Embed presentation
Downloaded 686 times

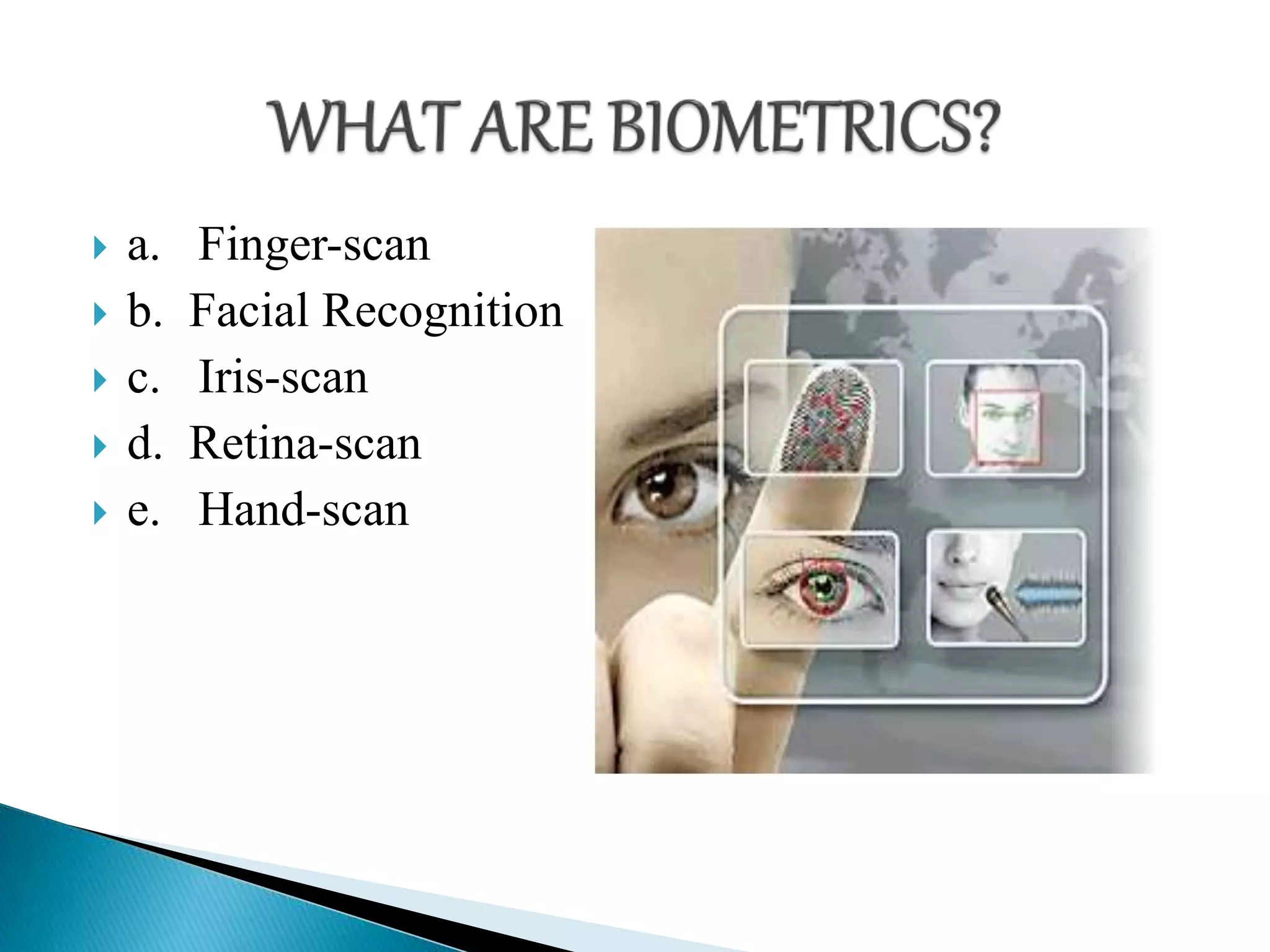


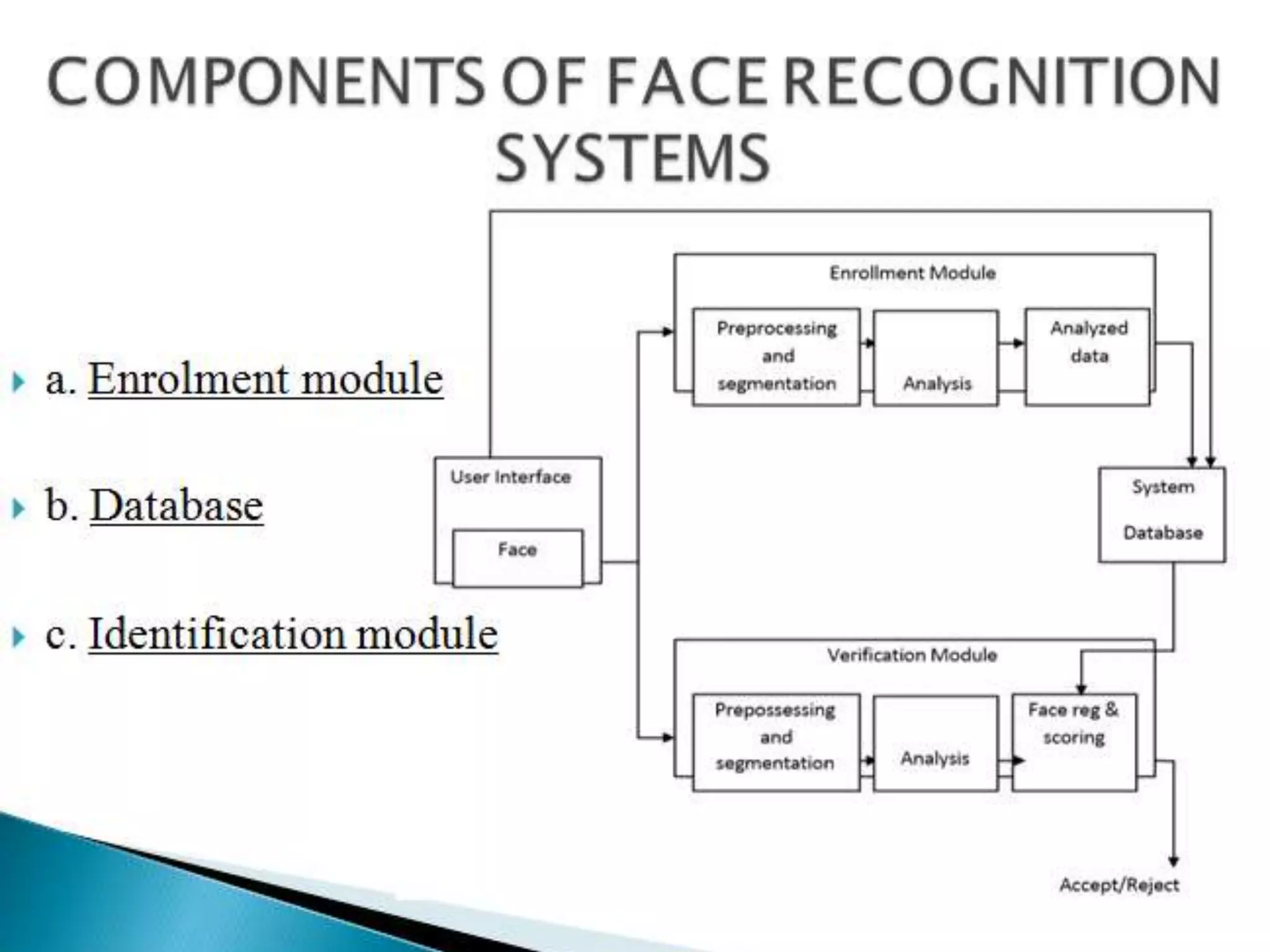
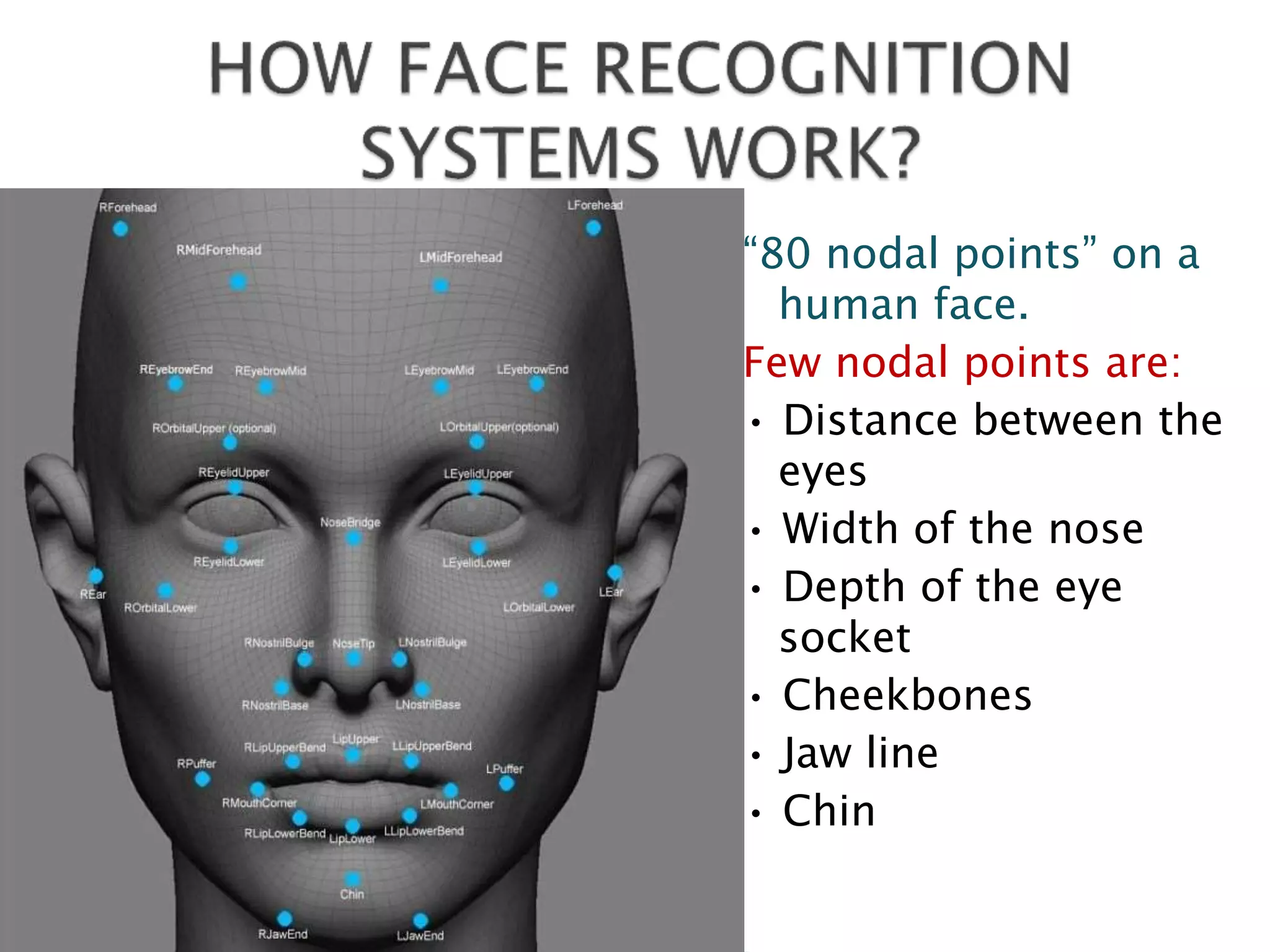
