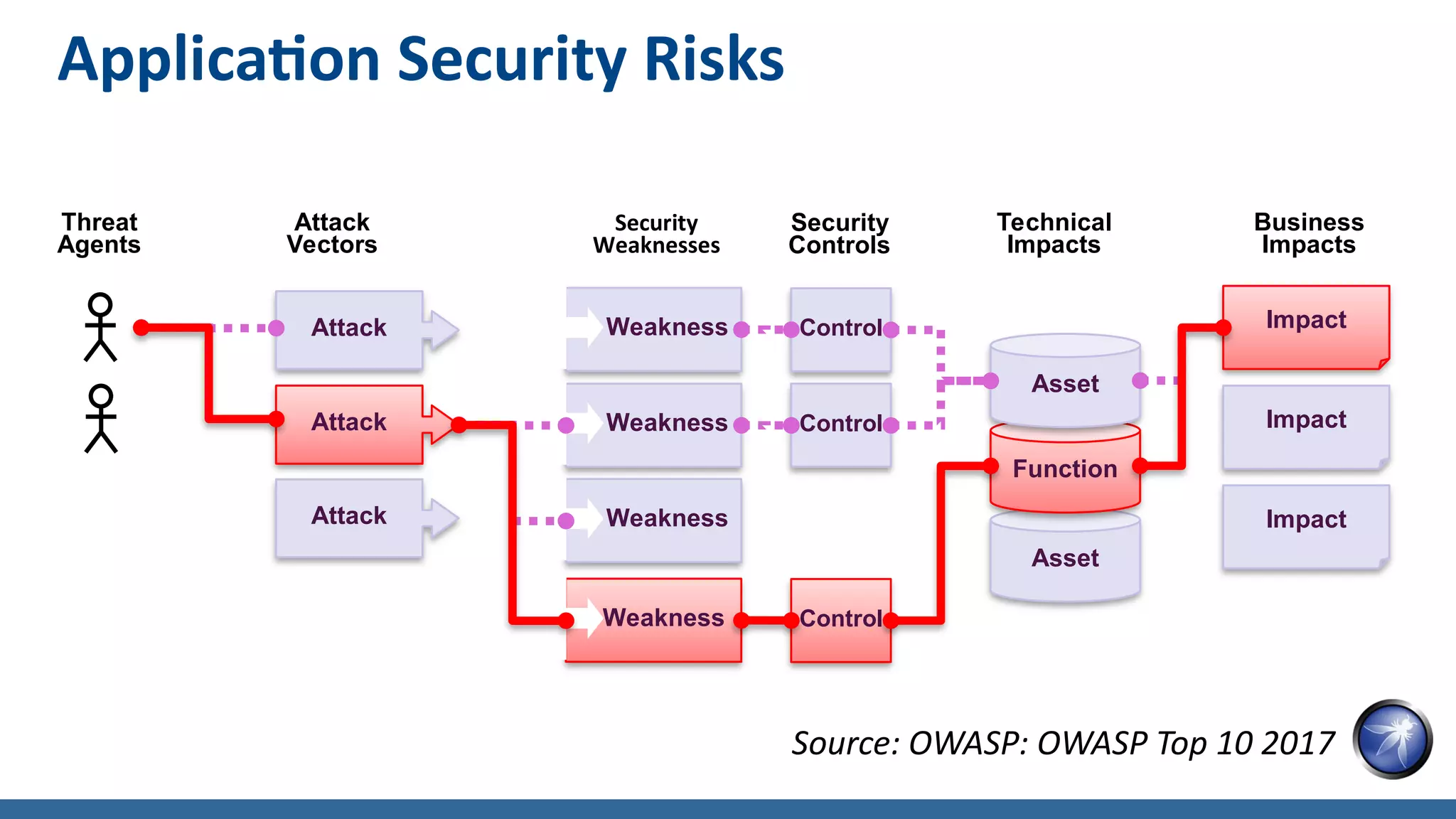
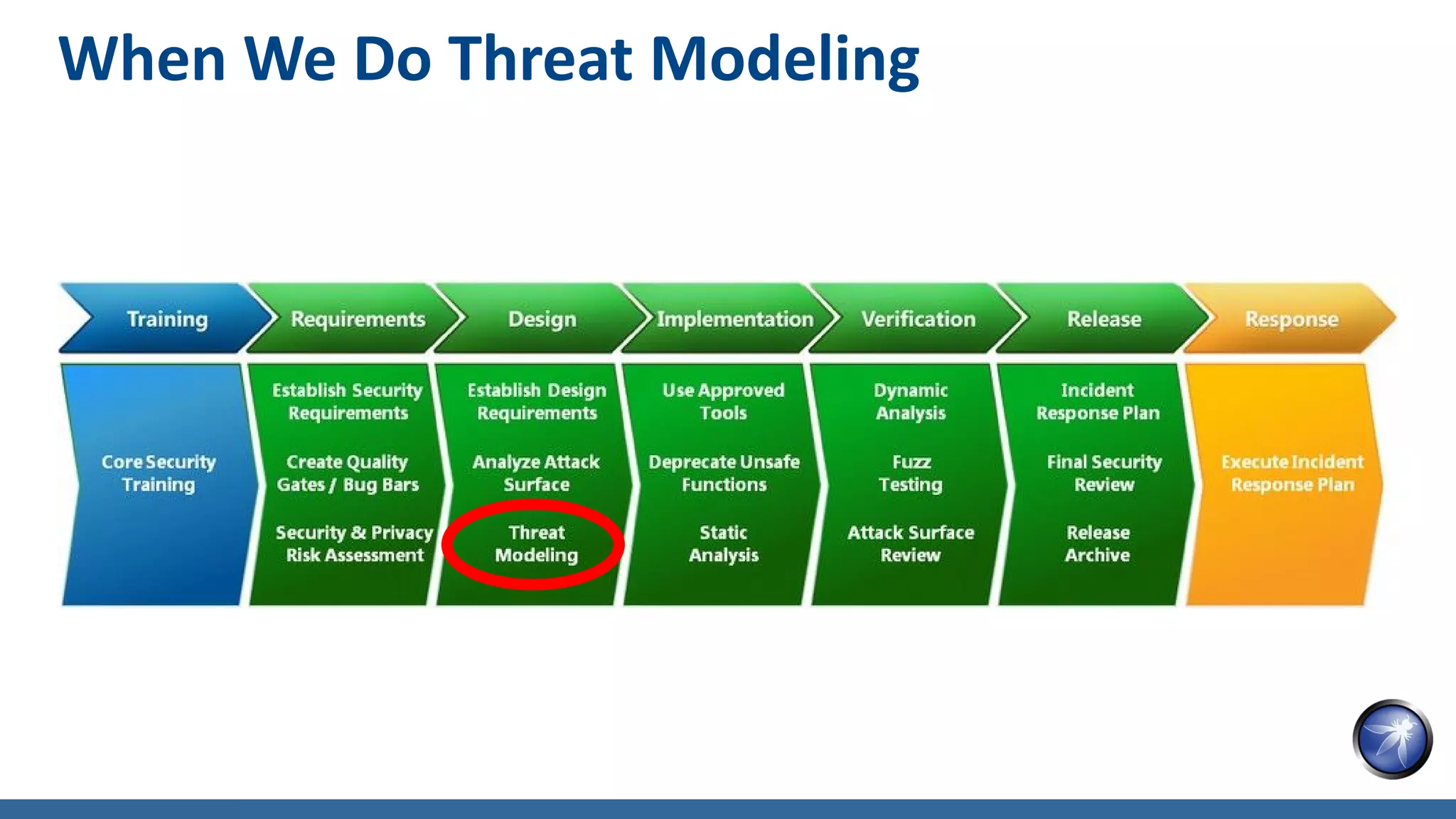
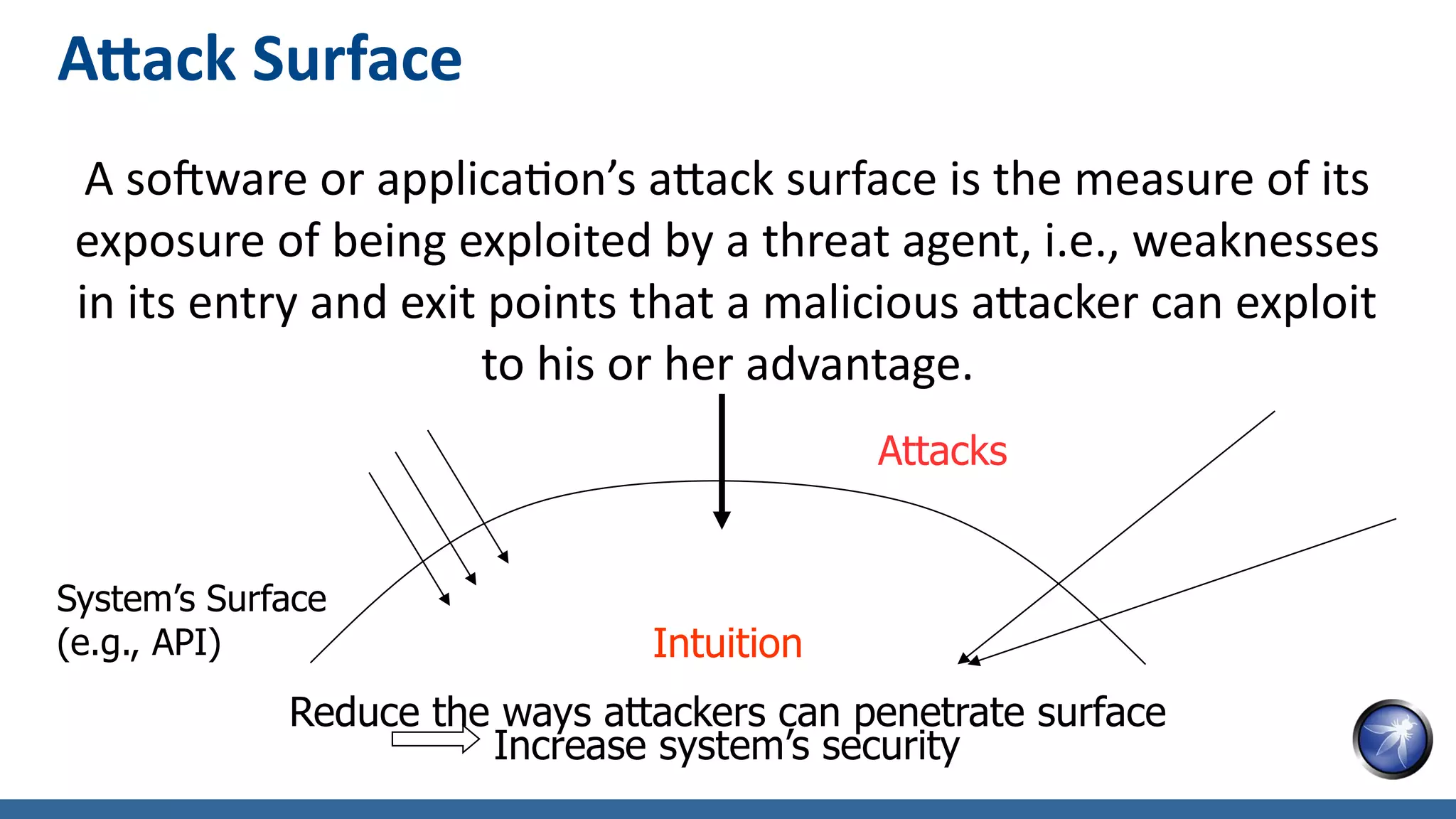
