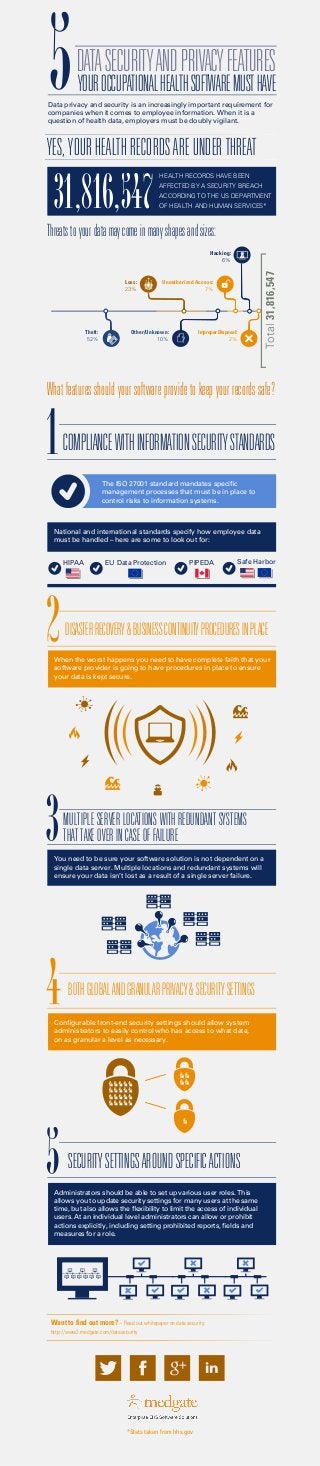
5 Data Security and Privacy Features your Occupational Health Software Must Have
- 1. COMPLIANCEWITHINFORMATIONSECURITYSTANDARDS DISASTERRECOVERY&BUSINESSCONTINUITYPROCEDURESINPLACE YES, YOURHEALTH RECORDS AREUNDER THREAT Threatstoyourdatamaycomeinmanyshapesandsizes: Whatfeaturesshouldyoursoftwareprovidetokeepyourrecordssafe? DATASECURITYANDPRIVACYFEATURES YOUROCCUPATIONALHEALTHSOFTWAREMUSTHAVE MULTIPLE SERVER LOCATIONS WITH REDUNDANT SYSTEMS THAT TAKE OVER IN CASE OF FAILURE BOTHGLOBALANDGRANULARPRIVACY&SECURITYSETTINGS Want to find out more? – Read out whitepaper on data security: http://www2.medgate.com/datasecurity *Stats taken from hhs.gov Data privacy and security is an increasingly important requirement for companies when it comes to employee information. When it is a question of health data, employers must be doubly vigilant. Total31,816,547 The ISO 27001 standard mandates specific management processes that must be in place to control risks to information systems. National and international standards specify how employee data must be handled – here are some to look out for: You need to be sure your software solution is not dependent on a single data server. Multiple locations and redundant systems will ensure your data isn’t lost as a result of a single server failure. HIPAA EU Data Protection PIPEDA Safe Harbor 31,816,547 HEALTH RECORDS HAVE BEEN AFFECTED BY A SECURITY BREACH ACCORDING TO THE US DEPARTMENT OF HEALTH AND HUMAN SERVICES* 0 20 40 60 80 100 Improper Disposal: 2% Hacking: 6% Theft: 52% Unauthorized Access: 7% Other/Unknown: 10% Loss: 23% Configurable front-end security settings should allow system administrators to easily control who has access to what data, on as granular a level as necessary. When the worst happens you need to have complete faith that your software provider is going to have procedures in place to ensure your data is kept secure. SECURITYSETTINGSAROUNDSPECIFICACTIONS Administrators should be able to set up various user roles. This allows you to update security settings for many users at the same time, but also allows the flexibility to limit the access of individual users. At an individual level administrators can allow or prohibit actions explicitly, including setting prohibited reports, fields and measures for a role.
