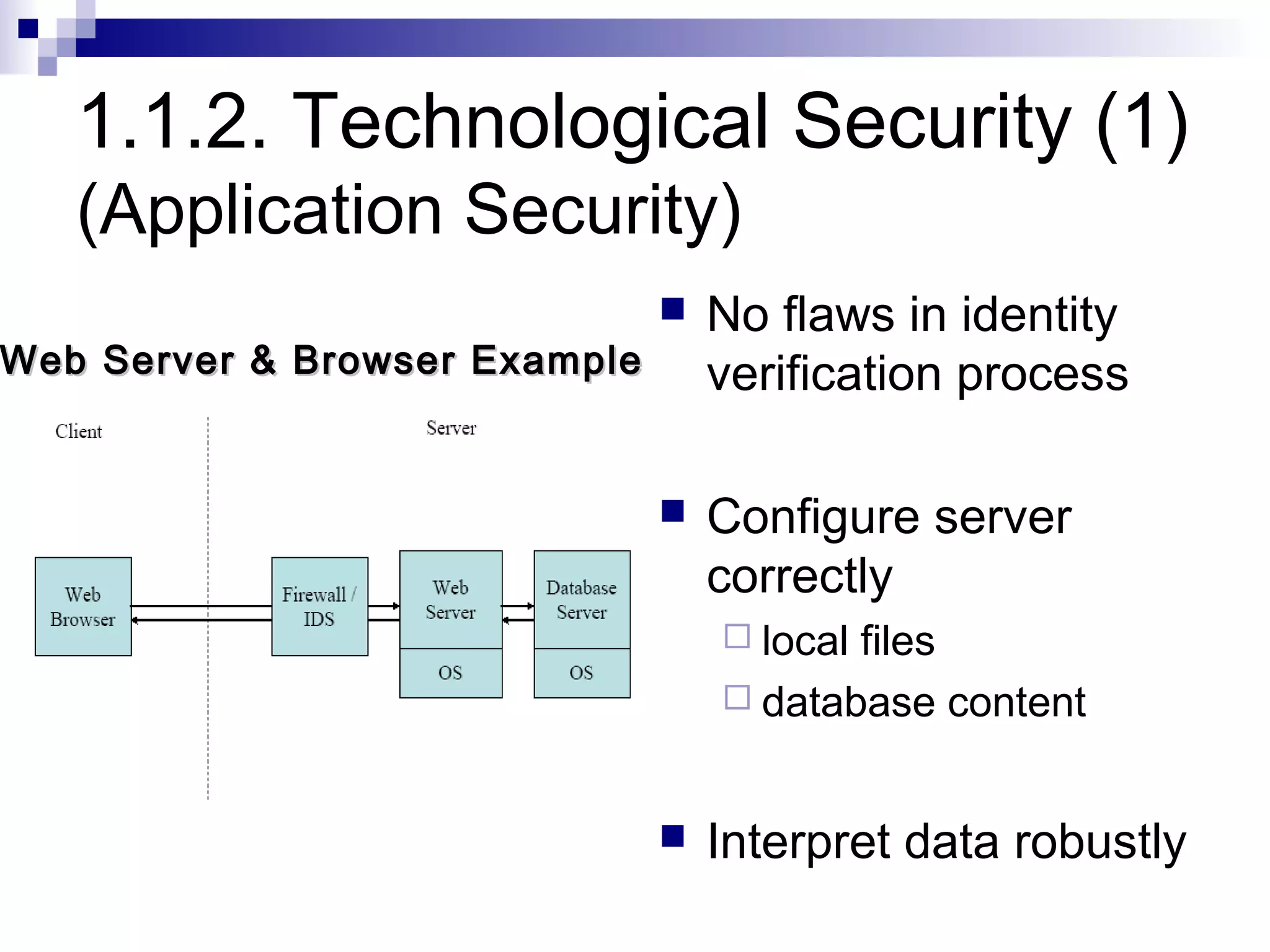
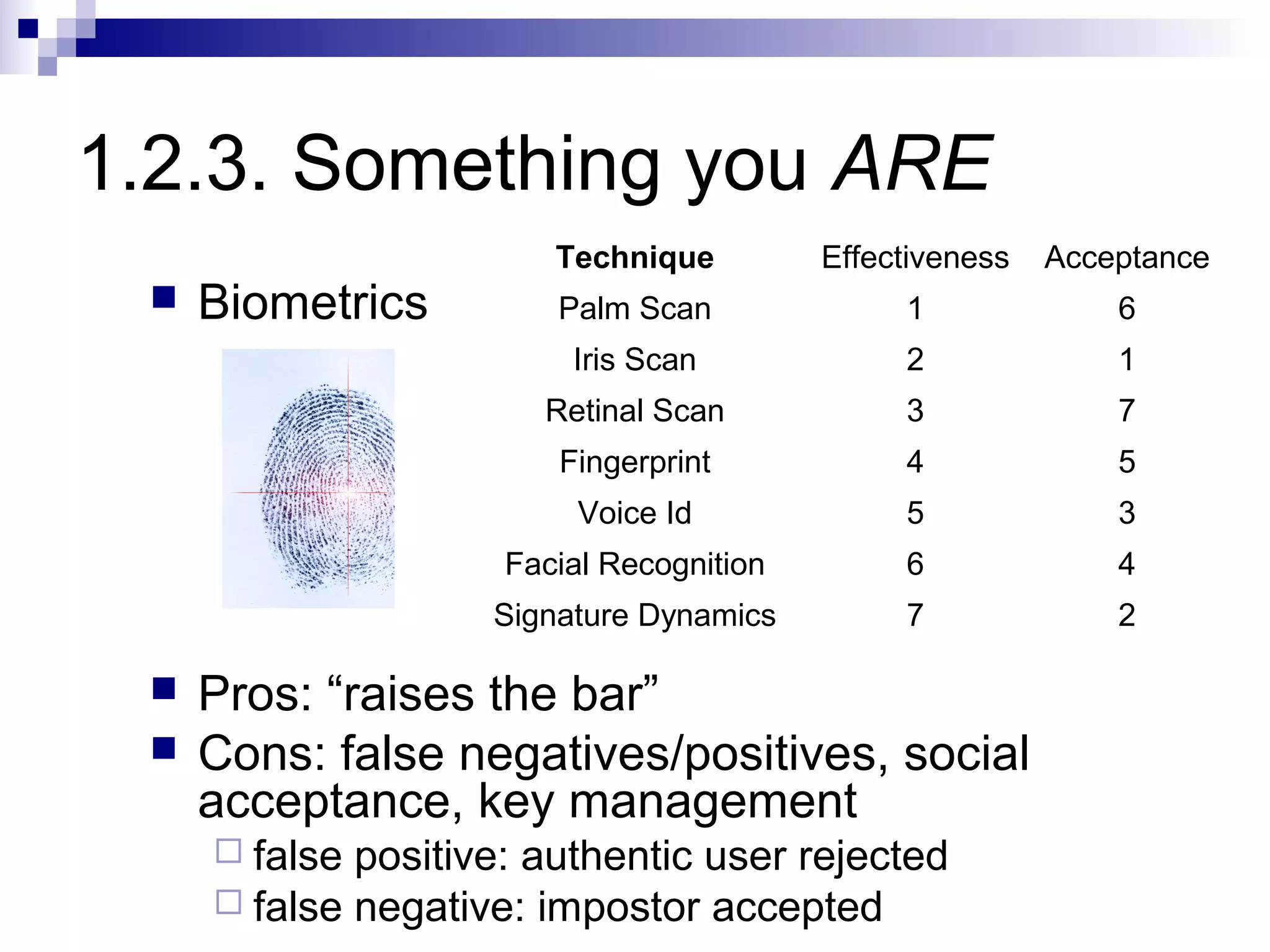
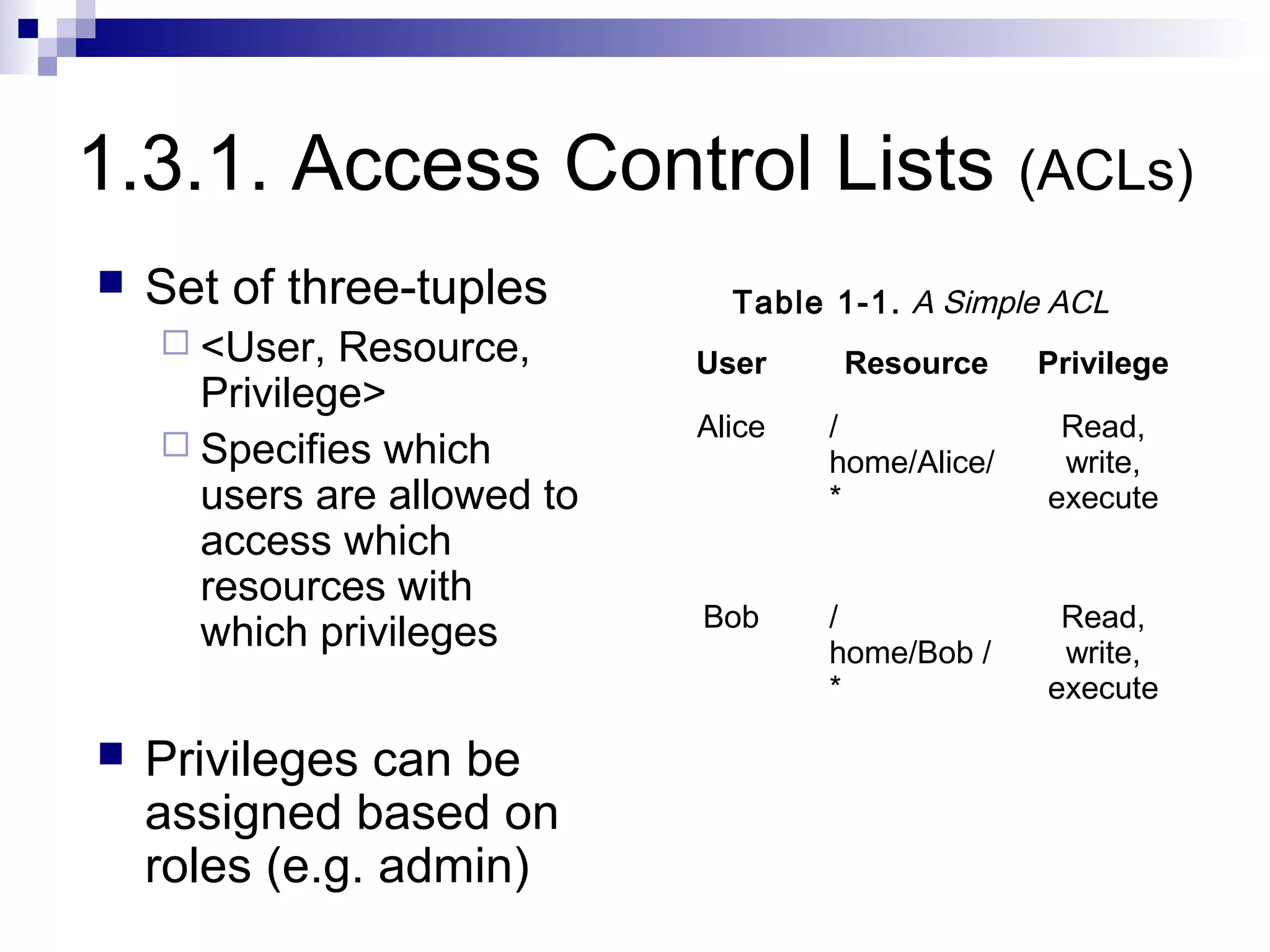
