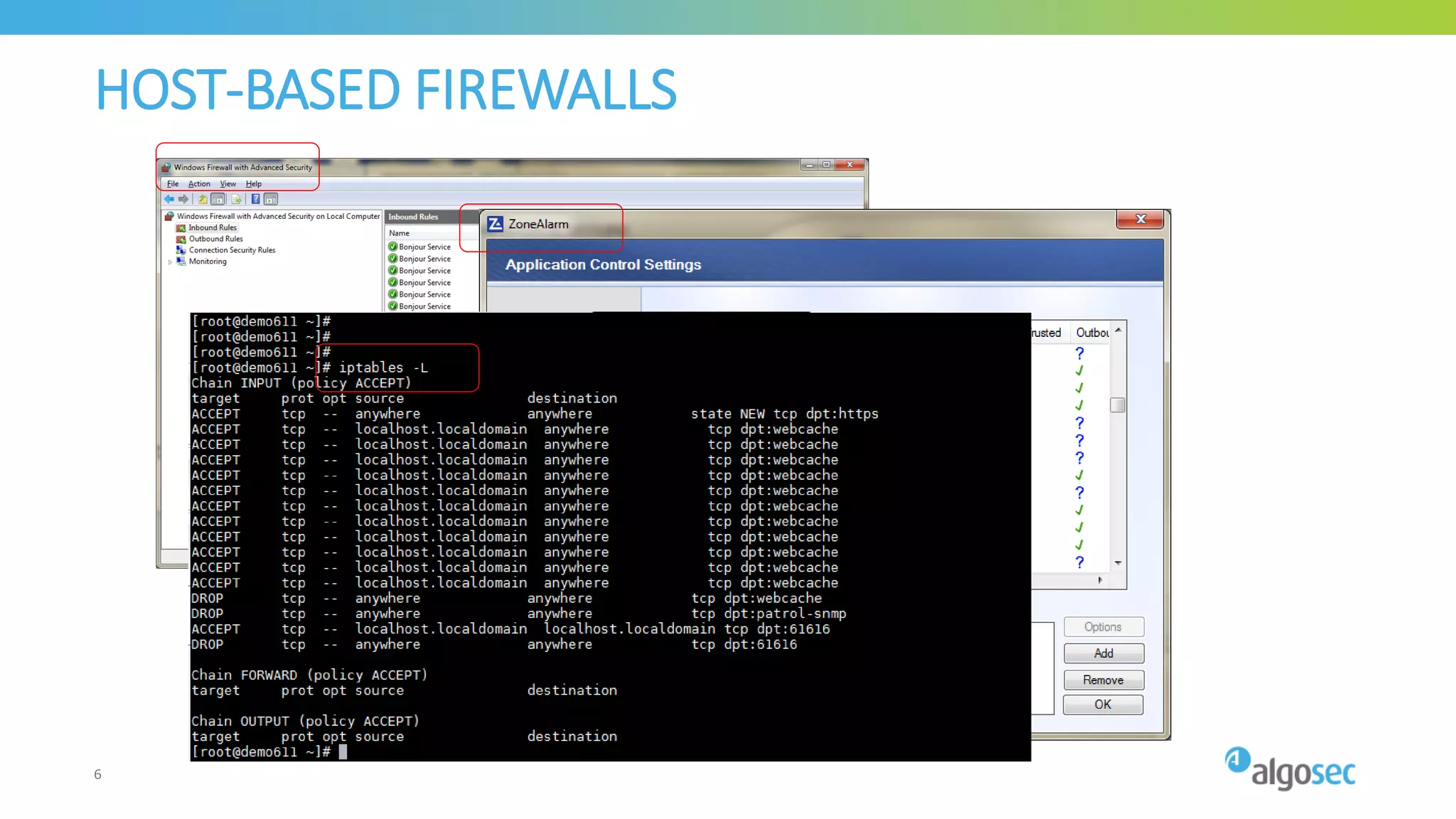
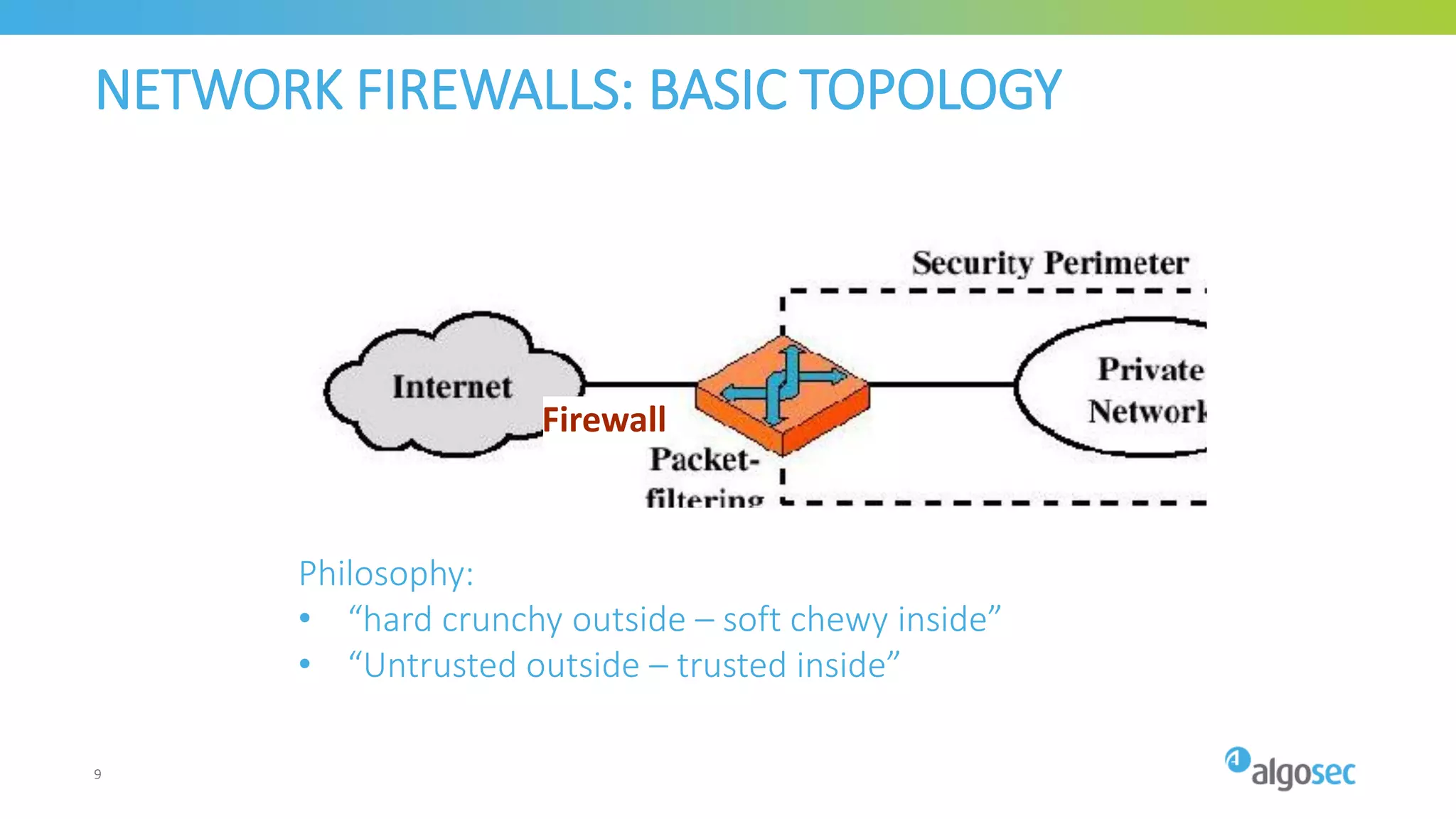
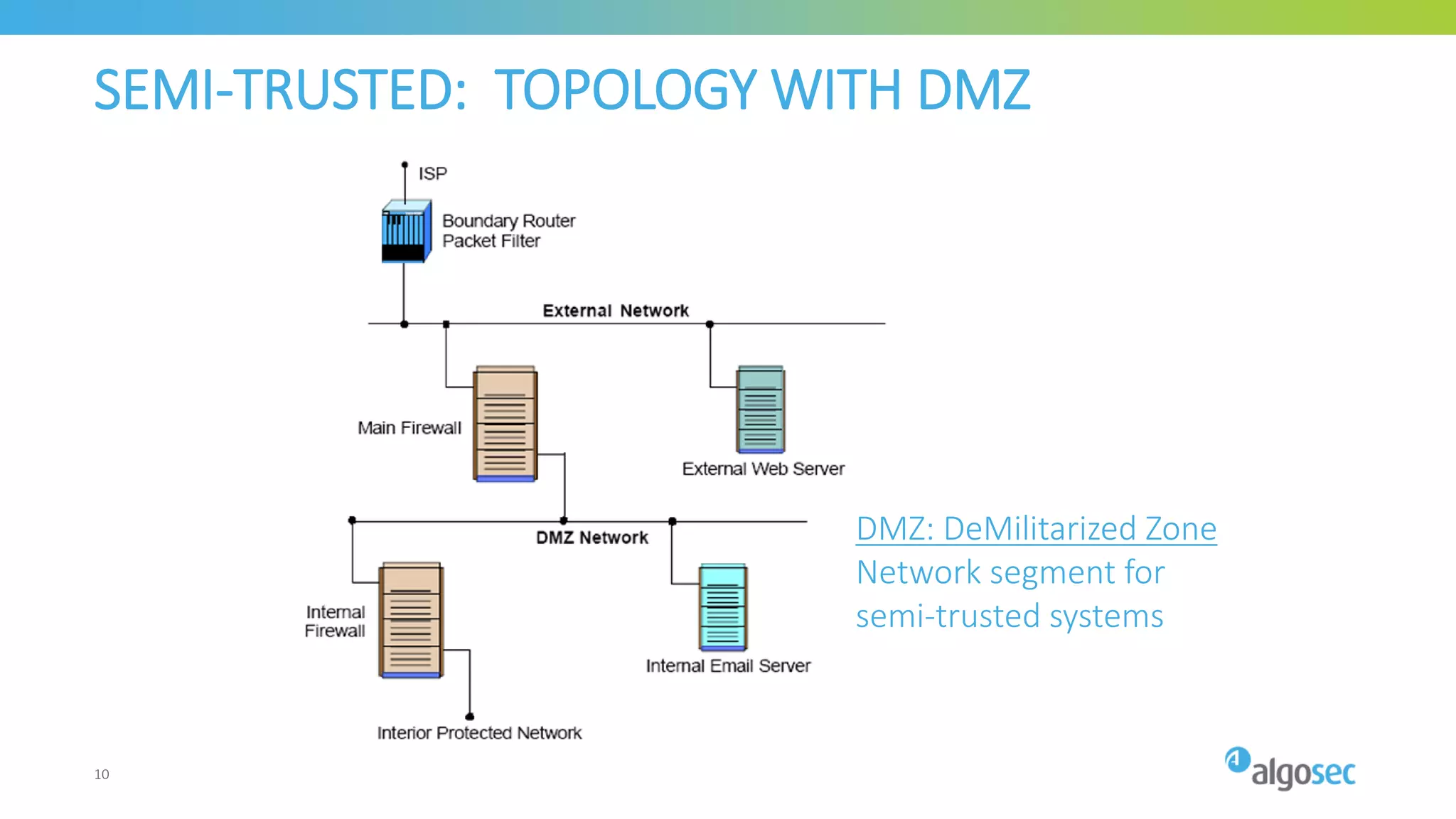
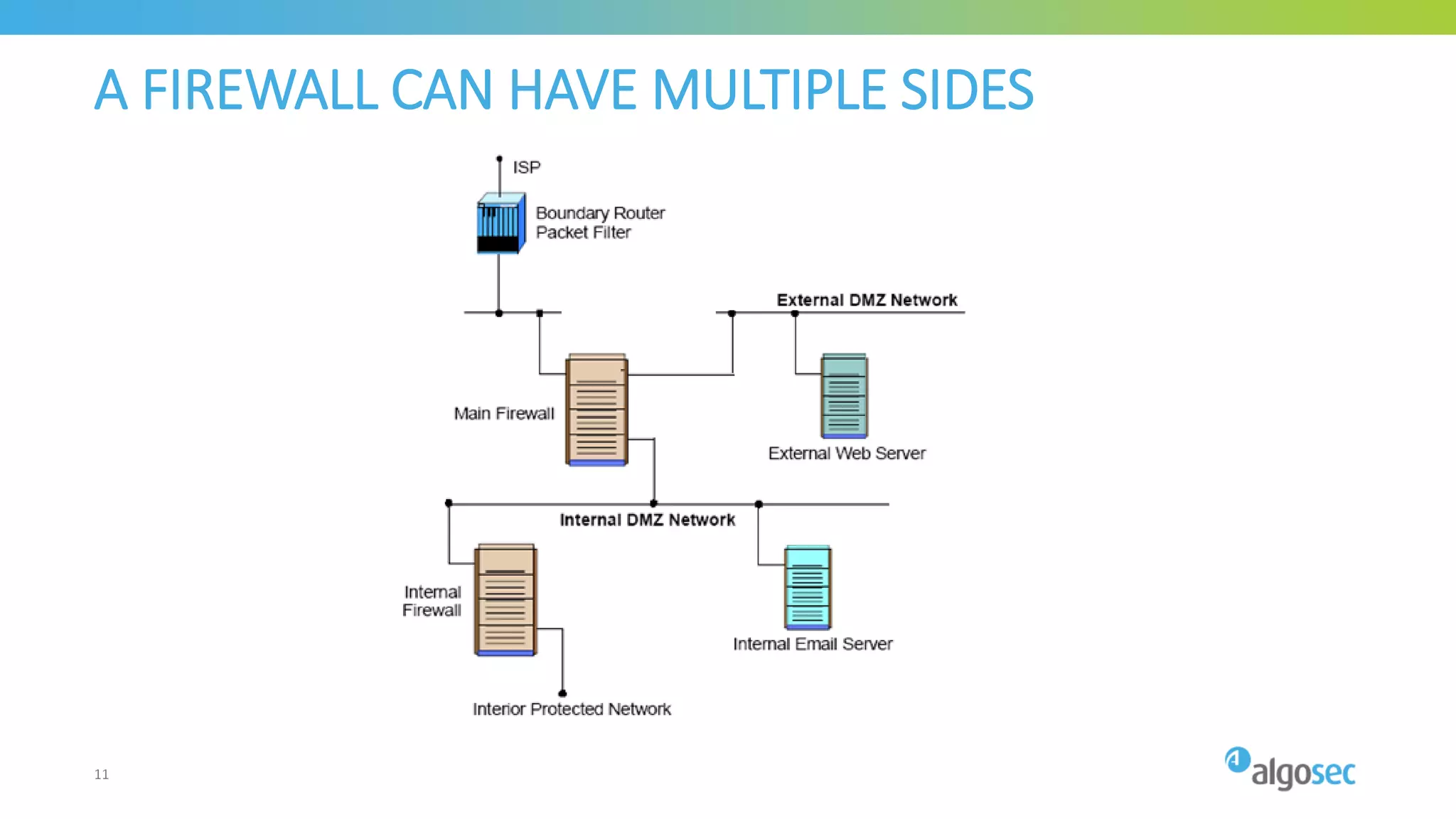