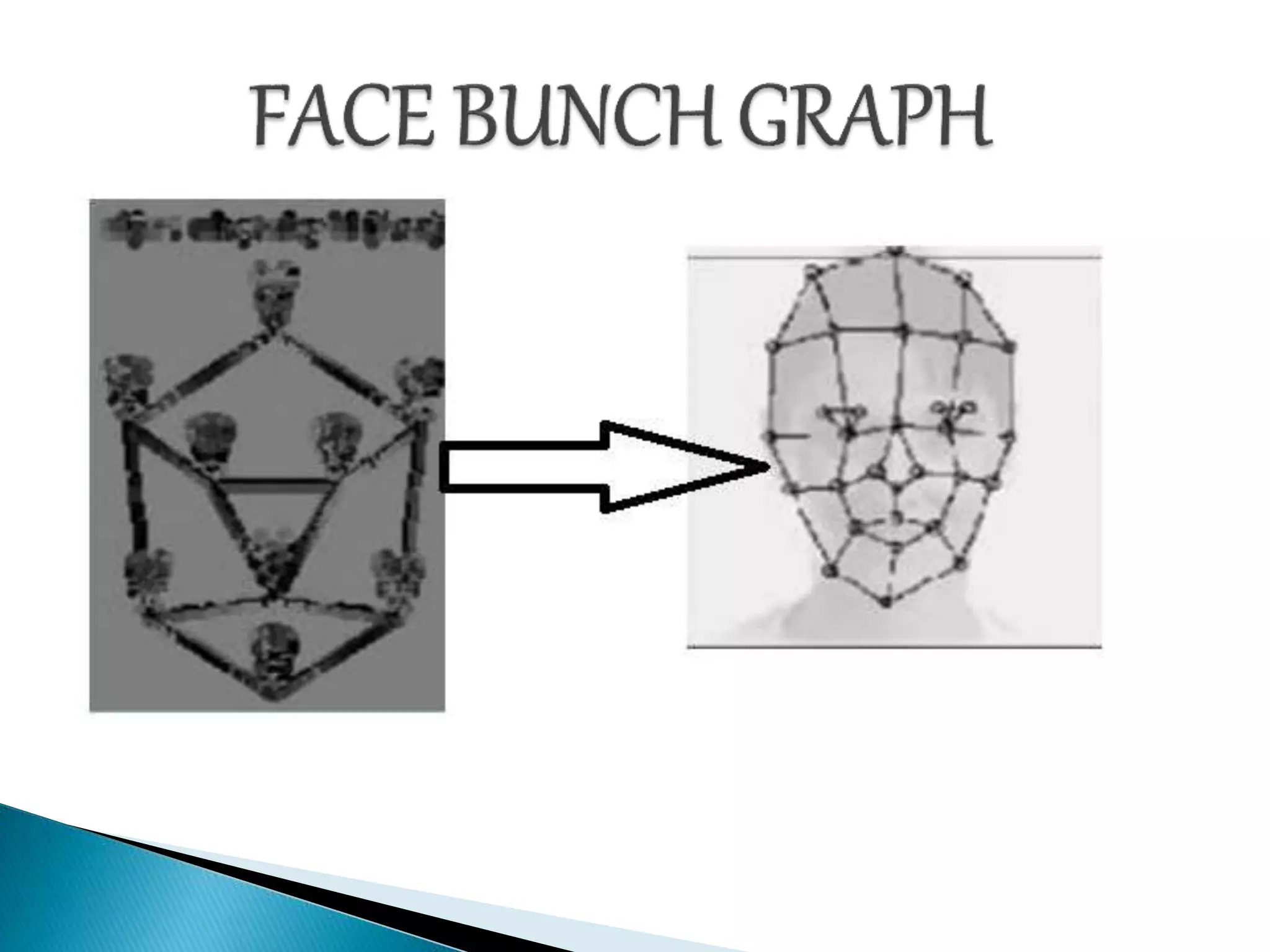




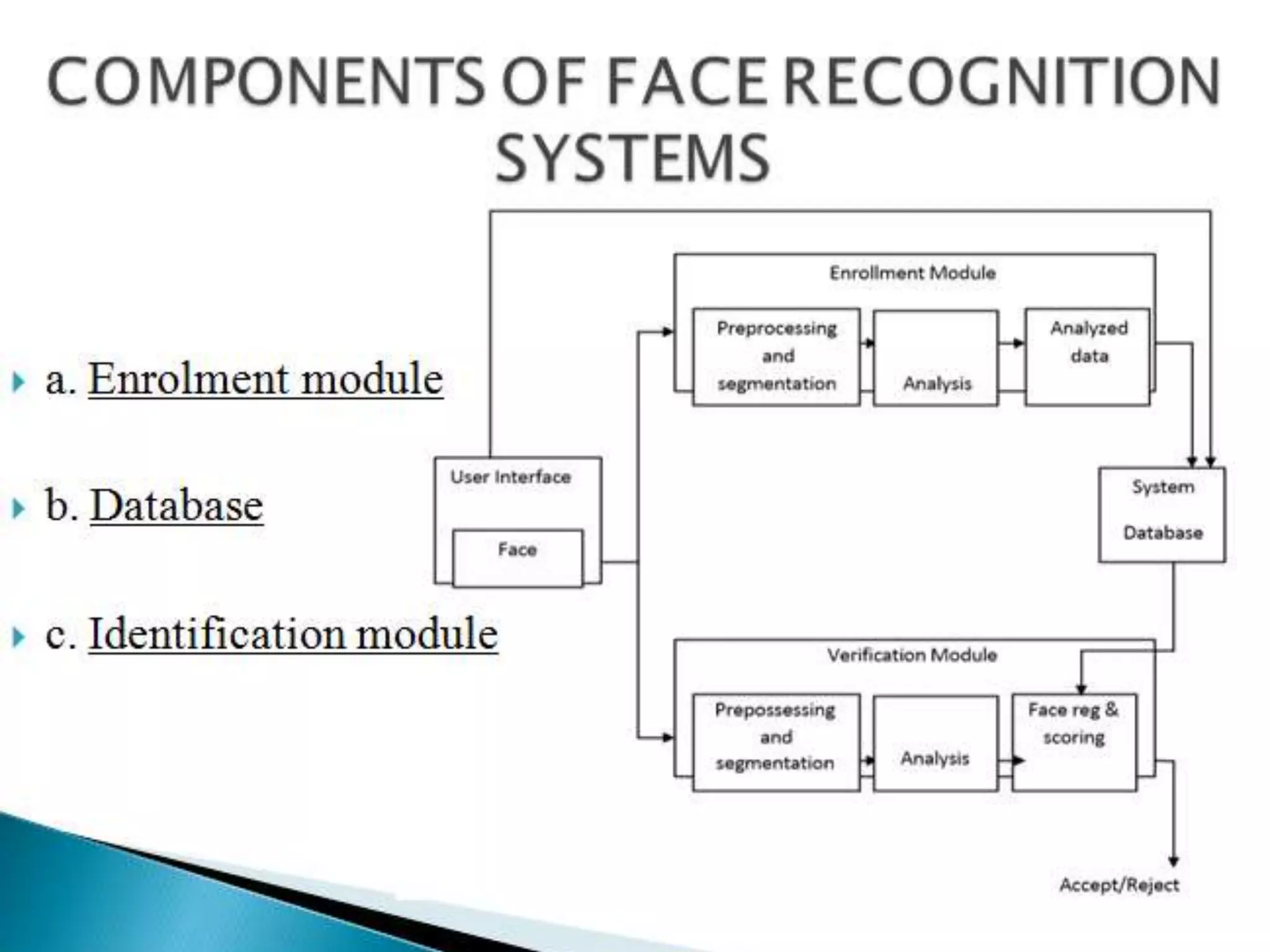
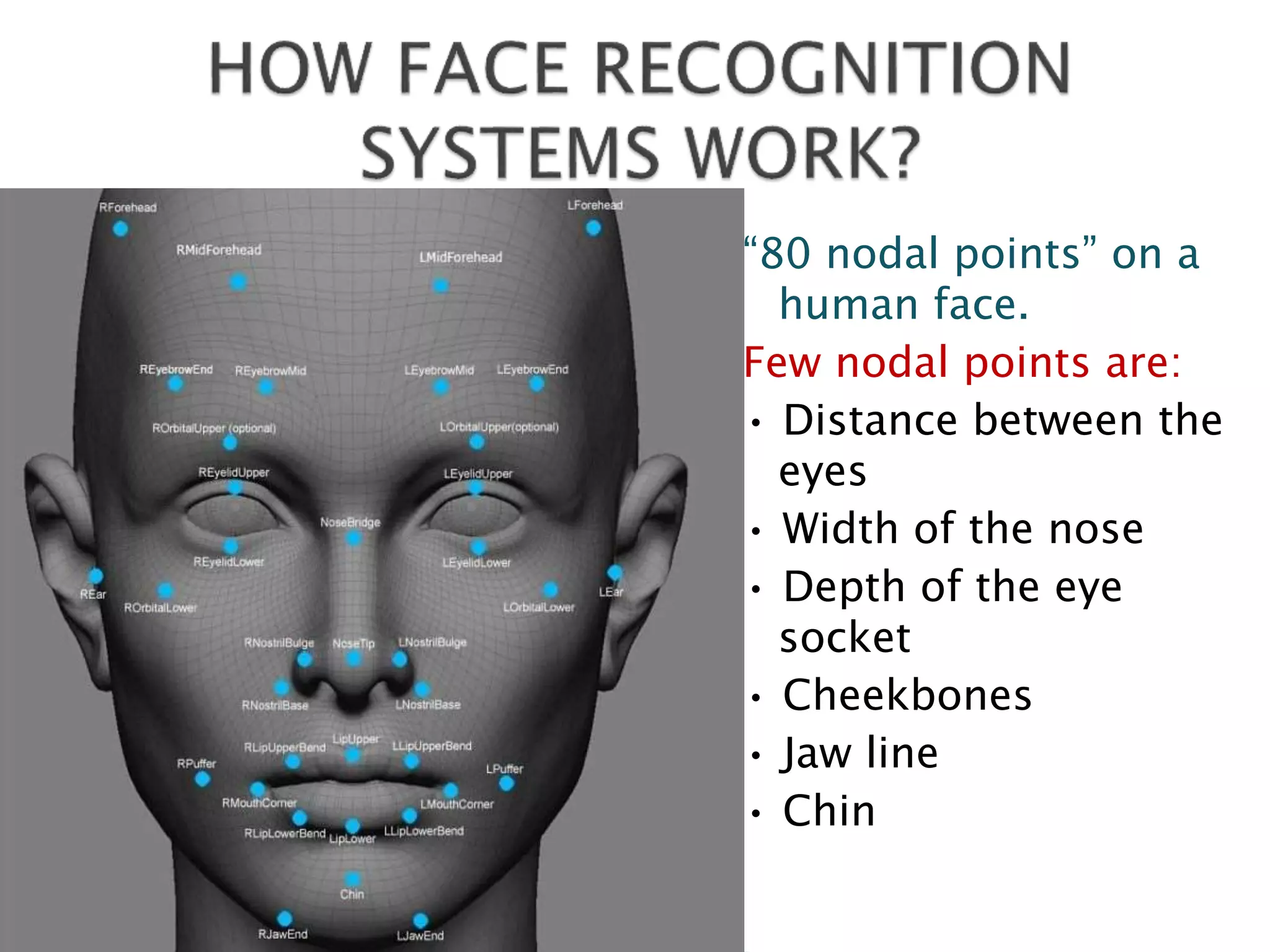
