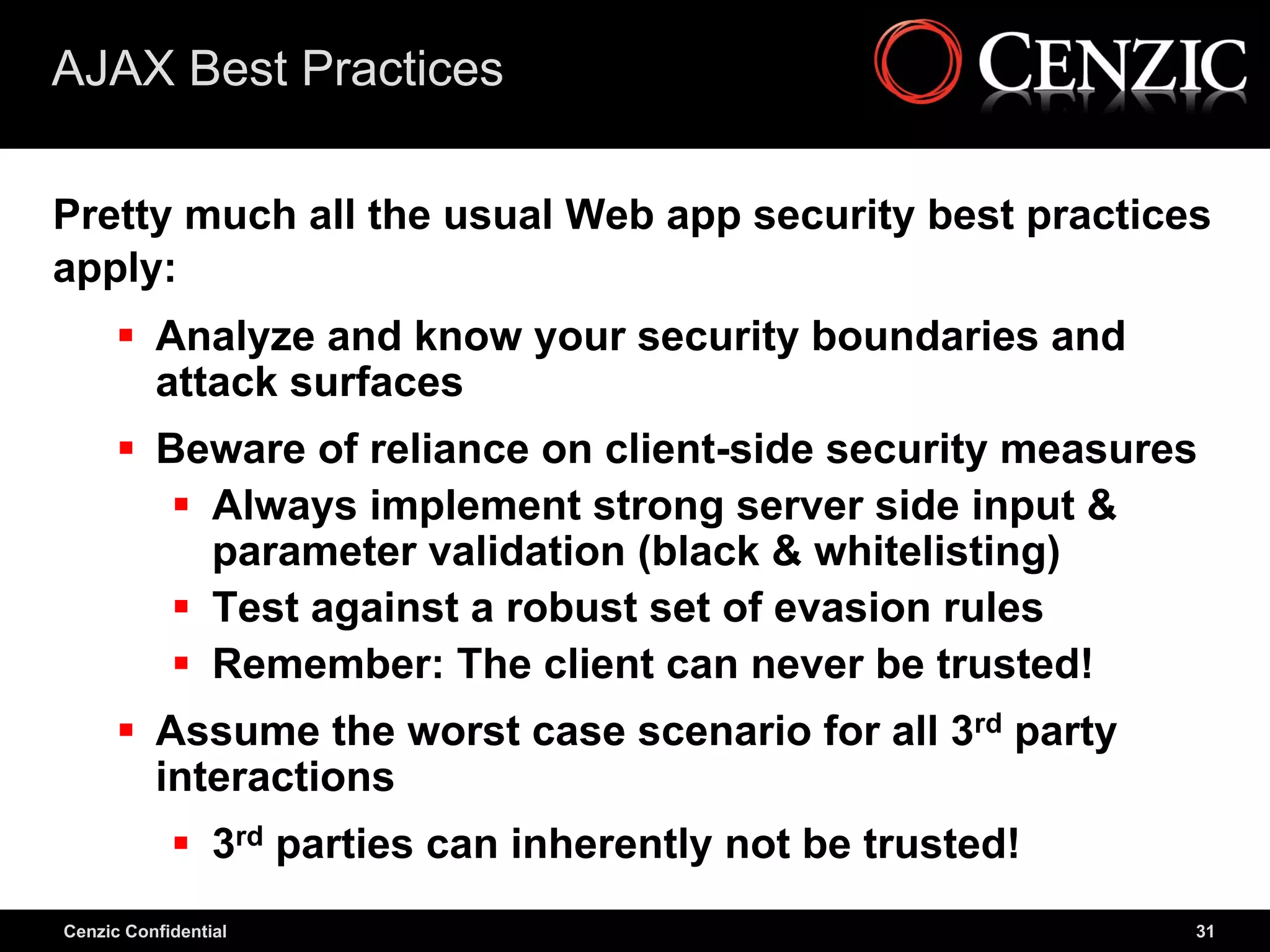
![JavaScript Hijacking Examples
Example #2: Implement Callback
Attacker code (implement callback)
<script>
function callback(foo){
/* Put hack to access callback data here */
}
</script>
AJAX Call
<script src="http://put_AJAX_call_here"
type="text/javascript"></script>
Example AJAX response
callback(["foo","bar"]);
Cenzic Confidential 29](https://image.slidesharecdn.com/ajaxsecuritysans-100816170712-phpapp02/75/AJAX-How-to-Divert-Threats-29-2048.jpg)