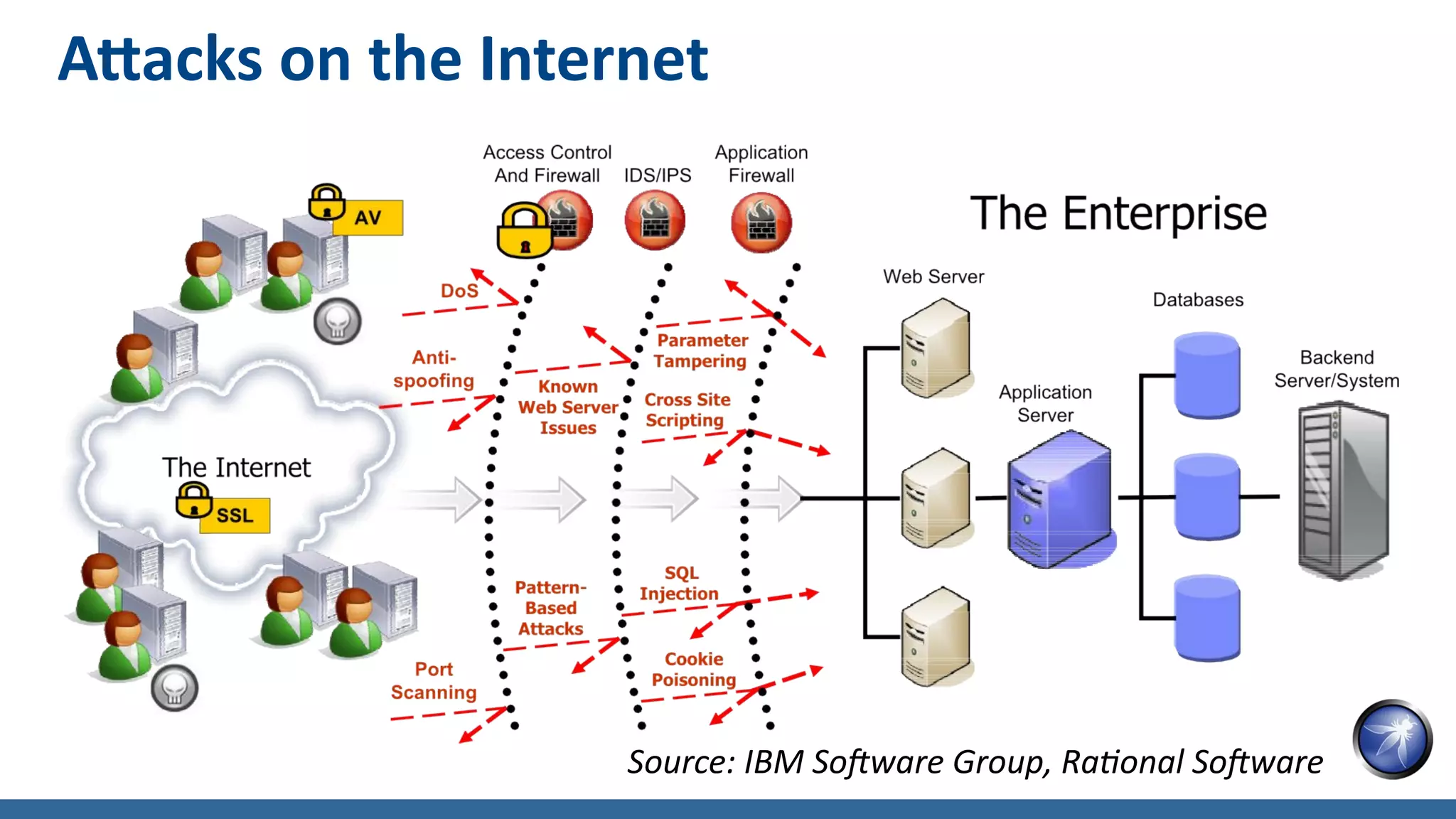
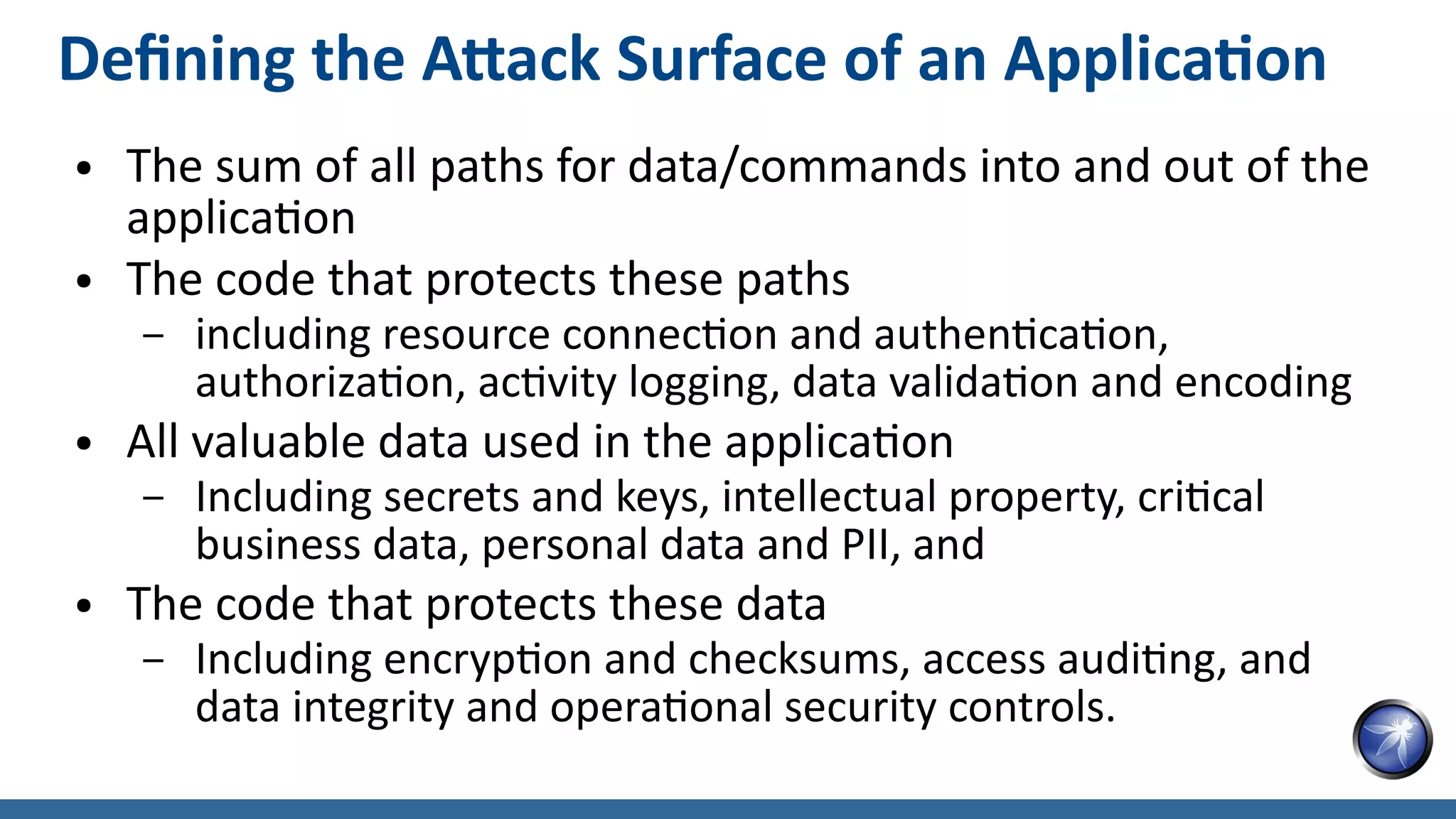
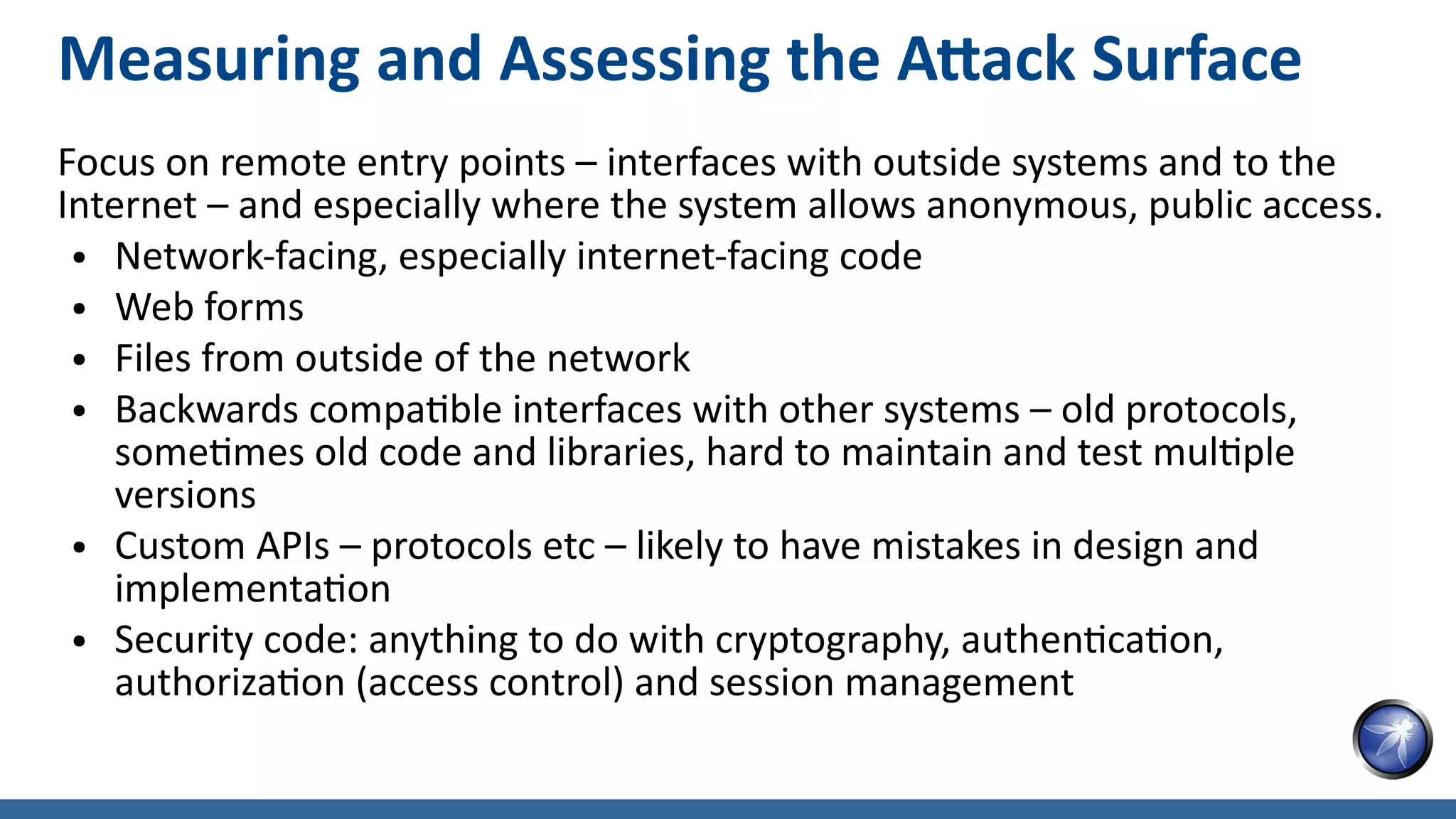
