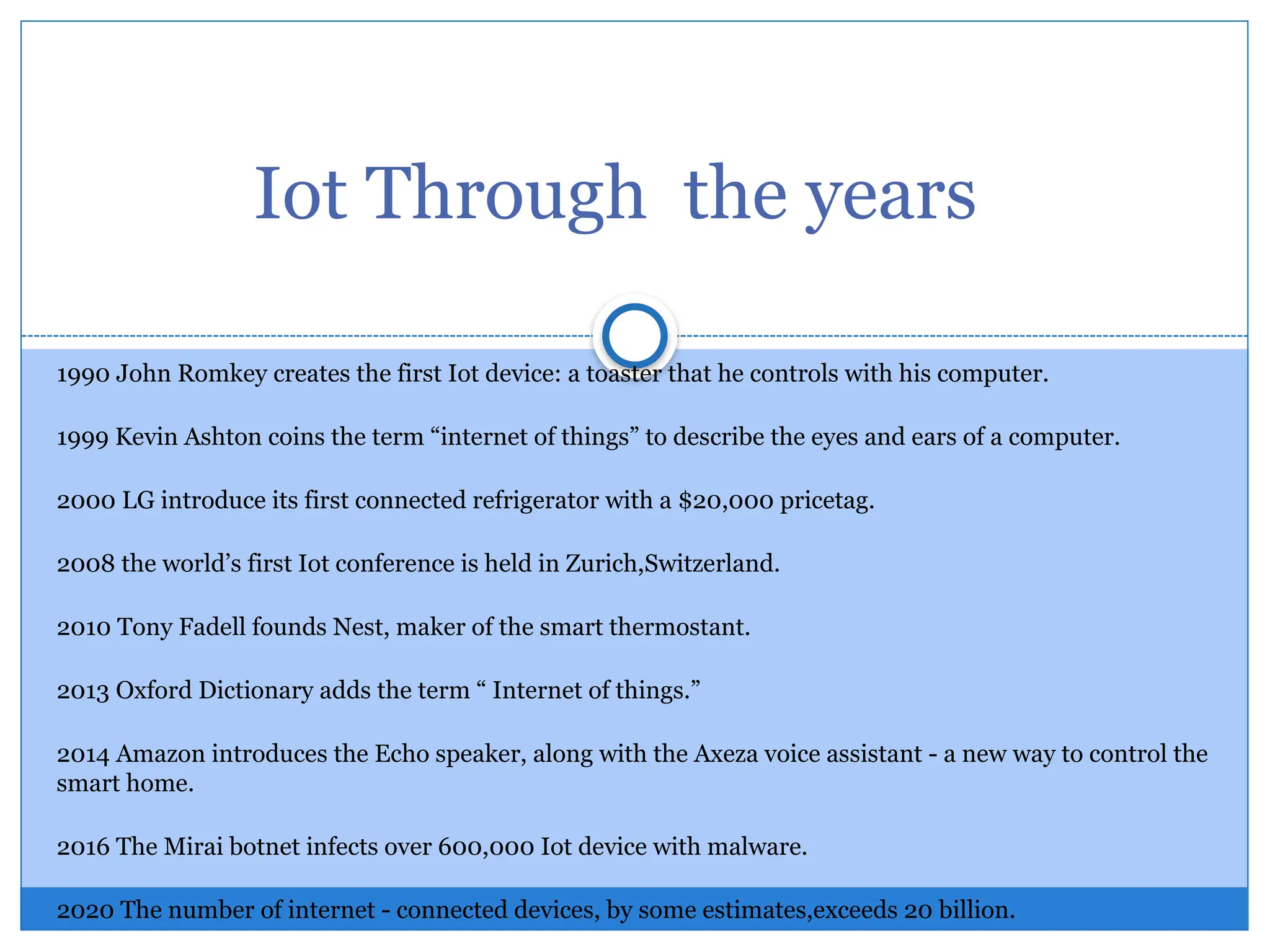
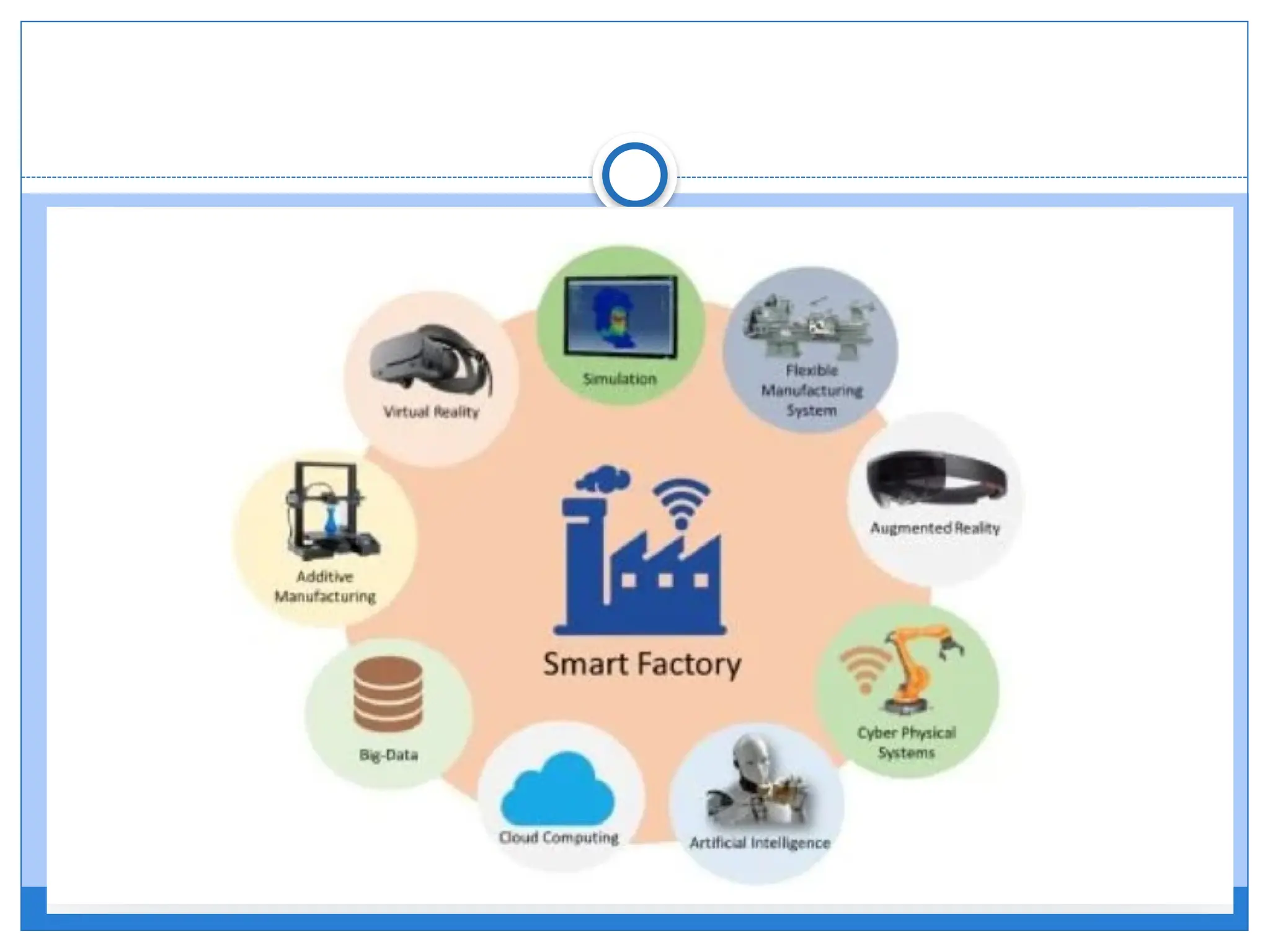
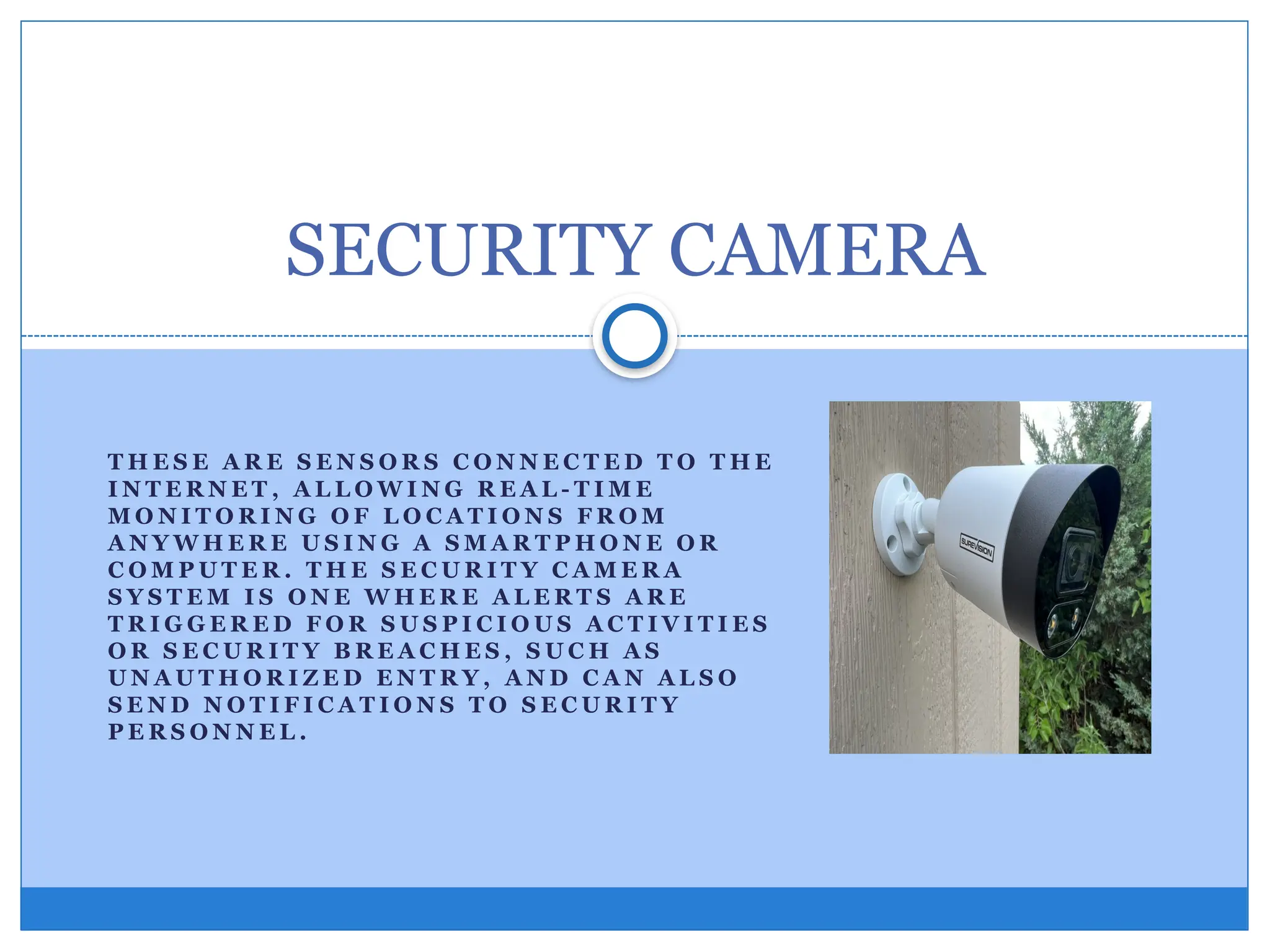
