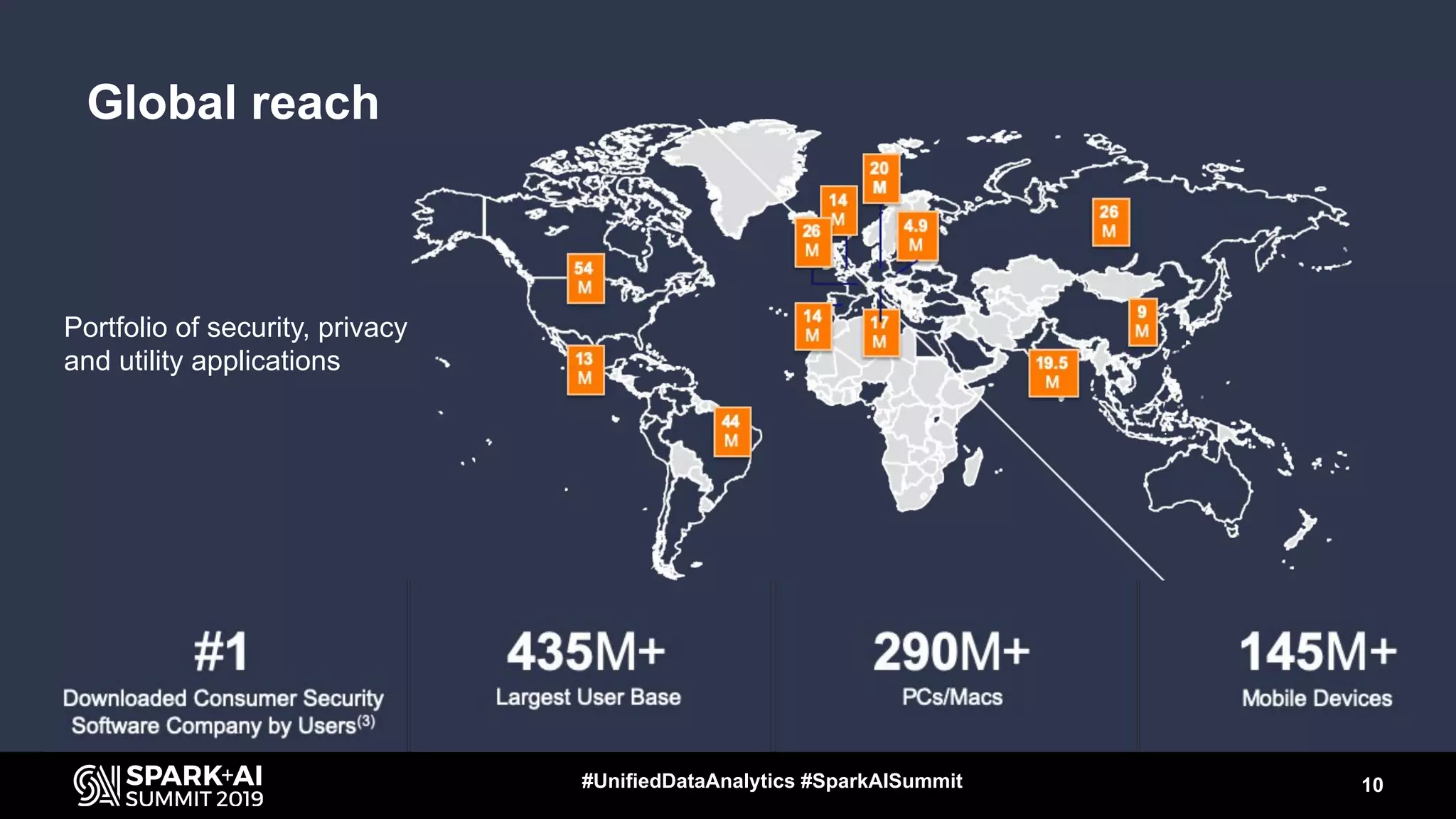
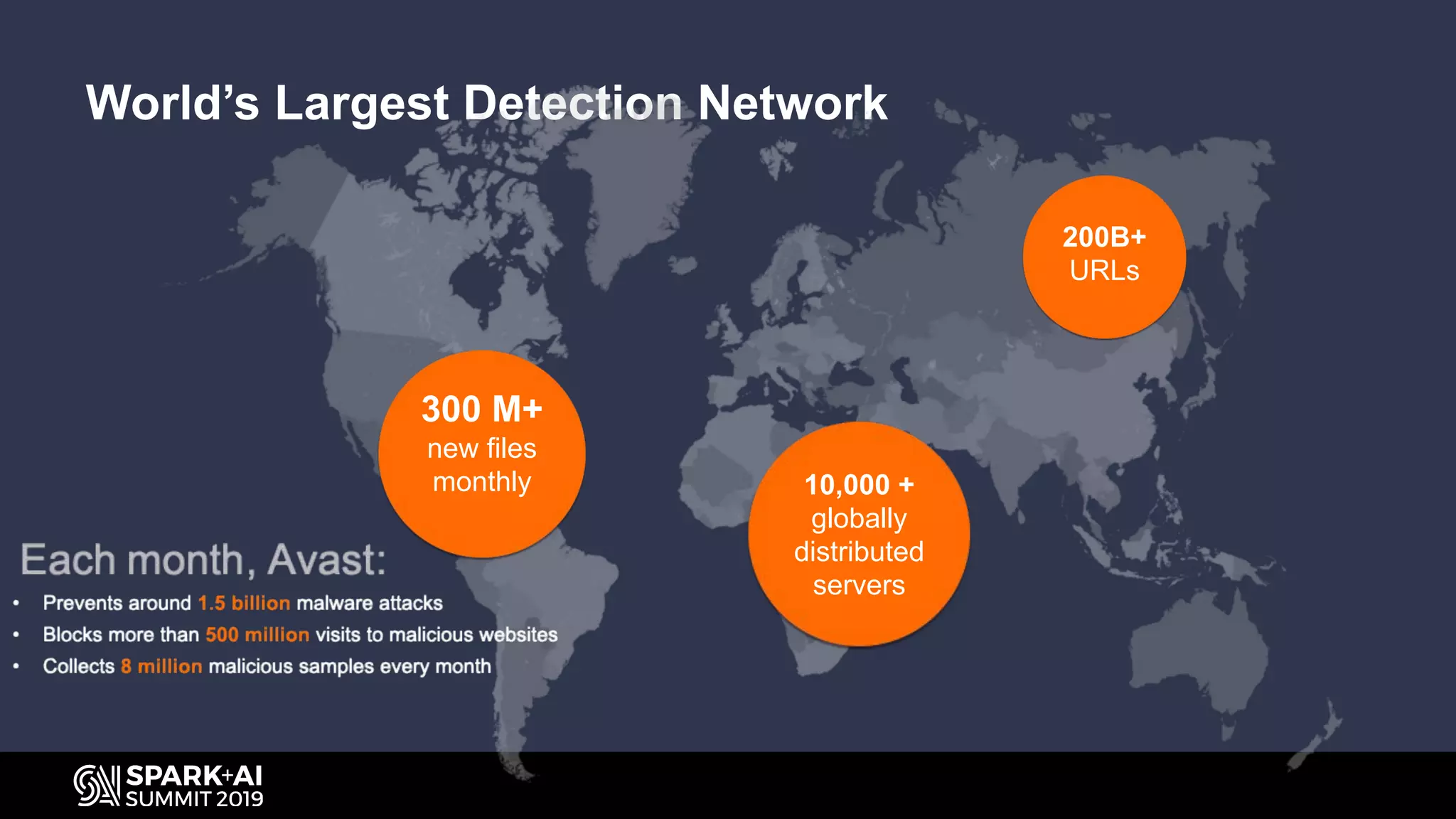
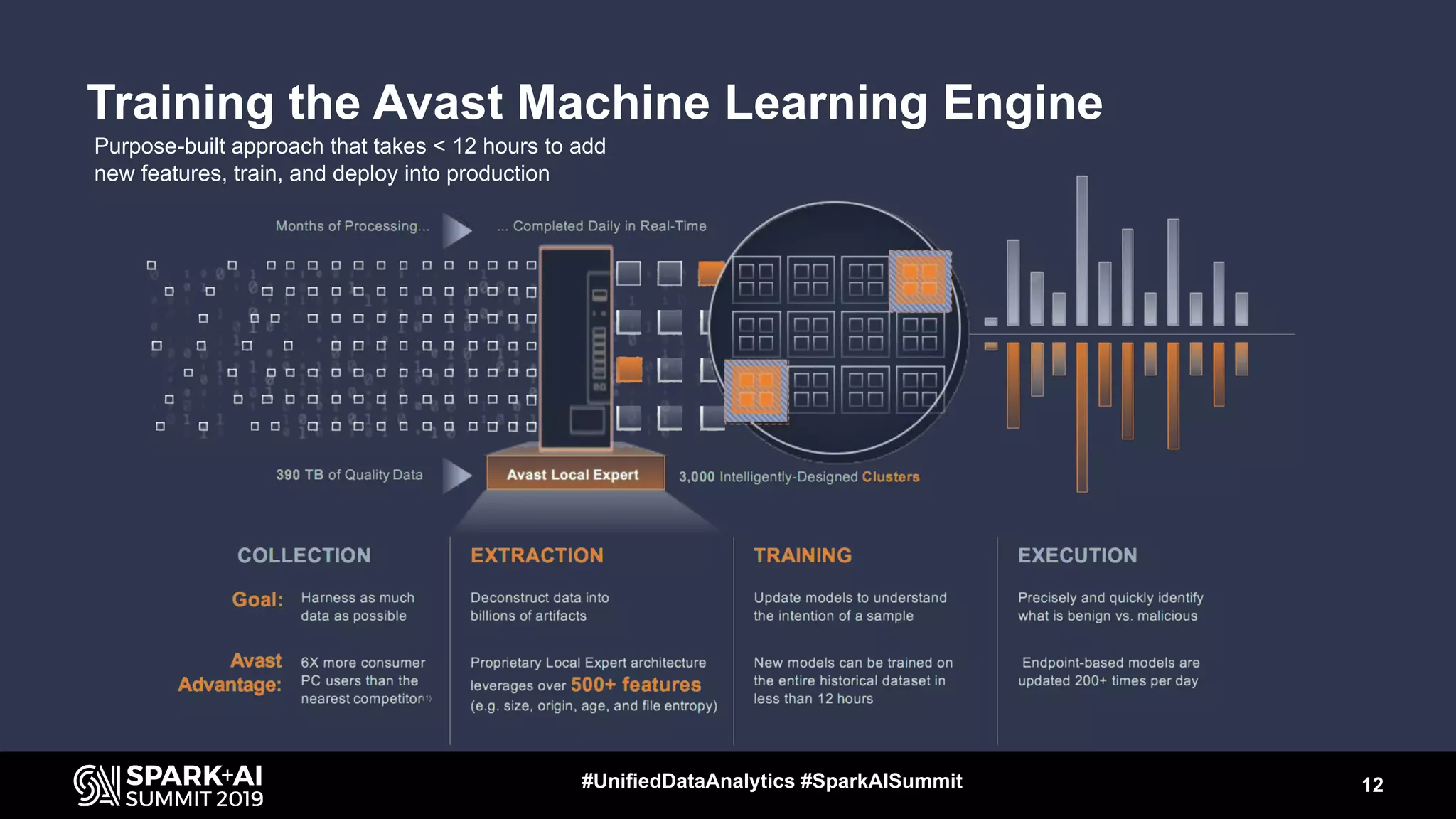