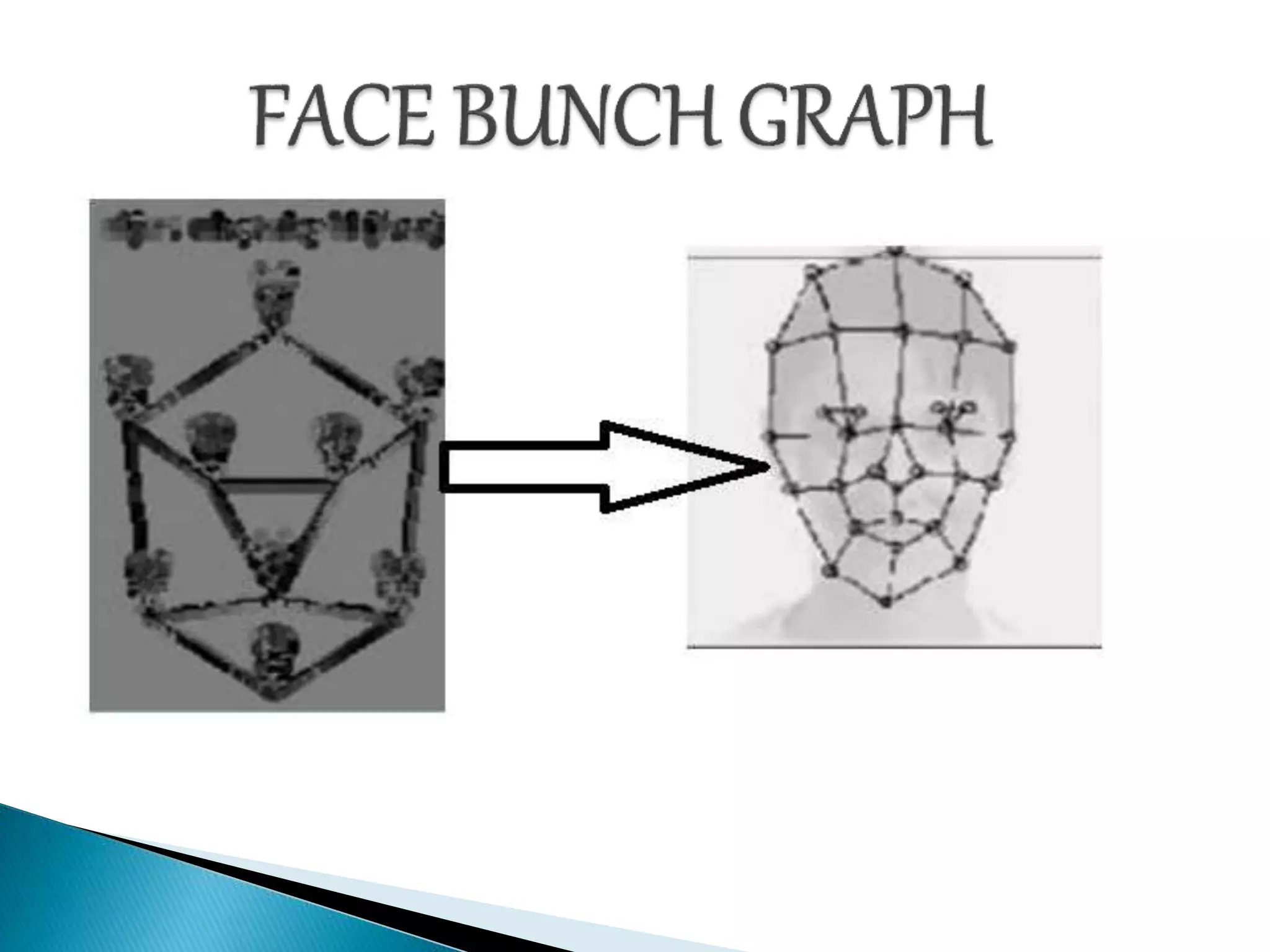
This document discusses different biometric identification methods such as finger-scan, facial recognition, iris-scan, and retina-scan. It notes there are approximately 80 nodal points on a human face that can be used for facial recognition, including the distance between the eyes, width of the nose, depth of the eye socket, cheekbones, jaw line, and chin. The document outlines several existing facial recognition algorithms and notes they are not yet 100% efficient. It concludes by describing potential government and commercial uses of facial recognition technology, such as for law enforcement, security, immigration, voting verification, residential security, and banking ATMs.