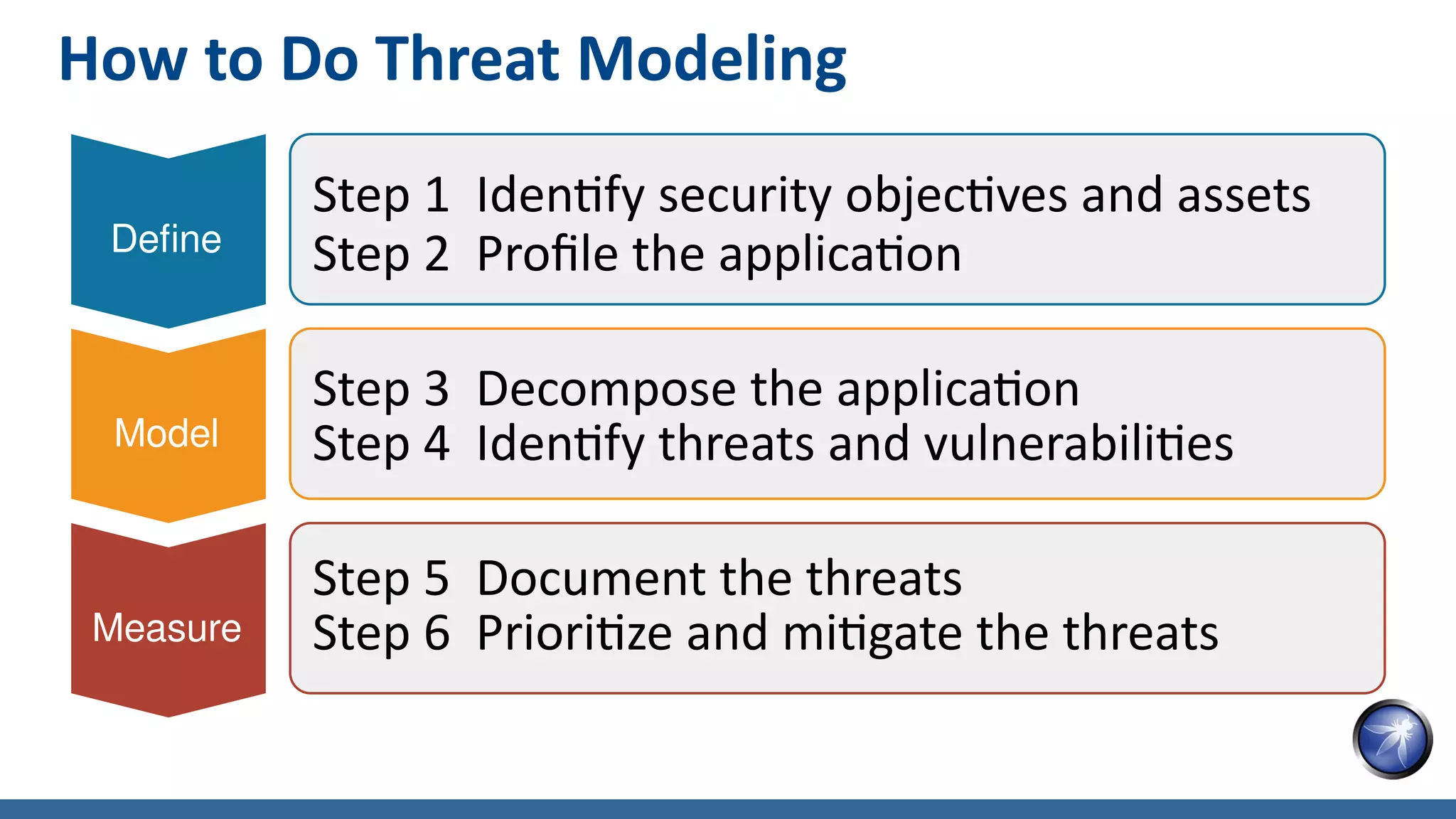
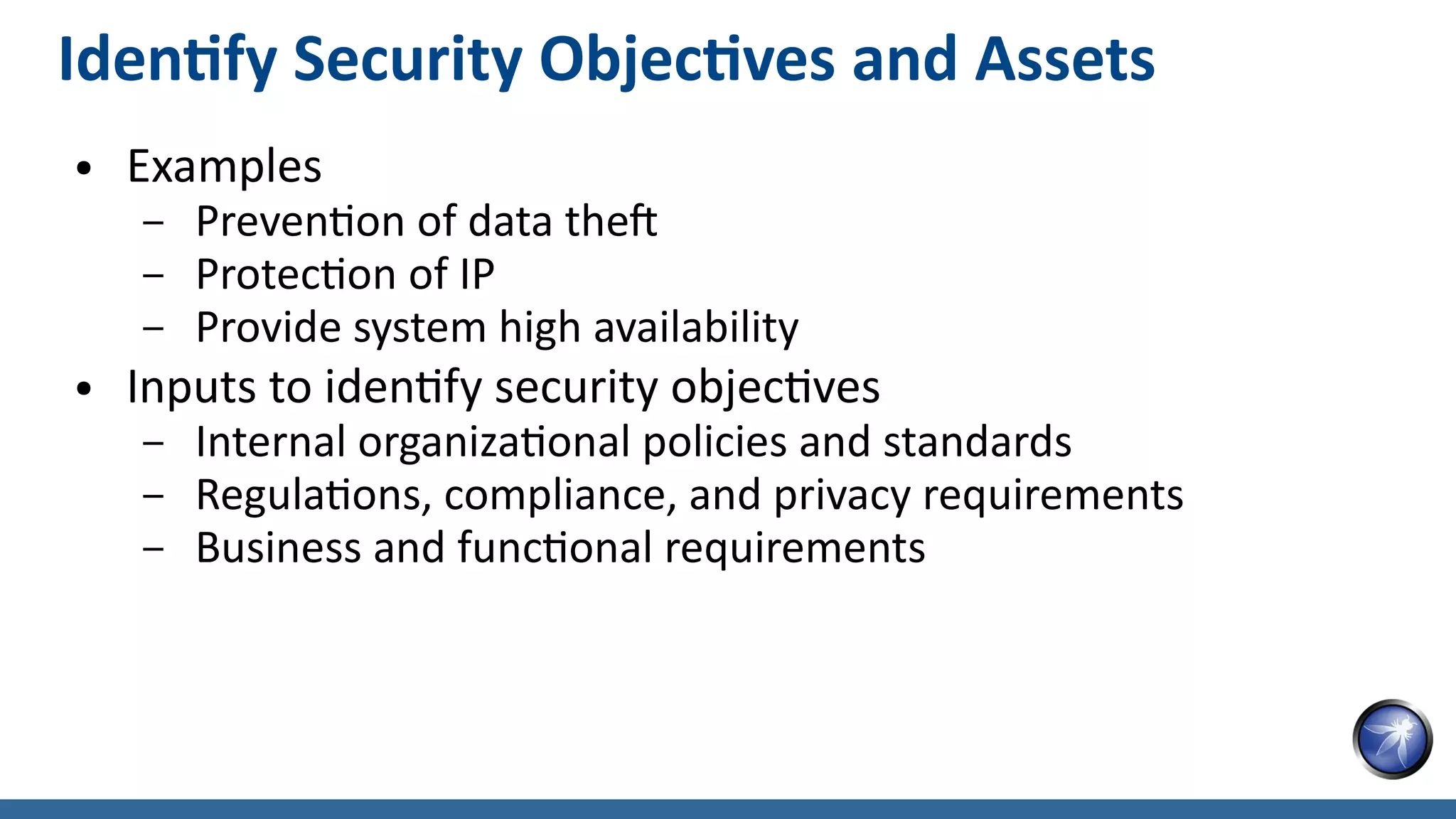
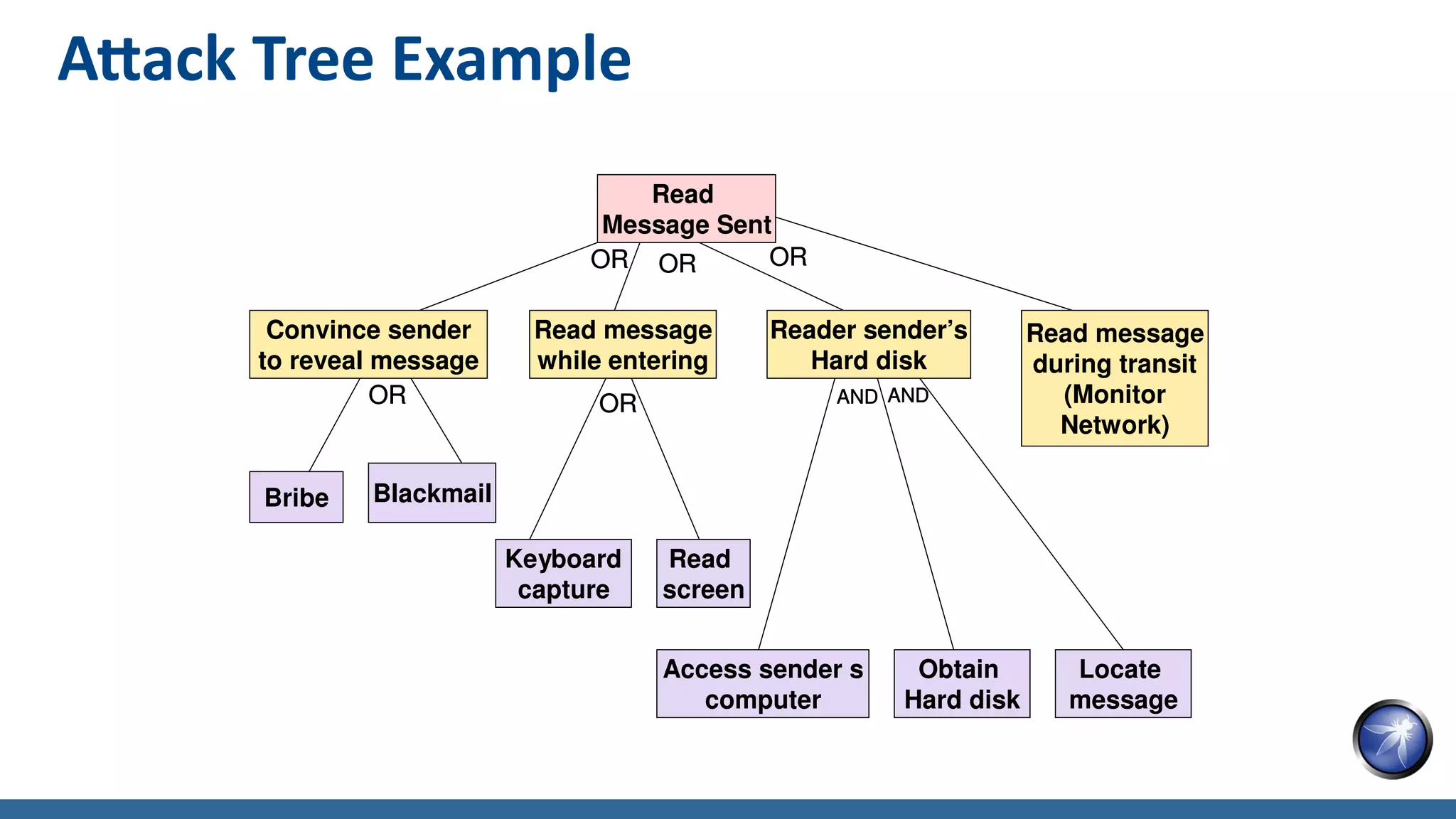
