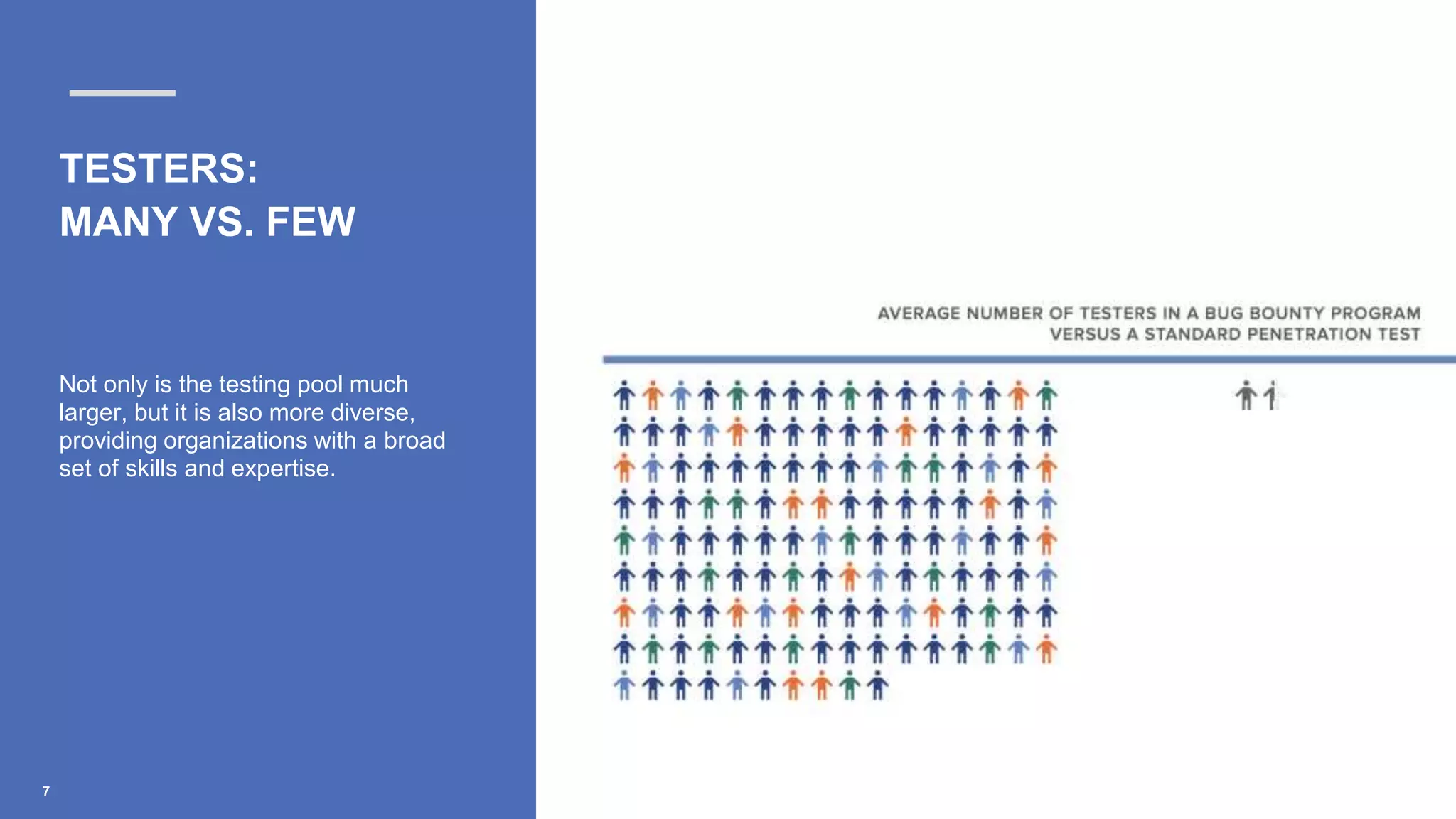
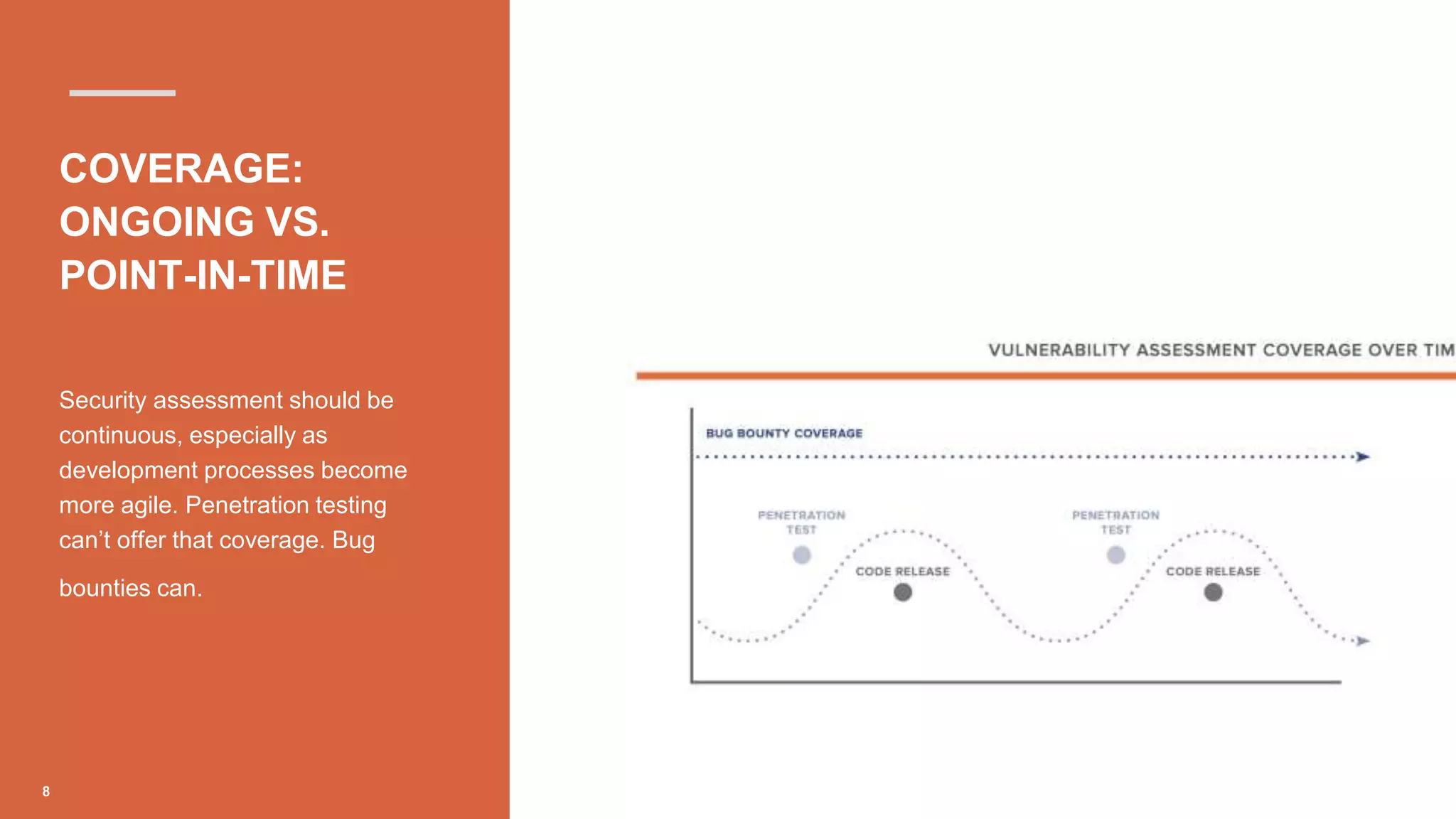
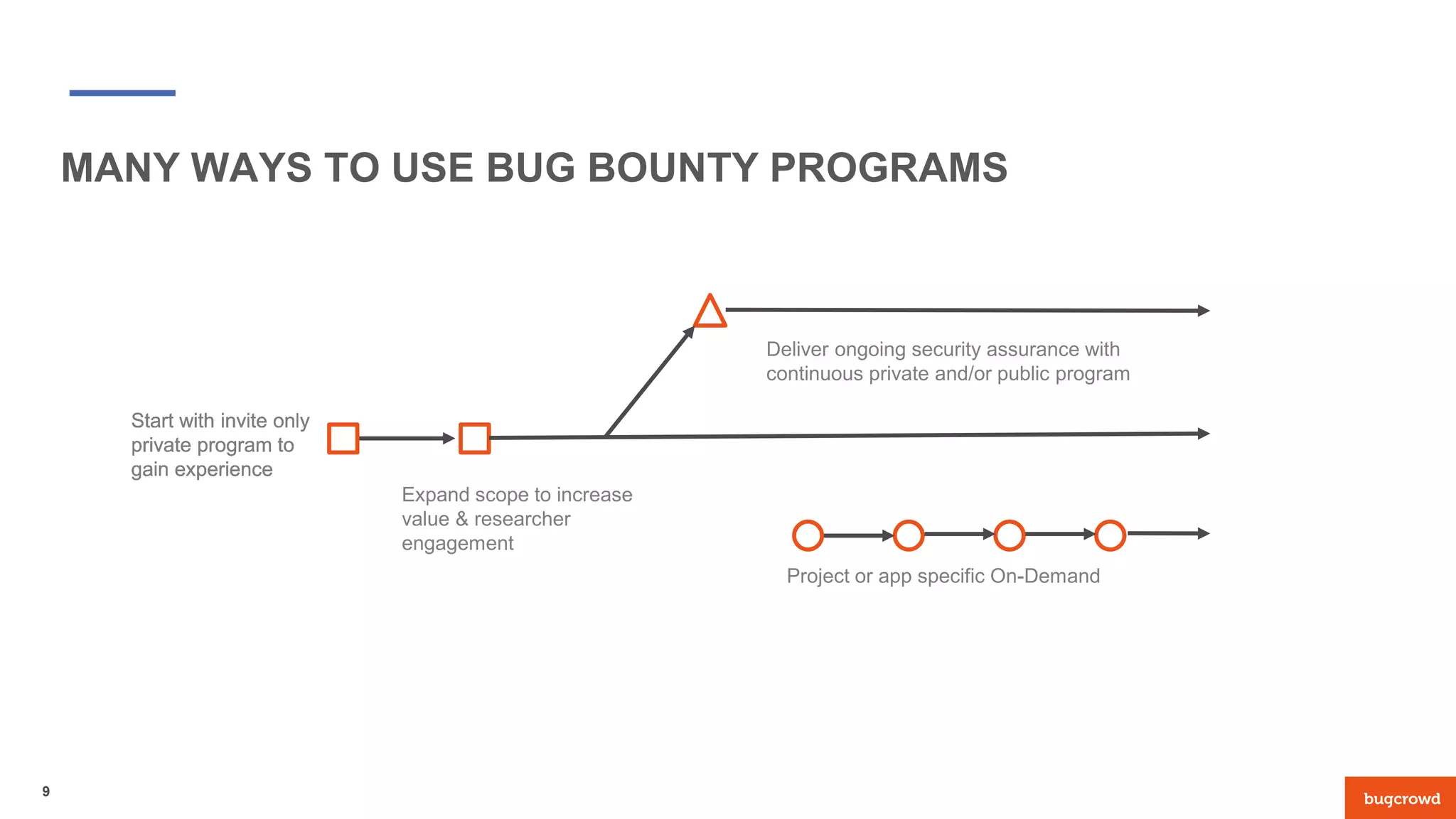
