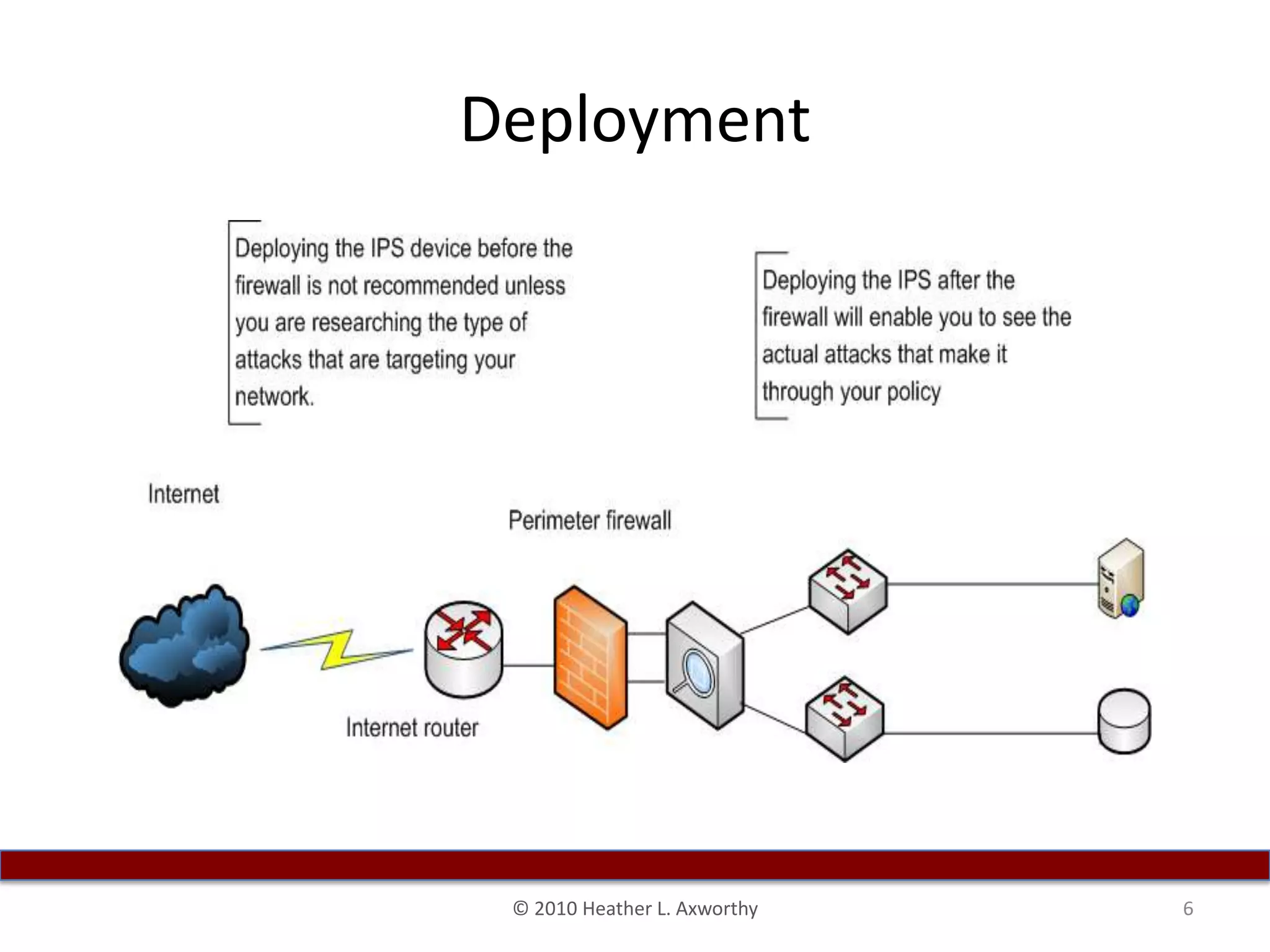
Heather Axworthy gives a presentation on intrusion prevention systems (IPS). She discusses what an IPS is and how it works inline to prevent attacks from penetrating networks. She emphasizes the importance of proper capacity planning and tuning when deploying an IPS. Ensuring company buy-in and adequate staffing levels are also key to ensuring the success of an IPS implementation. Several major IPS vendors are listed for reference.