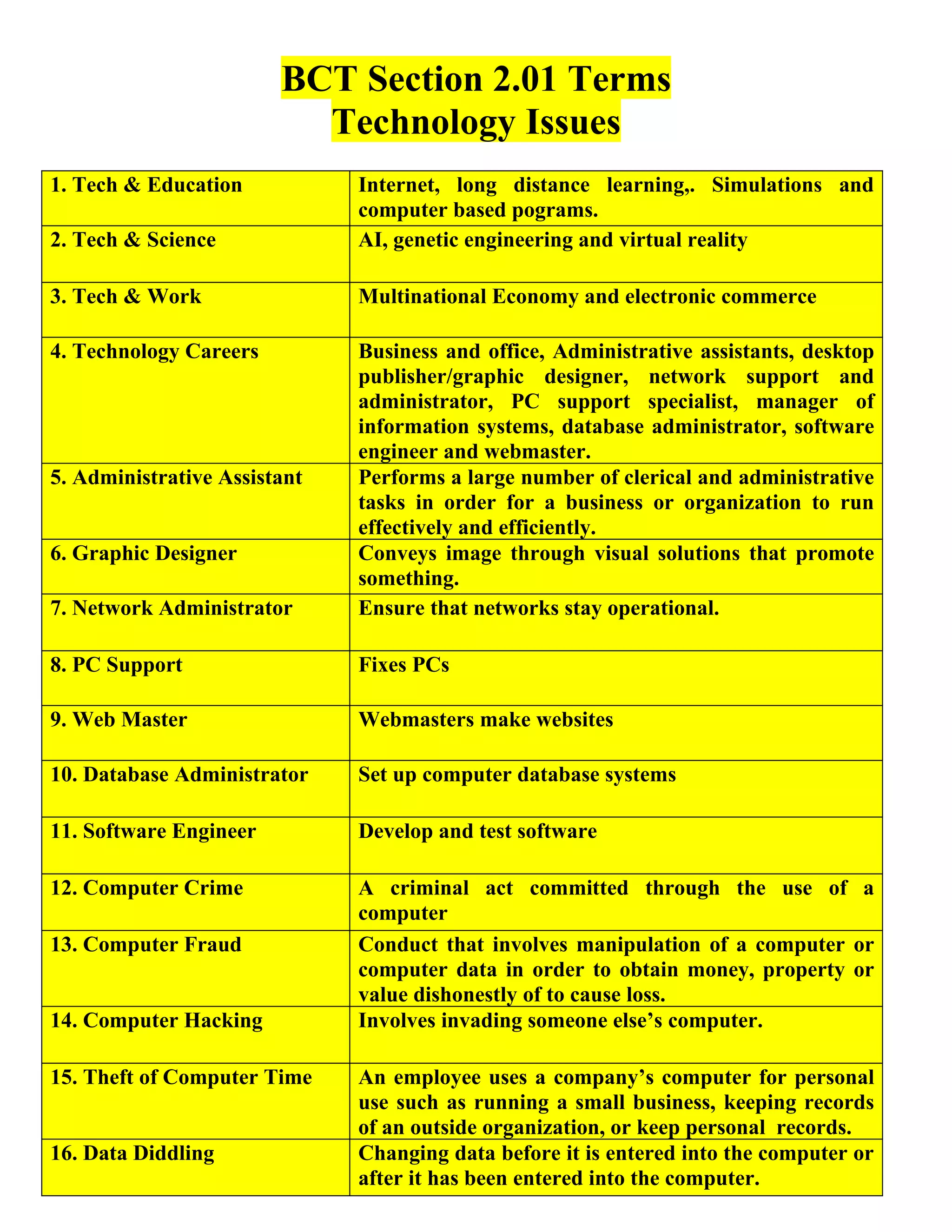
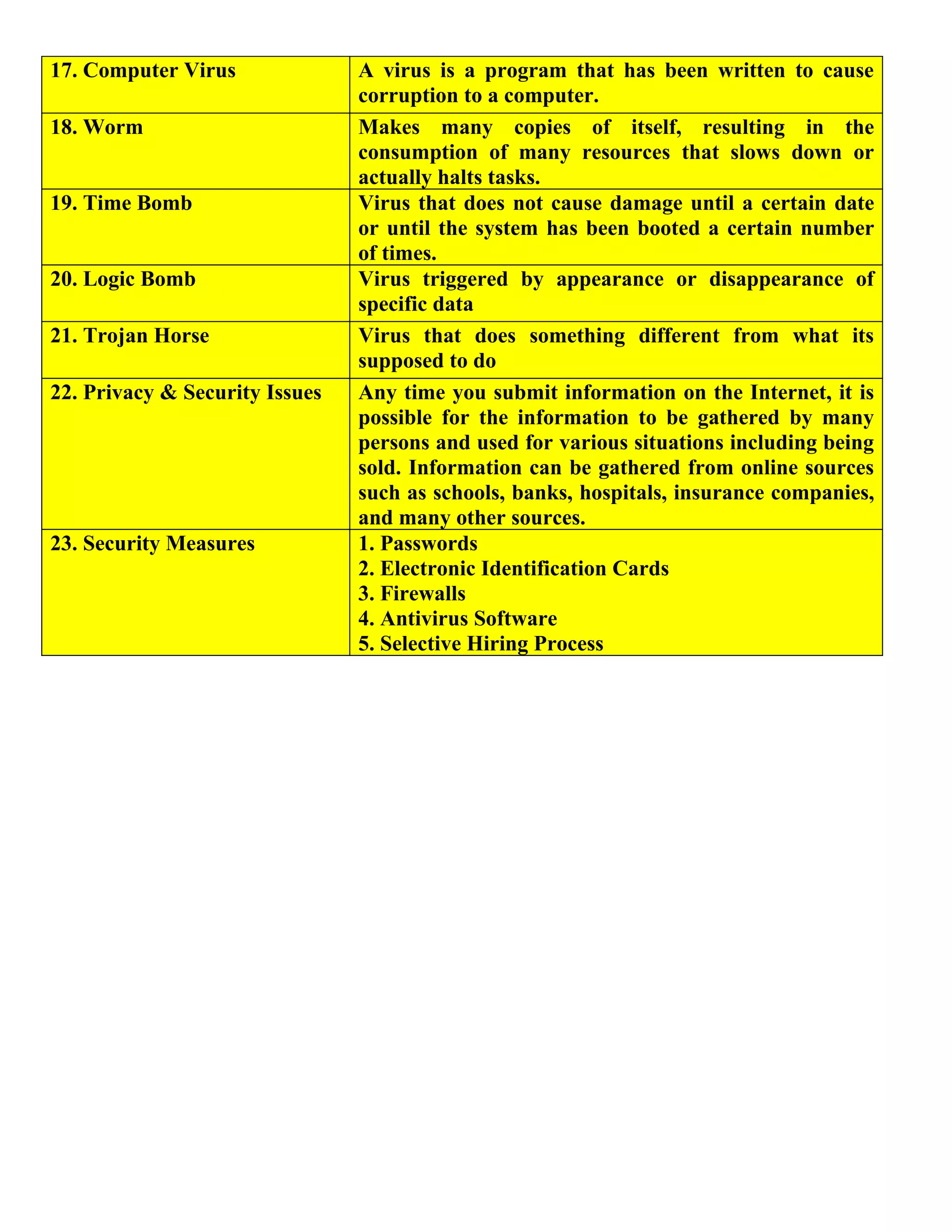
This document discusses various technology topics including how technology impacts education, science, and the workplace. It also outlines several technology-focused careers such as administrative assistant, graphic designer, network administrator, and software engineer. The document concludes by covering computer crimes like hacking and viruses as well as privacy and security issues and some common security measures used to address those issues.