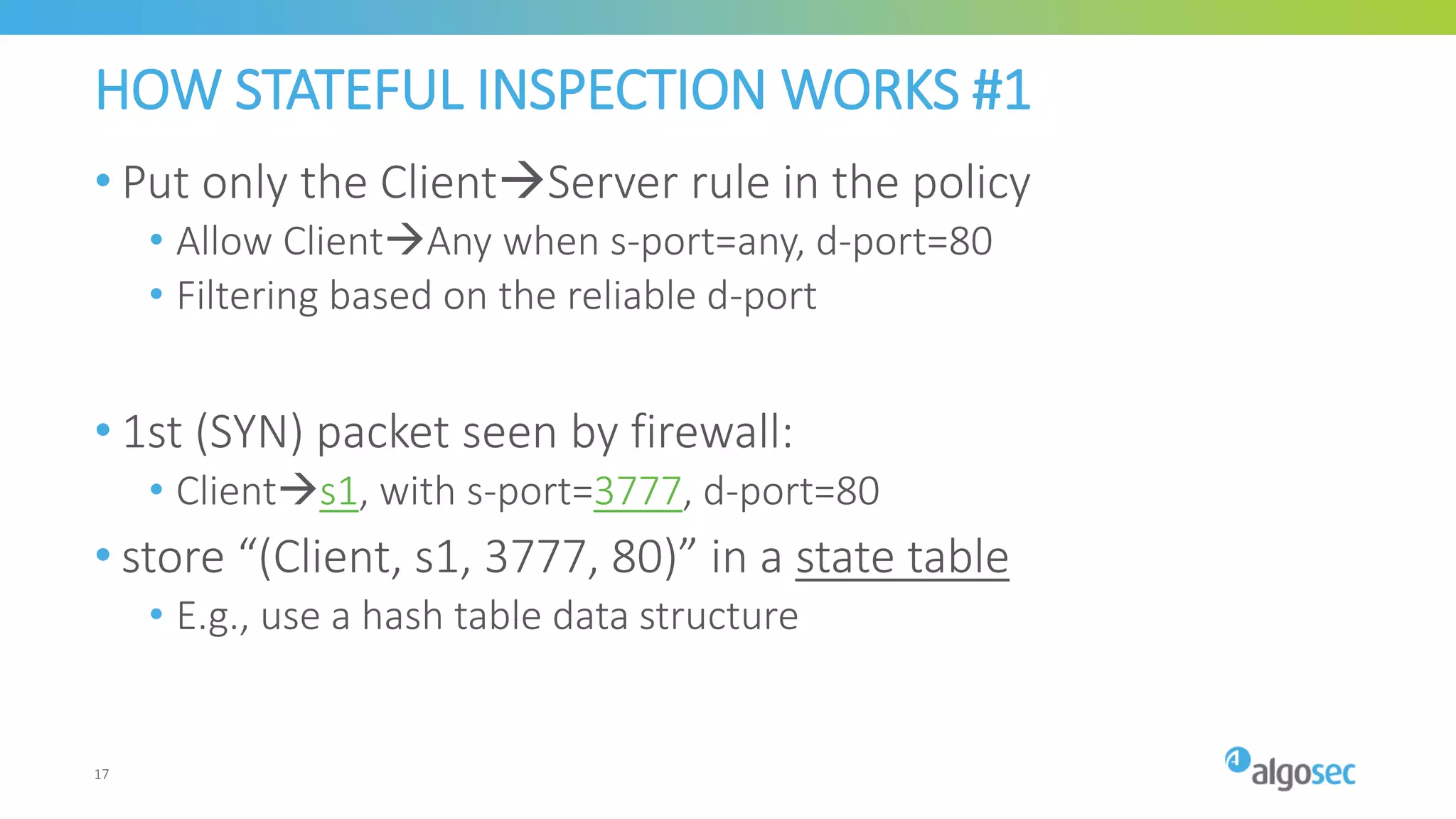
The document presents a comprehensive overview of the evolution of firewalls and network filtering over the past 25 years, starting from host-based firewalls in the 1990s to next-generation and cloud-based solutions. It discusses significant developments in firewall technology, including stateful inspection, zone-based firewalls, and application awareness, along with their advantages and challenges. The current trend highlights the shift towards virtualized and cloud environments, emphasizing the importance of host-based firewalls in dynamic cloud settings.