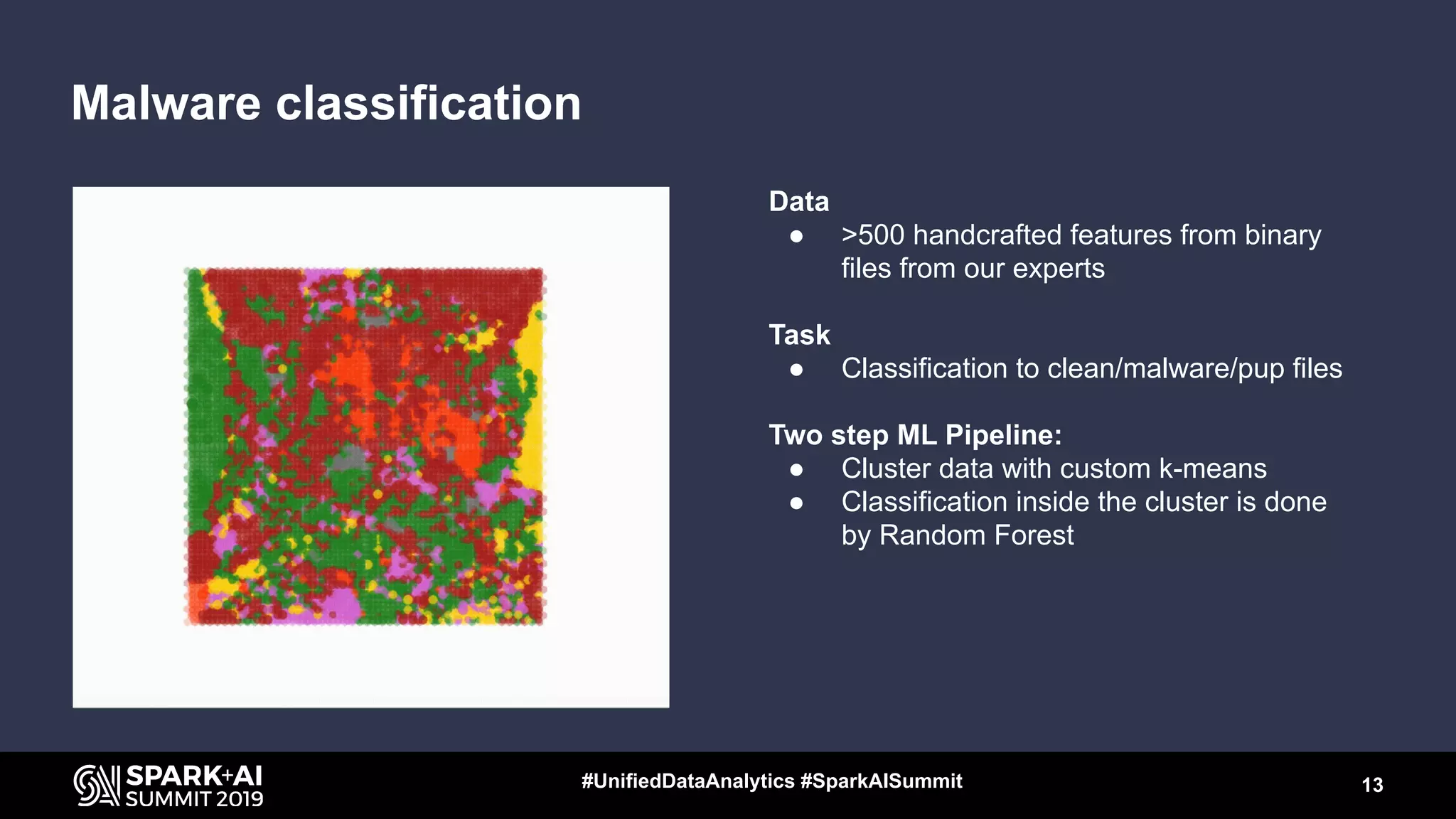
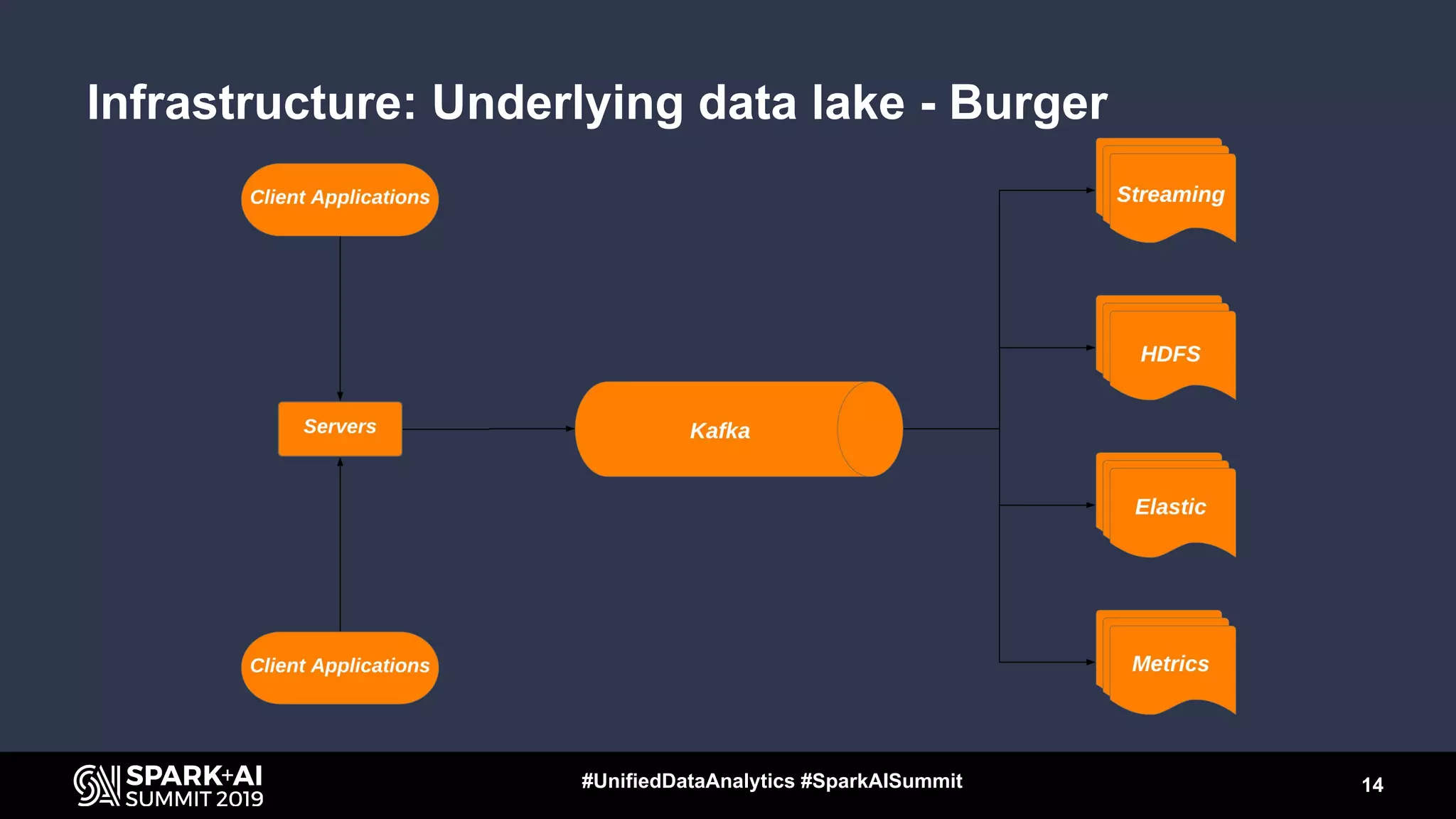
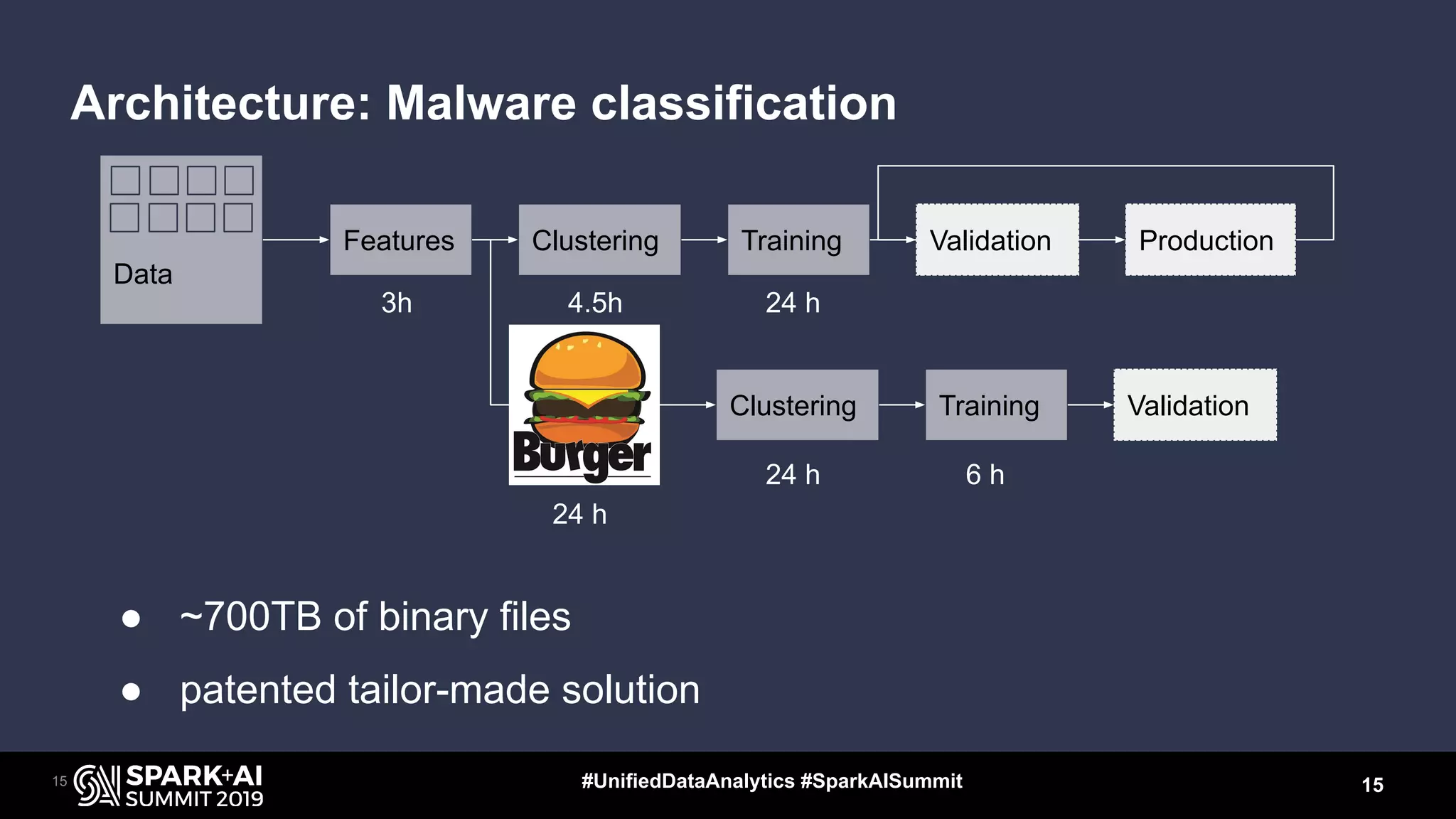