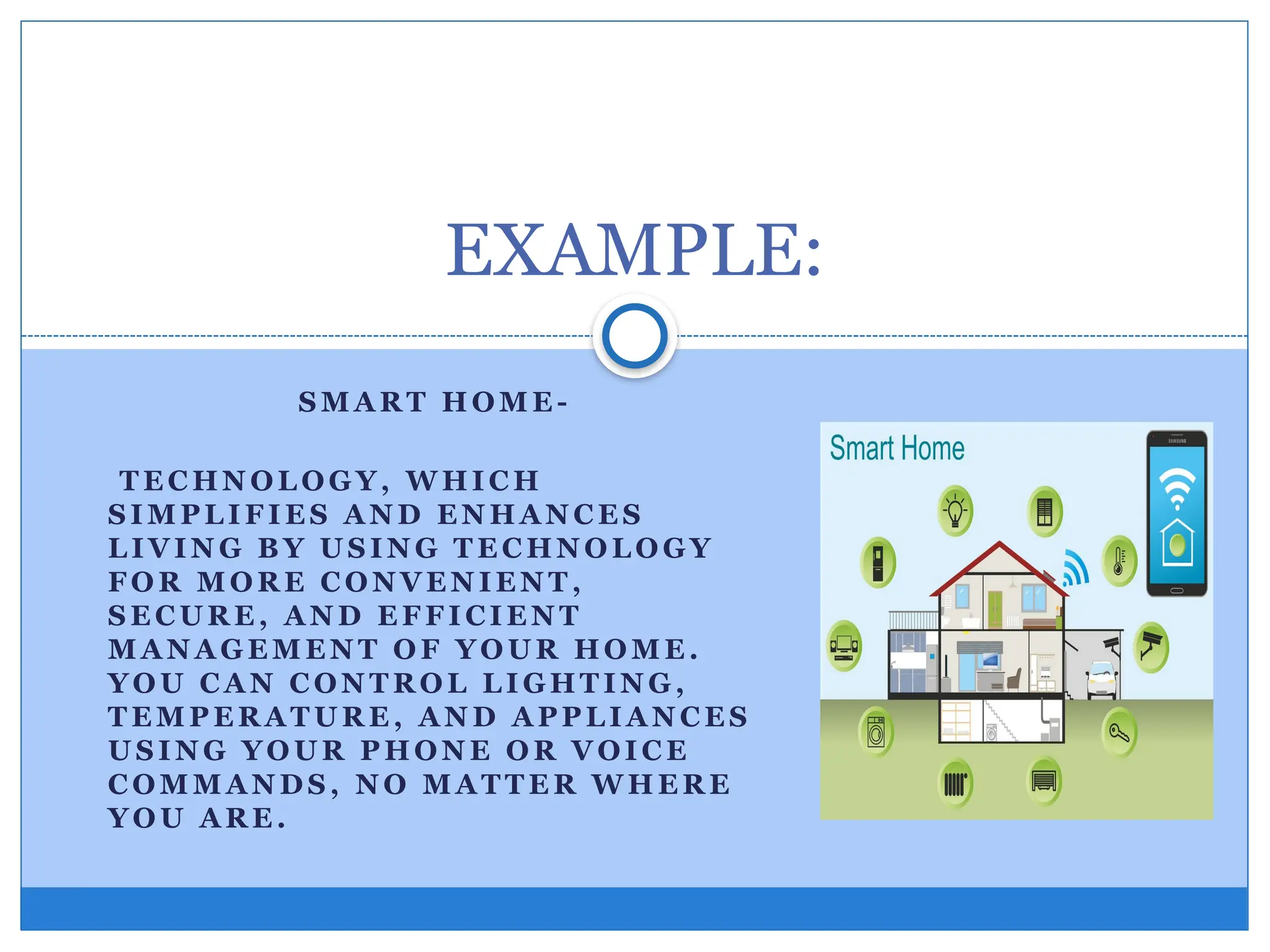
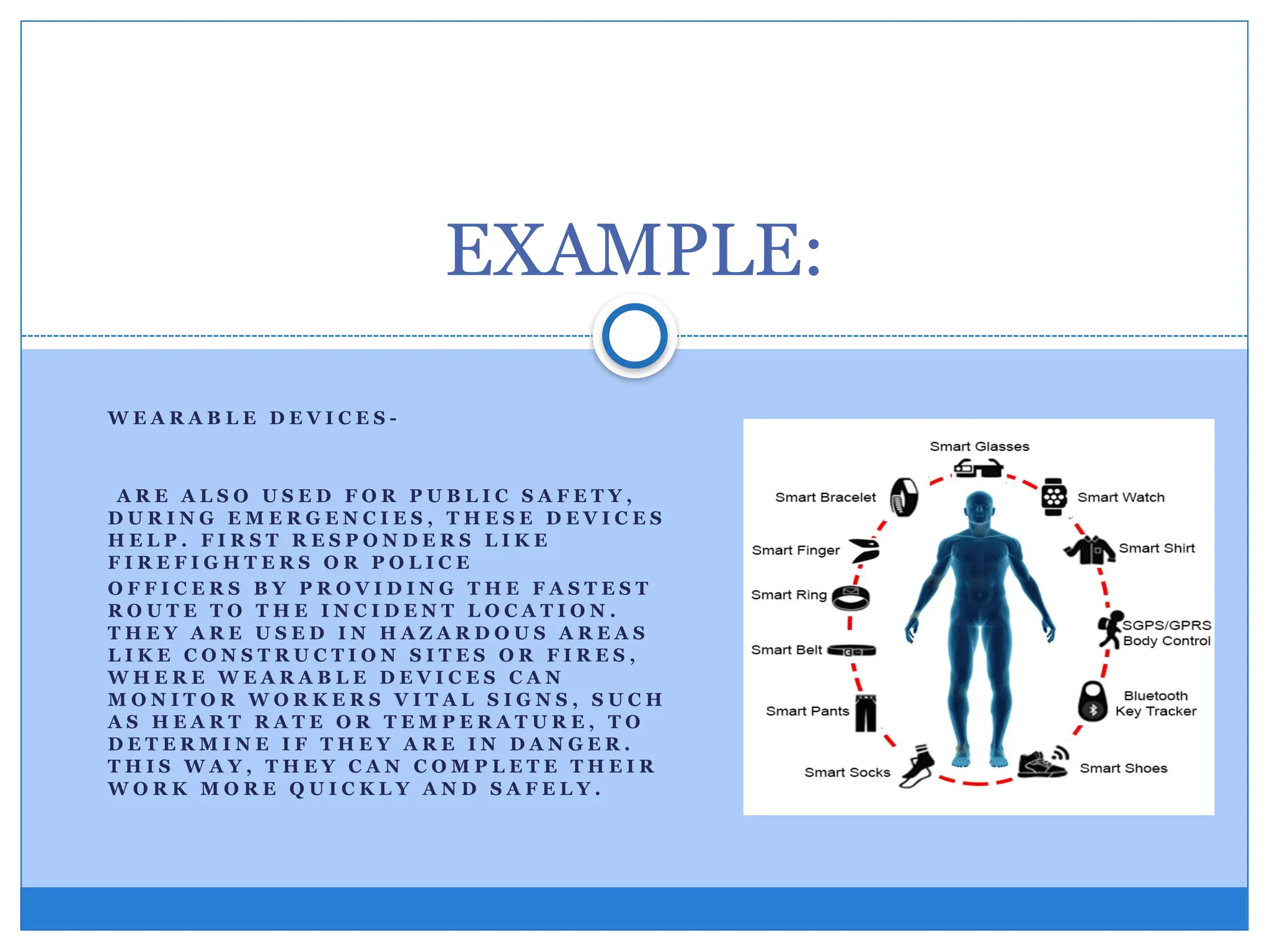
The document is a module from Baao Community College discussing the impact of information and communications technology, focusing on the Internet of Things (IoT). It explores how IoT enhances business processes, customer experience, and automation, while also addressing potential challenges such as security risks and compatibility issues. The module outlines various applications of IoT across industries, including automotive, telecom, and energy, emphasizing its importance in modern society.