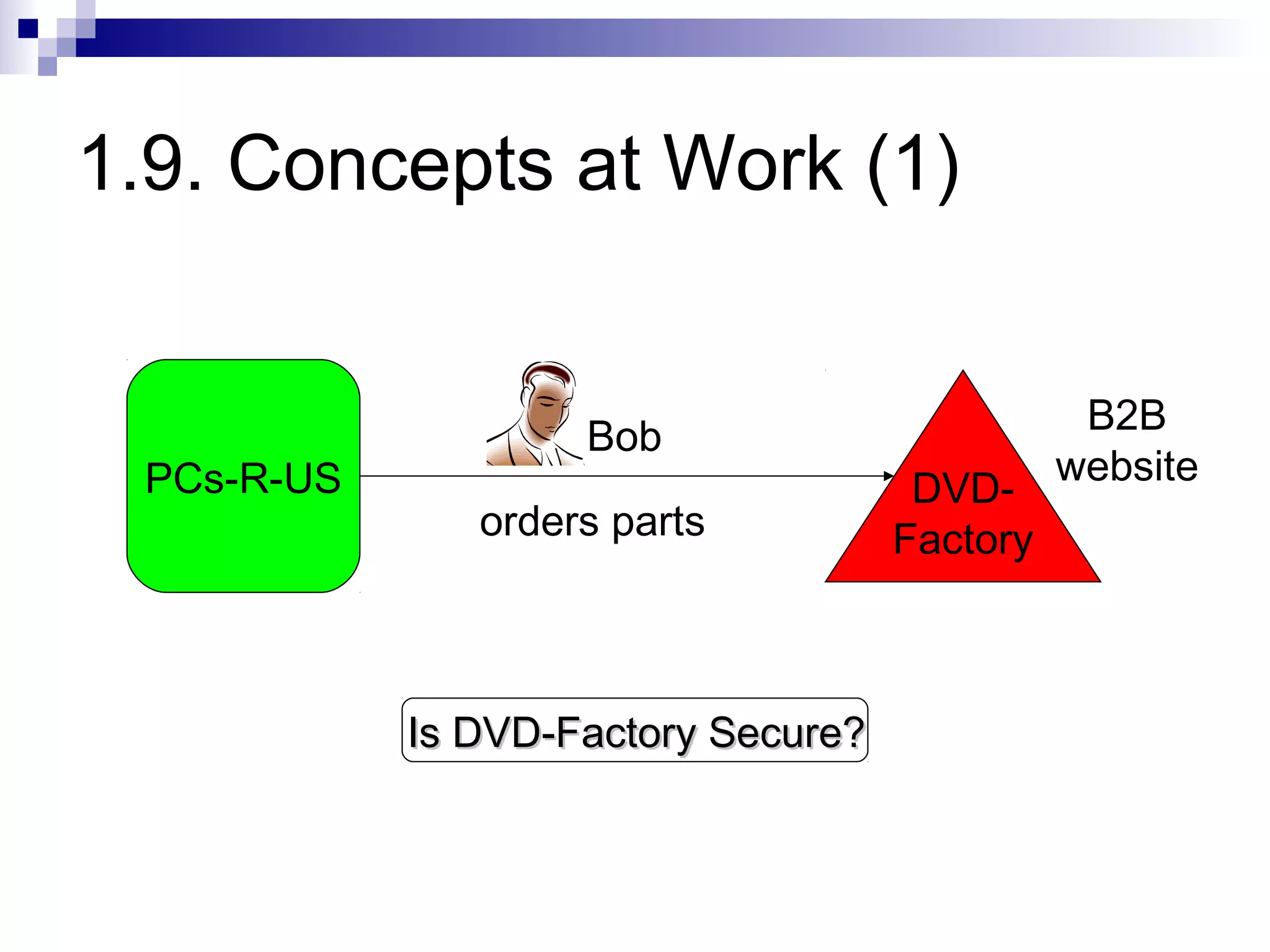
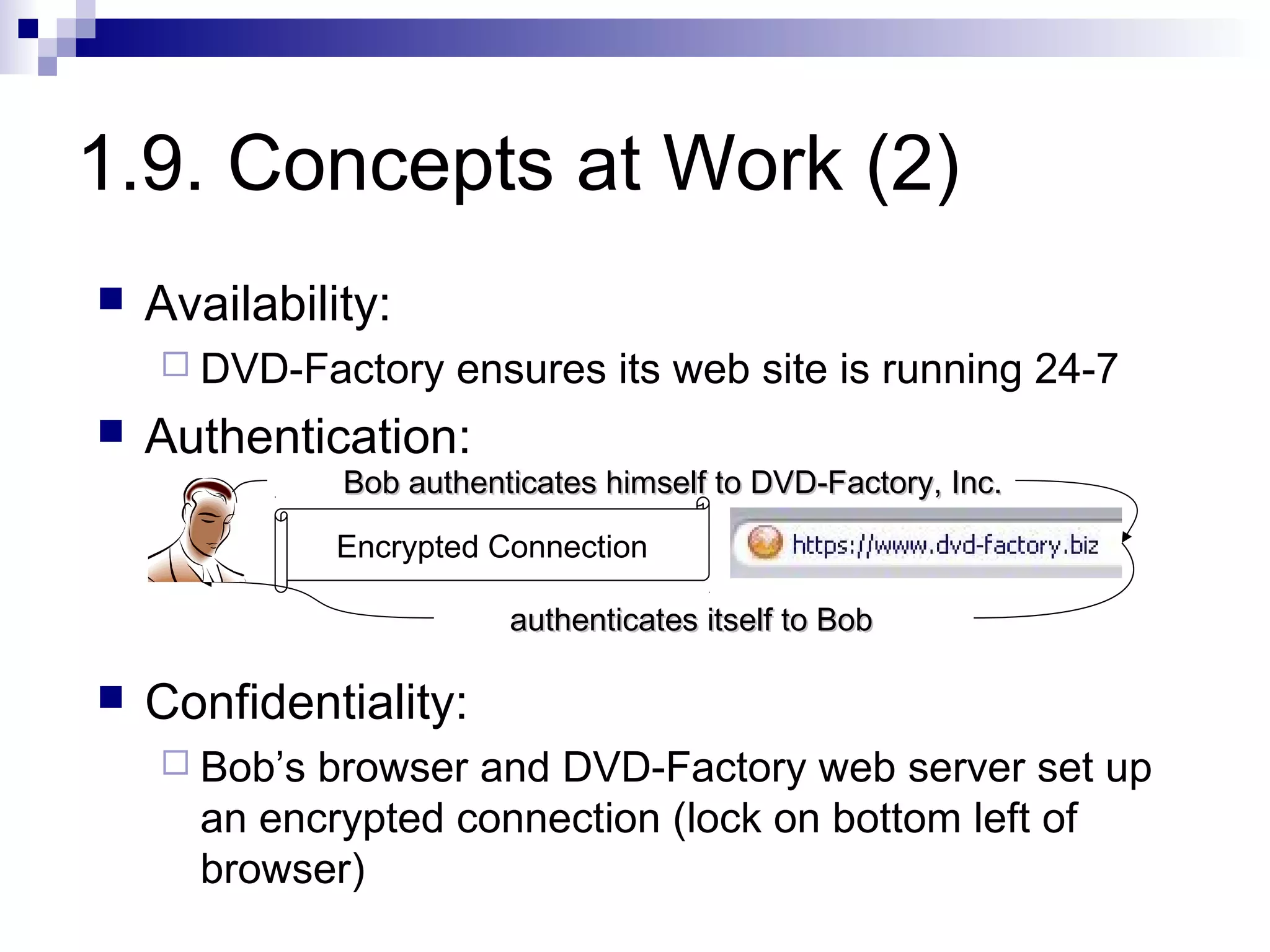
The document discusses security concepts including authentication, authorization, confidentiality, integrity, accountability, availability, and non-repudiation. It provides examples of how these concepts apply to physical, technological, and policy/procedural security. It also summarizes how these concepts would work in a scenario where Bob orders parts from a DVD factory website.