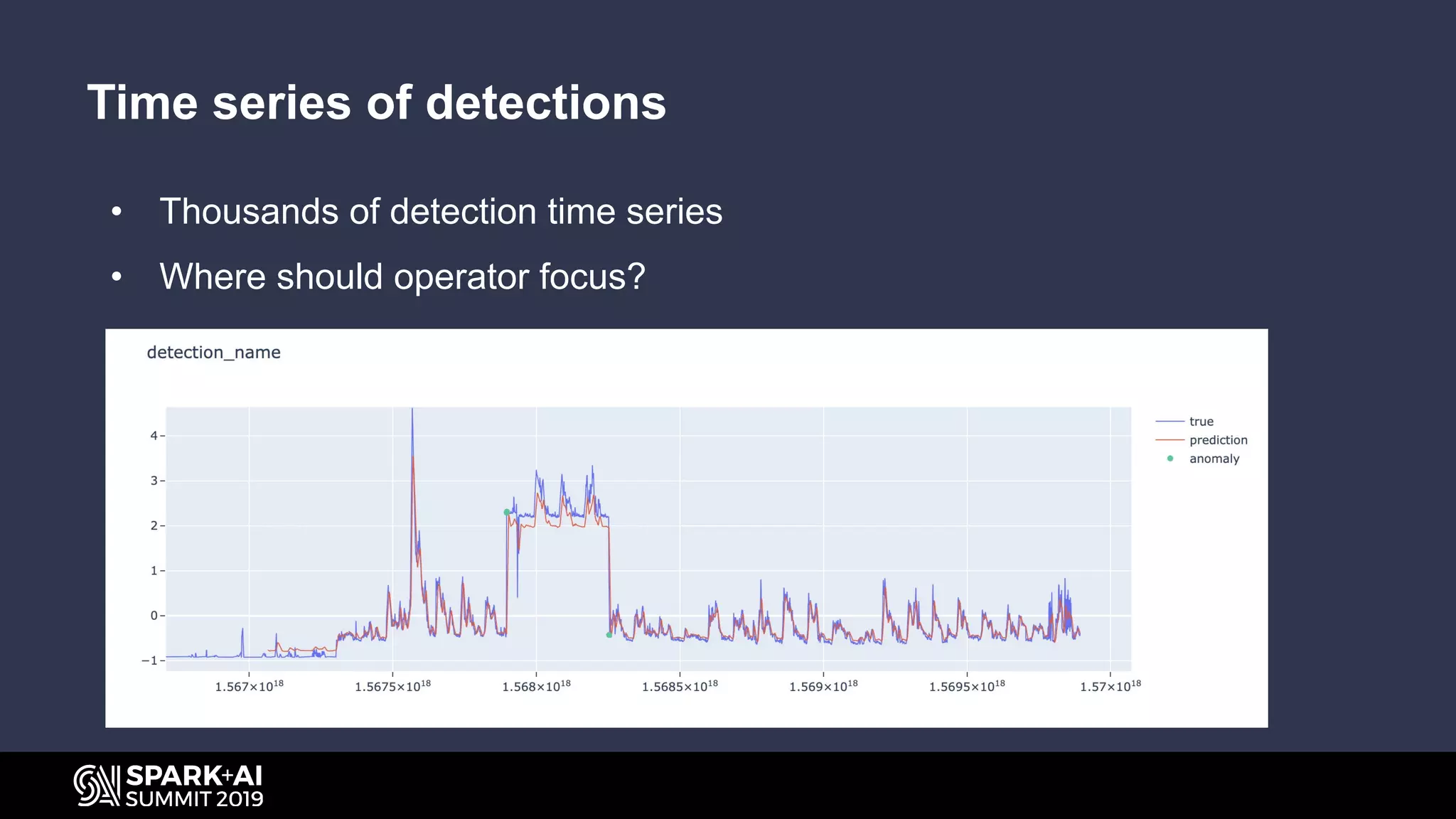
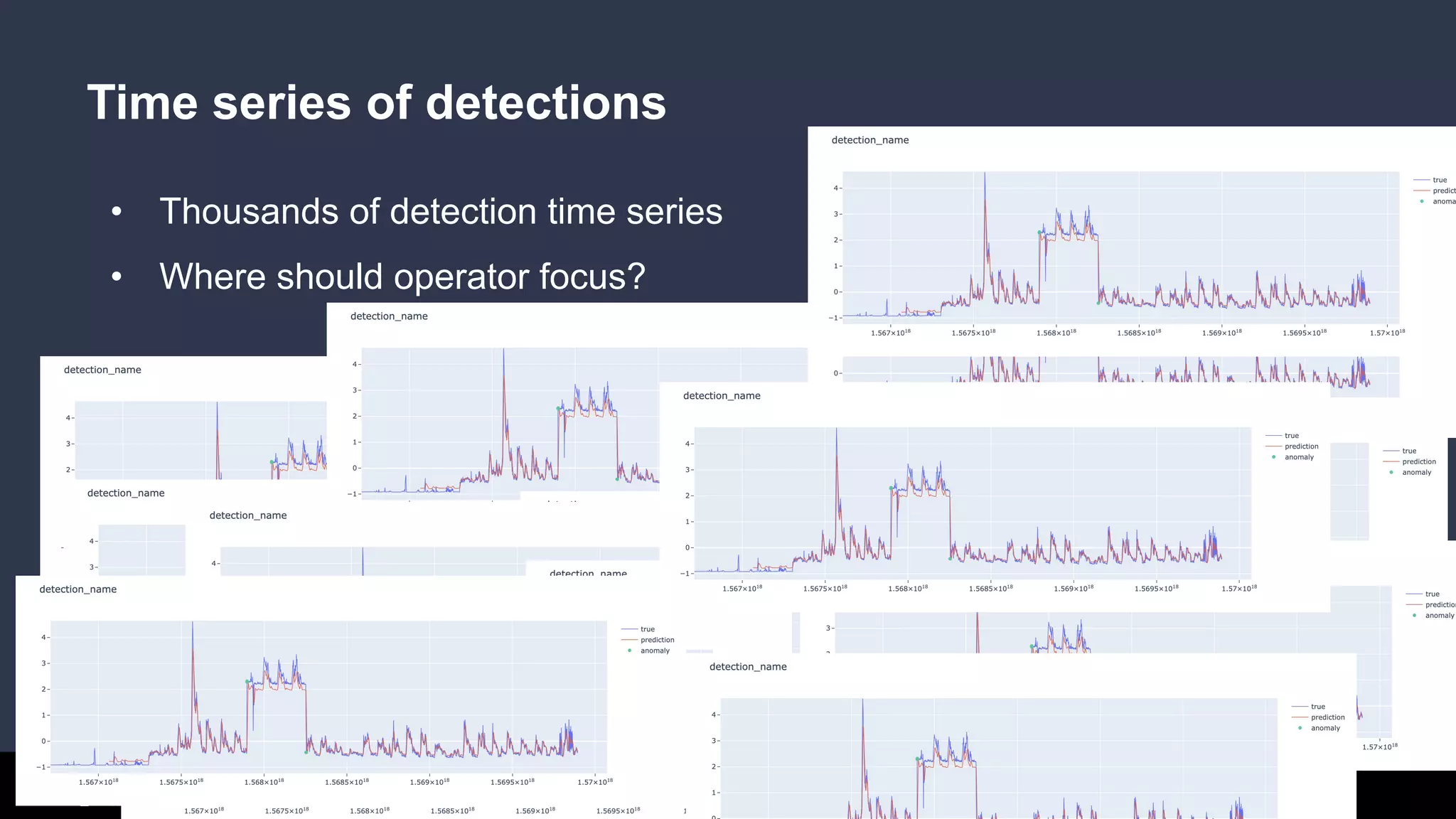
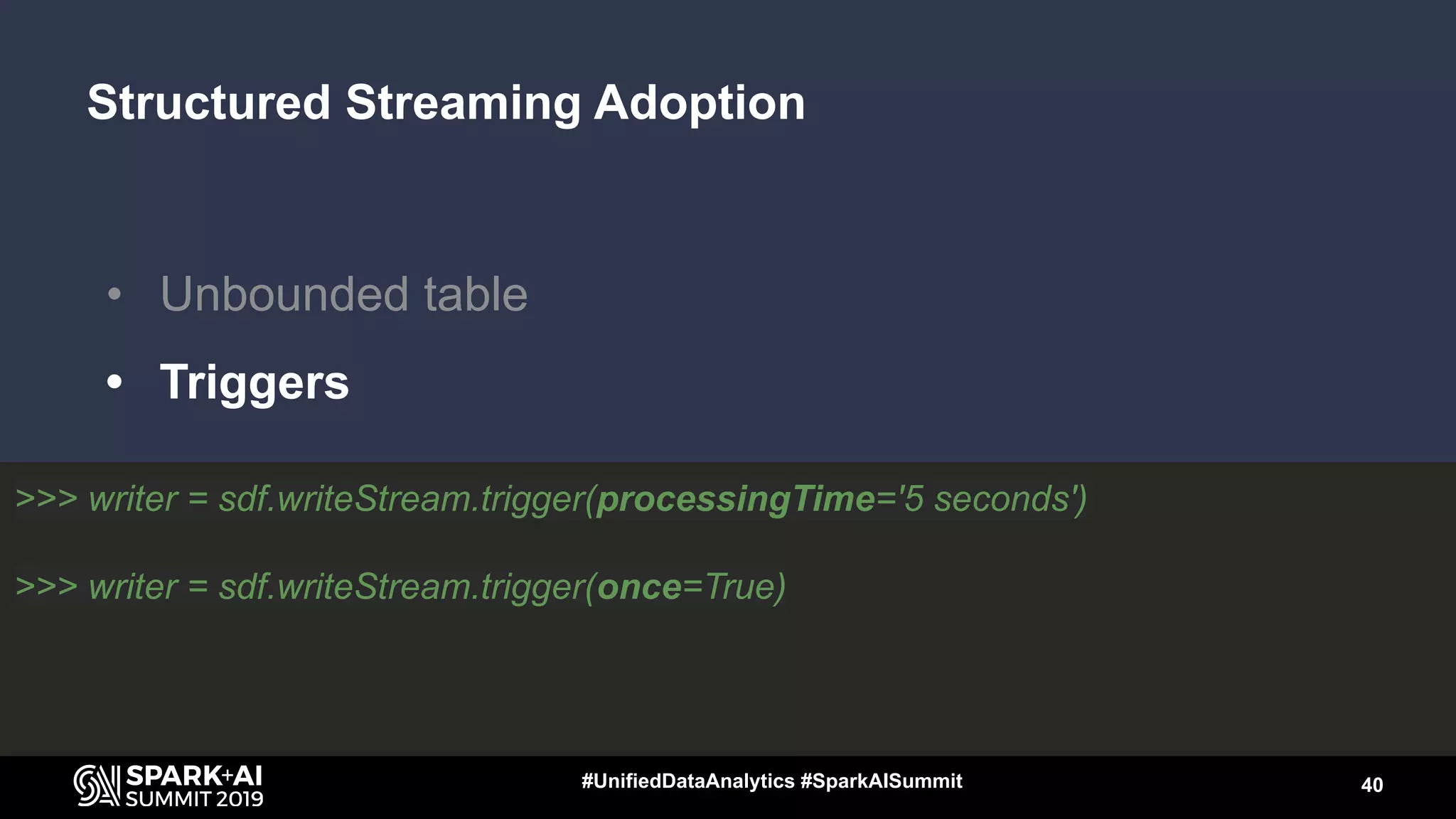
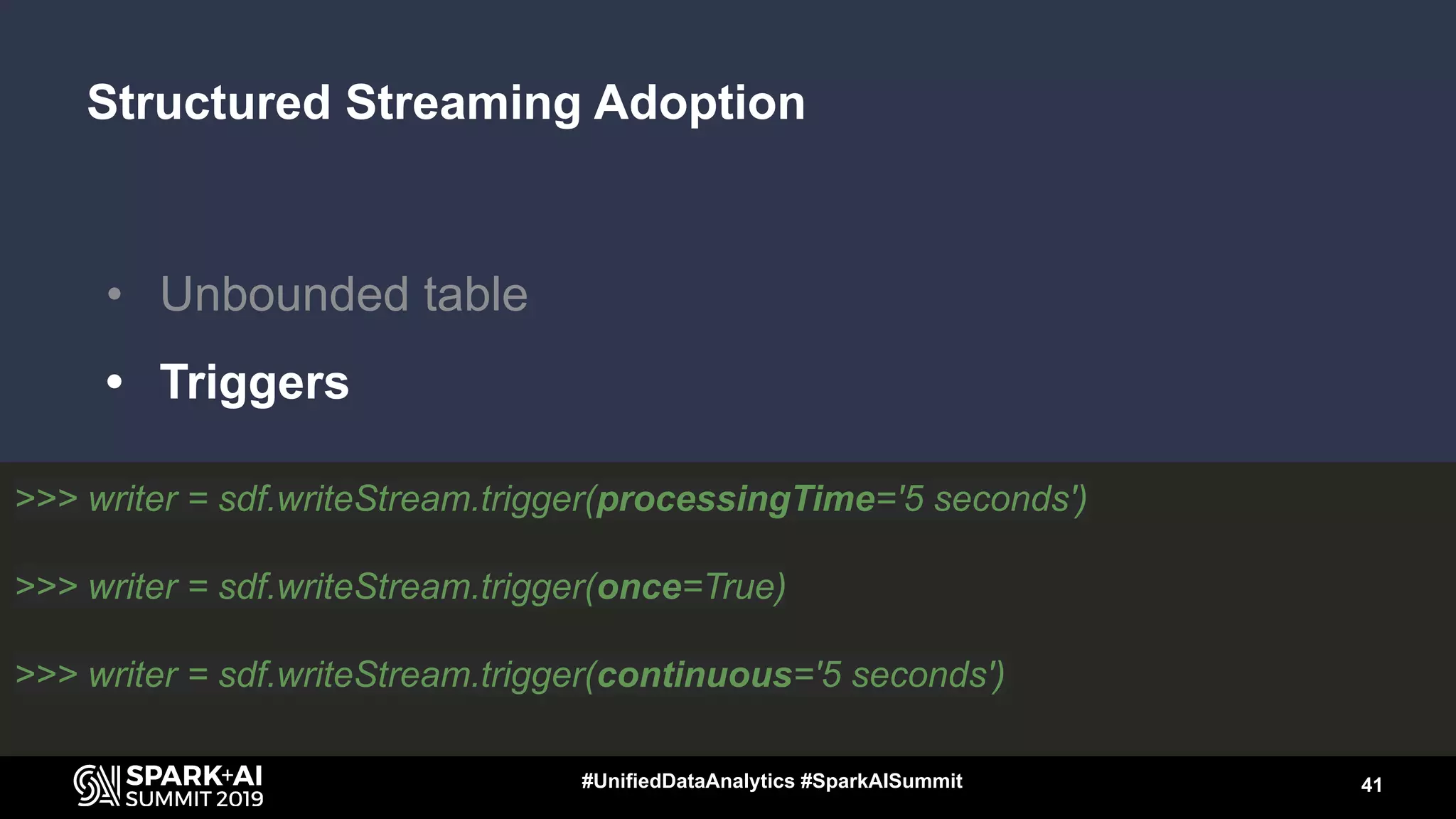
