Multiple Macbooks Theft Recovery Case from Absolute Software – Case Number 8E6A3
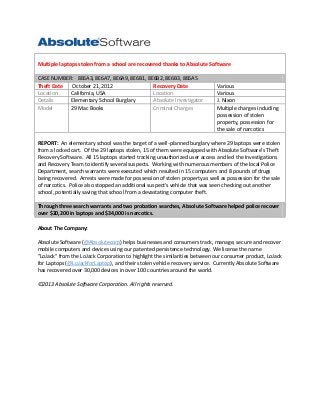
- 1. Multiple laptops stolen from a school are recovered thanks to Absolute Software CASE NUMBER: 8E6A3, 8E6A7, 8E6A9, 8E6B1, 8E6B2, 8E6B3, 8E6A5 Theft Date October 21, 2012 Recovery Date Location California, USA Location Details Elementary School Burglary Absolute Investigator Model 29 Mac Books Criminal Charges Various Various J. Nixon Multiple charges including possession of stolen property, possession for the sale of narcotics REPORT: An elementary school was the target of a well-planned burglary where 29 laptops were stolen from a locked cart. Of the 29 laptops stolen, 15 of them were equipped with Absolute Software’s Theft Recovery Software. All 15 laptops started tracking unauthorized user access and led the Investigations and Recovery Team to identify several suspects. Working with numerous members of the local Police Department, search warrants were executed which resulted in 15 computers and 8 pounds of drugs being recovered. Arrests were made for possession of stolen property as well as possession for the sale of narcotics. Police also stopped an additional suspect’s vehicle that was seen checking out another school, potentially saving that school from a devastating computer theft. Through three search warrants and two probation searches, Absolute Software helped police recover over $20,200 in laptops and $34,000 is narcotics. About The Company: Absolute Software (@Absolutecorp) helps businesses and consumers track, manage, secure and recover mobile computers and devices using our patented persistence technology. We license the name "LoJack" from the LoJack Corporation to highlight the similarities between our consumer product, LoJack for Laptops (@LoJackforLaptop), and their stolen vehicle recovery service. Currently Absolute Software has recovered over 30,000 devices in over 100 countries around the world. ©2013 Absolute Software Corporation. All rights reserved.