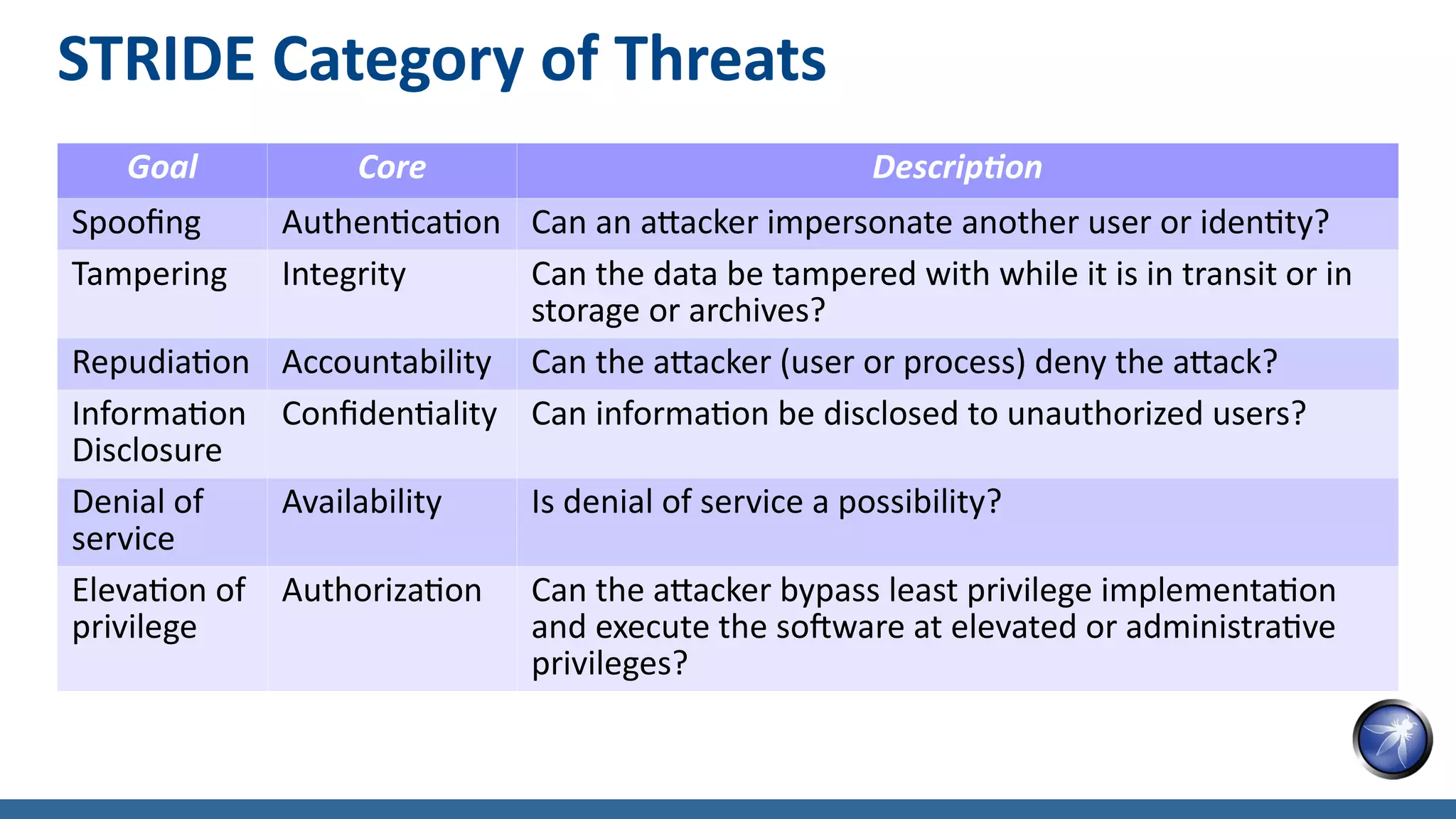
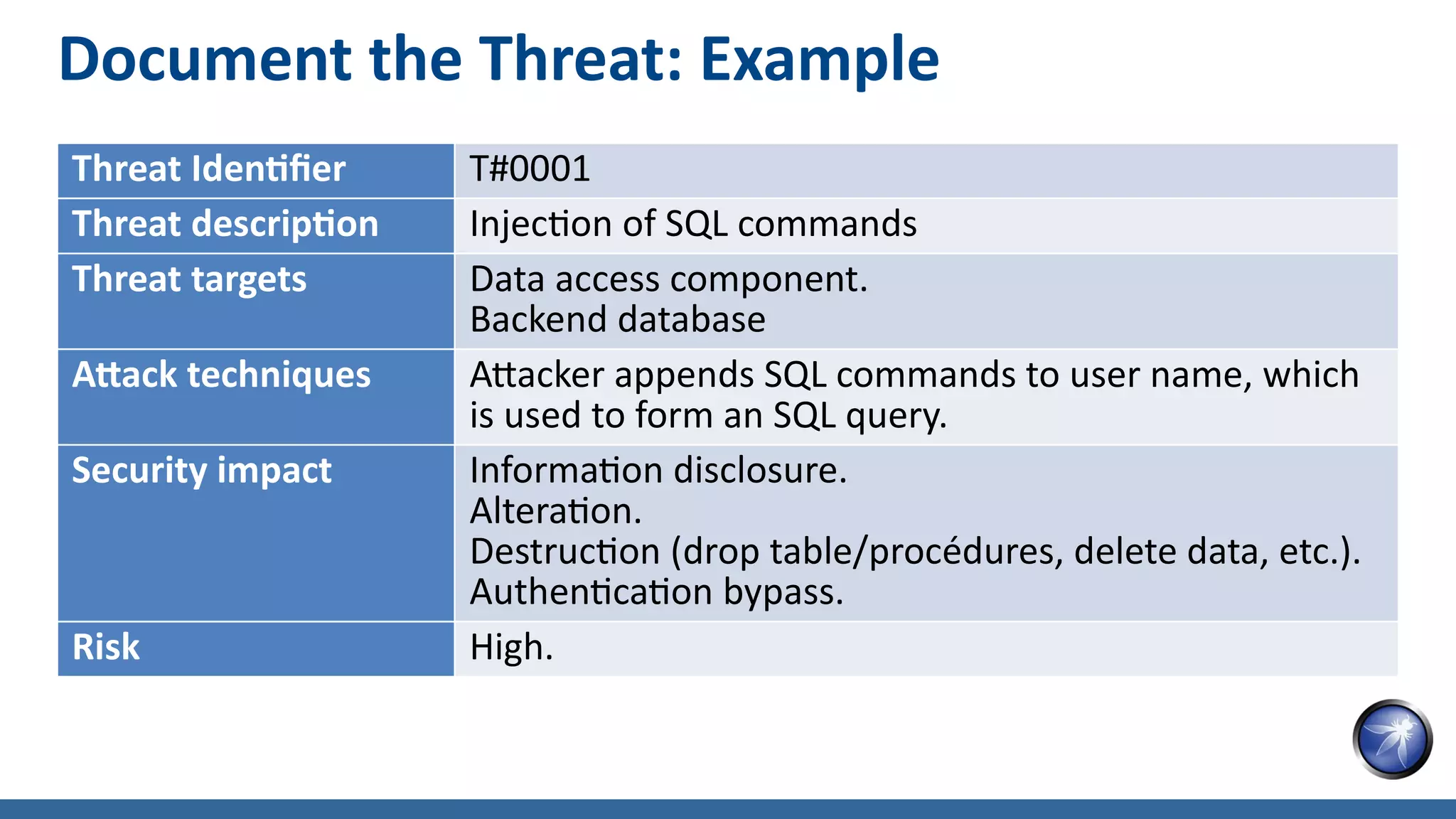
The document discusses threat modeling as a structured approach to analyze application security, emphasizing its importance in identifying and mitigating security risks early in the development process. It outlines the concept of attack surface, detailing how to assess and minimize vulnerabilities in software applications, and provides a step-by-step guide for effective threat modeling. The text also highlights key components in understanding threats, including potential attack vectors, categorized threat types, and best practices for documenting and prioritizing risks.