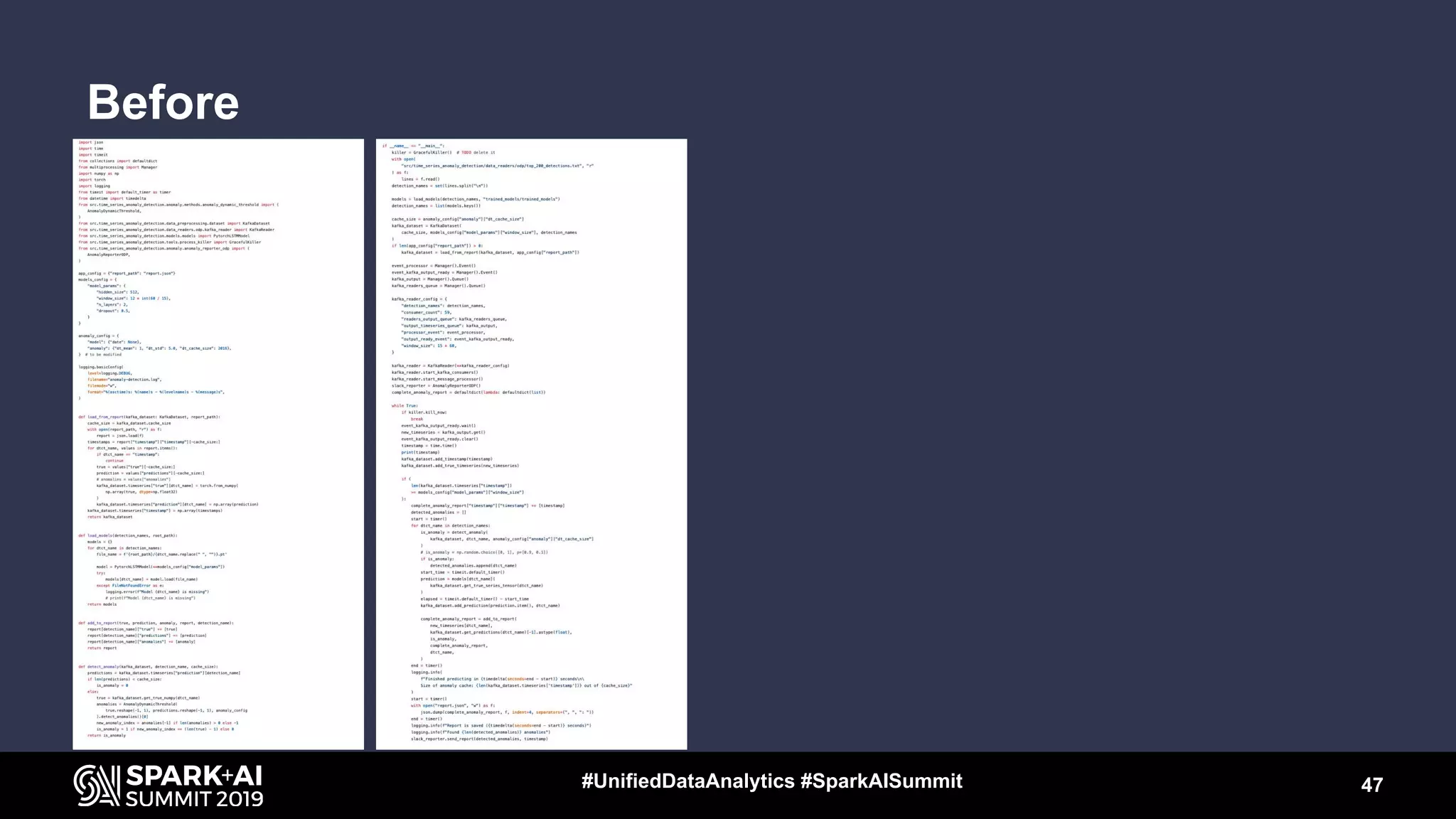
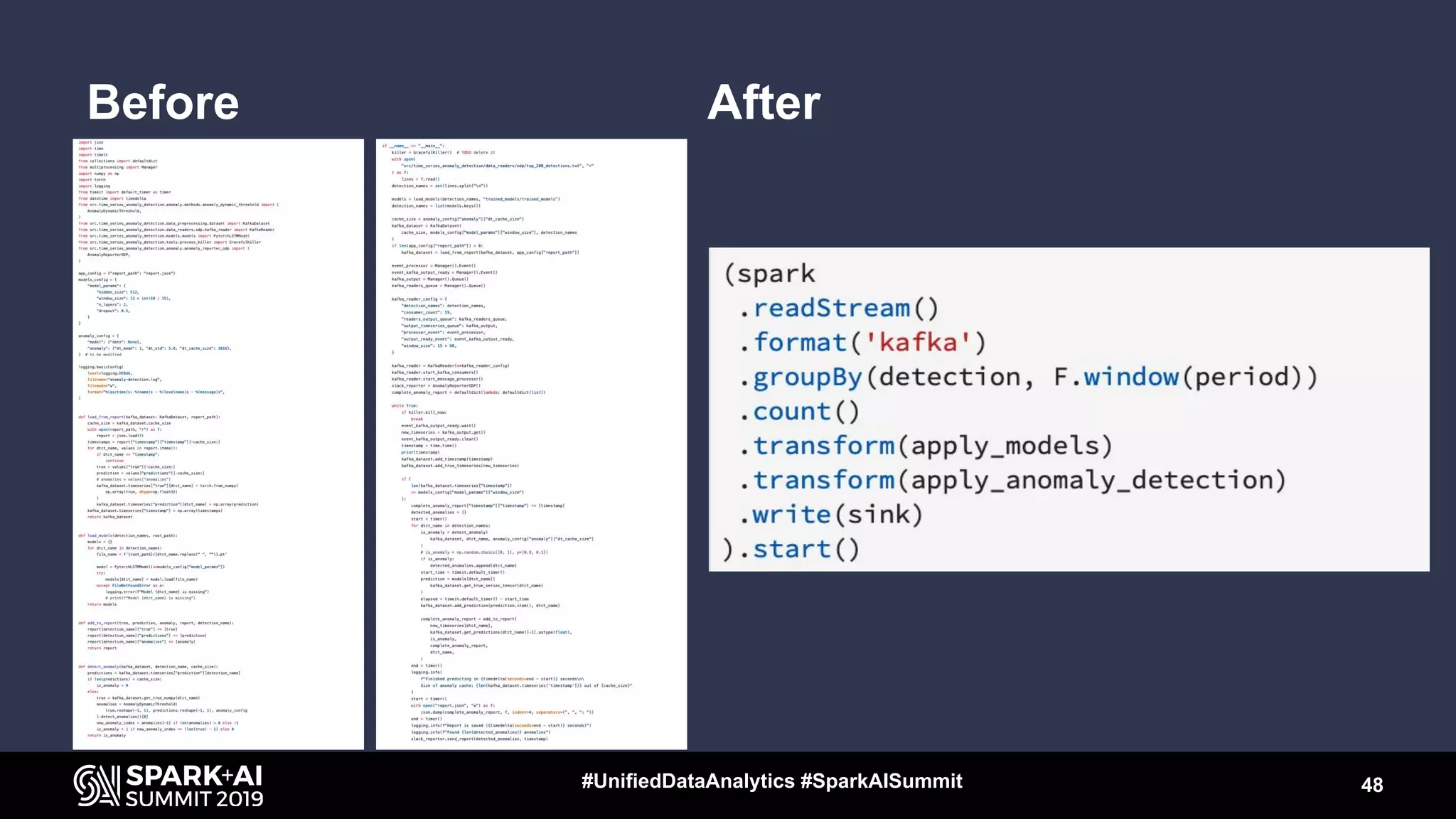
The document presents an overview of how Avast employs AI and big data for malware analysis and threat detection, highlighting their structured streaming approach for fast threat identification. It details the machine learning pipeline used for malware classification and the advantages of structured streaming in handling large datasets for real-time anomaly detection. The session concludes with insights on collaboration between science and engineering teams and emphasizes the integration of machine learning tools for effective threat analysis.