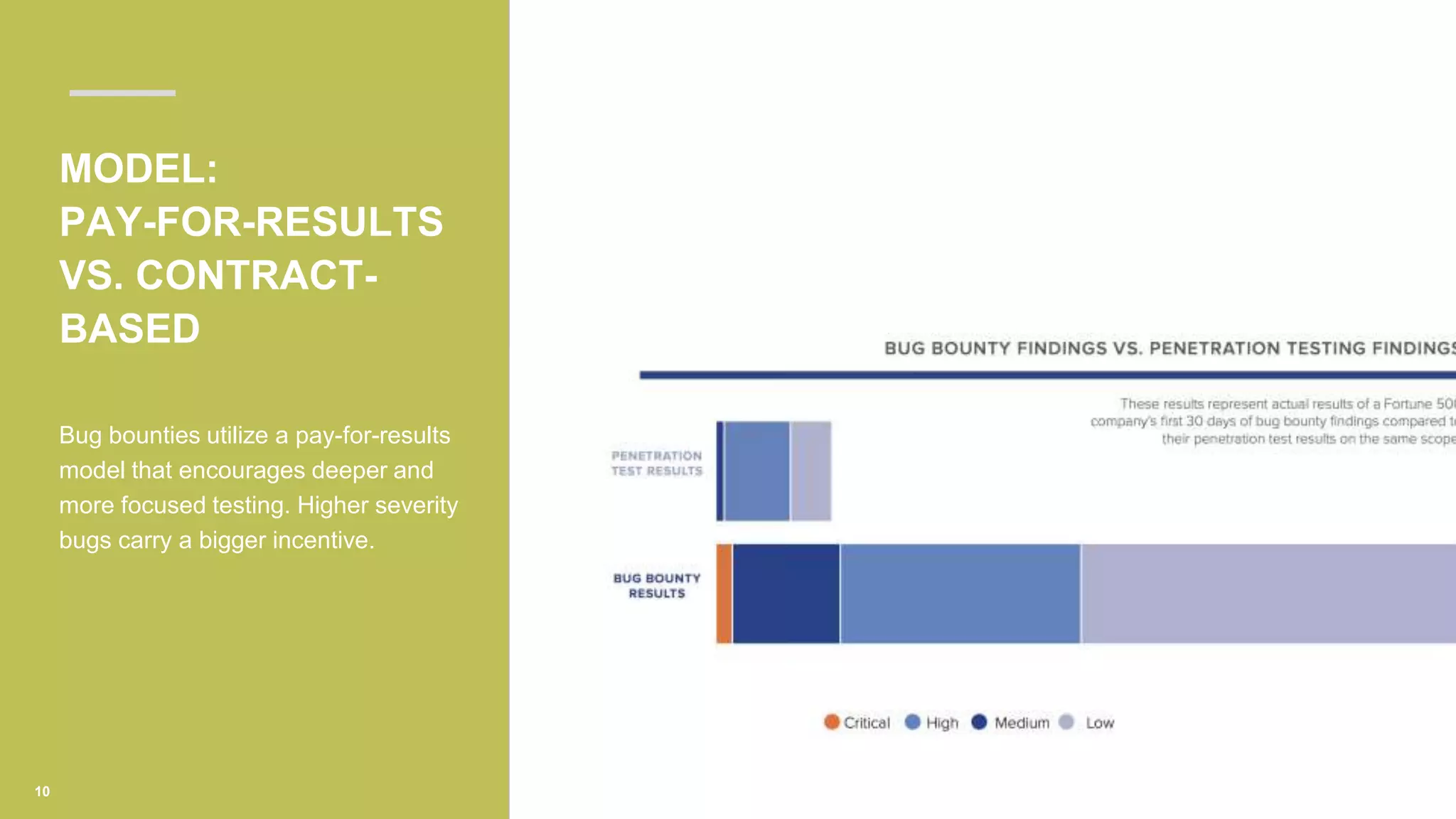
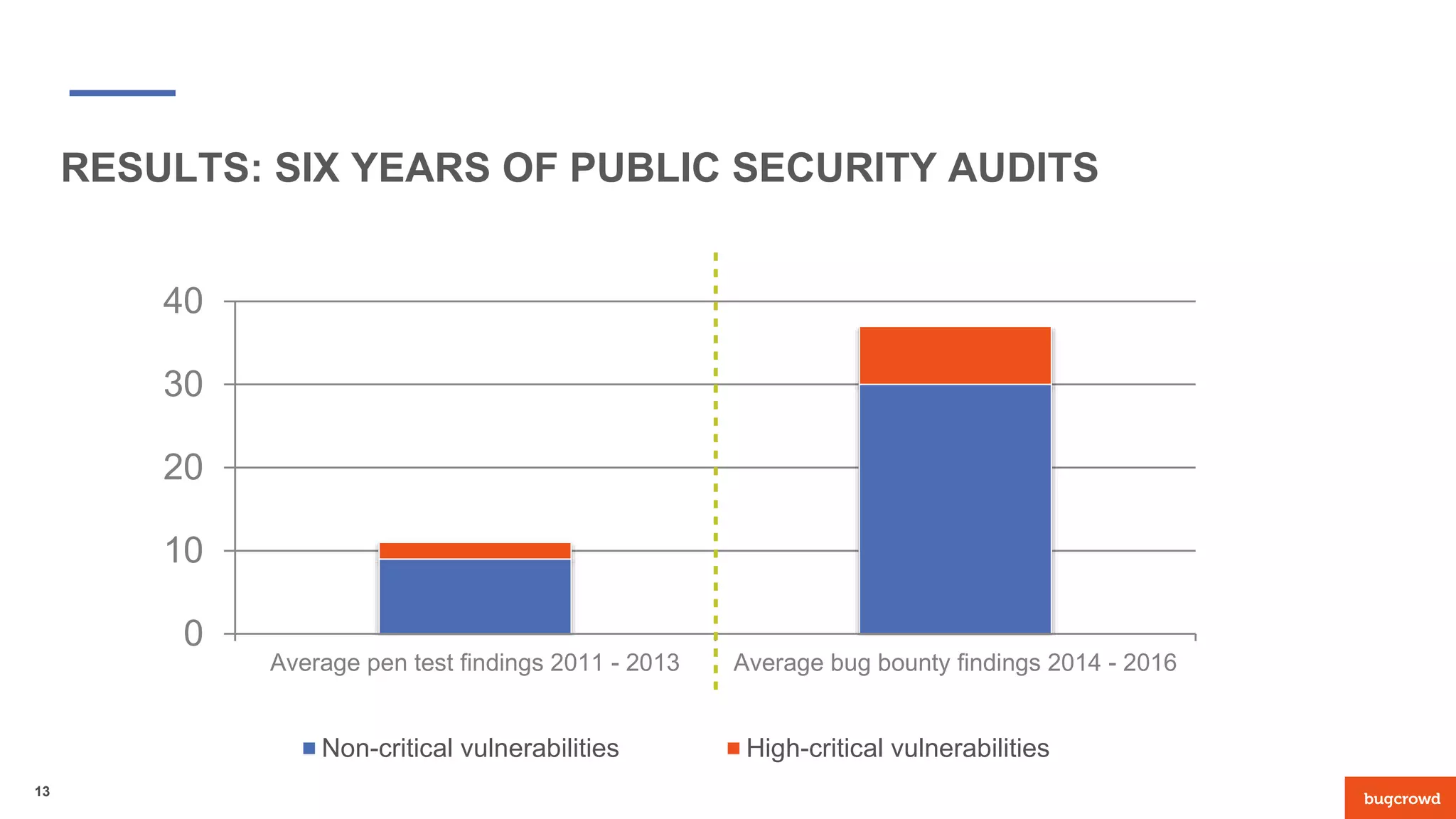
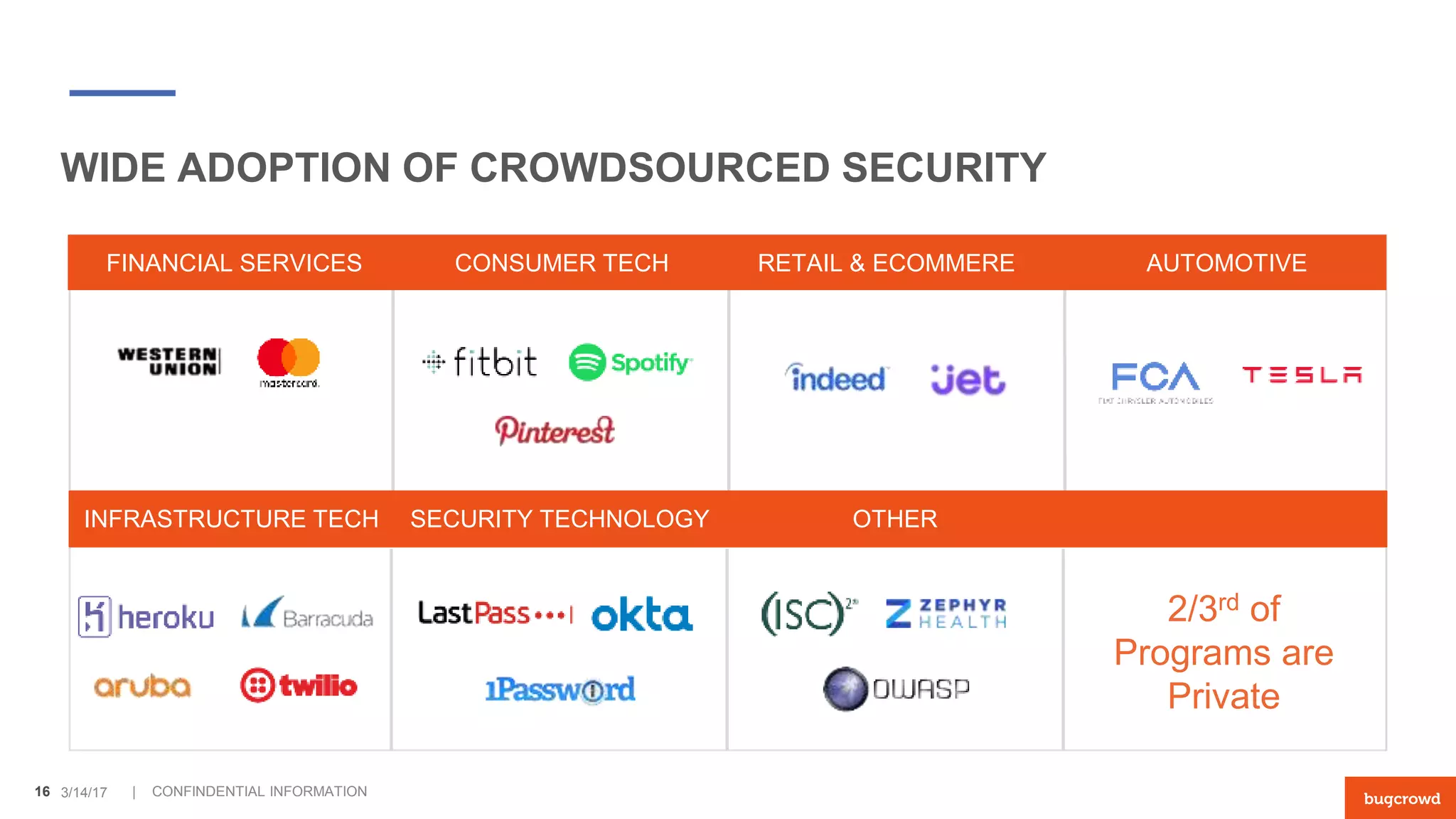
The document discusses the advantages of replacing traditional penetration testing with bug bounty programs, highlighting key differences in testers, coverage, and the payment model. Bug bounty programs involve a larger and more diverse pool of independent researchers for ongoing security assessments, while penetration tests are typically time-limited and fixed-cost. A case study from Canvas illustrates the effectiveness of bug bounties in identifying critical vulnerabilities and the growing trend towards crowdsourced security.